 System Tutorial
System Tutorial
 LINUX
LINUX
 Linux Binary Analysis for Reverse Engineering and Vulnerability Discovery
Linux Binary Analysis for Reverse Engineering and Vulnerability Discovery
Linux Binary Analysis for Reverse Engineering and Vulnerability Discovery

Introduction
Binary analysis occupies a unique position in the fields of network security and software development. It is a technique that allows you to check compiled programs to understand their functionality, identify vulnerabilities, or debug problems without accessing the original source code. Binary analytics skills are crucial for Linux systems that dominate servers, embedded systems, and even personal computing.
This article will take you into the world of Linux binary analysis, reverse engineering and vulnerability discovery. Whether you are an experienced cybersecurity professional or an aspiring reverse engineer, you will gain insight into the tools, technical and ethical considerations that define this fascinating discipline.
Understanding Linux binary files
To analyze a binary file, you must first understand its structure and behavior.
What is a Linux binary? Linux binary files are compiled machine code files executed by the operating system. These files generally comply with Executable and Linkable Formats (ELF), a common standard used in Unix-class systems.
Composition of ELF fileELF binary files are divided into several key parts, each of which has its own unique function:
- Head: Contains metadata, including architecture, entry points, and types (executable files, shared libraries, etc.).
- Section: Includes code (.text), initialized data (.data), uninitialized data (.bss), etc.
- Segment: The memory-mapped part of the binary file used during execution.
- Symbol table: Map function names and variables to addresses (in unstripped binary files).
Tools for checking binary filesSome commonly used beginner tools:
- readelf: Displays detailed information about the ELF file structure.
- objdump: Disassemble binary files and provide in-depth understanding of machine code.
- strings: Extract printable strings from binary files, usually revealing configuration data or error messages.
Introduction to reverse engineering
What is reverse engineering? Reverse engineering refers to profiling a program to understand its internal workings. This is crucial for scenarios such as debugging proprietary software, analyzing malware, and performing security audits.
Legal and Ethical ConsiderationsReverse Engineering is usually in the legal gray area. Be sure to comply with the laws and licensing agreements. Avoid immoral practices, such as using reverse engineering insights for unauthorized purposes.
Reverse Engineering Method
Efficient reverse engineering combines static and dynamic analysis techniques.
Static Analysis Techniques- Disassembler: Tools such as Ghidra and IDA Pro convert machine code into human-readable assembly code. This helps analysts reconstruct control flow and logic.
- Manual Code Review: Analysts identify patterns and vulnerabilities such as suspicious loops or memory access.
- Binary Difference Analysis: Comparison of two binary files to identify differences, usually used to analyze patches or updates.
Dynamic Analysis Technology- Debugger: Tools such as GDB and LLDB allow real-time debugging of running binary files to check variables, memory, and execution processes.
- Tracking Tools: strace and ltrace monitor system and library calls to reveal runtime behavior.
- Embroider: Platforms such as QEMU provide a secure environment to execute and analyze binary files.
Mixed technologyCombining static and dynamic analysis can give you a more comprehensive understanding of the situation. For example, static analysis may reveal suspicious functions, while dynamic analysis can test their execution in real time.
Vulnerability discovery in Linux binary files
Common vulnerabilities in binary files - Buffer overflow: Memory overwrite exceeds the allocated buffer, which may cause code execution.
- Format string vulnerability: Take advantage of incorrect user input in printf class functions.
- Error in use after release: Accessing memory after memory is released usually results in crashes or exploits.
Vulnerability Discovery Tool- Fuzzer: Tools such as AFL and libFuzzer> automatically generate input to detect crashes or unexpected behavior.
- Static Analyzer: CodeQL and Clang Static Analyzer detect code patterns that indicate vulnerabilities.
- Symbol execution: Tools such as Angr analyze all possible execution paths to identify potential security issues.
Case Study: The infamous Heartbleed vulnerability in OpenSSL exploits incorrect bounds checks, allowing attackers to leak sensitive data. Analyzing such vulnerabilities highlights the importance of powerful binary analysis.
Practical steps for binary analysis
Set the environment- For security reasons, use a virtual machine or container.
- Installing necessary tools: gdb, radare2, binwalk, etc.
- Isolate unknown binary files in a sandbox to prevent accidental damage.
Practical steps1. Check binary files: Use files and readelf to collect basic information. 2. Disassembly: Load binary files in Ghidra or IDA Pro to analyze their structure. 3. Tracking execution: Use gdb to step in the program and observe its behavior. 4. Identify vulnerabilities: Find functions such as strcpy or sprintf, which usually represent unsafe practices. 5. Test input: Use the fuzzing tool to provide unexpected input and observe the reaction.
Advanced Theme
Confused and anti-reverse technology
Attackers or developers may use techniques such as code obfuscation or anti-debug techniques to hinder analysis. Tools such as Unpacker or techniques such as bypassing anti-debug checks can help.
Vulnerability exploitation
- After the vulnerability is discovered, tools such as pwntools and ROPgadget help create a proof of concept.
- Techniques such as return-guided programming (ROP) can utilize buffer overflow.
Machine Learning in Binary Analysis
Emerging tools use machine learning to identify patterns in binary files to help identify vulnerabilities. Projects such as DeepCode and research on neural network-assisted analysis are pushing the boundaries.
Conclusion
Linux binary analysis is both an art and a science, requiring careful attention to details and a solid understanding of programming, operating systems and security concepts. By combining the right tools, techniques and ethical practices, reverse engineers can identify vulnerabilities and enhance security environments.
The above is the detailed content of Linux Binary Analysis for Reverse Engineering and Vulnerability Discovery. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1393
1393
 52
52
 37
37
 111
111
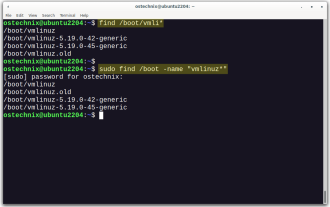 How To List Or Check All Installed Linux Kernels From Commandline
Mar 23, 2025 am 10:43 AM
How To List Or Check All Installed Linux Kernels From Commandline
Mar 23, 2025 am 10:43 AM
Linux Kernel is the core component of a GNU/Linux operating system. Developed by Linus Torvalds in 1991, it is a free, open-source, monolithic, modular, and multitasking Unix-like kernel. In Linux, it is possible to install multiple kernels on a sing
 What is the Linux best used for?
Apr 03, 2025 am 12:11 AM
What is the Linux best used for?
Apr 03, 2025 am 12:11 AM
Linux is best used as server management, embedded systems and desktop environments. 1) In server management, Linux is used to host websites, databases, and applications, providing stability and reliability. 2) In embedded systems, Linux is widely used in smart home and automotive electronic systems because of its flexibility and stability. 3) In the desktop environment, Linux provides rich applications and efficient performance.
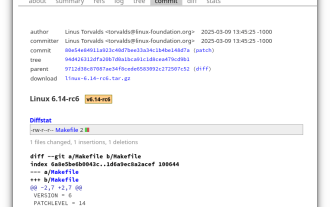 Linux Kernel 6.14 RC6 Released
Mar 24, 2025 am 10:21 AM
Linux Kernel 6.14 RC6 Released
Mar 24, 2025 am 10:21 AM
Linus Torvalds has released Linux Kernel 6.14 Release Candidate 6 (RC6), reporting no significant issues and keeping the release on track. The most notable change in this update addresses an AMD microcode signing issue, while the rest of the updates
 What are the 5 basic components of Linux?
Apr 06, 2025 am 12:05 AM
What are the 5 basic components of Linux?
Apr 06, 2025 am 12:05 AM
The five basic components of Linux are: 1. The kernel, managing hardware resources; 2. The system library, providing functions and services; 3. Shell, the interface for users to interact with the system; 4. The file system, storing and organizing data; 5. Applications, using system resources to implement functions.
 LocalSend - The Open-Source Airdrop Alternative For Secure File Sharing
Mar 24, 2025 am 09:20 AM
LocalSend - The Open-Source Airdrop Alternative For Secure File Sharing
Mar 24, 2025 am 09:20 AM
If you're familiar with AirDrop, you know it's a popular feature developed by Apple Inc. that enables seamless file transfer between supported Macintosh computers and iOS devices using Wi-Fi and Bluetooth. However, if you're using Linux and missing o
 How To Monitor Battery Level And Get Notifications On Linux Using battmon
Mar 24, 2025 am 10:23 AM
How To Monitor Battery Level And Get Notifications On Linux Using battmon
Mar 24, 2025 am 10:23 AM
Keeping your Laptop battery in check is very important for maintaining its longevity and ensuring you're never caught off guard by a sudden shutdown. If you’re a Linux user, you can easily monitor your Laptop's battery level and receive notifications
 What is the most use of Linux?
Apr 09, 2025 am 12:02 AM
What is the most use of Linux?
Apr 09, 2025 am 12:02 AM
Linux is widely used in servers, embedded systems and desktop environments. 1) In the server field, Linux has become an ideal choice for hosting websites, databases and applications due to its stability and security. 2) In embedded systems, Linux is popular for its high customization and efficiency. 3) In the desktop environment, Linux provides a variety of desktop environments to meet the needs of different users.
 What is basic Linux administration?
Apr 02, 2025 pm 02:09 PM
What is basic Linux administration?
Apr 02, 2025 pm 02:09 PM
Linux system management ensures the system stability, efficiency and security through configuration, monitoring and maintenance. 1. Master shell commands such as top and systemctl. 2. Use apt or yum to manage the software package. 3. Write automated scripts to improve efficiency. 4. Common debugging errors such as permission problems. 5. Optimize performance through monitoring tools.



