配置TFS服务器所需要的数据库权限
原文: http://www.almnetworks.net/zh-CN/post/2010/08/25/Database-Permissions-Required-to-Configure-TFS.aspx 大多数时候,我们使用SQL Admin来安装TFS服务器是没有任何问题的,但是你要碰上一个留着大胡子的DBA的话,恐怕就没有那么简单了。很多的大公
原文: http://www.almnetworks.net/zh-CN/post/2010/08/25/Database-Permissions-Required-to-Configure-TFS.aspx
大多数时候,我们使用SQL Admin来安装TFS服务器是没有任何问题的,但是你要碰上一个留着大胡子的DBA的话,恐怕就没有那么简单了。很多的大公司对安全问题非常重视,所以我们还是需要了解到底TFS需要怎样的权限来进行安装和配置。
如果你是那个碰到了大胡子DBA的倒霉程序员,请往下看:
- 安装TFS的用户需要是serveradmin 的服务器角色,因为在配置TFS的过程中,我们需要安装新的系统信息(system messages)。这个操作需要ServerAdmin的角色权限,具体请见: http://msdn.microsoft.com/en-us/library/ms178649.aspx.
- ALTER ANY LOGIN, VIEW ANY DEFINITION 服务器权限,因为在配置TFS的过程中我们需要查询已经有的SQL用户并为服务账户创建新的SQL用户名。
-
CONTROL on master. 在master数据库上的权限
- CREATE ROLE – 我们需要这个权限来创建 TFSEXECROLE.
- VIEW DEFINITION – 我们需要次权限来查询数据库的扩展属性
- ALTER – 用来安装消息,我们会删除并重建 prc_Install*Messages 存储过程, 比如 prc_InstallBuildMessages, prc_InstallVersionControlMessage, 等等。
- EXECUTE – 我们需要此权限来执行 prc_Install*Messages 存储过程.
- CREATE DATABASE - 我们需要此权限来创建,配置数据挖掘数据库。

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
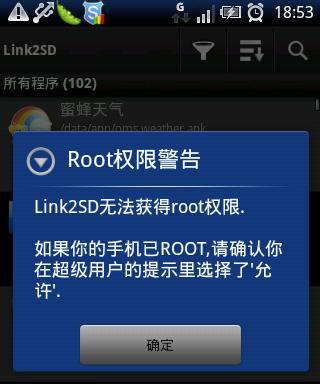 Enable root permissions with one click (quickly obtain root permissions)
Jun 02, 2024 pm 05:32 PM
Enable root permissions with one click (quickly obtain root permissions)
Jun 02, 2024 pm 05:32 PM
It allows users to perform more in-depth operations and customization of the system. Root permission is an administrator permission in the Android system. Obtaining root privileges usually requires a series of tedious steps, which may not be very friendly to ordinary users, however. By enabling root permissions with one click, this article will introduce a simple and effective method to help users easily obtain system permissions. Understand the importance and risks of root permissions and have greater freedom. Root permissions allow users to fully control the mobile phone system. Strengthen security controls, customize themes, and users can delete pre-installed applications. For example, accidentally deleting system files causing system crashes, excessive use of root privileges, and inadvertent installation of malware are also risky, however. Before using root privileges
 How does Go language implement the addition, deletion, modification and query operations of the database?
Mar 27, 2024 pm 09:39 PM
How does Go language implement the addition, deletion, modification and query operations of the database?
Mar 27, 2024 pm 09:39 PM
Go language is an efficient, concise and easy-to-learn programming language. It is favored by developers because of its advantages in concurrent programming and network programming. In actual development, database operations are an indispensable part. This article will introduce how to use Go language to implement database addition, deletion, modification and query operations. In Go language, we usually use third-party libraries to operate databases, such as commonly used sql packages, gorm, etc. Here we take the sql package as an example to introduce how to implement the addition, deletion, modification and query operations of the database. Assume we are using a MySQL database.
 How to install PHP FFmpeg extension on server?
Mar 28, 2024 pm 02:39 PM
How to install PHP FFmpeg extension on server?
Mar 28, 2024 pm 02:39 PM
How to install PHPFFmpeg extension on server? Installing the PHPFFmpeg extension on the server can help us process audio and video files in PHP projects and implement functions such as encoding, decoding, editing, and processing of audio and video files. This article will introduce how to install the PHPFFmpeg extension on the server, as well as specific code examples. First, we need to ensure that PHP and FFmpeg are installed on the server. If FFmpeg is not installed, you can follow the steps below to install FFmpe
 How does Hibernate implement polymorphic mapping?
Apr 17, 2024 pm 12:09 PM
How does Hibernate implement polymorphic mapping?
Apr 17, 2024 pm 12:09 PM
Hibernate polymorphic mapping can map inherited classes to the database and provides the following mapping types: joined-subclass: Create a separate table for the subclass, including all columns of the parent class. table-per-class: Create a separate table for subclasses, containing only subclass-specific columns. union-subclass: similar to joined-subclass, but the parent class table unions all subclass columns.
 iOS 18 adds a new 'Recovered' album function to retrieve lost or damaged photos
Jul 18, 2024 am 05:48 AM
iOS 18 adds a new 'Recovered' album function to retrieve lost or damaged photos
Jul 18, 2024 am 05:48 AM
Apple's latest releases of iOS18, iPadOS18 and macOS Sequoia systems have added an important feature to the Photos application, designed to help users easily recover photos and videos lost or damaged due to various reasons. The new feature introduces an album called "Recovered" in the Tools section of the Photos app that will automatically appear when a user has pictures or videos on their device that are not part of their photo library. The emergence of the "Recovered" album provides a solution for photos and videos lost due to database corruption, the camera application not saving to the photo library correctly, or a third-party application managing the photo library. Users only need a few simple steps
 An in-depth analysis of how HTML reads the database
Apr 09, 2024 pm 12:36 PM
An in-depth analysis of how HTML reads the database
Apr 09, 2024 pm 12:36 PM
HTML cannot read the database directly, but it can be achieved through JavaScript and AJAX. The steps include establishing a database connection, sending a query, processing the response, and updating the page. This article provides a practical example of using JavaScript, AJAX and PHP to read data from a MySQL database, showing how to dynamically display query results in an HTML page. This example uses XMLHttpRequest to establish a database connection, send a query and process the response, thereby filling data into page elements and realizing the function of HTML reading the database.
 Detailed tutorial on establishing a database connection using MySQLi in PHP
Jun 04, 2024 pm 01:42 PM
Detailed tutorial on establishing a database connection using MySQLi in PHP
Jun 04, 2024 pm 01:42 PM
How to use MySQLi to establish a database connection in PHP: Include MySQLi extension (require_once) Create connection function (functionconnect_to_db) Call connection function ($conn=connect_to_db()) Execute query ($result=$conn->query()) Close connection ( $conn->close())
 Introduction to how to set everyone permissions on win7 computer
Mar 26, 2024 pm 04:11 PM
Introduction to how to set everyone permissions on win7 computer
Mar 26, 2024 pm 04:11 PM
1. Take e-disk as an example. Open [Computer], and click [eDisk], right-click [Properties]. As shown in the figure: 2. In the [Window] page, switch the interface to the [Security] option, and click the [Edit] option below. As shown in the figure: 3. In the [Permissions] option, click the [Add] option. As shown in the figure: 4. The users and groups window pops up and click the [Advanced] option. As shown in the figure: 5. Click to expand the [Find Now] - [Everyone] options in order. When completed, click OK. As shown in the figure: 6. When you see that the user [everyone] has been added to [Group or User] on the [E Disk Permissions] page, select [everyone] and check the box in front of [Full Control]. After the setting is completed, Just press [OK]






