 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Block SQL Server injection vulnerability in three simple steps_PHP tutorial
Block SQL Server injection vulnerability in three simple steps_PHP tutorial
Block SQL Server injection vulnerability in three simple steps_PHP tutorial
What is SQL injection?
When writing many website programs, they do not judge the legality of user input data, causing security risks in the application. Users can submit a database query code (usually in the browser address bar, accessed through the normal www port), and obtain certain data they want to know based on the results returned by the program. This is the so-called SQL Injection, that is, SQL injection. .
SQL injection modifies the website database through web pages. It is able to add users with administrator rights directly in the database, thereby ultimately gaining system administrator rights. Hackers can use the obtained administrator rights to arbitrarily obtain files on the website or add Trojan horses and various malicious programs to the web page, causing great harm to the website and the netizens who visit the website.
There is a wonderful way to prevent SQL injection
Step 1: Many novices download the SQL universal anti-injection system program from the Internet, and use it in the header of the page that needs to prevent injection to prevent others from performing manual injection testing.
But if you use SQL injection analyzer, you can easily skip the anti-injection system and automatically analyze its injection points. Then it only takes a few minutes for your administrator account and password to be analyzed.
The second step: Regarding the prevention of injection analyzers, the author discovered a simple and effective prevention method through experiments. First we need to know how the SQL injection analyzer works. During the operation, I found that the software was not directed to the "admin" administrator account, but to the permissions (such as flag=1). In this way, no matter how your administrator account changes, you cannot escape detection.
Step 3: Since we can’t escape detection, we will create two accounts, one is an ordinary administrator account, and the other is an account to prevent injection. Why do we say this? The author thinks that if you find an account with the highest authority to create a false impression and attract detection by the software, and the content in this account is more than 1,000 Chinese characters, it will force the software to enter a full load state and even use resources when analyzing this account. Exhausted and crashed. Let's modify the database next.
1. Modify the table structure. Modify the data type of the administrator's account field, changing the text type to the maximum field of 255 (actually it is enough, if you want to make it larger, you can choose the note type), and set the password field in the same way.
2. Modify the table. Set the account with administrator rights in ID1, and enter a large number of Chinese characters (preferably more than 100 characters).
3. Put the real administrator password in any position after ID2 (such as ID549).
We have completed the modification of the database through the above three steps.
Is the modification finished now? In fact, it is not the case. You must understand that the ID1 account you created is actually an account with real permissions. Nowadays, computer processing speed is so fast. If you encounter a software that must calculate it, this is also unsafe. I think most people have already thought of a way at this time. Yes, just write the character limit in the page file where the administrator logs in! Even if the other party uses this account password with thousands of characters, it will be blocked, but the real password can be unrestricted.

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to make Google Maps the default map in iPhone
Apr 17, 2024 pm 07:34 PM
How to make Google Maps the default map in iPhone
Apr 17, 2024 pm 07:34 PM
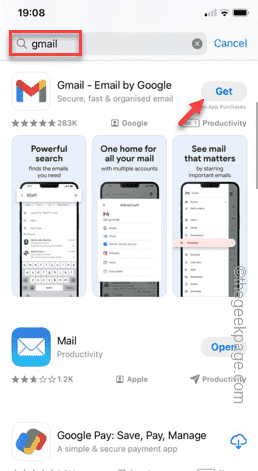
The default map on the iPhone is Maps, Apple's proprietary geolocation provider. Although the map is getting better, it doesn't work well outside the United States. It has nothing to offer compared to Google Maps. In this article, we discuss the feasible steps to use Google Maps to become the default map on your iPhone. How to Make Google Maps the Default Map in iPhone Setting Google Maps as the default map app on your phone is easier than you think. Follow the steps below – Prerequisite steps – You must have Gmail installed on your phone. Step 1 – Open the AppStore. Step 2 – Search for “Gmail”. Step 3 – Click next to Gmail app
 How to solve the problem that the object named already exists in the sqlserver database
Apr 05, 2024 pm 09:42 PM
How to solve the problem that the object named already exists in the sqlserver database
Apr 05, 2024 pm 09:42 PM
For objects with the same name that already exist in the SQL Server database, the following steps need to be taken: Confirm the object type (table, view, stored procedure). IF NOT EXISTS can be used to skip creation if the object is empty. If the object has data, use a different name or modify the structure. Use DROP to delete existing objects (use caution, backup recommended). Check for schema changes to make sure there are no references to deleted or renamed objects.
 How to import mdf file into sqlserver
Apr 08, 2024 am 11:41 AM
How to import mdf file into sqlserver
Apr 08, 2024 am 11:41 AM
The import steps are as follows: Copy the MDF file to SQL Server's data directory (usually C:\Program Files\Microsoft SQL Server\MSSQL\DATA). In SQL Server Management Studio (SSMS), open the database and select Attach. Click the Add button and select the MDF file. Confirm the database name and click the OK button.
 What is the difference between HQL and SQL in Hibernate framework?
Apr 17, 2024 pm 02:57 PM
What is the difference between HQL and SQL in Hibernate framework?
Apr 17, 2024 pm 02:57 PM
HQL and SQL are compared in the Hibernate framework: HQL (1. Object-oriented syntax, 2. Database-independent queries, 3. Type safety), while SQL directly operates the database (1. Database-independent standards, 2. Complex executable queries and data manipulation).
 What to do if the sqlserver service cannot be started
Apr 05, 2024 pm 10:00 PM
What to do if the sqlserver service cannot be started
Apr 05, 2024 pm 10:00 PM
When the SQL Server service fails to start, here are some steps to resolve: Check the error log to determine the root cause. Make sure the service account has permission to start the service. Check whether dependency services are running. Disable antivirus software. Repair SQL Server installation. If the repair does not work, reinstall SQL Server.
 How to check sqlserver port number
Apr 05, 2024 pm 09:57 PM
How to check sqlserver port number
Apr 05, 2024 pm 09:57 PM
To view the SQL Server port number: Open SSMS and connect to the server. Find the server name in Object Explorer, right-click it and select Properties. In the Connection tab, view the TCP Port field.
 How to recover accidentally deleted database in sqlserver
Apr 05, 2024 pm 10:39 PM
How to recover accidentally deleted database in sqlserver
Apr 05, 2024 pm 10:39 PM
If you accidentally delete a SQL Server database, you can take the following steps to recover: stop database activity; back up log files; check database logs; recovery options: restore from backup; restore from transaction log; use DBCC CHECKDB; use third-party tools. Please back up your database regularly and enable transaction logging to prevent data loss.
 Where is the sqlserver database?
Apr 05, 2024 pm 08:21 PM
Where is the sqlserver database?
Apr 05, 2024 pm 08:21 PM
SQL Server database files are usually stored in the following default location: Windows: C:\Program Files\Microsoft SQL Server\MSSQL\DATALinux: /var/opt/mssql/data The database file location can be customized by modifying the database file path setting.





