Rethinking Threat Detection In A Decentralized World

But that’s changing—thanks in large part to a fundamental shift in how we interpret and respond to risk.
The Cloud Visibility Gap Is a Threat Vector in Itself
Hybrid and multi-cloud environments have become the new normal.
Organizations run workloads across AWS, Azure, Google Cloud, and on-prem data centers—all while managing sprawling APIs, ephemeral containers, and third-party integrations. The result is a security visibility crisis.
Traditional Network Detection and Response tools can’t scale across cloud providers. Cloud-native application protection platforms, meanwhile, offer great telemetry—if you're entirely in the cloud. But most enterprises aren’t. And even when these platforms work as advertised, they often lack the context needed to act.
“There are really two fundamental issues here,” explains Jon Oltsik, analyst in residence at SiliconANGLE and theCUBE. “One is real-time visibility across all associated assets and components. The other is the ability to add context—such as an asset’s location, vulnerability, business value, etc. This visibility and context really requires massive scale and superior analytics.”
As Mario Espinoza, Chief Product Officer at Illumio, put it: “A breach doesn’t have to become a cyber disaster. But you can’t stop what you can’t see—and you can’t contain what you don’t understand.”
In short, detection isn’t enough. To mount an effective defense, you need to understand what’s happening—and why it matters.
Why Conventional Tools Fall Short
Let’s break it down:
- NDR tools rely on perimeter traffic and predefined rules. That’s great for well-understood threats, but attackers today exploit complexity and blind spots—especially through lateral movement.
- CNAPPs focus primarily on posture and configuration. They often miss the real-time activity that indicates an attack in progress.
- Both tend to overwhelm SOCs with high volumes of alerts while offering little guidance on what matters or what to do next.
And here's the hard truth: even the best-prevention strategy eventually fails. Breaches are inevitable. The real question is—what happens next?
Enter the AI Security Graph
The answer is the AI security graph, a data model that maps every workload, resource, and connection across the environment—on-prem and in the cloud. Think of it as a living, evolving blueprint of your organization’s digital nervous system.
By layering AI on top of this graph, organizations can detect previously invisible patterns, such as stealthy lateral movement or anomalous traffic between systems that should never be communicating.
Putting It Into Practice
This isn’t just theoretical. Illumio Insights brings the AI security graph to life. Espinoza explains it this way: “The attacker sees your network as a graph. Until now, defenders have been stuck thinking in lists. We’re changing that.”
Espinoza explained to me that Illumio Insights ingests billions of flows across hybrid and multi-cloud environments, in real time, without the need for agents or invasive infrastructure changes. The platform analyzes that data to identify blast radius, high-value targets under attack, and even obscure threats like shadow LLM activity or policy violations that expose critical workloads.
“We compress what could be hundreds of thousands of flows into a single, meaningful insight,” Espinoza notes. “Instead of overwhelming the SOC with alerts, we deliver a distilled view of what’s actually going on—and what needs to happen next.”
This approach doesn’t just reduce alert fatigue. It has the potential to fundamentally changes the nature of incident response. Analysts no longer need to sift through raw logs or stitch together disjointed alerts. They simply get an immediate, contextualized picture—with the ability to act on it instantly.
From Insight to Action
According to Espinoza, one of the most powerful features of Illumio Insights is its integration with Illumio Segmentation. With a single click, security teams can dynamically quarantine compromised systems—restricting communication without disrupting operations. Espinoza calls it "surgical enforcement."
“You might see a suspicious machine,” he explains, “but instead of shutting it down entirely and risking business disruption, you isolate the threat by disabling just the risky communication paths. It's like neurosurgery instead of amputation.”
That level of precision is critical in sensitive environments like manufacturing, energy, and healthcare—where taking a system offline isn’t just inconvenient, it’s potentially catastrophic.
Rethinking the Security Workflow
Perhaps most compelling is the flexibility that Illumio Insights offers. Organizations can deploy it in read-only mode for observability, integrate it into existing SIEM and SOAR workflows, or let it autonomously take action based on pre-approved rules. And as Espinoza shared, many customers who start with observability quickly ask to move into enforcement once they “see the full picture.”
Interestingly, while segmentation was originally positioned as a proactive Zero Trust control, it's the incident responders and threat hunters who have driven adoption of Insights. "They saw the gold mine in the graph,” Espinoza says. “They didn’t want to wait for a segmentation strategy—they wanted visibility and insights now.”
According to Oltsik, the real differentiator is how Illumio connects detection to enforcement in a seamless loop. “The beauty with Illumio is that it connects this detection and analysis with remediation capabilities. So, when Insights detects malicious traffic, security teams can further segment networks to prevent any further damage. This is an element of cyber-resilience—the ability to recover quickly from a cyberattack while minimizing damages.”
Smarter, Connected Graphs
Illumio isn’t stopping with network flows. Espinoza also hinted at a future where Illumio Insights connects with other graphs—like Microsoft’s and CrowdStrike’s—to offer even deeper context and automation.
The vision is clear: to arm defenders with tools that not only match, but surpass, the sophistication of modern attackers. “This is how we turn the tide,” he says. “Security at a system level. Defense that understands the environment better than the adversary does.”
From Reaction to Resilience
Organizations need something that is both profound and practical: a unified, intelligent view of the environment that empowers security teams to detect, understand, and contain threats—before they spiral into full-blown crises.
Because in a world where attackers think in graphs, it’s time defenders started doing the same.
The above is the detailed content of Rethinking Threat Detection In A Decentralized World. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Best AI Art Generators (Free & Paid) for Creative Projects
Apr 02, 2025 pm 06:10 PM
Best AI Art Generators (Free & Paid) for Creative Projects
Apr 02, 2025 pm 06:10 PM
The article reviews top AI art generators, discussing their features, suitability for creative projects, and value. It highlights Midjourney as the best value for professionals and recommends DALL-E 2 for high-quality, customizable art.
 Getting Started With Meta Llama 3.2 - Analytics Vidhya
Apr 11, 2025 pm 12:04 PM
Getting Started With Meta Llama 3.2 - Analytics Vidhya
Apr 11, 2025 pm 12:04 PM
Meta's Llama 3.2: A Leap Forward in Multimodal and Mobile AI Meta recently unveiled Llama 3.2, a significant advancement in AI featuring powerful vision capabilities and lightweight text models optimized for mobile devices. Building on the success o
 Best AI Chatbots Compared (ChatGPT, Gemini, Claude & More)
Apr 02, 2025 pm 06:09 PM
Best AI Chatbots Compared (ChatGPT, Gemini, Claude & More)
Apr 02, 2025 pm 06:09 PM
The article compares top AI chatbots like ChatGPT, Gemini, and Claude, focusing on their unique features, customization options, and performance in natural language processing and reliability.
 Is ChatGPT 4 O available?
Mar 28, 2025 pm 05:29 PM
Is ChatGPT 4 O available?
Mar 28, 2025 pm 05:29 PM
ChatGPT 4 is currently available and widely used, demonstrating significant improvements in understanding context and generating coherent responses compared to its predecessors like ChatGPT 3.5. Future developments may include more personalized interactions and real-time data processing capabilities, further enhancing its potential for various applications.
 Top AI Writing Assistants to Boost Your Content Creation
Apr 02, 2025 pm 06:11 PM
Top AI Writing Assistants to Boost Your Content Creation
Apr 02, 2025 pm 06:11 PM
The article discusses top AI writing assistants like Grammarly, Jasper, Copy.ai, Writesonic, and Rytr, focusing on their unique features for content creation. It argues that Jasper excels in SEO optimization, while AI tools help maintain tone consist
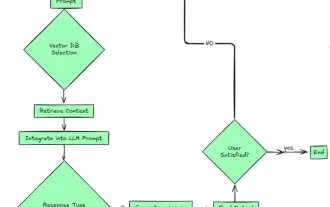 Top 7 Agentic RAG System to Build AI Agents
Mar 31, 2025 pm 04:25 PM
Top 7 Agentic RAG System to Build AI Agents
Mar 31, 2025 pm 04:25 PM
2024 witnessed a shift from simply using LLMs for content generation to understanding their inner workings. This exploration led to the discovery of AI Agents – autonomous systems handling tasks and decisions with minimal human intervention. Buildin
 Choosing the Best AI Voice Generator: Top Options Reviewed
Apr 02, 2025 pm 06:12 PM
Choosing the Best AI Voice Generator: Top Options Reviewed
Apr 02, 2025 pm 06:12 PM
The article reviews top AI voice generators like Google Cloud, Amazon Polly, Microsoft Azure, IBM Watson, and Descript, focusing on their features, voice quality, and suitability for different needs.
 AV Bytes: Meta's Llama 3.2, Google's Gemini 1.5, and More
Apr 11, 2025 pm 12:01 PM
AV Bytes: Meta's Llama 3.2, Google's Gemini 1.5, and More
Apr 11, 2025 pm 12:01 PM
This week's AI landscape: A whirlwind of advancements, ethical considerations, and regulatory debates. Major players like OpenAI, Google, Meta, and Microsoft have unleashed a torrent of updates, from groundbreaking new models to crucial shifts in le






