访问控制列表access
欢迎进入网络技术社区论坛,与200万技术人员互动交流 >>进入 思科路由器交换机中的access-list(访问列表)最基本的有两种,分别是标准访问列表和扩展---- access-list 1 permit host 192.46.27.8 ---- access-list 1 permit host 192.46.27.12 ---- 注意,因为
欢迎进入网络技术社区论坛,与200万技术人员互动交流 >>进入
思科路由器交换机中的access-list(访问列表)最基本的有两种,分别是标准访问列表和扩展---- access-list 1 permit host 192.46.27.8
---- access-list 1 permit host 192.46.27.12
---- 注意,因为所有的访问列表会自动在最后包括该语句.
---- 顺便讨论一下标准型IP访问列表的参数“log”,它起日志的作用.一旦访问列表
作用于某个接口,那么包括关键字“log”的语句将记录那些满足访问列表放在所有其它VLAN上直接.
3) 如果在内网口上放置: 在入上设置Reflect
如果在外网口上放置: 在出口上放置Reflect
LAN WAN
-
inbound outbound
4)reflect不对本地路由器上的数据包跟踪,所以对待进入的数据包时注意,要允许一些
数据流进入
从IOS12.0开始,CISCO路由器新增加了一种基于时间的访问列表.通过它,可以根据一天ed auto
!
interface Serial2/0
ip address 12.1.1.1 255.255.255.0
encapsulation frame-relay
ip ospf network point-to-point
serial restart_delay 0
frame-relay map ip 12.1.1.2 102 broadcast
no frame-relay inverse-arp
!
interface Serial2/1
ip address 13.1.1.1 255.255.255.0
encapsulation frame-relay
ip ospf network point-to-point
serial restart_delay 0
frame-relay map ip 13.1.1.3 113 broadcast
!
interface Serial2/2
no ip address
shutdown
serial restart_delay 0
!
interface Serial2/3
no ip address
shutdown
serial restart_delay 0
!
router ospf 10
log-adjacency-changes
network 0.0.0.0 255.255.255.255 area 0
!
ip http server
no ip http secure-server
ip classless
!
!
!
!
!
call rsvp-sync
!
!
mgcp profile default
!
!
!
dial-peer cor custom
!
!
!
!
!
line con 0
line aux 0
line vty 0 4
no login
!
!
end
!
!
!
[1] [2]


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
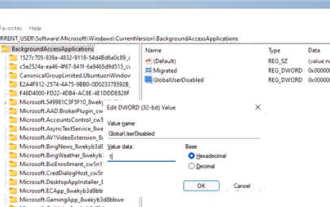 How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
1. Open settings in Windows 11. You can use Win+I shortcut or any other method. 2. Go to the Apps section and click Apps & Features. 3. Find the application you want to prevent from running in the background. Click the three-dot button and select Advanced Options. 4. Find the [Background Application Permissions] section and select the desired value. By default, Windows 11 sets power optimization mode. It allows Windows to manage how applications work in the background. For example, once you enable battery saver mode to preserve battery, the system will automatically close all apps. 5. Select [Never] to prevent the application from running in the background. Please note that if you notice that the program is not sending you notifications, failing to update data, etc., you can
 How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
DeepSeek cannot convert files directly to PDF. Depending on the file type, you can use different methods: Common documents (Word, Excel, PowerPoint): Use Microsoft Office, LibreOffice and other software to export as PDF. Image: Save as PDF using image viewer or image processing software. Web pages: Use the browser's "Print into PDF" function or the dedicated web page to PDF tool. Uncommon formats: Find the right converter and convert it to PDF. It is crucial to choose the right tools and develop a plan based on the actual situation.
 How does the Java reflection mechanism modify the behavior of a class?
May 03, 2024 pm 06:15 PM
How does the Java reflection mechanism modify the behavior of a class?
May 03, 2024 pm 06:15 PM
The Java reflection mechanism allows programs to dynamically modify the behavior of classes without modifying the source code. By operating the Class object, you can create instances through newInstance(), modify private field values, call private methods, etc. Reflection should be used with caution, however, as it can cause unexpected behavior and security issues, and has a performance overhead.
 How to cross-domain iframe in vue
May 02, 2024 pm 10:48 PM
How to cross-domain iframe in vue
May 02, 2024 pm 10:48 PM
Ways to solve iframe cross-domain issues in Vue: CORS: Enable CORS support in the backend server and use XMLHttpRequest or fetch API to send CORS requests in Vue. JSONP: Dynamically load JSONP scripts in Vue using the JSONP endpoint in the backend server. Proxy server: Set up a proxy server to forward requests, use a third-party library (such as axios) in Vue to send requests and set the proxy server URL.
 Common exception types and their repair measures in Java function development
May 03, 2024 pm 02:09 PM
Common exception types and their repair measures in Java function development
May 03, 2024 pm 02:09 PM
Common exception types and their repair measures in Java function development During the development of Java functions, various exceptions may be encountered, which affect the correct execution of the function. The following are common exception types and their repair measures: 1. NullPointerException Description: Thrown when accessing an object that has not been initialized. Fix: Make sure you check the object for non-null before using it. Sample code: try{Stringname=null;System.out.println(name.length());}catch(NullPointerExceptione){
 How to read dbf file in oracle
May 10, 2024 am 01:27 AM
How to read dbf file in oracle
May 10, 2024 am 01:27 AM
Oracle can read dbf files through the following steps: create an external table and reference the dbf file; query the external table to retrieve data; import the data into the Oracle table.
 How to use Fail2Ban to protect your server from brute force attacks
Apr 27, 2024 am 08:34 AM
How to use Fail2Ban to protect your server from brute force attacks
Apr 27, 2024 am 08:34 AM
An important task for Linux administrators is to protect the server from illegal attacks or access. By default, Linux systems come with well-configured firewalls, such as iptables, Uncomplicated Firewall (UFW), ConfigServerSecurityFirewall (CSF), etc., which can prevent a variety of attacks. Any machine connected to the Internet is a potential target for malicious attacks. There is a tool called Fail2Ban that can be used to mitigate illegal access on the server. What is Fail2Ban? Fail2Ban[1] is an intrusion prevention software that protects servers from brute force attacks. It is written in Python programming language
 How to use explain in oracle
May 03, 2024 am 12:06 AM
How to use explain in oracle
May 03, 2024 am 12:06 AM
The EXPLAIN command in Oracle is used to analyze the execution plan of a SQL statement. The method of use is to add the EXPLAIN keyword before the SQL statement. EXPLAIN results contain information such as ID, operator type, row count estimate, cost estimate, output row count estimate, access predicates, and filter predicates, which can be used to optimize query performance, identify costly operators, and tables that may benefit from optimization techniques.






