SqlServer2008基础知识:安全与权限
这两天在调用Microsoft.SqlServer.SMO.dll组件 《add login,create,backup,restore database to Sql Server using SMO》,接触到一些数据库的名词定义: 登录名,用户,角色,架构,权限 ,部分新人对几个名词的概念不是很清晰 所以参考部分文档,摘录如下(权当
这两天在调用Microsoft.SqlServer.SMO.dll组件 《add login,create,backup,restore database to Sql Server using SMO》,接触到一些数据库的名词定义:登录名,用户,角色,架构,权限,部分新人对几个名词的概念不是很清晰 所以参考部分文档,摘录如下(权当温故⑧^_^):
SqlServer2008的安全机制分为四个级别:
1.操作系统的安全性
创建操作系统用户账号(win7):

2.数据库服务器的登录安全性【下面两种验证模式下登录所使用的用户名,即为:登录名定义。】
数据库服务器登录模式分为:
①Windows身份验证模式(如下图)

用户名即是:当前Windows操作系统中的用户账户,我这里是用的管理员账号(计算机名),如果系统账户有登录密码 可以相应的输入
登录成功后,设置SqlServer 验证模式如图:


②混合身份验证模式(Windows身份验证模式&SqlServer身份验证模式[前者安全性比后者高]),如下图:

在安装SQLServer2008时 会默认生成一个登录名:sa,其隶属于服务器角色:sysadmin。
而新创建的登录名,则会自动关联服务器角色:public,除了默认的数据库:master,美国服务器,其他的数据都将没有访问权限,如果想要访问其他数据库:
1.则需要在登录名-新建-用户映射里面勾选相应的数据库:则相应的数据库会自动创建一个同名(登录名)数据库用户账号
(注①:master数据库不勾选也是默认访问的 数据库用户里是没有同名账号。)
(注②:当登录名要删除之前 要先手动删除由登录名映射数据库而生成的用户)
2.或者在登录名-新建-服务器角色 中直接勾选sysadmin这样就可以访问所有的数据库(或在服务器角色sysadmin-右击属性-添加-登录名)了:修改服务器角色为 sysadmin 不会在数据库用户里创建同名账号。
以下是数据库服务器的角色列表以及其对应所拥有的操作权限,如下图:


3.数据库的使用安全性
登录名 只能登录进SqlServer服务器,并不能让访问服务器中的数据库,而使用登录名登录进数据库服务器后想要访问特定的数据库 还必须具有数据库用户名,用户名在特定的数据库内创建,并必须关联一个登录名,通过授权给该用户指定可以访问的数据库对象的权限
数据库用户可以新建或者由登录名映射数据库而生成。注:无论是新建的数据库用户 还是由登录名映射数据库生成的数据库用户 都要遵循 数据库用户1:1登录名的规则
创建数据库用户时 需要关联登录名;创建数据库角色是 需要关联使用者 一般选择dbo; dbo(DataBase Owner)是数据库的所有者,拥有数据库中的所有对象,每个数据库都有dbo,sysadmin服务器角色的成员自动映射成dbo,无法删除dbo,且此用户始终出现在每个数据库中。通常 登录名sa映射为数据库用户dbo.
数据库用户的生成需要关联数据库角色:数据库角色有三种:固定数据库角色,用户定义数据库角色,应用程序角色,如下图:

4.数据库对象的使用安全性
我们一般将表,视图,存储过程,函数 统称为数据库对象,而数据库对象包含在架构中,而给角色划分权限也就是开放架构中部分或者全部的对象做相应的执行权限操作,
数据库对象的常用权限 如下图:

权限操作分为三种:授予,拒绝,撤销,语法及代码如下
权限操作
students ,inster, stu 8 to students_msg students , stu students stu stu 29 to guest ,美国服务器,美国服务器

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
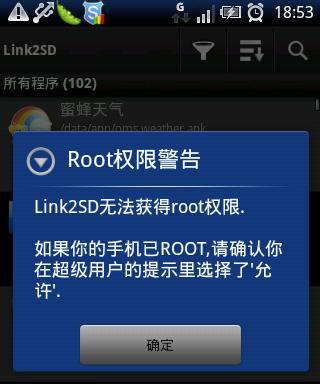 Enable root permissions with one click (quickly obtain root permissions)
Jun 02, 2024 pm 05:32 PM
Enable root permissions with one click (quickly obtain root permissions)
Jun 02, 2024 pm 05:32 PM
It allows users to perform more in-depth operations and customization of the system. Root permission is an administrator permission in the Android system. Obtaining root privileges usually requires a series of tedious steps, which may not be very friendly to ordinary users, however. By enabling root permissions with one click, this article will introduce a simple and effective method to help users easily obtain system permissions. Understand the importance and risks of root permissions and have greater freedom. Root permissions allow users to fully control the mobile phone system. Strengthen security controls, customize themes, and users can delete pre-installed applications. For example, accidentally deleting system files causing system crashes, excessive use of root privileges, and inadvertent installation of malware are also risky, however. Before using root privileges
 Detailed explanation of how to turn off Windows 11 Security Center
Mar 27, 2024 pm 03:27 PM
Detailed explanation of how to turn off Windows 11 Security Center
Mar 27, 2024 pm 03:27 PM
In the Windows 11 operating system, the Security Center is an important function that helps users monitor the system security status, defend against malware, and protect personal privacy. However, sometimes users may need to temporarily turn off Security Center, such as when installing certain software or performing system tuning. This article will introduce in detail how to turn off the Windows 11 Security Center to help you operate the system correctly and safely. 1. How to turn off Windows 11 Security Center In Windows 11, turning off the Security Center does not
 How should the Java framework security architecture design be balanced with business needs?
Jun 04, 2024 pm 02:53 PM
How should the Java framework security architecture design be balanced with business needs?
Jun 04, 2024 pm 02:53 PM
Java framework design enables security by balancing security needs with business needs: identifying key business needs and prioritizing relevant security requirements. Develop flexible security strategies, respond to threats in layers, and make regular adjustments. Consider architectural flexibility, support business evolution, and abstract security functions. Prioritize efficiency and availability, optimize security measures, and improve visibility.
 AI's new world challenges: What happened to security and privacy?
Mar 31, 2024 pm 06:46 PM
AI's new world challenges: What happened to security and privacy?
Mar 31, 2024 pm 06:46 PM
The rapid development of generative AI has created unprecedented challenges in privacy and security, triggering urgent calls for regulatory intervention. Last week, I had the opportunity to discuss the security-related impacts of AI with some members of Congress and their staff in Washington, D.C. Today's generative AI reminds me of the Internet in the late 1980s, with basic research, latent potential, and academic uses, but it's not yet ready for the public. This time, unchecked vendor ambition, fueled by minor league venture capital and inspired by Twitter echo chambers, is rapidly advancing AI’s “brave new world.” The "public" base model is flawed and unsuitable for consumer and commercial use; privacy abstractions, if present, leak like a sieve; security structures are important because of the attack surface
 How to implement PHP security best practices
May 05, 2024 am 10:51 AM
How to implement PHP security best practices
May 05, 2024 am 10:51 AM
How to Implement PHP Security Best Practices PHP is one of the most popular backend web programming languages used for creating dynamic and interactive websites. However, PHP code can be vulnerable to various security vulnerabilities. Implementing security best practices is critical to protecting your web applications from these threats. Input validation Input validation is a critical first step in validating user input and preventing malicious input such as SQL injection. PHP provides a variety of input validation functions, such as filter_var() and preg_match(). Example: $username=filter_var($_POST['username'],FILTER_SANIT
 Security configuration and hardening of Struts 2 framework
May 31, 2024 pm 10:53 PM
Security configuration and hardening of Struts 2 framework
May 31, 2024 pm 10:53 PM
To protect your Struts2 application, you can use the following security configurations: Disable unused features Enable content type checking Validate input Enable security tokens Prevent CSRF attacks Use RBAC to restrict role-based access
 Implementing Machine Learning Algorithms in C++: Security Considerations and Best Practices
Jun 01, 2024 am 09:26 AM
Implementing Machine Learning Algorithms in C++: Security Considerations and Best Practices
Jun 01, 2024 am 09:26 AM
When implementing machine learning algorithms in C++, security considerations are critical, including data privacy, model tampering, and input validation. Best practices include adopting secure libraries, minimizing permissions, using sandboxes, and continuous monitoring. The practical case demonstrates the use of the Botan library to encrypt and decrypt the CNN model to ensure safe training and prediction.
 Tips for turning off real-time protection in Windows Security Center
Mar 27, 2024 pm 10:09 PM
Tips for turning off real-time protection in Windows Security Center
Mar 27, 2024 pm 10:09 PM
In today's digital society, computers have become an indispensable part of our lives. As one of the most popular operating systems, Windows is widely used around the world. However, as network attack methods continue to escalate, protecting personal computer security has become particularly important. The Windows operating system provides a series of security functions, of which "Windows Security Center" is one of its important components. In Windows systems, "Windows Security Center" can help us






