Introduction to Access Control Testing

Access Control Testing: Securing Your Systems and Data
In the digital age, ensuring that sensitive data and resources are only accessible to authorized users is a cornerstone of cybersecurity. Access control testing helps organizations maintain control over who can access what within their systems, protecting them from data breaches and unauthorized access.
What is Access Control?
Access control refers to the practice of restricting or granting permissions to users, systems, or processes to access resources based on predefined rules. It ensures that users can only access resources and perform actions permitted by their assigned privileges, providing a foundation for secure operations in IT environments.
Importance of Access Control Testing
Access control testing is essential for identifying and mitigating potential vulnerabilities that could lead to unauthorized access or data breaches. Without rigorous testing, organizations risk exposing sensitive data, violating compliance regulations, and compromising operational integrity.
Types of Access Control Mechanisms
- Discretionary Access Control (DAC): DAC allows the resource owner to decide who can access specific data or systems. For instance, a file owner can define access permissions for others.
- Mandatory Access Control (MAC): MAC enforces strict policies set by the organization, limiting user permissions based on security classifications. This approach is common in government and military environments.
- Role-Based Access Control (RBAC): RBAC assigns permissions based on user roles within the organization. For example, an HR manager may have access to employee records, while a developer does not.
- Attribute-Based Access Control (ABAC): ABAC grants access based on specific user attributes, such as location, time, or device type, providing a more dynamic approach to permissions.
Key Objectives of Access Control Testing
The primary aim of access control testing is to validate that only authorized users can access sensitive data and functionalities. Key objectives include:
- Validating Permissions: Ensuring users have appropriate access based on their roles and responsibilities.
- Identifying Unauthorized Access: Testing for scenarios where access is unintentionally granted to unauthorized users.
- Evaluating Access Revocation: Confirming that access permissions are properly revoked when no longer needed.
Common Methods for Access Control Testing
Access control testing involves a variety of methods to identify vulnerabilities and ensure compliance:
- Role Testing: Verifying that roles are configured correctly and permissions align with organizational policies.
- Privilege Escalation Testing: Testing whether users can escalate their privileges beyond their intended access.
- Session Management Testing: Ensuring that session timeouts, logout functionalities, and session security are robust.
- Multi-Factor Authentication (MFA) Testing: Testing the effectiveness and implementation of MFA mechanisms to strengthen security.
Tools for Access Control Testing
Various tools can assist in automating and streamlining access control testing processes:
- Burp Suite: A powerful tool for identifying vulnerabilities in web applications, including access control issues.
- OWASP ZAP: An open-source tool designed for web application security testing, including access controls.
- AccessChk: A Windows-specific tool for analyzing access control lists and permissions.
- Custom Scripts: Tailored scripts can be developed to test specific access control scenarios unique to your environment.
Best Practices for Access Control Testing
To ensure comprehensive and effective access control testing, follow these best practices:
- Regularly update and test access policies to adapt to evolving threats.
- Automate repetitive testing processes to maintain consistency and save time.
- Implement the principle of least privilege to minimize potential risks.
- Document all testing procedures and findings to ensure a clear record for audits and continuous improvement.
Challenges in Access Control Testing
Despite its importance, access control testing comes with its own set of challenges:
- Testing all possible scenarios can be complex and time-consuming.
- Ensuring compatibility with third-party tools and integrations adds layers of complexity.
- Managing access policies in dynamic environments, such as those using cloud or hybrid setups, requires constant vigilance.
Real-World Examples of Access Control Failures
Understanding real-world incidents highlights the importance of robust access control mechanisms:
- Example 1: A data breach occurred when misconfigured permissions allowed sensitive files to be publicly accessible.
- Example 2: Unauthorized access was gained through privilege escalation, where an attacker exploited vulnerabilities to gain admin-level access.
Conclusion
Access control testing is an indispensable part of securing applications and systems, ensuring that sensitive resources are safeguarded from unauthorized access. By understanding access control mechanisms, using effective testing methods, and adhering to best practices, organizations can build a robust defense against potential threats. Prioritizing access control testing today ensures a secure tomorrow.
The above is the detailed content of Introduction to Access Control Testing. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1664
1664
 14
14
 1423
1423
 52
52
 1317
1317
 25
25
 1268
1268
 29
29
 1246
1246
 24
24
 The Evolution of JavaScript: Current Trends and Future Prospects
Apr 10, 2025 am 09:33 AM
The Evolution of JavaScript: Current Trends and Future Prospects
Apr 10, 2025 am 09:33 AM
The latest trends in JavaScript include the rise of TypeScript, the popularity of modern frameworks and libraries, and the application of WebAssembly. Future prospects cover more powerful type systems, the development of server-side JavaScript, the expansion of artificial intelligence and machine learning, and the potential of IoT and edge computing.
 JavaScript Engines: Comparing Implementations
Apr 13, 2025 am 12:05 AM
JavaScript Engines: Comparing Implementations
Apr 13, 2025 am 12:05 AM
Different JavaScript engines have different effects when parsing and executing JavaScript code, because the implementation principles and optimization strategies of each engine differ. 1. Lexical analysis: convert source code into lexical unit. 2. Grammar analysis: Generate an abstract syntax tree. 3. Optimization and compilation: Generate machine code through the JIT compiler. 4. Execute: Run the machine code. V8 engine optimizes through instant compilation and hidden class, SpiderMonkey uses a type inference system, resulting in different performance performance on the same code.
 Python vs. JavaScript: The Learning Curve and Ease of Use
Apr 16, 2025 am 12:12 AM
Python vs. JavaScript: The Learning Curve and Ease of Use
Apr 16, 2025 am 12:12 AM
Python is more suitable for beginners, with a smooth learning curve and concise syntax; JavaScript is suitable for front-end development, with a steep learning curve and flexible syntax. 1. Python syntax is intuitive and suitable for data science and back-end development. 2. JavaScript is flexible and widely used in front-end and server-side programming.
 JavaScript: Exploring the Versatility of a Web Language
Apr 11, 2025 am 12:01 AM
JavaScript: Exploring the Versatility of a Web Language
Apr 11, 2025 am 12:01 AM
JavaScript is the core language of modern web development and is widely used for its diversity and flexibility. 1) Front-end development: build dynamic web pages and single-page applications through DOM operations and modern frameworks (such as React, Vue.js, Angular). 2) Server-side development: Node.js uses a non-blocking I/O model to handle high concurrency and real-time applications. 3) Mobile and desktop application development: cross-platform development is realized through ReactNative and Electron to improve development efficiency.
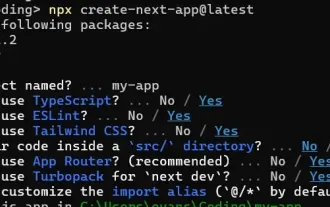 How to Build a Multi-Tenant SaaS Application with Next.js (Frontend Integration)
Apr 11, 2025 am 08:22 AM
How to Build a Multi-Tenant SaaS Application with Next.js (Frontend Integration)
Apr 11, 2025 am 08:22 AM
This article demonstrates frontend integration with a backend secured by Permit, building a functional EdTech SaaS application using Next.js. The frontend fetches user permissions to control UI visibility and ensures API requests adhere to role-base
 Building a Multi-Tenant SaaS Application with Next.js (Backend Integration)
Apr 11, 2025 am 08:23 AM
Building a Multi-Tenant SaaS Application with Next.js (Backend Integration)
Apr 11, 2025 am 08:23 AM
I built a functional multi-tenant SaaS application (an EdTech app) with your everyday tech tool and you can do the same. First, what’s a multi-tenant SaaS application? Multi-tenant SaaS applications let you serve multiple customers from a sing
 From C/C to JavaScript: How It All Works
Apr 14, 2025 am 12:05 AM
From C/C to JavaScript: How It All Works
Apr 14, 2025 am 12:05 AM
The shift from C/C to JavaScript requires adapting to dynamic typing, garbage collection and asynchronous programming. 1) C/C is a statically typed language that requires manual memory management, while JavaScript is dynamically typed and garbage collection is automatically processed. 2) C/C needs to be compiled into machine code, while JavaScript is an interpreted language. 3) JavaScript introduces concepts such as closures, prototype chains and Promise, which enhances flexibility and asynchronous programming capabilities.
 JavaScript and the Web: Core Functionality and Use Cases
Apr 18, 2025 am 12:19 AM
JavaScript and the Web: Core Functionality and Use Cases
Apr 18, 2025 am 12:19 AM
The main uses of JavaScript in web development include client interaction, form verification and asynchronous communication. 1) Dynamic content update and user interaction through DOM operations; 2) Client verification is carried out before the user submits data to improve the user experience; 3) Refreshless communication with the server is achieved through AJAX technology.




