数据库中的数据模型
我学数据库(3)--数据库中的数据模型 本次随笔和随笔(4)、随笔(5)和随笔(6)主要是详细的了解了一下数据模型的相关知识,因为这是数据库系统的核心与基础,所以必须对数据模型有一个清楚的认识,数据模型呢本来就是抽象出来的,所以呢这里面都是些概念的
我学数据库(3)--数据库中的数据模型
本次随笔和随笔(4)、随笔(5)和随笔(6)主要是详细的了解了一下数据模型的相关知识,因为这是数据库系统的核心与基础,所以必须对数据模型有一个清楚的认识,数据模型呢本来就是抽象出来的,所以呢这里面都是些概念的东西,可能有些难以理解,但是也没有办法,既然想学习这门“艺术”,就必须了解这些,而且必须有深刻的认识。不多说了,转入正题吧,开始数据模型的学习 ,fighting!
数据模型,一个是数据一个是模型,所以得先对这两个名词进行了解。
数据是记录信息的按一定规则排列组合的物理符号。可以是数字、文字、图像,也可以是计算机代码。对信息的接收始于对数据的接收,对信息的获取只能通过对数据背景的解读。
模型,像飞机模型等具体模型,对我们来说再熟悉不过了。因为这些我们都见过真实的事物。模型是现实世界中某个对象特征的模拟和抽象,是用以分析问题的概念、数学关系、逻辑关系和算法序列的表示体系。
综上,数据模型(Data Model)是数据特征的抽象,用来分析数据问题的概念、数据之间的各种关系的表示体系,也就是说,是用来描述数据、组织数据和对数据进行操作的。选择一个数据模型不是那么的随便,不能随便的对某数据进行抽象后就拿来当模型,数据模型必须满足一定的要求才行:一是能比较真实的模拟现实世界,这里用的比较一词来形容,是因为模型就是模型,不可能完全真实的模拟世界;而是容易被人们理解才行,晦涩难懂,那就失去了抽象的意义;三是便于在计算机上实现,这一个条件我是这样理解的,如果让人脑去实现,恐怕得是爱因斯坦或者霍金那样的才行啊,人脑毕竟是受限的,这个层次上电脑要比人脑好使多了。但问题又出现了,什么数据模型能很好的全面的满足这三个条件呢?答案是现在还没有,也就是说,这个地方的数据模型可能在那个地方不再适用。所以必须针对不同的对象和应用,也只能采用不同的数据模型去满足要求。在数据库系统中也是这样做的,即在开发实施数据库应用系统的不同阶段使用不同的数据模型:概念模型、逻辑模型和物理模型。其实是首先描述是什么,紧接着是如何表示,最后就是如何实现了。说白了就是发现问题,香港空间,分析问题和解决问题的这么一个过程。
在描述问题的过程中用的是概念数据模型,也叫信息模型,这是面向数据库用户的实现世界的数据模型,主要用来描述世界的概念化结构,它使数据库的设计人员在设计的初始阶段,摆脱计算机系统及DBMS的具体技术问题,集中精力分析数据以及数据之间的联系等,与具体的DBMS无关。此模型是面向现实世界中的真实需求,这个模型构造的是否成功直接决定了相应的数据库应用系统的成败与否。
在如何表示的过程中用的是逻辑数据模型,这是用户从数据库看到的数据模型,是具体的DBMS所支持的数据模型,网站空间,如网状数据模型、层次数据模型、关系模型、面向对象模型和对象关系模型等。此模型既要面向用户,又要面向系统。之所以说面向用户是因为逻辑模型是由概念模型直接转换而来,在转换的过程中还会有更深层次的问题暴露出来,而这些问题是要回归到概念模型再次讨论;之所以面向系统,在前面说了,既然是模型了就要容易被计算机实现,而此模型就是在计算机系统的观点上对数据建模的,主要用于DBMS的实现。
在实现的过程中使用的是物理数据模型,这是描述数据在存储介质上的组织结构的数据模型它不但与具体的DBMS有关,而且还和操作系统以及硬件有关。每一种逻辑数据模型在实现时都有其对应的物理数据模型。DBMS为了保证其独立性与可移植性,大部分物理数据模型的实现工作由系统自动完成,而设计者只设计索引、聚集等特殊结构。此模型纯粹的面向系统的,从计算机的角度来,从最低层次对数据进行抽象。
接下来了解一下数据模型的共性。一般而言,数据模型是一组严格定义的概念的集合。这些概念精确地描述了系统的静态特征(数据结构)、动态特征(数据操作)和完整性约束条件,这就是数据模型的三要素,即数据模型的共性。
数据结构是所研究的对象类型的集合。这些对象是数据库的组成部分,数据结构指对象和对象间联系的表达和实现,是系统静态特征的描述,包括两个方面:一方面是关于数据对象本身的,比如类型、内容、性质;一方面是关于数据之间的联系,服务器空间,关于数据之间是如何相互联系的。
数据操作是对数据库中对象的实例允许执行的操作集合,主要指检索和更新(插入、删除、修改)两类操作。数据模型必须定义这些操作的确切含义、操作符号、操作规则(如优先级)以及实现操作的语言。数据操作是对系统动态特征的描述。
数据完整性约束是一组完整性规则的集合,规定数据库状态及状态变化所应满足的条件,以保证数据的正确性、有效性和相容性。原先也提过为什么文件系统已不能再满足与日递增的要求,其中一条原因就是因为文件系统不能给出完整性规则约束,这也是文件系统不能保证数据的正确性、有效性和一致性的本质原因。
在下一次呢,讨论一下数据模型中的概念模型。
posted on
Powered by:
博客园
Copyright © 满天海晨星

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
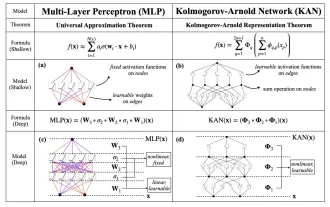 KAN, which replaces MLP, has been extended to convolution by open source projects
Jun 01, 2024 pm 10:03 PM
KAN, which replaces MLP, has been extended to convolution by open source projects
Jun 01, 2024 pm 10:03 PM
Earlier this month, researchers from MIT and other institutions proposed a very promising alternative to MLP - KAN. KAN outperforms MLP in terms of accuracy and interpretability. And it can outperform MLP running with a larger number of parameters with a very small number of parameters. For example, the authors stated that they used KAN to reproduce DeepMind's results with a smaller network and a higher degree of automation. Specifically, DeepMind's MLP has about 300,000 parameters, while KAN only has about 200 parameters. KAN has a strong mathematical foundation like MLP. MLP is based on the universal approximation theorem, while KAN is based on the Kolmogorov-Arnold representation theorem. As shown in the figure below, KAN has
 Comprehensively surpassing DPO: Chen Danqi's team proposed simple preference optimization SimPO, and also refined the strongest 8B open source model
Jun 01, 2024 pm 04:41 PM
Comprehensively surpassing DPO: Chen Danqi's team proposed simple preference optimization SimPO, and also refined the strongest 8B open source model
Jun 01, 2024 pm 04:41 PM
In order to align large language models (LLMs) with human values and intentions, it is critical to learn human feedback to ensure that they are useful, honest, and harmless. In terms of aligning LLM, an effective method is reinforcement learning based on human feedback (RLHF). Although the results of the RLHF method are excellent, there are some optimization challenges involved. This involves training a reward model and then optimizing a policy model to maximize that reward. Recently, some researchers have explored simpler offline algorithms, one of which is direct preference optimization (DPO). DPO learns the policy model directly based on preference data by parameterizing the reward function in RLHF, thus eliminating the need for an explicit reward model. This method is simple and stable
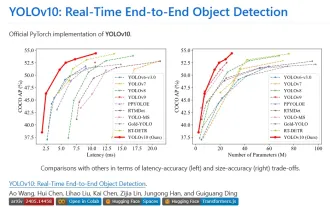 Yolov10: Detailed explanation, deployment and application all in one place!
Jun 07, 2024 pm 12:05 PM
Yolov10: Detailed explanation, deployment and application all in one place!
Jun 07, 2024 pm 12:05 PM
1. Introduction Over the past few years, YOLOs have become the dominant paradigm in the field of real-time object detection due to its effective balance between computational cost and detection performance. Researchers have explored YOLO's architectural design, optimization goals, data expansion strategies, etc., and have made significant progress. At the same time, relying on non-maximum suppression (NMS) for post-processing hinders end-to-end deployment of YOLO and adversely affects inference latency. In YOLOs, the design of various components lacks comprehensive and thorough inspection, resulting in significant computational redundancy and limiting the capabilities of the model. It offers suboptimal efficiency, and relatively large potential for performance improvement. In this work, the goal is to further improve the performance efficiency boundary of YOLO from both post-processing and model architecture. to this end
 No OpenAI data required, join the list of large code models! UIUC releases StarCoder-15B-Instruct
Jun 13, 2024 pm 01:59 PM
No OpenAI data required, join the list of large code models! UIUC releases StarCoder-15B-Instruct
Jun 13, 2024 pm 01:59 PM
At the forefront of software technology, UIUC Zhang Lingming's group, together with researchers from the BigCode organization, recently announced the StarCoder2-15B-Instruct large code model. This innovative achievement achieved a significant breakthrough in code generation tasks, successfully surpassing CodeLlama-70B-Instruct and reaching the top of the code generation performance list. The unique feature of StarCoder2-15B-Instruct is its pure self-alignment strategy. The entire training process is open, transparent, and completely autonomous and controllable. The model generates thousands of instructions via StarCoder2-15B in response to fine-tuning the StarCoder-15B base model without relying on expensive manual annotation.
 Tsinghua University took over and YOLOv10 came out: the performance was greatly improved and it was on the GitHub hot list
Jun 06, 2024 pm 12:20 PM
Tsinghua University took over and YOLOv10 came out: the performance was greatly improved and it was on the GitHub hot list
Jun 06, 2024 pm 12:20 PM
The benchmark YOLO series of target detection systems has once again received a major upgrade. Since the release of YOLOv9 in February this year, the baton of the YOLO (YouOnlyLookOnce) series has been passed to the hands of researchers at Tsinghua University. Last weekend, the news of the launch of YOLOv10 attracted the attention of the AI community. It is considered a breakthrough framework in the field of computer vision and is known for its real-time end-to-end object detection capabilities, continuing the legacy of the YOLO series by providing a powerful solution that combines efficiency and accuracy. Paper address: https://arxiv.org/pdf/2405.14458 Project address: https://github.com/THU-MIG/yo
 Li Feifei reveals the entrepreneurial direction of 'spatial intelligence': visualization turns into insight, seeing becomes understanding, and understanding leads to action
Jun 01, 2024 pm 02:55 PM
Li Feifei reveals the entrepreneurial direction of 'spatial intelligence': visualization turns into insight, seeing becomes understanding, and understanding leads to action
Jun 01, 2024 pm 02:55 PM
After Stanford's Feifei Li started his business, he unveiled the new concept "spatial intelligence" for the first time. This is not only her entrepreneurial direction, but also the "North Star" that guides her. She considers it "the key puzzle piece to solve the artificial intelligence problem." Visualization leads to insight; seeing leads to understanding; understanding leads to action. Based on Li Feifei's 15-minute TED talk, which is fully open to the public, it starts from the origin of life evolution hundreds of millions of years ago, to how humans are not satisfied with what nature has given them and develops artificial intelligence, to how to build spatial intelligence in the next step. Nine years ago, Li Feifei introduced the newly born ImageNet to the world on the same stage - one of the starting points for this round of deep learning explosion. She herself also encouraged netizens: If you watch both videos, you will be able to understand the computer vision of the past 10 years.
 70B model generates 1,000 tokens in seconds, code rewriting surpasses GPT-4o, from the Cursor team, a code artifact invested by OpenAI
Jun 13, 2024 pm 03:47 PM
70B model generates 1,000 tokens in seconds, code rewriting surpasses GPT-4o, from the Cursor team, a code artifact invested by OpenAI
Jun 13, 2024 pm 03:47 PM
70B model, 1000 tokens can be generated in seconds, which translates into nearly 4000 characters! The researchers fine-tuned Llama3 and introduced an acceleration algorithm. Compared with the native version, the speed is 13 times faster! Not only is it fast, its performance on code rewriting tasks even surpasses GPT-4o. This achievement comes from anysphere, the team behind the popular AI programming artifact Cursor, and OpenAI also participated in the investment. You must know that on Groq, a well-known fast inference acceleration framework, the inference speed of 70BLlama3 is only more than 300 tokens per second. With the speed of Cursor, it can be said that it achieves near-instant complete code file editing. Some people call it a good guy, if you put Curs
 AI startups collectively switched jobs to OpenAI, and the security team regrouped after Ilya left!
Jun 08, 2024 pm 01:00 PM
AI startups collectively switched jobs to OpenAI, and the security team regrouped after Ilya left!
Jun 08, 2024 pm 01:00 PM
Last week, amid the internal wave of resignations and external criticism, OpenAI was plagued by internal and external troubles: - The infringement of the widow sister sparked global heated discussions - Employees signing "overlord clauses" were exposed one after another - Netizens listed Ultraman's "seven deadly sins" Rumors refuting: According to leaked information and documents obtained by Vox, OpenAI’s senior leadership, including Altman, was well aware of these equity recovery provisions and signed off on them. In addition, there is a serious and urgent issue facing OpenAI - AI safety. The recent departures of five security-related employees, including two of its most prominent employees, and the dissolution of the "Super Alignment" team have once again put OpenAI's security issues in the spotlight. Fortune magazine reported that OpenA






