Tell you how to ensure web application security
Web applications are at the forefront of most enterprise applications today. Web applications can perform many different functions in a complex hybrid architecture. It has applications ranging from service-oriented solutions running on the latest cloud technologies, to older multi-tier Web applications, to Web portals that allow customers to access legacy applications on mainframes.
Managing the risks associated with these complex web applications is an inevitable requirement for companies, and the security of the underlying code running these web applications directly affects the risk profile of the data available to the company's applications. Unfortunately, developing repeatable and efficient security practices for web applications is no simple task. Many organizations attempt to use post-production solutions to provide security controls, such as web application firewalls and intrusion prevention systems.
But waiting until the production phase of the life cycle to deploy security mechanisms is a bit too late and its effectiveness is too little. Design or architectural issues are easier to resolve early in the lifecycle than waiting until after the application is in production can be extremely costly. Security vulnerabilities in web applications can lead to data leaks, policy violations, and post-deployment patching or comprehensive code remediation can significantly increase the overall cost.
To ensure effectiveness and efficiency, the security of Web applications must start from the requirements definition phase to the final acceptance phase. This approach requires all designers to be able to work together as a team throughout the process. During phases such as implementation and testing, using automated tools that follow a strategy can support repeatable testing and lead to faster development cycles as the testing process is standardized.
Building security from the earliest stages of the development process doesn’t have to be complicated. Implementing security checks and balances throughout the development cycle enables faster release cycles and can greatly reduce web application vulnerabilities.
The high cost of implementing security testing late in the development cycle
Incorporating security checkpoints into the development process can indeed reduce overall delivery time. It may sound counterintuitive, but the costs associated with correcting design errors and coding errors after a web application is deployed into production is extremely high.
For example, in many development environments, security and audit experts tend to appear at the end of the development cycle. At this point, the application is complete and any delays are seen as unnecessary bottlenecks. The intense pressure on businesses to roll out software products quickly means that security controls can be overlooked, resulting in web applications not undergoing proper security review. In this extremely time-sensitive environment, even if a scanning tool reports a large number of vulnerabilities without validation and prioritization, such scanning can do more harm than good.
Conducting security audits late in the development process, rather than working together throughout the development cycle, can lead to delays in release times, especially if some serious bugs are discovered. The cost of fixing design and coding errors late in the development cycle is much higher than the cost of catching them early. A study by the National Science Foundation estimates that if serious software problems are discovered and corrected during the requirements and design stages, the cost is approximately 100 times lower than if the problem is discovered after the software is put into production.
When building security into a web application, in most cases the goal is not to build an impenetrable web application or to eliminate every possible vulnerability. Instead, the goal should be to match the required characteristics with the accepted risk profile for the web application. Throughout the development cycle of a Web application, the goal should be to achieve software assurance, that is, a level of functionality and sensitivity appropriate to the specific Web application that provides reasonable assurance that the software will continue to achieve its required characteristics, even if the software So can being attacked.
Benefits of an Integrated Approach
When developers from different groups work together as a team, it creates a high efficiency in the web application development process. While security professionals often lament that business leaders simply don't understand software risks, it's also important that security professionals are familiar with business risks. Building web applications with appropriate levels of software assurance requires risk management trade-offs between business needs, availability, and security. To achieve the right balance, the needs of all developers must be gathered.
From the beginning of software development, requirements definition and application design should consider security requirements as well as functional requirements and business needs. This information should be communicated to designers and software developers before writing code. This approach can prevent most or all security design vulnerabilities and architectural vulnerabilities.
However, software design that focuses on security does not eliminate all vulnerabilities associated with web applications. Developers themselves must be trained in secure coding techniques to ensure that security vulnerabilities are not introduced during the design of applications. Giving developers insight into the development language and runtime environment in a secure way can support better coding practices and result in the final web application being less buggy. Another efficiency benefit of incorporating security into the design process is the ability to establish misuse scenarios during requirements and design. Doing this during the testing and receiving phases saves time and helps eliminate bottlenecks.
The benefits of integrated synthetic testing
The integrated synthetic analysis method of software testing can greatly improve efficiency. Specific plug-ins for integrated development environments warn coders when they detect coding errors in the user's code. Static analysis, also known as "white box" testing, is a technique used by developers and auditors on different modules before they are assembled into a final product. Static analysis provides an insider's look at an application at the code level. Static analysis is effective at finding syntax errors and code-level flaws, but it is not suitable for determining whether a flaw results in an exploitable vulnerability.
Dynamic analysis and manual penetration testing are effective in verifying whether an application is vulnerable to attack. It is also called "black box testing". It mainly shows the inspection and analysis of the application by outsiders. It can conduct in-depth inspection of the application put into production to see whether it is easy for attackers to exploit its vulnerabilities. However, dynamic testing techniques can only be used in the later stages of software development, only in the post-generation phase. Another limitation of dynamic testing is that it can be difficult to find the source of code in the code that causes the vulnerability.
This is the reason why static testing and dynamic testing are combined to perform hybrid testing in a "grey box" or combined approach. By combining the results of code-level internal inspections with dynamic external inspections, you can leverage the best of both technologies. Using static and dynamic assessment tools allows managers and developers to prioritize applications, modules, vulnerabilities and address the highest-impact issues first. Another benefit of the combined analysis approach is that vulnerabilities identified by dynamic testing can be traced back to specific lines or blocks of code using static tools. This facilitates collaborative communication between test and development teams and makes it easier for security and test experts to provide developers with specific, actionable guidance on correcting problems.
Building security into the software life cycle: Practical methods
Building security requires people, processes, and technologies and methods. While there are numerous tools that can help automate the process of hardening web application security, no tool will be truly effective without the proper processes and trained personnel to create and test web applications.
This process should include a formal software development cycle and published strategy. Additionally, it is important to establish roles for all developers and assign inspection and supervisory responsibilities. Security and business should be represented at every stage of the software development cycle so that risk management can be addressed at every step.
Throughout the entire software development cycle, a beneficial and eternal theme is education. Education is important for developers, and it benefits everyone involved in web application development. Because security awareness needs to be both top-down and bottom-up. Don’t underestimate the importance of educating managers on how web application vulnerabilities can impact the business. Telling an executive that a web application is vulnerable to cross-site request forgery (CSRF) may be confusing, but showing him how a software bug can lead to the exposure of customer data can help make him aware of the insecurity. The real consequences of web applications. Specific cases and metrics should be prepared to illustrate potential various cost savings. For example, demonstrating that investments in developer training and static analysis plug-ins for IDEs can prevent the sources of data leakage in software applications before they inspect their code.
Auditors and evaluators can learn about common coding errors, assess their consequences, and interact with the web application "ecosystem" (including the back-end supporting systems, existing security controls, and anything that is part of the web application environment). service or application). Testers and quality assessment experts should be familiar with misuse scenarios and how they differ from applications of the standard. They should also know how to interpret safety test results and be able to prioritize results as needed.
Focus on specific steps in the software development cycle where opportunities exist to increase efficiency while implementing security and risk management.
Requirements
Web application designers are very familiar with defining functional and business requirements, but they may not understand how to define security requirements. At this point, the entire team needs to work together to decide which security controls are critical to the final web application.
Steps to integrate security into the requirements phase
1. Discuss and define security requirements based on company policy, compliance and regulatory requirements.
2. Security and audit teams should evaluate the business requirements and functionality of the web application and begin developing misuse cases (misuse scenarios) during testing and acceptance.
The benefits are twofold. One is to eliminate or reduce security or violation issues in advance, and the other is to reduce deployment time.
Architecture and Design
Now that the architecture and design of the web application have been defined, the next step is to assess security issues. It is during this phase that costly, difficult-to-correct safety issues can be fixed at the time they are most resolvable. To prevent costly mistakes, the program's architecture should be evaluated from both performance and security perspectives. Detailed design specifications are compiled to show developers what security controls should be included and how the application's components interact with the full Web application.
Steps to integrate security into the architecture and design phases
1. Perform a risk assessment of the proposed architecture and deployment environment to determine whether the design poses risks.
2. Evaluate the security implications and risks when the application interacts with the original system, as well as the security issues of data flow between different components, layers or systems.
3. Comment on any specific exposure issues that need to be addressed during the implementation or deployment phase (i.e., vulnerabilities that depend on how and where the application is deployed).
4. Consider dependencies and vulnerabilities caused by interactions with mashups, SOA, and partner services. Deliver the final design to security and audit to identify security test plans and misuse scenarios.
Its benefits are reflected in five aspects:
1. The risk assessment analysis process and reusable risk assessment model can be carefully coordinated.
2. Risks posed by the architectural environment or deployment environment can be identified at an early stage.
3. Reusable misuse cases can save time during the testing phase.
4. Reduce specific design vulnerabilities.
5. If necessary, you can adjust or change the architectural constraints that bring risks. If the risks cannot be completely eliminated, you can also use compensating controls to define risk mitigation strategies.
Code Execution and Compilation
When developers start writing code, they must have a complete set of risk assessment designs and clear guidelines for security controls, or use them through an approved service. security control. Automated static code tools integrated into IDEs can provide developers with inspections and guidance while writing code. Automated tools can also be used to check code for violations against policy templates during compilation and provide insight into code-level security issues.
Steps to integrate security into the code execution and compilation phases
1. Install a static source code inspection tool that can be integrated with the integrated development environment.
2. As an option, developers can use independent coding tools to perform automated code inspections before delivering code.
3. The security and audit team spot-checks code modules to see if they comply with compliance requirements, and uses automated or manual code inspections to check for security risks before compilation.
4. During the compilation process, perform automated static code scanning to find security issues and policy compliance.
5. Use tools to track developers’ coding errors and provide explanatory feedback and reasons for the security risks they pose.
This will bring the following benefits:
1. Cleaner or less buggy code can be submitted to quality assessors.
2. Over time, personnel can improve their secure coding capabilities.
3. Reusable strategies can improve the accuracy of risk analysis.
4. Fewer coding errors or vulnerabilities are discovered during the testing phase, resulting in a shorter development cycle.
Quality Assessment/Testing
Specific security tools for testing applications range from standalone solutions and services that can evaluate complete applications to fully integrated suites. This suite provides testing and support for multiple stages, from education to implementation. Integrated solutions provide multi-phase support for companies that have demonstrated maturity in repeatable web application security cycles. Integrated suites can be implemented at multiple points in the process and provide metrics and feedback for continuous improvement.
So, what steps should be taken to integrate security and improve security during the quality evaluation and testing phase?
1. Focus on discovering the most important issues with certain resources.
2. Validate these test findings within an application architecture that includes existing remediation controls (such as firewalls and IPS).
3. Prioritize discovered vulnerabilities based on security and business needs.
4. Suggest repairs for lines of code or APIs, services, libraries, etc. that they depend on.
The benefits are also obvious: 1. Application developers can communicate better with each other. 2. There is less plausibility. 3. Faster repair cycle.
Deployment/Commissioning
Web application security does not end at the deployment stage of the application. Once a web application is in production, additional testing and monitoring should be implemented to ensure data and services are protected. Automated security monitoring of actual web applications ensures that the application is running as expected and is not leaking information that could pose a risk. Monitoring can be done in-house or outsourced to an outside vendor that can monitor applications around the clock.
Steps to integrate and improve security during the deployment and production phases:
1. Monitor misuse to identify so-called "unexploited vulnerabilities" in testing It really won't be used after it's put into production.
2. Monitor data leaks to find all places where it has been incorrectly used, sent or stored.
3. Compare the pre-deployment risk assessment with the post-production exposure scope and provide feedback to the testing team.
4. Implement web application firewalls, IPS, or other remediation measures to mitigate exposure before code is fixed or to comply with new security regulations.
The benefits are as follows:
1. Improve the knowledge base of vulnerability exploits that can be successfully implemented, thereby improving scanning efficiency during static and dynamic testing.
2. Discover and prevent application misuse.
3. Achieve better integration between dynamic testing and application controls in production (such as Web Application Firewall or IPS).
4. Meet compliance needs before writing code again.
5. Use feedback mechanisms to achieve continuous improvement.
Summary
Securing web applications does not necessarily mean extending the development cycle. With good education for all developers and a clear and repeatable build process, organizations can incorporate security and risk into the development process in an efficient and collaborative way.
Building security into the web application delivery cycle does require a collaborative approach that integrates people, processes and technology. While web application security tools and suites can help improve the process, they are not a panacea. To get the most benefit, you should consider choosing a web application security tool vendor that understands the complete development cycle and has tools that can provide support at multiple stages of the development process.
The above is the detailed content of Tell you how to ensure web application security. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to Undo Delete from Home Screen in iPhone
Apr 17, 2024 pm 07:37 PM
How to Undo Delete from Home Screen in iPhone
Apr 17, 2024 pm 07:37 PM
Deleted something important from your home screen and trying to get it back? You can put app icons back on the screen in a variety of ways. We have discussed all the methods you can follow and put the app icon back on the home screen. How to Undo Remove from Home Screen in iPhone As we mentioned before, there are several ways to restore this change on iPhone. Method 1 – Replace App Icon in App Library You can place an app icon on your home screen directly from the App Library. Step 1 – Swipe sideways to find all apps in the app library. Step 2 – Find the app icon you deleted earlier. Step 3 – Simply drag the app icon from the main library to the correct location on the home screen. This is the application diagram
 The role and practical application of arrow symbols in PHP
Mar 22, 2024 am 11:30 AM
The role and practical application of arrow symbols in PHP
Mar 22, 2024 am 11:30 AM
The role and practical application of arrow symbols in PHP In PHP, the arrow symbol (->) is usually used to access the properties and methods of objects. Objects are one of the basic concepts of object-oriented programming (OOP) in PHP. In actual development, arrow symbols play an important role in operating objects. This article will introduce the role and practical application of arrow symbols, and provide specific code examples to help readers better understand. 1. The role of the arrow symbol to access the properties of an object. The arrow symbol can be used to access the properties of an object. When we instantiate a pair
 Security challenges in Golang development: How to avoid being exploited for virus creation?
Mar 19, 2024 pm 12:39 PM
Security challenges in Golang development: How to avoid being exploited for virus creation?
Mar 19, 2024 pm 12:39 PM
Security challenges in Golang development: How to avoid being exploited for virus creation? With the wide application of Golang in the field of programming, more and more developers choose to use Golang to develop various types of applications. However, like other programming languages, there are security challenges in Golang development. In particular, Golang's power and flexibility also make it a potential virus creation tool. This article will delve into security issues in Golang development and provide some methods to avoid G
 From beginner to proficient: Explore various application scenarios of Linux tee command
Mar 20, 2024 am 10:00 AM
From beginner to proficient: Explore various application scenarios of Linux tee command
Mar 20, 2024 am 10:00 AM
The Linuxtee command is a very useful command line tool that can write output to a file or send output to another command without affecting existing output. In this article, we will explore in depth the various application scenarios of the Linuxtee command, from entry to proficiency. 1. Basic usage First, let’s take a look at the basic usage of the tee command. The syntax of tee command is as follows: tee[OPTION]...[FILE]...This command will read data from standard input and save the data to
 What is the relationship between memory management techniques and security in Java functions?
May 02, 2024 pm 01:06 PM
What is the relationship between memory management techniques and security in Java functions?
May 02, 2024 pm 01:06 PM
Memory management in Java involves automatic memory management, using garbage collection and reference counting to allocate, use and reclaim memory. Effective memory management is crucial for security because it prevents buffer overflows, wild pointers, and memory leaks, thereby improving the safety of your program. For example, by properly releasing objects that are no longer needed, you can avoid memory leaks, thereby improving program performance and preventing crashes.
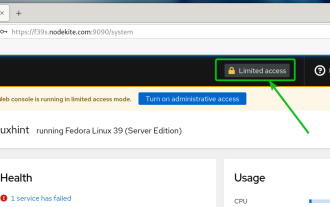 How to enable administrative access from the cockpit web UI
Mar 20, 2024 pm 06:56 PM
How to enable administrative access from the cockpit web UI
Mar 20, 2024 pm 06:56 PM
Cockpit is a web-based graphical interface for Linux servers. It is mainly intended to make managing Linux servers easier for new/expert users. In this article, we will discuss Cockpit access modes and how to switch administrative access to Cockpit from CockpitWebUI. Content Topics: Cockpit Entry Modes Finding the Current Cockpit Access Mode Enable Administrative Access for Cockpit from CockpitWebUI Disabling Administrative Access for Cockpit from CockpitWebUI Conclusion Cockpit Entry Modes The cockpit has two access modes: Restricted Access: This is the default for the cockpit access mode. In this access mode you cannot access the web user from the cockpit
 Explore the advantages and application scenarios of Go language
Mar 27, 2024 pm 03:48 PM
Explore the advantages and application scenarios of Go language
Mar 27, 2024 pm 03:48 PM
The Go language is an open source programming language developed by Google and first released in 2007. It is designed to be a simple, easy-to-learn, efficient, and highly concurrency language, and is favored by more and more developers. This article will explore the advantages of Go language, introduce some application scenarios suitable for Go language, and give specific code examples. Advantages: Strong concurrency: Go language has built-in support for lightweight threads-goroutine, which can easily implement concurrent programming. Goroutin can be started by using the go keyword
 The wide application of Linux in the field of cloud computing
Mar 20, 2024 pm 04:51 PM
The wide application of Linux in the field of cloud computing
Mar 20, 2024 pm 04:51 PM
The wide application of Linux in the field of cloud computing With the continuous development and popularization of cloud computing technology, Linux, as an open source operating system, plays an important role in the field of cloud computing. Due to its stability, security and flexibility, Linux systems are widely used in various cloud computing platforms and services, providing a solid foundation for the development of cloud computing technology. This article will introduce the wide range of applications of Linux in the field of cloud computing and give specific code examples. 1. Application virtualization technology of Linux in cloud computing platform Virtualization technology






