 Java
Java
 javaTutorial
javaTutorial
 How does the Java framework security architecture design adapt to changing security threats?
How does the Java framework security architecture design adapt to changing security threats?
How does the Java framework security architecture design adapt to changing security threats?
The Java framework can be used to build a dynamic security architecture to respond to changing security threats. Adherence to principles include multi-layered defense, continuous monitoring, resiliency and zero trust. Recommended frameworks are Spring Security, OWASP Java ESAPI, and Apache Shiro. Practical cases show how Spring Security implements multi-layer defense. Continuous monitoring and response require logging tools and event handling libraries. Through these measures, enterprises can create an adaptable security architecture that protects them from ever-changing threats.
Use Java framework to implement dynamic security architecture to deal with changing security threats
Introduction
As the cyber threat landscape continues to evolve, enterprises need to adopt adaptable security strategies to effectively respond to growing security risks. This article explores how to use a Java framework to design and implement a dynamic security architecture to provide enterprises with comprehensive protection against ever-changing security threats.
Security Architecture Principles
When designing a security architecture, the following principles should be followed:
- Multi-layer defense: Implement multiple A layered defense mechanism creates multiple security layers to prevent a single failure from causing a security breach.
- Continuous Monitoring: Monitor security events and take prompt action when suspicious activity occurs.
- Resilience and Responsiveness: The architecture should be able to adapt to changes in the threat environment and respond quickly to security incidents.
- Zero Trust: Assume everything in your network is a potential threat and always authenticate visitors and resources.
Java Framework Selection
To build a dynamic security architecture, it is recommended to use a mature Java framework. Here are some popular choices:
- Spring Security: A security framework that handles authentication, authorization, and securing web applications.
- OWASP Java Enterprise Security API (ESAPI): Provides a set of tools and libraries for dealing with common web application security threats.
- Apache Shiro: Lightweight security framework focusing on authentication and authorization.
Practical case: Spring Security implements multi-layer defense
Spring Security provides a variety of multi-layer defense mechanisms, including:
// 配置基础身份验证
SecurityConfigurerAdapter securityConfigurerAdapter = new SecurityConfigurerAdapter() {
@Override
public void configure(HttpSecurity http) throws Exception {
http
.authorizeRequests()
.anyRequest().authenticated()
.and().formLogin();
}
};// 添加基于角色的授权
RoleHierarchyConfigurer roleHierarchyConfigurer = new RoleHierarchyConfigurer() {
@Override
public void configure(HttpSecurity http) throws Exception {
http.authorizeRequests()
.expressionHandler(new DefaultWebSecurityExpressionHandler())
.accessDeniedPage("/403");
}
};// 实现 CSRF 保护 CsrfConfigurer csrfConfigurer = new CsrfConfigurer(); http.addFilterAfter(csrfConfigurer.csrfTokenRepository(CookieCsrfTokenRepository.withHttpOnlyFalse()), SecurityContextPersistenceFilter.class);
Continuous monitoring and response
To achieve continuous monitoring, logging and monitoring tools such as Apache Log4j or ElasticSearch can be integrated. These tools can be used to collect security event data and generate alerts.
For fast response, you can use a Java event handling library such as EventBus to quickly propagate events and trigger appropriate security measures.
Conclusion
By using Java frameworks and following these design principles, enterprises can build dynamic security architectures that respond to ever-changing security threats. Multiple layers of defense, continuous monitoring and resilient response capabilities are critical to keeping your business secure.
The above is the detailed content of How does the Java framework security architecture design adapt to changing security threats?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1382
1382
 52
52
 Perfect Number in Java
Aug 30, 2024 pm 04:28 PM
Perfect Number in Java
Aug 30, 2024 pm 04:28 PM
Guide to Perfect Number in Java. Here we discuss the Definition, How to check Perfect number in Java?, examples with code implementation.
 Weka in Java
Aug 30, 2024 pm 04:28 PM
Weka in Java
Aug 30, 2024 pm 04:28 PM
Guide to Weka in Java. Here we discuss the Introduction, how to use weka java, the type of platform, and advantages with examples.
 Smith Number in Java
Aug 30, 2024 pm 04:28 PM
Smith Number in Java
Aug 30, 2024 pm 04:28 PM
Guide to Smith Number in Java. Here we discuss the Definition, How to check smith number in Java? example with code implementation.
 Java Spring Interview Questions
Aug 30, 2024 pm 04:29 PM
Java Spring Interview Questions
Aug 30, 2024 pm 04:29 PM
In this article, we have kept the most asked Java Spring Interview Questions with their detailed answers. So that you can crack the interview.
 Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Java 8 introduces the Stream API, providing a powerful and expressive way to process data collections. However, a common question when using Stream is: How to break or return from a forEach operation? Traditional loops allow for early interruption or return, but Stream's forEach method does not directly support this method. This article will explain the reasons and explore alternative methods for implementing premature termination in Stream processing systems. Further reading: Java Stream API improvements Understand Stream forEach The forEach method is a terminal operation that performs one operation on each element in the Stream. Its design intention is
 TimeStamp to Date in Java
Aug 30, 2024 pm 04:28 PM
TimeStamp to Date in Java
Aug 30, 2024 pm 04:28 PM
Guide to TimeStamp to Date in Java. Here we also discuss the introduction and how to convert timestamp to date in java along with examples.
 Java Program to Find the Volume of Capsule
Feb 07, 2025 am 11:37 AM
Java Program to Find the Volume of Capsule
Feb 07, 2025 am 11:37 AM
Capsules are three-dimensional geometric figures, composed of a cylinder and a hemisphere at both ends. The volume of the capsule can be calculated by adding the volume of the cylinder and the volume of the hemisphere at both ends. This tutorial will discuss how to calculate the volume of a given capsule in Java using different methods. Capsule volume formula The formula for capsule volume is as follows: Capsule volume = Cylindrical volume Volume Two hemisphere volume in, r: The radius of the hemisphere. h: The height of the cylinder (excluding the hemisphere). Example 1 enter Radius = 5 units Height = 10 units Output Volume = 1570.8 cubic units explain Calculate volume using formula: Volume = π × r2 × h (4
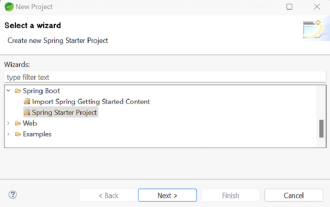 How to Run Your First Spring Boot Application in Spring Tool Suite?
Feb 07, 2025 pm 12:11 PM
How to Run Your First Spring Boot Application in Spring Tool Suite?
Feb 07, 2025 pm 12:11 PM
Spring Boot simplifies the creation of robust, scalable, and production-ready Java applications, revolutionizing Java development. Its "convention over configuration" approach, inherent to the Spring ecosystem, minimizes manual setup, allo



