车窗控制系统的LIN2.1协议应用
欢迎进入IT技术社区论坛,与200万技术人员互动交流 >>进入 主节点的请求帧在D1中给出需要分配帧ID的第一个帧在帧数组中的序号,一般来说,从节点所用到的所有帧的ID会被排列成一个帧数组。如果要分配帧ID,则通过D2到D5给出新的帧ID;如果要禁止某个帧,则将
欢迎进入IT技术社区论坛,与200万技术人员互动交流 >>进入
主节点的请求帧在D1中给出需要分配帧ID的第一个帧在帧数组中的序号,一般来说,从节点所用到的所有帧的ID会被排列成一个帧数组。如果要分配帧ID,则通过D2到D5给出新的帧ID;如果要禁止某个帧,则将这个帧对应的PID设为0x00;如果要继续使用现在的帧ID,则将这个帧对应的PID设为0xFF.(5)读取从节点信息读取节点信息根据D1中ID的值,可以读取不同的从节点信息。目前,只规定了ID为0和ID为1的情况,其他可保留或由用户自己确定。
3 LIN通信的实现
3.1 TLE9832的LIN模块
TLE9832是一款由英飞凌公司生产的8位功率级单片机,专门用于车窗控制。其中的LIN总线模块支持LIN2.1和LIN2.0,并向下兼容LIN 1.3.该模块可以工作在普通模式、接收模式和禁止模式下。各个模式的特点如表1所列。

其中,普通模式又可根据传输速率的大小分为低速模式、中速模式、高速模式和Flash模式。低速模式的最大传输速率为10.4 kbps;中速模式是普通的LIN传输模式,最大传输速率为20 kbps;高速模式的最大传输速率为40 kbps;Flash模式的最大传输速率为11 5 khps.为了避免打断传输过程,在普通模式下禁止改变传输速率。正确的做法是先禁止发送功能,再改变传输速率,最后允许发送功能。
LIN模块在普通模式下还建立了一种自动省电机制。当发送队列中没有数据时,将自动禁止发送功能;当有发送请求时,将自动开启发送功能。
3.2基于TLE9832的车窗防夹控制系统
基丁TLE9832的防夹车窗控制系统是英飞凌-同济微控制器与嵌入式系统实验室的最新研究成果。用户可以通过按键或者LIN总线控制车窗的上升和下降。基于TLE9832的防夹车窗系统原理图如图4所示。可通过控制PWM信号控制电机的转速,而霍尔传感器TLE4966又会采集电机的转速并传送给TLE9832,这样就构成了闭环控制。此外,电机的电枢电流在转化为电压信号后,被传送给TLE9832的ADC模块。如果车窗在上升过程中遇到不正常的阻力,电枢电流和电机转速都会发生异常的变化,TLE9832可以根据这种变化判断是否执行防夹算法,避免伤害乘客。

3.3 LIN通信部分的软件设计
LIN通信部分的程序流程如图5所示。可将车窗控制器中LIN通信部分的程序分为两个部分:①第一部分为初始化,在每次重新上电后,程序都会首先读取Flash中的数据,若0x8000中的数据为0x78,则判断产品在出厂后执行过保存配置的功能。所以程序会将存储在Flash中的NAD和帧ID读出来,作为当前的NAD和帧ID.接着是初始化LIN模块,包括设置与LIN通信相关的定时器和UART等外设,设置从节点的各个参数、波特率等。

②第二部分则放在定时器中断里面,在每次中断时进行节点配置、数据的发送和接收。首先是根据帧ID判断有无节点配置任务,若有则根据SID执行各种节点配置任务;接着根据收到的数据帧内容控制车窗的自动上升和自动下降;最后将车窗信息,包括电枢电流、车窗位置等发给主节点。
4 LIN通信的测试结果
本测试借助Kvaser公司出品的LIN通信测试工具Lcaf Professional LIN及其配套软件CANLab完成。测试时测试工具设置为主节点,TLE9 832单片机设置为从节点,比特率设置为19200 bps.初始NAD设置为0x06,初始帧ID为无条件帧0x00、0x01和诊断配置帧0x3C、0x3D,Suppli erID和Function ID都为0x0000.首先测试节点配置的各个功能:先测试分配NAD功能,将NAD修改为0x03;接着测试有条件分配NAD功能,将NAD修改为0x08;然后测试分配一系列帧ID功能,并保存设置;最后重新上电,并读取从节点信息。节点配置功能的测试结果如图6所示。

然后通过LIN总线控制车窗自动上升和下降,测试结果如图7所示。
最后通过LIN总线获得车窗上升过程中电枢电流的数据,并转换成图形,如图8所示。其中电流值为经过A/D转换后的结果。

结语
本文基于LIN2.1协议设计了防夹车窗控制系统中的通信模块。可以看出,该模块可以很好地满足用户在数据传输和诊断等方面的需求。LIN总线自身的发展必将推动车身控制领域的进一步发展。
[1] [2]


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 The role and practical application of arrow symbols in PHP
Mar 22, 2024 am 11:30 AM
The role and practical application of arrow symbols in PHP
Mar 22, 2024 am 11:30 AM
The role and practical application of arrow symbols in PHP In PHP, the arrow symbol (->) is usually used to access the properties and methods of objects. Objects are one of the basic concepts of object-oriented programming (OOP) in PHP. In actual development, arrow symbols play an important role in operating objects. This article will introduce the role and practical application of arrow symbols, and provide specific code examples to help readers better understand. 1. The role of the arrow symbol to access the properties of an object. The arrow symbol can be used to access the properties of an object. When we instantiate a pair
 How to Undo Delete from Home Screen in iPhone
Apr 17, 2024 pm 07:37 PM
How to Undo Delete from Home Screen in iPhone
Apr 17, 2024 pm 07:37 PM
Deleted something important from your home screen and trying to get it back? You can put app icons back on the screen in a variety of ways. We have discussed all the methods you can follow and put the app icon back on the home screen. How to Undo Remove from Home Screen in iPhone As we mentioned before, there are several ways to restore this change on iPhone. Method 1 – Replace App Icon in App Library You can place an app icon on your home screen directly from the App Library. Step 1 – Swipe sideways to find all apps in the app library. Step 2 – Find the app icon you deleted earlier. Step 3 – Simply drag the app icon from the main library to the correct location on the home screen. This is the application diagram
 DualBEV: significantly surpassing BEVFormer and BEVDet4D, open the book!
Mar 21, 2024 pm 05:21 PM
DualBEV: significantly surpassing BEVFormer and BEVDet4D, open the book!
Mar 21, 2024 pm 05:21 PM
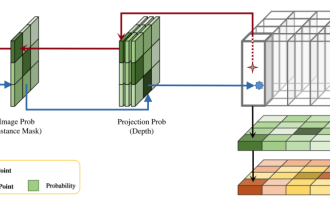
This paper explores the problem of accurately detecting objects from different viewing angles (such as perspective and bird's-eye view) in autonomous driving, especially how to effectively transform features from perspective (PV) to bird's-eye view (BEV) space. Transformation is implemented via the Visual Transformation (VT) module. Existing methods are broadly divided into two strategies: 2D to 3D and 3D to 2D conversion. 2D-to-3D methods improve dense 2D features by predicting depth probabilities, but the inherent uncertainty of depth predictions, especially in distant regions, may introduce inaccuracies. While 3D to 2D methods usually use 3D queries to sample 2D features and learn the attention weights of the correspondence between 3D and 2D features through a Transformer, which increases the computational and deployment time.
 From beginner to proficient: Explore various application scenarios of Linux tee command
Mar 20, 2024 am 10:00 AM
From beginner to proficient: Explore various application scenarios of Linux tee command
Mar 20, 2024 am 10:00 AM
The Linuxtee command is a very useful command line tool that can write output to a file or send output to another command without affecting existing output. In this article, we will explore in depth the various application scenarios of the Linuxtee command, from entry to proficiency. 1. Basic usage First, let’s take a look at the basic usage of the tee command. The syntax of tee command is as follows: tee[OPTION]...[FILE]...This command will read data from standard input and save the data to
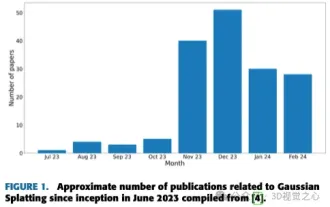 More than just 3D Gaussian! Latest overview of state-of-the-art 3D reconstruction techniques
Jun 02, 2024 pm 06:57 PM
More than just 3D Gaussian! Latest overview of state-of-the-art 3D reconstruction techniques
Jun 02, 2024 pm 06:57 PM
Written above & The author’s personal understanding is that image-based 3D reconstruction is a challenging task that involves inferring the 3D shape of an object or scene from a set of input images. Learning-based methods have attracted attention for their ability to directly estimate 3D shapes. This review paper focuses on state-of-the-art 3D reconstruction techniques, including generating novel, unseen views. An overview of recent developments in Gaussian splash methods is provided, including input types, model structures, output representations, and training strategies. Unresolved challenges and future directions are also discussed. Given the rapid progress in this field and the numerous opportunities to enhance 3D reconstruction methods, a thorough examination of the algorithm seems crucial. Therefore, this study provides a comprehensive overview of recent advances in Gaussian scattering. (Swipe your thumb up
 Revolutionary GPT-4o: Reshaping the human-computer interaction experience
Jun 07, 2024 pm 09:02 PM
Revolutionary GPT-4o: Reshaping the human-computer interaction experience
Jun 07, 2024 pm 09:02 PM
The GPT-4o model released by OpenAI is undoubtedly a huge breakthrough, especially in its ability to process multiple input media (text, audio, images) and generate corresponding output. This ability makes human-computer interaction more natural and intuitive, greatly improving the practicality and usability of AI. Several key highlights of GPT-4o include: high scalability, multimedia input and output, further improvements in natural language understanding capabilities, etc. 1. Cross-media input/output: GPT-4o+ can accept any combination of text, audio, and images as input and directly generate output from these media. This breaks the limitation of traditional AI models that only process a single input type, making human-computer interaction more flexible and diverse. This innovation helps power smart assistants
 Explore the advantages and application scenarios of Go language
Mar 27, 2024 pm 03:48 PM
Explore the advantages and application scenarios of Go language
Mar 27, 2024 pm 03:48 PM
The Go language is an open source programming language developed by Google and first released in 2007. It is designed to be a simple, easy-to-learn, efficient, and highly concurrency language, and is favored by more and more developers. This article will explore the advantages of Go language, introduce some application scenarios suitable for Go language, and give specific code examples. Advantages: Strong concurrency: Go language has built-in support for lightweight threads-goroutine, which can easily implement concurrent programming. Goroutin can be started by using the go keyword
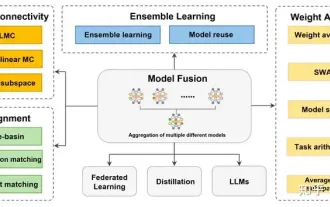 Review! Deep model fusion (LLM/basic model/federated learning/fine-tuning, etc.)
Apr 18, 2024 pm 09:43 PM
Review! Deep model fusion (LLM/basic model/federated learning/fine-tuning, etc.)
Apr 18, 2024 pm 09:43 PM
In September 23, the paper "DeepModelFusion:ASurvey" was published by the National University of Defense Technology, JD.com and Beijing Institute of Technology. Deep model fusion/merging is an emerging technology that combines the parameters or predictions of multiple deep learning models into a single model. It combines the capabilities of different models to compensate for the biases and errors of individual models for better performance. Deep model fusion on large-scale deep learning models (such as LLM and basic models) faces some challenges, including high computational cost, high-dimensional parameter space, interference between different heterogeneous models, etc. This article divides existing deep model fusion methods into four categories: (1) "Pattern connection", which connects solutions in the weight space through a loss-reducing path to obtain a better initial model fusion






