Design Patterns Serie — Structural Chapter: Proxy Pattern
Design patterns: efficient solutions for common software development challenges. These pre-built solutions prevent "reinventing the wheel," offering answers to frequently recurring problems. However, they aren't one-size-fits-all; developers must adapt patterns to specific project needs.
Design patterns are categorized into three groups: Creational, Structural, and Behavioral, each with distinct characteristics. This article focuses on a popular structural pattern: the Proxy Pattern.
Understanding the Proxy Pattern
To grasp the Proxy pattern, consider this scenario: accessing user data requires first obtaining a JWT (JSON Web Token) via a separate service.
The Problem
Without the Proxy pattern, each user data request necessitates a JWT request, leading to performance bottlenecks, especially if the JWT service is slow or the token's expiration time isn't managed efficiently. This inefficient approach is illustrated below:

This repeated JWT fetching slows down data retrieval.

The solution lies in the Proxy pattern.
The Solution
The Proxy pattern introduces an intermediary layer—the Proxy—between the client and the real object (the JWT service). This intermediary manages access, adding functionality like caching or security checks.

This improves efficiency by caching the JWT, reducing calls to the JWT service. The improved architecture using the proxy pattern looks like this:

A class diagram illustrates the implementation:
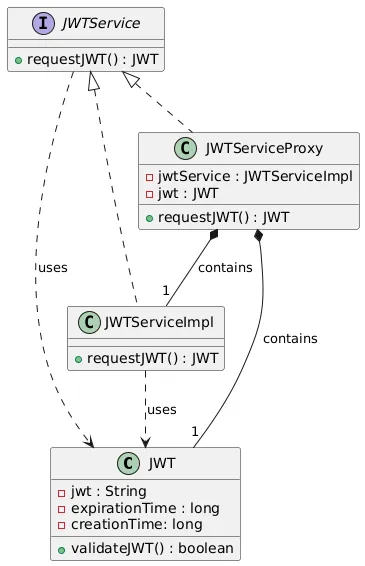
The class diagram shows:
-
Subject (JWTService): A common interface implemented by both the Proxy and the real JWT service. It defines the
requestJWT()method. -
Real Subject (JWTServiceImpl): Implements
JWTServiceand provides the actual JWT generation functionality. -
Proxy (JWTServiceProxy): Controls access to
JWTServiceImpl. It adds caching and validation logic.
Implementing the Proxy Pattern for JWT Generation
A complete code example is available at Proxy Pattern Repo. Below are key components:
The JWT Object
A JWT class (using Java 16 records) stores JWT data (token, expiration time, creation time) and includes a validateJWT() method for checking validity.
public record JWT(String token, long expirationTime, long creationTime) {
public boolean validateJWT(){
long currentTimeInSeconds = System.currentTimeMillis() / 1000;
return currentTimeInSeconds < creationTime + expirationTime;
}
}The Subject (Interface)
The JWTService interface declares the requestJWT() method.
public interface JWTService {
JWT requestJWT();
}The Real Subject
JWTServiceImpl implements JWTService, generating a mock JWT.
public class JWTServiceImpl implements JWTService {
@Override
public JWT requestJWT() {
return new JWT(generateToken(), 5, System.currentTimeMillis() / 1000);
}
// ... generateToken() method (simplified for this example) ...
}The Proxy
JWTServiceProxy caches and validates the JWT.
public class JWTServiceProxy implements JWTService {
private final JWTService jwtService;
private JWT jwt;
public JWTServiceProxy() {
this.jwtService = new JWTServiceImpl();
}
@Override
public JWT requestJWT() {
if (jwt == null || !jwt.validateJWT()) {
jwt = jwtService.requestJWT();
}
return jwt;
}
}Testing the Proxy Pattern
A simple test demonstrates the Proxy's caching behavior:
// ... (Main class with logging and Thread.sleep(5000) to simulate token expiration) ...
The output shows that only one JWT is generated initially, and a new one is generated only after the first one expires, demonstrating the proxy's caching and validation functionality.

Conclusion
The Proxy pattern enhances software efficiency and security. By carefully considering system architecture and potential bottlenecks, developers can leverage this pattern to create more robust and maintainable applications. Remember to adapt the pattern to your specific needs. Happy coding! ❤️
The above is the detailed content of Design Patterns Serie — Structural Chapter: Proxy Pattern. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1381
1381
 52
52
 How does Java's classloading mechanism work, including different classloaders and their delegation models?
Mar 17, 2025 pm 05:35 PM
How does Java's classloading mechanism work, including different classloaders and their delegation models?
Mar 17, 2025 pm 05:35 PM
Java's classloading involves loading, linking, and initializing classes using a hierarchical system with Bootstrap, Extension, and Application classloaders. The parent delegation model ensures core classes are loaded first, affecting custom class loa
 How do I implement multi-level caching in Java applications using libraries like Caffeine or Guava Cache?
Mar 17, 2025 pm 05:44 PM
How do I implement multi-level caching in Java applications using libraries like Caffeine or Guava Cache?
Mar 17, 2025 pm 05:44 PM
The article discusses implementing multi-level caching in Java using Caffeine and Guava Cache to enhance application performance. It covers setup, integration, and performance benefits, along with configuration and eviction policy management best pra
 How can I use JPA (Java Persistence API) for object-relational mapping with advanced features like caching and lazy loading?
Mar 17, 2025 pm 05:43 PM
How can I use JPA (Java Persistence API) for object-relational mapping with advanced features like caching and lazy loading?
Mar 17, 2025 pm 05:43 PM
The article discusses using JPA for object-relational mapping with advanced features like caching and lazy loading. It covers setup, entity mapping, and best practices for optimizing performance while highlighting potential pitfalls.[159 characters]
 How do I use Maven or Gradle for advanced Java project management, build automation, and dependency resolution?
Mar 17, 2025 pm 05:46 PM
How do I use Maven or Gradle for advanced Java project management, build automation, and dependency resolution?
Mar 17, 2025 pm 05:46 PM
The article discusses using Maven and Gradle for Java project management, build automation, and dependency resolution, comparing their approaches and optimization strategies.
 How do I create and use custom Java libraries (JAR files) with proper versioning and dependency management?
Mar 17, 2025 pm 05:45 PM
How do I create and use custom Java libraries (JAR files) with proper versioning and dependency management?
Mar 17, 2025 pm 05:45 PM
The article discusses creating and using custom Java libraries (JAR files) with proper versioning and dependency management, using tools like Maven and Gradle.




