How to attack through Session file? _PHP Tutorial
How to attack through Session file?
PHP 4 or newer versions provide support for sessions. Its main function is to save state information between pages in the PHP program. For example, when a user logs in to the website, the fact that he logged in and the information about who logged in to the website will be saved in the session. When he browses around the website, all PHP code can obtain this state. information.
In fact, when a session is started (actually set in the configuration file to automatically start on the first request), a random "session id" is generated, which if the remote browser always submits when sending the request If this "session id" is used, the session will always be maintained. This is easily accomplished via cookies, or by submitting a form variable (containing the "session id") on each page. PHP programs can use session to register a special variable. Its value will be stored in the session file after each PHP script ends, and will also be loaded into the variable before each PHP script starts. Here is a simple example:
<?php
$session_auth = "shaun"; session_register("session_auth"); // Register $session_auth as a session variable ?> |
New versions of PHP will automatically set the value of "$session_auth" to "shaun". If they are modified, future scripts will automatically accept the modified values, which is really good for the stateless Web. tools, but we should also be careful.
| <?php if (!empty($session_auth)) // Grant access to site here ?> |
| <?php if (!empty($session_auth)) // Grant access to site here ?> |
The above code assumes that if "$session_auth" is assigned a value, it is assigned from the session, not from user input. If the attacker assigns the value through form input, he can gain access to the site. Note that the attacker must register the variable in the session before using this attack method. Once the variable is put into the session, it will overwrite any form input.
Session data is generally saved in a file (the location is configurable, usually "/tmp"). The file name is generally in the form of "sess_
The Session mechanism also provides another convenience for attackers to save their own input in files on the remote system. For the above example, the attacker needs to place a file containing PHP code on the remote system. If this cannot be done using file upload, he usually uses session to assign a value to a variable according to his own wishes, and then guesses the session file. The location, and he knows that the file name is "php
In addition, the attacker can arbitrarily specify a "session id" (such as "hello"), and then use this "session id" to create a session file (such as "/tmp/sess_hello"), but the "session id" can only be letters and numbers. combination.
How to attack through data types?
PHP has loose data types, and the types of variables depend on the context in which they are located. For example: "$hello" starts as a string variable with a value of "", but when evaluated, it becomes an integer variable "0", which may sometimes lead to unexpected results. If the value of "$hello" is different between "000" and "0", the result returned by empty() will not be true.
Arrays in PHP are associative arrays, that is to say, the index of the array is of string type. This means that "$hello["000"]" and "$hello[0]" are also different.
The above issues should be carefully considered when developing programs. For example, we should not test whether a variable is "0" in one place and use empty() to verify it in another place.
How to attack through error-prone functions? The following is a more detailed list of error-prone functions:
<PHP code execution>
require(): Read the contents of the specified file and interpret it as PHP code
include(): Same as above
eval(): Execute the given string as PHP code
preg_replace(): When used with the "/e" switch, the replacement string will be interpreted as PHP code
<Command execution>
exec(): Execute the specified command and return the last line of the execution result
passthru(): Execute the specified command and return all results to the client browser
``: Execute the specified command and return all results to an array
system(): Same as passthru(), but does not process binary data
popen(): Execute the specified command and connect the input or output to the PHP file descriptor
<File leak>
fopen(): Open a file and correspond to a PHP file descriptor
readfile(): Read the content of the file and then output it to the client browser
file(): Read the entire file content into an array
How to enhance the security of PHP?
All the attacks we introduced above can be implemented well with the default installation of PHP4, but the configuration of PHP is very flexible. By configuring some PHP options, it is entirely possible for us to resist some of these attacks. Below we classify some configurations according to the difficulty of implementation:
*Low difficulty
**Medium and low difficulty
***Medium to high difficulty
****High difficulty
If you use all the options provided by PHP, then your PHP will be very safe, even with third-party code, because many of its features are no longer available.
****Set "register_globals" to "off"
This option will disable PHP from creating global variables for user input, that is, if the user submits the form variable "hello", PHP will not create "$hello", but only create "HTTP_GET/POST_VARS['hello']". This is an extremely important option in PHP. Turning off this option will bring great inconvenience to programming.
***Set "safe_mode" to "on"
Turning this option on will add the following restrictions:
1. Limit which commands can be executed
2. Limit which functions can be used
3. File access restrictions based on script ownership and target file ownership
4. Disable file upload function
This is a "great" option for ISPs, and it also greatly improves PHP security.
** Set "open_basedir"
This option can prohibit file operations outside the specified directory, effectively eliminating attacks on local files or remote files by include(), but you still need to pay attention to attacks on file uploads and session files.
** Set "display_errors" to "off" and set "log_errors" to "on"
This option disables error messages from being displayed on the web page and instead records them in a log file, which can effectively resist attackers from detecting functions in the target script.
* Set "allow_url_fopen" to "off"
This option disables remote file functionality.

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
To work with date and time in cakephp4, we are going to make use of the available FrozenTime class.
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
Validator can be created by adding the following two lines in the controller.
 CakePHP File upload
Sep 10, 2024 pm 05:27 PM
CakePHP File upload
Sep 10, 2024 pm 05:27 PM
To work on file upload we are going to use the form helper. Here, is an example for file upload.
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c
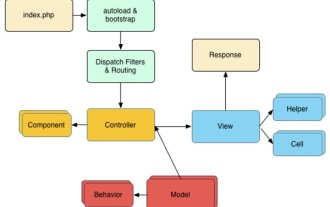 CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP is an open source MVC framework. It makes developing, deploying and maintaining applications much easier. CakePHP has a number of libraries to reduce the overload of most common tasks.
 How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
This tutorial demonstrates how to efficiently process XML documents using PHP. XML (eXtensible Markup Language) is a versatile text-based markup language designed for both human readability and machine parsing. It's commonly used for data storage an




