Access Control Flaws
Access Control Flaw:访问控制缺陷 角色的访问 控制方案: 个角色代表一组访问权限和特权, 单个用户可以设置多个角色。 角色访问控制方案由:角色权限管理,角色分配 构成 目前访问控制出现问题的地方一般在:事务,资源。 事务:值操作,比如:delete,mo
Access Control Flaw:访问控制缺陷
角色的访问控制方案:个角色代表一组访问权限和特权,单个用户可以设置多个角色。
角色访问控制方案由:角色权限管理,角色分配 构成
目前访问控制出现问题的地方一般在:事务,资源。
事务:值操作,比如:delete,modified等
资源:好理解,就是访问的内容,有一个标志,比如:ID,Name
水平权限概念
URL中若包含用户身份标识,通过修改该标识来达到转换身份的目的
URL或请求中包含资源ID,通过修改该ID来达到跨身份的操作资源
垂直权限概念
复制其他不同角色的URL或请求,在普通用户身份时发起,检查是否越权
Webgoat中的内容:
1、Using an Access Control Matrix
找出除了admin以外,角色是[User, Manager],可以访问Account Manager资源的用户
2、Bypass a Path Based Access Control Scheme
尝试访问服务器文件,比如tomcat/conf/tomcat-users.xml
3、LAB: Role Based Access Control
Bypass Business Layer Access Control:绕过事务层
Bypass Data Layer Access Control:绕过数据层
4、Remote Admin Access
直接在URL中加一个参数&admin=true, 试图使用管理员身份访问该页面

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
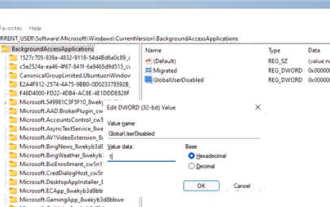 How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
1. Open settings in Windows 11. You can use Win+I shortcut or any other method. 2. Go to the Apps section and click Apps & Features. 3. Find the application you want to prevent from running in the background. Click the three-dot button and select Advanced Options. 4. Find the [Background Application Permissions] section and select the desired value. By default, Windows 11 sets power optimization mode. It allows Windows to manage how applications work in the background. For example, once you enable battery saver mode to preserve battery, the system will automatically close all apps. 5. Select [Never] to prevent the application from running in the background. Please note that if you notice that the program is not sending you notifications, failing to update data, etc., you can
 How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
DeepSeek cannot convert files directly to PDF. Depending on the file type, you can use different methods: Common documents (Word, Excel, PowerPoint): Use Microsoft Office, LibreOffice and other software to export as PDF. Image: Save as PDF using image viewer or image processing software. Web pages: Use the browser's "Print into PDF" function or the dedicated web page to PDF tool. Uncommon formats: Find the right converter and convert it to PDF. It is crucial to choose the right tools and develop a plan based on the actual situation.
 What does dao mean in java
Apr 21, 2024 am 02:08 AM
What does dao mean in java
Apr 21, 2024 am 02:08 AM
DAO (Data Access Object) in Java is used to separate application code and persistence layer, its advantages include: Separation: Independent from application logic, making it easier to modify it. Encapsulation: Hide database access details and simplify interaction with the database. Scalability: Easily expandable to support new databases or persistence technologies. With DAOs, applications can call methods to perform database operations such as create, read, update, and delete entities without directly dealing with database details.
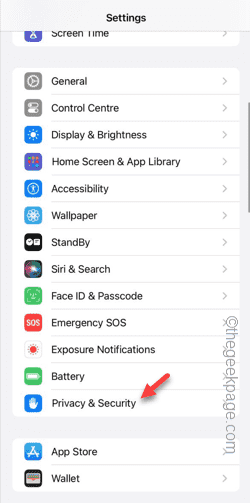 Can't allow access to camera and microphone in iPhone
Apr 23, 2024 am 11:13 AM
Can't allow access to camera and microphone in iPhone
Apr 23, 2024 am 11:13 AM
Are you getting "Unable to allow access to camera and microphone" when trying to use the app? Typically, you grant camera and microphone permissions to specific people on a need-to-provide basis. However, if you deny permission, the camera and microphone will not work and will display this error message instead. Solving this problem is very basic and you can do it in a minute or two. Fix 1 – Provide Camera, Microphone Permissions You can provide the necessary camera and microphone permissions directly in settings. Step 1 – Go to the Settings tab. Step 2 – Open the Privacy & Security panel. Step 3 – Turn on the “Camera” permission there. Step 4 – Inside, you will find a list of apps that have requested permission for your phone’s camera. Step 5 – Open the “Camera” of the specified app
 What does field mean in java
Apr 25, 2024 pm 10:18 PM
What does field mean in java
Apr 25, 2024 pm 10:18 PM
In Java, a "field" is a data member in a class or interface that is used to store data or state. The properties of field include: type (can be any Java data type), access rights, static (belongs to a class rather than an instance), final (immutable) and transient (not serialized). Field is used to store state information of a class or interface, such as storing object data and maintaining object state.
 How does the Java reflection mechanism modify the behavior of a class?
May 03, 2024 pm 06:15 PM
How does the Java reflection mechanism modify the behavior of a class?
May 03, 2024 pm 06:15 PM
The Java reflection mechanism allows programs to dynamically modify the behavior of classes without modifying the source code. By operating the Class object, you can create instances through newInstance(), modify private field values, call private methods, etc. Reflection should be used with caution, however, as it can cause unexpected behavior and security issues, and has a performance overhead.
 How to read dbf file in oracle
May 10, 2024 am 01:27 AM
How to read dbf file in oracle
May 10, 2024 am 01:27 AM
Oracle can read dbf files through the following steps: create an external table and reference the dbf file; query the external table to retrieve data; import the data into the Oracle table.
 Common exception types and their repair measures in Java function development
May 03, 2024 pm 02:09 PM
Common exception types and their repair measures in Java function development
May 03, 2024 pm 02:09 PM
Common exception types and their repair measures in Java function development During the development of Java functions, various exceptions may be encountered, which affect the correct execution of the function. The following are common exception types and their repair measures: 1. NullPointerException Description: Thrown when accessing an object that has not been initialized. Fix: Make sure you check the object for non-null before using it. Sample code: try{Stringname=null;System.out.println(name.length());}catch(NullPointerExceptione){






