Protecting Your JavaScript Applications from DOM-based XSS Attacks

Cross-site scripting (XSS) attacks are a common vulnerability in web applications, and one of the most dangerous types is DOM-based XSS. This form of XSS occurs when the Document Object Model (DOM) of a web page is manipulated to execute malicious scripts. In this blog, we'll explore DOM-based XSS, how it works, and how you can protect your applications from these attacks with real-world example code.
What is DOM-based XSS?
DOM-based XSS is a type of XSS attack where the vulnerability lies in the client-side code rather than the server-side code. It occurs when a web application uses data from an untrusted source, such as user input, and writes it to the DOM without proper validation or escaping. This can lead to the execution of malicious scripts within the context of the web page, allowing attackers to steal data, hijack sessions, and more.
How DOM-based XSS Works
Let's break down a simple scenario to understand how an attacker could exploit DOM-based XSS:
Vulnerable Web Application Example
Consider a simple web page that displays a greeting message using user input from the URL hash.
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>DOM-based XSS Example</title>
</head>
<body>
<div id="message"></div>
<script>
// Assume user input is taken from the URL hash
var userInput = window.location.hash.substring(1);
// Directly inserting user input into the DOM
document.getElementById('message').innerHTML = "Hello, " + userInput + "!";
</script>
</body>
</html>
How an Attacker Exploits the Vulnerability
1. Crafting a Malicious URL: An attacker can craft a URL that includes malicious JavaScript code in the URL hash. For example:
https://xyz.com/#<script>alert('XSS');</script>
2. Sharing the Malicious URL: The attacker shares this URL with potential victims, who might click on it without suspicion. The attacker can distribute this link via email, social media, or any other means.
3. Exploiting the Vulnerability: When a victim visits the malicious URL, the web application extracts the value from the URL hash and inserts it into the DOM. The malicious script executes in the context of the web page.
Result: The victim sees an alert box with the message 'XSS', indicating that the script has executed. In a real attack, the malicious script could perform actions like stealing cookies, capturing keystrokes, or redirecting the user to a phishing site.
<script>
// User visits: https://xyz.com/#<script>alert('XSS');</script>
var userInput = window.location.hash.substring(1);
document.getElementById('message').innerHTML = "Hello, " + userInput + "!";
// This results in: Hello, <script>alert('XSS');</script>!
// The alert will pop up
Preventing DOM-based XSS
To protect against DOM-based XSS, follow these best practices:
1. Sanitize and Escape User Input: Always sanitize and escape any user input before inserting it into the DOM. Use libraries like DOMPurify to sanitize HTML.
<script src="https://cdnjs.cloudflare.com/ajax/libs/dompurify/2.2.8/purify.min.js"></script>
<script>
var userInput = window.location.hash.substring(1);
// Sanitize the user input
var sanitizedInput = DOMPurify.sanitize(userInput);
// Insert sanitized input into the DOM
document.getElementById('message').innerHTML = "Hello, " + sanitizedInput + "!";
</script>
2. Use Safe DOM Manipulation Methods: Instead of using innerHTML, use safer methods like textContent or createElement and appendChild.
<script>
var userInput = window.location.hash.substring(1);
var messageDiv = document.getElementById('message');
// Create a text node with the user input
var textNode = document.createTextNode("Hello, " + userInput + "!");
// Append the text node to the message div
messageDiv.appendChild(textNode);
</script>
3. Content Security Policy (CSP): Implement a strong CSP to restrict the sources from which scripts can be loaded and executed.
<meta http-equiv="Content-Security-Policy" content="default-src 'self'; script-src 'self';">
DOM-based XSS is a critical security risk that can compromise your web application and user data. By following best practices such as sanitizing and escaping user input, using safe DOM manipulation methods, and implementing a robust Content Security Policy, you can significantly reduce the risk of DOM-based XSS attacks.
Stay vigilant and ensure your JavaScript applications are secure from these and other vulnerabilities. If you have any questions or need further assistance, feel free to reach out in the comments below.
The above is the detailed content of Protecting Your JavaScript Applications from DOM-based XSS Attacks. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1663
1663
 14
14
 1420
1420
 52
52
 1315
1315
 25
25
 1266
1266
 29
29
 1239
1239
 24
24
 Demystifying JavaScript: What It Does and Why It Matters
Apr 09, 2025 am 12:07 AM
Demystifying JavaScript: What It Does and Why It Matters
Apr 09, 2025 am 12:07 AM
JavaScript is the cornerstone of modern web development, and its main functions include event-driven programming, dynamic content generation and asynchronous programming. 1) Event-driven programming allows web pages to change dynamically according to user operations. 2) Dynamic content generation allows page content to be adjusted according to conditions. 3) Asynchronous programming ensures that the user interface is not blocked. JavaScript is widely used in web interaction, single-page application and server-side development, greatly improving the flexibility of user experience and cross-platform development.
 The Evolution of JavaScript: Current Trends and Future Prospects
Apr 10, 2025 am 09:33 AM
The Evolution of JavaScript: Current Trends and Future Prospects
Apr 10, 2025 am 09:33 AM
The latest trends in JavaScript include the rise of TypeScript, the popularity of modern frameworks and libraries, and the application of WebAssembly. Future prospects cover more powerful type systems, the development of server-side JavaScript, the expansion of artificial intelligence and machine learning, and the potential of IoT and edge computing.
 JavaScript Engines: Comparing Implementations
Apr 13, 2025 am 12:05 AM
JavaScript Engines: Comparing Implementations
Apr 13, 2025 am 12:05 AM
Different JavaScript engines have different effects when parsing and executing JavaScript code, because the implementation principles and optimization strategies of each engine differ. 1. Lexical analysis: convert source code into lexical unit. 2. Grammar analysis: Generate an abstract syntax tree. 3. Optimization and compilation: Generate machine code through the JIT compiler. 4. Execute: Run the machine code. V8 engine optimizes through instant compilation and hidden class, SpiderMonkey uses a type inference system, resulting in different performance performance on the same code.
 Python vs. JavaScript: The Learning Curve and Ease of Use
Apr 16, 2025 am 12:12 AM
Python vs. JavaScript: The Learning Curve and Ease of Use
Apr 16, 2025 am 12:12 AM
Python is more suitable for beginners, with a smooth learning curve and concise syntax; JavaScript is suitable for front-end development, with a steep learning curve and flexible syntax. 1. Python syntax is intuitive and suitable for data science and back-end development. 2. JavaScript is flexible and widely used in front-end and server-side programming.
 JavaScript: Exploring the Versatility of a Web Language
Apr 11, 2025 am 12:01 AM
JavaScript: Exploring the Versatility of a Web Language
Apr 11, 2025 am 12:01 AM
JavaScript is the core language of modern web development and is widely used for its diversity and flexibility. 1) Front-end development: build dynamic web pages and single-page applications through DOM operations and modern frameworks (such as React, Vue.js, Angular). 2) Server-side development: Node.js uses a non-blocking I/O model to handle high concurrency and real-time applications. 3) Mobile and desktop application development: cross-platform development is realized through ReactNative and Electron to improve development efficiency.
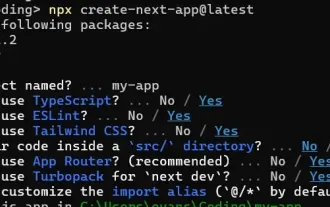 How to Build a Multi-Tenant SaaS Application with Next.js (Frontend Integration)
Apr 11, 2025 am 08:22 AM
How to Build a Multi-Tenant SaaS Application with Next.js (Frontend Integration)
Apr 11, 2025 am 08:22 AM
This article demonstrates frontend integration with a backend secured by Permit, building a functional EdTech SaaS application using Next.js. The frontend fetches user permissions to control UI visibility and ensures API requests adhere to role-base
 From C/C to JavaScript: How It All Works
Apr 14, 2025 am 12:05 AM
From C/C to JavaScript: How It All Works
Apr 14, 2025 am 12:05 AM
The shift from C/C to JavaScript requires adapting to dynamic typing, garbage collection and asynchronous programming. 1) C/C is a statically typed language that requires manual memory management, while JavaScript is dynamically typed and garbage collection is automatically processed. 2) C/C needs to be compiled into machine code, while JavaScript is an interpreted language. 3) JavaScript introduces concepts such as closures, prototype chains and Promise, which enhances flexibility and asynchronous programming capabilities.
 Building a Multi-Tenant SaaS Application with Next.js (Backend Integration)
Apr 11, 2025 am 08:23 AM
Building a Multi-Tenant SaaS Application with Next.js (Backend Integration)
Apr 11, 2025 am 08:23 AM
I built a functional multi-tenant SaaS application (an EdTech app) with your everyday tech tool and you can do the same. First, what’s a multi-tenant SaaS application? Multi-tenant SaaS applications let you serve multiple customers from a sing




