 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Detailed explanation and prevention of SQL injection in php_PHP tutorial
Detailed explanation and prevention of SQL injection in php_PHP tutorial
Detailed explanation and prevention of SQL injection in php_PHP tutorial
One is that the input data is not filtered (filtered input), and the other is that the data sent to the database is not escaped (escaped output). These two important steps are indispensable and require special attention to reduce program errors.
For attackers, conducting SQL injection attacks requires thinking and experimenting. It is very necessary to conduct well-founded reasoning about the database solution (assuming of course that the attacker cannot see your source program and database solution). Consider the following Simple login form:
As an attacker, he will start by guessing the query statement to verify the username and password. By looking at the source files, he can start guessing your habits.
For example, naming conventions. It is usually assumed that the field names in your form are the same as the field names in the data table. Of course, ensuring they are different is not necessarily a reliable security measure.
For the first guess, you will generally use the query in the following example:
< ;?php
$password_hash = md5($_POST['password']);
$sql = "SELECT count(*)
FROM users
WHERE username = '{$_POST ['username']}'
AND password = '$password_hash'";
?>
Using the MD5 value of the user password was originally a common practice, but now it is not Not particularly safe anymore. Recent research shows that the MD5 algorithm is flawed, and the large number of MD5 databases reduces the difficulty of MD5 reverse cracking. Please visit http://md5.rednoize.com/ to view the demo (sic. Research by Professor Wang Xiaoyun of Shandong University shows that MD5 "collision" can be quickly found, that is, two different files and words that can produce the same MD5 value. String. MD5 is a message digest algorithm, not an encryption algorithm, and reverse cracking is out of the question. However, according to this result, it is dangerous to use md5 directly in the above special case.)
The best protection method is to append a string of your own definition to the password, for example:
$salt = 'SHIFLETT';
$password_hash = md5($salt . md5($_POST['password'] . $salt));
?> ;
Of course, attackers may not be able to guess right the first time, and they often need to do some experiments. A better way to experiment is to enter single quotes as the username, because this may expose some important information. Many developers call the function mysql_error() to report the error when an error occurs during Mysql statement execution. See the example below:
mysql_query($sql) or exit(mysql_error());
?>
While this method is useful in development, it can expose important information to an attacker. If the attacker uses single quotes as the username and mypass as the password, the query statement will become:
$sql = "SELECT *
FROM users
WHERE username = '''
AND password = 'a029d0df84eb5549c641e04a9ef389e5'";
?>
When the statement is sent to MySQL, the system will display the following error message:
You have an error in your SQL syntax. Check the manual that corresponds to your
MySQL server version for the right syntax to use near 'WHERE username = ''' AND
password = 'a029d0df84eb55
Without any effort, the attacker already knows the two field names (username and password) and the order in which they appear in the query. In addition, the attacker also knows that the data is not filtered correctly (the program does not prompt illegal user names) and escaped (a database error occurs), and the format of the entire WHERE condition is also exposed, so that the attacker can try to manipulate There are records that match the query.
At this point, the attacker has many options. One is to try to fill in a special username so that the query can get a match regardless of whether the username and password match:
myuser' or 'foo' = 'foo' --
Assuming that mypass is used as the password, the entire query will become:
< ?php
$sql = "SELECT *
FROM users
WHERE username = 'myuser' or 'foo' = 'foo' --
AND password = 'a029d0df84eb5549c641e04a9ef389e5'" ;
?>
Fortunately, SQL injection is easy to avoid. As mentioned before, you have to insist on filtering input and escaping output.
Although neither step can be omitted, implementing one of them can eliminate most SQL injection risks. If you just filter the input without escaping the output, you are likely to encounter database errors (legal data may also affect the correct format of the SQL query), but this is also unreliable, and legal data may also change the behavior of the SQL statement. On the other hand, if you escape the output without filtering the input, you can ensure that the data will not affect the format of the SQL statement, and also prevent many common SQL injection attack methods.
Of course, you still have to stick to using these two steps at the same time. How you filter the input depends entirely on the type of input data (see examples in Chapter 1), but escaping the output data for sending to the database simply uses the same function. For MySQL users, you can use the function mysql_real_escape_string( ):
$clean = array();
$mysql = array();
$clean['last_name'] = "O'Reilly";
$mysql['last_name'] = mysql_real_escape_string( $clean['last_name']);
$sql = "INSERT
INTO user (last_name)
VALUES ('{$mysql['last_name']}')";
?>
Try to use escape functions designed for your database. If not, using the addslashes() function is ultimately a better approach.
When all data used to build a SQL statement is properly filtered and escaped, the risk of SQL injection is actually avoided. If you are using a database operation class that supports parameterized queries and placeholders (such as PEAR::DB, PDO, etc.), you will have an extra layer of protection. See the example below using PEAR::DB:
$sql = 'INSERT
INTO user (last_name)
VALUES (?)';
$dbh->query($sql, array($clean['last_name']));
?>
Since the data in the above example cannot directly affect the format of the query statement, the risk of SQL injection is reduced. PEAR::DB will automatically escape according to your database's requirements, so you only need to filter the output.
If you are using parameterized query statements, the input content will only be processed as data. This eliminates the need for escaping, although you might consider it a necessary step if you wish to stick to the escaping output habit. In fact, whether to escape at this time will basically have no impact, because there are no special characters that need to be converted at this time. Parameterized queries provide powerful protection for your program when it comes to preventing SQL injection.
Note: Regarding SQL injection, it must be said that most virtual hosts now turn on the magic_quotes_gpc option. In this case, all client GET and POST data will automatically be processed by addslashes, so at this time, the string SQL injection of values is not feasible, but SQL injection of numeric values should be prevented, such as using functions such as intval() for processing. But if you are writing general software, you need to read the magic_quotes_gpc of the server and process it accordingly.

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c
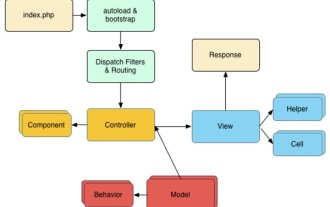 CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP is an open source MVC framework. It makes developing, deploying and maintaining applications much easier. CakePHP has a number of libraries to reduce the overload of most common tasks.
 How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
This tutorial demonstrates how to efficiently process XML documents using PHP. XML (eXtensible Markup Language) is a versatile text-based markup language designed for both human readability and machine parsing. It's commonly used for data storage an
 PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
A string is a sequence of characters, including letters, numbers, and symbols. This tutorial will learn how to calculate the number of vowels in a given string in PHP using different methods. The vowels in English are a, e, i, o, u, and they can be uppercase or lowercase. What is a vowel? Vowels are alphabetic characters that represent a specific pronunciation. There are five vowels in English, including uppercase and lowercase: a, e, i, o, u Example 1 Input: String = "Tutorialspoint" Output: 6 explain The vowels in the string "Tutorialspoint" are u, o, i, a, o, i. There are 6 yuan in total
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 7 PHP Functions I Regret I Didn't Know Before
Nov 13, 2024 am 09:42 AM
7 PHP Functions I Regret I Didn't Know Before
Nov 13, 2024 am 09:42 AM
If you are an experienced PHP developer, you might have the feeling that you’ve been there and done that already.You have developed a significant number of applications, debugged millions of lines of code, and tweaked a bunch of scripts to achieve op



