Understand OAuth 2.0, understand oauth2.0_PHP tutorial
Understand OAuth 2.0, understand oauth2.0
OAuth is an open network standard for authorization, which is widely used around the world. The current version is version 2.0.
This article provides a concise and popular explanation of the design ideas and operation process of OAuth 2.0. The main reference material is RFC 6749.

1. Application scenarios
To understand where OAuth is applicable, let me give a hypothetical example.
There is a "cloud printing" website that can print out photos stored by users on Google. In order to use this service, users must let "Cloud Print" read their photos stored on Google.

The problem is that Google will only allow "Cloud Print" to read these photos with the user's authorization. So, how does "Cloud Printing" obtain the user's authorization?
The traditional method is for the user to tell "Cloud Print" their Google username and password, and the latter can read the user's photos. This approach has several serious shortcomings.
<p>(1)"Understand OAuth 2.0, understand oauth2.0_PHP tutorial"为了后续的服务,会保存用户的密码,这样很不安全。</p> <p>(2)Google不得不部署密码登录,而我们知道,单纯的密码登录并不安全。</p> <p>(3)"Understand OAuth 2.0, understand oauth2.0_PHP tutorial"拥有了获取用户储存在Google所有资料的权力,用户没法限制"Understand OAuth 2.0, understand oauth2.0_PHP tutorial"获得授权的范围和有效期。</p> <p>(4)用户只有修改密码,才能收回赋予"Understand OAuth 2.0, understand oauth2.0_PHP tutorial"的权力。但是这样做,会使得其他所有获得用户授权的第三方应用程序全部失效。</p> <p>(5)只要有一个第三方应用程序被破解,就会导致用户密码泄漏,以及所有被密码保护的数据泄漏。</p>
OAuth was born to solve the above problems.
2. Definition of nouns
Before explaining OAuth 2.0 in detail, you need to understand a few special terms. They are crucial to understanding the following explanations, especially the several pictures.
<p>(1) <strong>Third-party application</strong>:第三方应用程序,本文中又称"客户端"(client),即上一节例子中的"Understand OAuth 2.0, understand oauth2.0_PHP tutorial"。</p> <p>(2)<strong>HTTP service</strong>:HTTP服务提供商,本文中简称"服务提供商",即上一节例子中的Google。</p> <p>(3)<strong>Resource Owner</strong>:资源所有者,本文中又称"用户"(user)。</p> <p>(4)<strong>User Agent</strong>:用户代理,本文中就是指浏览器。</p> <p>(5)<strong>Authorization server</strong>:认证服务器,即服务提供商专门用来处理认证的服务器。</p> <p>(6)<strong>Resource server</strong>:资源服务器,即服务提供商存放用户生成的资源的服务器。它与认证服务器,可以是同一台服务器,也可以是不同的服务器。</p>
After knowing the above terms, it is not difficult to understand that the function of OAuth is to allow the "client" to obtain the authorization of the "user" in a safe and controllable manner and interact with the "service provider".
3. The idea of OAuth
OAuth sets an authorization layer between the "client" and the "service provider". The "client" cannot directly log in to the "service provider", but can only log in to the authorization layer to distinguish the user from the client. The token used by the "client" to log in to the authorization layer is different from the user's password. Users can specify the permission scope and validity period of the authorization layer token when logging in.
After the "client" logs in to the authorization layer, the "service provider" opens the user's stored information to the "client" based on the authority scope and validity period of the token.
4. Operation process
The running process of OAuth 2.0 is as shown below, excerpted from RFC 6749.

<p>(A)用户打开客户端以后,客户端要求用户给予授权。</p> <p>(B)用户同意给予客户端授权。</p> <p>(C)客户端使用上一步获得的授权,向认证服务器申请令牌。</p> <p>(D)认证服务器对客户端进行认证以后,确认无误,同意发放令牌。</p> <p>(E)客户端使用令牌,向资源服务器申请获取资源。</p> <p>(F)资源服务器确认令牌无误,同意向客户端开放资源。</p>
It is not difficult to see that among the above six steps, B is the key, that is, how can the user authorize the client. With this authorization, the client can obtain the token and then obtain resources based on the token.
The following explains one by one the four modes for the client to obtain authorization.
5. Client authorization mode
The client must obtain the user's authorization (authorization grant) to obtain the token (access token). OAuth 2.0 defines four authorization methods.
- Authorization code mode
- Simplified mode (implicit)
- Password mode (resource owner password credentials)
- Client mode (client credentials)
6. Authorization code mode
Authorization code mode is the authorization mode with the most complete functions and the strictest process. Its characteristic is that it interacts with the authentication server of the "service provider" through the client's backend server.

The steps are as follows:
<p>(A)用户访问客户端,后者将前者导向认证服务器。</p> <p>(B)用户选择是否给予客户端授权。</p> <p>(C)假设用户给予授权,认证服务器将用户导向客户端事先指定的"重定向URI"(redirection URI),同时附上一个授权码。</p> <p>(D)客户端收到授权码,附上早先的"重定向URI",向认证服务器申请令牌。这一步是在客户端的后台的服务器上完成的,对用户不可见。</p> <p>(E)认证服务器核对了授权码和重定向URI,确认无误后,向客户端发送访问令牌(access token)和更新令牌(refresh token)。</p>
The following are the parameters required for the above steps.
In step A, the URI used by the client to apply for authentication includes the following parameters:
- response_type: Indicates the authorization type, required. The value here is fixed to "code"
- client_id: Indicates the ID of the client, required
- redirect_uri: Represents redirect URI, optional
- scope: Indicates the scope of permissions applied for, optional
- state: Indicates the current state of the client. You can specify any value. The authentication server will return this value unchanged.
Here is an example.
<pre class=" language-http"><code class=" language-http">
GET /authorize?response_type=code&client_id=s6BhdRkqt3&state=xyz
&redirect_uri=https%3A%2F%2Fclient%2Eexample%2Ecom%2Fcb HTTP/1.1
<span class="token keyword">Host: server.example.com
</span></code>In step C, the server responds to the client’s URI, including the following parameters:
- code: indicates authorization code, required. The validity period of the code should be very short, usually set to 10 minutes. The client can only use the code once, otherwise it will be rejected by the authorization server. This code has a one-to-one correspondence with the client ID and redirect URI.
- state: If the client's request contains this parameter, the authentication server's response must also contain this parameter exactly.
Here is an example.
<pre class=" language-http"><code class=" language-http">
HTTP/1.1 302 Found
<span class="token keyword">Location: https://client.example.com/cb?code=SplxlOBeZQQYbYS6WxSbIA
&state=xyz
</span></code>In step D, the client applies for an HTTP request for a token from the authentication server, including the following parameters:
- grant_type: Indicates the authorization mode used, required. The value here is fixed to "authorization_code".
- code: Indicates the authorization code obtained in the previous step, required.
- redirect_uri: Represents the redirect URI, required, and must be consistent with the parameter value in step A.
- client_id: Indicates the client ID, required.
Here is an example.
<pre class=" language-http"><code class=" language-http"> POST /token HTTP/1.1 <span class="token keyword">Host: server.example.com <span class="token keyword">Authorization: Basic czZCaGRSa3F0MzpnWDFmQmF0M2JW <span class="token keyword">Content-Type: application/x-www-form-urlencoded grant_type=authorization_code&code=SplxlOBeZQQYbYS6WxSbIA &redirect_uri=https%3A%2F%2Fclient%2Eexample%2Ecom%2Fcb </span></span></span></code>
E步骤中,认证服务器发送的HTTP回复,包含以下参数:
- access_token:表示访问令牌,必选项。
- token_type:表示令牌类型,该值大小写不敏感,必选项,可以是bearer类型或mac类型。
- expires_in:表示过期时间,单位为秒。如果省略该参数,必须其他方式设置过期时间。
- refresh_token:表示更新令牌,用来获取下一次的访问令牌,可选项。
- scope:表示权限范围,如果与客户端申请的范围一致,此项可省略。
下面是一个例子。
<pre class=" language-http"><code class=" language-http">
HTTP/1.1 200 OK
Content-Type: application/json;charset=UTF-8
Cache-Control: no-store
Pragma: no-cache<span class="token application/json">
<span class="token punctuation">{
<span class="token string">"access_token"<span class="token punctuation">:<span class="token string">"2YotnFZFEjr1zCsicMWpAA"<span class="token punctuation">,
<span class="token string">"token_type"<span class="token punctuation">:<span class="token string">"example"<span class="token punctuation">,
<span class="token string">"expires_in"<span class="token punctuation">:<span class="token number">3600<span class="token punctuation">,
<span class="token string">"refresh_token"<span class="token punctuation">:<span class="token string">"tGzv3JOkF0XG5Qx2TlKWIA"<span class="token punctuation">,
<span class="token string">"example_parameter"<span class="token punctuation">:<span class="token string">"example_value"
<span class="token punctuation">}
</span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></code>从上面代码可以看到,相关参数使用JSON格式发送(Content-Type: application/json)。此外,HTTP头信息中明确指定不得缓存。
七、Understand OAuth 2.0, understand oauth2.0_PHP tutorial
Understand OAuth 2.0, understand oauth2.0_PHP tutorial(implicit grant type)不通过第三方应用程序的服务器,直接在浏览器中向认证服务器申请令牌,跳过了"授权码"这个步骤,因此得名。所有步骤在浏览器中完成,令牌对访问者是可见的,且客户端不需要认证。

它的步骤如下:
<p>(A)客户端将用户导向认证服务器。</p> <p>(B)用户决定是否给于客户端授权。</p> <p>(C)假设用户给予授权,认证服务器将用户导向客户端指定的"重定向URI",并在URI的Hash部分包含了访问令牌。</p> <p>(D)浏览器向资源服务器发出请求,其中不包括上一步收到的Hash值。</p> <p>(E)资源服务器返回一个网页,其中包含的代码可以获取Hash值中的令牌。</p> <p>(F)浏览器执行上一步获得的脚本,提取出令牌。</p> <p>(G)浏览器将令牌发给客户端。</p>
下面是上面这些步骤所需要的参数。
A步骤中,客户端发出的HTTP请求,包含以下参数:
- response_type:表示授权类型,此处的值固定为"token",必选项。
- client_id:表示客户端的ID,必选项。
- redirect_uri:表示重定向的URI,可选项。
- scope:表示权限范围,可选项。
- state:表示客户端的当前状态,可以指定任意值,认证服务器会原封不动地返回这个值。
下面是一个例子。
<pre class=" language-http"><code class=" language-http">
GET /authorize?response_type=token&client_id=s6BhdRkqt3&state=xyz
&redirect_uri=https%3A%2F%2Fclient%2Eexample%2Ecom%2Fcb HTTP/1.1
Host: server.example.com
</code>C步骤中,认证服务器回应客户端的URI,包含以下参数:
- access_token:表示访问令牌,必选项。
- token_type:表示令牌类型,该值大小写不敏感,必选项。
- expires_in:表示过期时间,单位为秒。如果省略该参数,必须其他方式设置过期时间。
- scope:表示权限范围,如果与客户端申请的范围一致,此项可省略。
- state:如果客户端的请求中包含这个参数,认证服务器的回应也必须一模一样包含这个参数。
下面是一个例子。
<pre class=" language-http"><code class=" language-http">
HTTP/1.1 302 Found
Location: http://example.com/cb#access_token=2YotnFZFEjr1zCsicMWpAA
&state=xyz&token_type=example&expires_in=3600
</code>在上面的例子中,认证服务器用HTTP头信息的Location栏,指定浏览器重定向的网址。注意,在这个网址的Hash部分包含了令牌。
根据上面的D步骤,下一步浏览器会访问Location指定的网址,但是Hash部分不会发送。接下来的E步骤,服务提供商的资源服务器发送过来的代码,会提取出Hash中的令牌。
八、Understand OAuth 2.0, understand oauth2.0_PHP tutorial
Understand OAuth 2.0, understand oauth2.0_PHP tutorial(Resource Owner Password Credentials Grant)中,用户向客户端提供自己的用户名和密码。客户端使用这些信息,向"服务商提供商"索要授权。
在这种模式中,用户必须把自己的密码给客户端,但是客户端不得储存密码。这通常用在用户对客户端高度信任的情况下,比如客户端是操作系统的一部分,或者由一个著名公司出品。而认证服务器只有在其他授权模式无法执行的情况下,才能考虑使用这种模式。

它的步骤如下:
<p>(A)用户向客户端提供用户名和密码。</p> <p>(B)客户端将用户名和密码发给认证服务器,向后者请求令牌。</p> <p>(C)认证服务器确认无误后,向客户端提供访问令牌。</p>
B步骤中,客户端发出的HTTP请求,包含以下参数:
- grant_type:表示授权类型,此处的值固定为"password",必选项。
- username:表示用户名,必选项。
- password:表示用户的密码,必选项。
- scope:表示权限范围,可选项。
下面是一个例子。
<pre class=" language-http"><code class=" language-http">
POST /token HTTP/1.1
Host: server.example.com
Authorization: Basic czZCaGRSa3F0MzpnWDFmQmF0M2JW
Content-Type: application/x-www-form-urlencoded
grant_type=password&username=johndoe&password=A3ddj3w
</code>C步骤中,认证服务器向客户端发送访问令牌,下面是一个例子。
<pre class=" language-http"><code class=" language-http">
HTTP/1.1 200 OK
Content-Type: application/json;charset=UTF-8
Cache-Control: no-store
Pragma: no-cache<span class="token application/json">
<span class="token punctuation">{
<span class="token string">"access_token"<span class="token punctuation">:<span class="token string">"2YotnFZFEjr1zCsicMWpAA"<span class="token punctuation">,
<span class="token string">"token_type"<span class="token punctuation">:<span class="token string">"example"<span class="token punctuation">,
<span class="token string">"expires_in"<span class="token punctuation">:<span class="token number">3600<span class="token punctuation">,
<span class="token string">"refresh_token"<span class="token punctuation">:<span class="token string">"tGzv3JOkF0XG5Qx2TlKWIA"<span class="token punctuation">,
<span class="token string">"example_parameter"<span class="token punctuation">:<span class="token string">"example_value"
<span class="token punctuation">}
</span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></code>上面代码中,各个参数的含义参见《Understand OAuth 2.0, understand oauth2.0_PHP tutorial》一节。
整个过程中,客户端不得保存用户的密码。
九、Understand OAuth 2.0, understand oauth2.0_PHP tutorial
Understand OAuth 2.0, understand oauth2.0_PHP tutorial(Client Credentials Grant)指客户端以自己的名义,而不是以用户的名义,向"服务提供商"进行认证。严格地说,Understand OAuth 2.0, understand oauth2.0_PHP tutorial并不属于OAuth框架所要解决的问题。在这种 模式中,用户直接向客户端注册,客户端以自己的名义要求"服务提供商"提供服务,其实不存在授权问题。

它的步骤如下:
<p>(A)客户端向认证服务器进行身份认证,并要求一个访问令牌。</p> <p>(B)认证服务器确认无误后,向客户端提供访问令牌。</p>
A步骤中,客户端发出的HTTP请求,包含以下参数:
- granttype:表示授权类型,此处的值固定为"clientcredentials",必选项。
- scope:表示权限范围,可选项。
<pre class=" language-http"><code class=" language-http">
POST /token HTTP/1.1
Host: server.example.com
Authorization: Basic czZCaGRSa3F0MzpnWDFmQmF0M2JW
Content-Type: application/x-www-form-urlencoded
grant_type=client_credentials
</code>认证服务器必须以某种方式,验证客户端身份。
B步骤中,认证服务器向客户端发送访问令牌,下面是一个例子。
<pre class=" language-http"><code class=" language-http">
HTTP/1.1 200 OK
Content-Type: application/json;charset=UTF-8
Cache-Control: no-store
Pragma: no-cache<span class="token application/json">
<span class="token punctuation">{
<span class="token string">"access_token"<span class="token punctuation">:<span class="token string">"2YotnFZFEjr1zCsicMWpAA"<span class="token punctuation">,
<span class="token string">"token_type"<span class="token punctuation">:<span class="token string">"example"<span class="token punctuation">,
<span class="token string">"expires_in"<span class="token punctuation">:<span class="token number">3600<span class="token punctuation">,
<span class="token string">"example_parameter"<span class="token punctuation">:<span class="token string">"example_value"
<span class="token punctuation">}
</span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></span></code>上面代码中,各个参数的含义参见《Understand OAuth 2.0, understand oauth2.0_PHP tutorial》一节。
十、更新令牌
如果用户访问的时候,客户端的"访问令牌"已经过期,则需要使用"更新令牌"申请一个新的访问令牌。
客户端发出更新令牌的HTTP请求,包含以下参数:
- granttype:表示使用的授权模式,此处的值固定为"refreshtoken",必选项。
- refresh_token:表示早前收到的更新令牌,必选项。
- scope:表示申请的授权范围,不可以超出上一次申请的范围,如果省略该参数,则表示与上一次一致。
下面是一个例子。
<pre class=" language-http"><code class=" language-http">
POST /token HTTP/1.1
Host: server.example.com
Authorization: Basic czZCaGRSa3F0MzpnWDFmQmF0M2JW
Content-Type: application/x-www-form-urlencoded
grant_type=refresh_token&refresh_token=tGzv3JOkF0XG5Qx2TlKWIA
</code>
Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to upgrade win10 enterprise version 2016 long-term service version to professional version
Jan 03, 2024 pm 11:26 PM
How to upgrade win10 enterprise version 2016 long-term service version to professional version
Jan 03, 2024 pm 11:26 PM
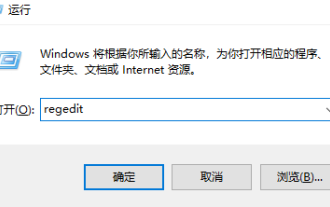
When we no longer want to continue using the current Win10 Enterprise Edition 2016 Long-Term Service Edition, we can choose to switch to the Professional Edition. The method is also very simple. We only need to change some contents and install the system image. How to change win10 enterprise version 2016 long-term service version to professional version 1. Press win+R, and then enter "regedit" 2. Paste the following path directly in the address bar above: Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion3 , then find the EditionID and replace the content with "professional" to confirm
 How to do Google Drive integration using PHP and OAuth
Jul 31, 2023 pm 04:41 PM
How to do Google Drive integration using PHP and OAuth
Jul 31, 2023 pm 04:41 PM
How to do GoogleDrive integration using PHP and OAuth GoogleDrive is a popular cloud storage service that allows users to store files in the cloud and share them with other users. Through GoogleDriveAPI, we can use PHP to write code to integrate with GoogleDrive to implement file uploading, downloading, deletion and other operations. To use GoogleDriveAPI we need to authenticate via OAuth and
 How to use Flask-Security to implement user authentication and authorization
Aug 04, 2023 pm 02:40 PM
How to use Flask-Security to implement user authentication and authorization
Aug 04, 2023 pm 02:40 PM
How to use Flask-Security to implement user authentication and authorization Introduction: In modern web applications, user authentication and authorization are essential functions. To simplify this process, Flask-Security is a very useful extension that provides a series of tools and functions to make user authentication and authorization simple and convenient. This article will introduce how to use Flask-Security to implement user authentication and authorization. 1. Install the Flask-Security extension: at the beginning
 How to implement authentication and authorization in PHP applications using JWT
Aug 03, 2023 pm 10:17 PM
How to implement authentication and authorization in PHP applications using JWT
Aug 03, 2023 pm 10:17 PM
How to use JWT to implement authentication and authorization in PHP applications Introduction: With the rapid development of the Internet, authentication and authorization are becoming increasingly important in web applications. JSONWebToken (JWT) is a popular authentication and authorization mechanism that is widely used in PHP applications. This article will introduce how to use JWT to implement authentication and authorization in PHP applications, and provide code examples to help readers better understand the use of JWT. 1. Introduction to JWT JSONWebTo
 How to get authorization for Douyin slices and goods? Is Douyin slicing easy to make?
Mar 07, 2024 pm 10:52 PM
How to get authorization for Douyin slices and goods? Is Douyin slicing easy to make?
Mar 07, 2024 pm 10:52 PM
Douyin, as a popular social media platform at the moment, not only provides people with a wealth of entertainment content, but has also become an important channel for many brands and merchants to promote products and achieve sales. Among them, Douyin’s slicing and selling products has become a novel and efficient marketing method. So, how do you get authorization for Douyin's sliced products? 1. How do you get authorization for Douyin's sliced products? Douyin's sliced products decompose long videos into short video clips and embed product promotion information in them to attract viewers to buy. . When slicing and selling goods on Douyin, the first step is to obtain authorization from the original video. When looking for a suitable licensor, you can consider using various channels such as Douyin platform, social media and industry forums. Find creators or copyright holders with popular video content and actively connect with them,
 OAuth2 authentication method and implementation in PHP
Aug 07, 2023 pm 10:53 PM
OAuth2 authentication method and implementation in PHP
Aug 07, 2023 pm 10:53 PM
OAuth2 authentication method and implementation in PHP With the development of the Internet, more and more applications need to interact with third-party platforms. In order to protect user privacy and security, many third-party platforms use the OAuth2 protocol to implement user authentication. In this article, we will introduce the OAuth2 authentication method and implementation in PHP, and attach corresponding code examples. OAuth2 is an authorization framework that allows users to authorize third-party applications to access their resources on another service provider without mentioning
 What to do if wps authorization has expired and text cannot be entered?
Mar 20, 2024 am 09:00 AM
What to do if wps authorization has expired and text cannot be entered?
Mar 20, 2024 am 09:00 AM
There are many genuine softwares in order to protect their own intellectual property rights. Before using the software, users must obtain some authorizations and obtain permission from the developer before they can use it. Some software has a trial period. After this period, you need to obtain re-authorization before you can use it normally. If wps prompts that the authorization has expired, we cannot perform any operations. How to solve this problem, let’s take a look at the explanation below. 1. I opened the WPS text program and clicked on the red box in the picture above, as shown in the picture below. 2. Click Configuration and Repair Tools. 3. Select "Advanced", as shown in the figure below. 4. Click the product management center and delete the "Expired" prompt content, as shown in the figure below. 5. After clicking "Add", enter the serial number, as shown in the figure below. 6. Then first
 How to use PHP and OAuth for QQ login integration
Jul 31, 2023 pm 12:37 PM
How to use PHP and OAuth for QQ login integration
Jul 31, 2023 pm 12:37 PM
Introduction to how to use PHP and OAuth for QQ login integration: With the development of social media, more and more websites and applications are beginning to provide third-party login functions to facilitate users to quickly register and log in. As one of China's largest social media platforms, QQ has also become a third-party login service provided by many websites and applications. This article will introduce the steps on how to use PHP and OAuth for QQ login integration, with code examples. Step 1: Register as a QQ open platform developer. Before starting to integrate QQ login, I






