 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 How to prevent SQL injection attacks in ASP.NET website programs_PHP tutorial
How to prevent SQL injection attacks in ASP.NET website programs_PHP tutorial
How to prevent SQL injection attacks in ASP.NET website programs_PHP tutorial
1. What is a SQL injection attack?
The so-called SQL injection attack means that the attacker inserts SQL commands into the input field of the Web form or the query string of the page request to trick the server into executing malicious SQL command. In some forms, the content entered by the user is directly used to construct (or affect) dynamic SQL commands, or is used as input parameters for stored procedures. Such forms are particularly vulnerable to SQL injection attacks. Common SQL injection attack processes include:
⑴ An ASP.NET web application has a login page. This login page controls whether the user has permission to access the application. It requires the user to enter a name and password.
⑵ The content entered on the login page will be directly used to construct dynamic SQL commands, or directly used as parameters of stored procedures. The following is an example of an ASP.NET application construction query:
System.Text.StringBuilder query = new System.Text.StringBuilder(
"SELECT * from Users WHERE login = '")
. Append(txtLogin.Text).Append("' AND password='")
.Append(txtPassword.Text).Append("'");
⑶ The attacker is in the user name And enter something like "' or '1'='1" in the password input box.
⑷ After the content input by the user is submitted to the server, the server runs the above ASP.NET code to construct an SQL command to query the user. However, because the content input by the attacker is very special, the final SQL command becomes :SELECT * from Users WHERE login = '' or '1'='1' AND password = '' or '1'='1'.
⑸ The server executes a query or stored procedure to compare the identity information entered by the user with the identity information saved in the server.
⑹ Since the SQL command has actually been modified by an injection attack, the user's identity cannot be truly verified, so the system will incorrectly authorize the attacker.
If an attacker knows that the application will directly use the content entered in the form for identity verification queries, he will try to enter some special SQL strings to tamper with the query to change its original functionality and trick the system into granting access. permissions.
Depending on the system environment, the damage that an attacker may cause is also different, which is mainly determined by the security permissions of the application to access the database. If the user's account has administrator or other relatively advanced rights, the attacker may perform various operations on the database tables that he wants to do, including adding, deleting or updating data, or even directly deleting the table.
2. How to prevent it?
Fortunately, it is not particularly difficult to prevent ASP.NET applications from being invaded by SQL injection attacks. As long as you use the content entered in the form to construct SQL Before issuing the command, just filter all the input content. Filtering input can be done in a variety of ways.
⑴ For dynamically constructing SQL queries, the following technology can be used:
First: Replace single quotes, that is, change all single quotes that appear alone into two single quotes to prevent The attacker modifies the meaning of SQL commands. Looking at the previous example again, "SELECT * from Users WHERE login = ''' or ''1''=''1' AND password = ''' or ''1''=''1'" will obviously get the same "SELECT * from Users WHERE login = '' or '1'='1' AND password = '' or '1'='1'" different results.
Second: Remove all hyphens in user input to prevent attackers from constructing queries such as "SELECT * from Users WHERE login = 'mas' -- AND password =''". Because the second half of this type of query has been commented out and is no longer valid, the attacker only needs to know a legitimate user login name and does not need to know the user's password to successfully gain access.
Third: Restrict the permissions of the database account used to execute queries. Use different user accounts to perform query, insert, update, and delete operations. By isolating the operations that can be performed by different accounts, it prevents the place originally used to execute the SELECT command from being used to execute the INSERT, UPDATE or DELETE command.
⑵ Use stored procedures to execute all queries. The way SQL parameters are passed will prevent attackers from using single quotes and hyphens to carry out attacks. In addition, it also allows database permissions to be restricted to only allow specific stored procedures to execute. All user input must comply with the security context of the called stored procedure, so that injection attacks are difficult to occur.
⑶ Limit the length of form or query string input. If the user's login name only has a maximum of 10 characters, do not accept more than 10 characters entered in the form. This will greatly increase the difficulty for attackers to insert harmful code into SQL commands.
⑷ Check the legality of user input and make sure that the input content only contains legal data. Data inspection should be performed on both the client and server sides - server-side validation is performed to compensate for the fragile security of the client-side validation mechanism.
On the client side, it is entirely possible for an attacker to obtain the source code of the web page, modify the script that verifies legality (or delete the script directly), and then submit the illegal content to the server through the modified form. Therefore, the only way to ensure that the verification operation has actually been performed is to perform verification on the server side as well. You can use many of the built-in validation objects, such as RegularExpressionValidator, which can automatically generate client-side scripts for validation, and of course you can also insert server-side method calls. If you can't find a ready-made validation object, you can create one yourself through CustomValidator.
⑸ Encrypt and save user login name, password and other data. Encrypting the data entered by the user and then comparing it with the data saved in the database is equivalent to "sterilizing" the data entered by the user. The data entered by the user no longer has any special meaning to the database, so it Prevents attackers from injecting SQL commands. The System.Web.Security.FormsAuthentication class has a HashPasswordForStoringInConfigFile, which is very suitable for sanitizing input data.
⑹ Check the number of records returned by the query that extracted the data. If the program only requires one record to be returned, but the actual returned record is more than one row, it will be treated as an error.

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
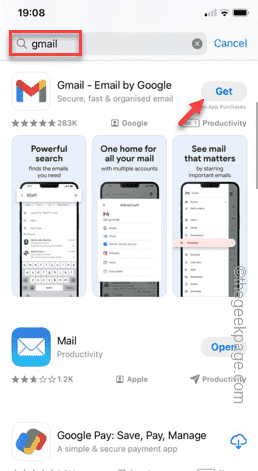 How to make Google Maps the default map in iPhone
Apr 17, 2024 pm 07:34 PM
How to make Google Maps the default map in iPhone
Apr 17, 2024 pm 07:34 PM
The default map on the iPhone is Maps, Apple's proprietary geolocation provider. Although the map is getting better, it doesn't work well outside the United States. It has nothing to offer compared to Google Maps. In this article, we discuss the feasible steps to use Google Maps to become the default map on your iPhone. How to Make Google Maps the Default Map in iPhone Setting Google Maps as the default map app on your phone is easier than you think. Follow the steps below – Prerequisite steps – You must have Gmail installed on your phone. Step 1 – Open the AppStore. Step 2 – Search for “Gmail”. Step 3 – Click next to Gmail app
 How to write a novel in the Tomato Free Novel app. Share the tutorial on how to write a novel in Tomato Novel.
Mar 28, 2024 pm 12:50 PM
How to write a novel in the Tomato Free Novel app. Share the tutorial on how to write a novel in Tomato Novel.
Mar 28, 2024 pm 12:50 PM
Tomato Novel is a very popular novel reading software. We often have new novels and comics to read in Tomato Novel. Every novel and comic is very interesting. Many friends also want to write novels. Earn pocket money and edit the content of the novel you want to write into text. So how do we write the novel in it? My friends don’t know, so let’s go to this site together. Let’s take some time to look at an introduction to how to write a novel. Share the Tomato novel tutorial on how to write a novel. 1. First open the Tomato free novel app on your mobile phone and click on Personal Center - Writer Center. 2. Jump to the Tomato Writer Assistant page - click on Create a new book at the end of the novel.
 What is the difference between HQL and SQL in Hibernate framework?
Apr 17, 2024 pm 02:57 PM
What is the difference between HQL and SQL in Hibernate framework?
Apr 17, 2024 pm 02:57 PM
HQL and SQL are compared in the Hibernate framework: HQL (1. Object-oriented syntax, 2. Database-independent queries, 3. Type safety), while SQL directly operates the database (1. Database-independent standards, 2. Complex executable queries and data manipulation).
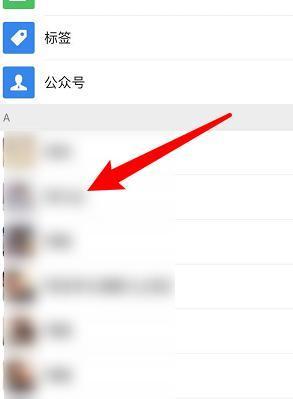 How to recover deleted contacts on WeChat (simple tutorial tells you how to recover deleted contacts)
May 01, 2024 pm 12:01 PM
How to recover deleted contacts on WeChat (simple tutorial tells you how to recover deleted contacts)
May 01, 2024 pm 12:01 PM
Unfortunately, people often delete certain contacts accidentally for some reasons. WeChat is a widely used social software. To help users solve this problem, this article will introduce how to retrieve deleted contacts in a simple way. 1. Understand the WeChat contact deletion mechanism. This provides us with the possibility to retrieve deleted contacts. The contact deletion mechanism in WeChat removes them from the address book, but does not delete them completely. 2. Use WeChat’s built-in “Contact Book Recovery” function. WeChat provides “Contact Book Recovery” to save time and energy. Users can quickly retrieve previously deleted contacts through this function. 3. Enter the WeChat settings page and click the lower right corner, open the WeChat application "Me" and click the settings icon in the upper right corner to enter the settings page.
 Clock app missing in iPhone: How to fix it
May 03, 2024 pm 09:19 PM
Clock app missing in iPhone: How to fix it
May 03, 2024 pm 09:19 PM
Is the clock app missing from your phone? The date and time will still appear on your iPhone's status bar. However, without the Clock app, you won’t be able to use world clock, stopwatch, alarm clock, and many other features. Therefore, fixing missing clock app should be at the top of your to-do list. These solutions can help you resolve this issue. Fix 1 – Place the Clock App If you mistakenly removed the Clock app from your home screen, you can put the Clock app back in its place. Step 1 – Unlock your iPhone and start swiping to the left until you reach the App Library page. Step 2 – Next, search for “clock” in the search box. Step 3 – When you see “Clock” below in the search results, press and hold it and
 Quickly master: How to open two WeChat accounts on Huawei mobile phones revealed!
Mar 23, 2024 am 10:42 AM
Quickly master: How to open two WeChat accounts on Huawei mobile phones revealed!
Mar 23, 2024 am 10:42 AM
In today's society, mobile phones have become an indispensable part of our lives. As an important tool for our daily communication, work, and life, WeChat is often used. However, it may be necessary to separate two WeChat accounts when handling different transactions, which requires the mobile phone to support logging in to two WeChat accounts at the same time. As a well-known domestic brand, Huawei mobile phones are used by many people. So what is the method to open two WeChat accounts on Huawei mobile phones? Let’s reveal the secret of this method. First of all, you need to use two WeChat accounts at the same time on your Huawei mobile phone. The easiest way is to
 The secret of hatching mobile dragon eggs is revealed (step by step to teach you how to successfully hatch mobile dragon eggs)
May 04, 2024 pm 06:01 PM
The secret of hatching mobile dragon eggs is revealed (step by step to teach you how to successfully hatch mobile dragon eggs)
May 04, 2024 pm 06:01 PM
Mobile games have become an integral part of people's lives with the development of technology. It has attracted the attention of many players with its cute dragon egg image and interesting hatching process, and one of the games that has attracted much attention is the mobile version of Dragon Egg. To help players better cultivate and grow their own dragons in the game, this article will introduce to you how to hatch dragon eggs in the mobile version. 1. Choose the appropriate type of dragon egg. Players need to carefully choose the type of dragon egg that they like and suit themselves, based on the different types of dragon egg attributes and abilities provided in the game. 2. Upgrade the level of the incubation machine. Players need to improve the level of the incubation machine by completing tasks and collecting props. The level of the incubation machine determines the hatching speed and hatching success rate. 3. Collect the resources required for hatching. Players need to be in the game
 How to set font size on mobile phone (easily adjust font size on mobile phone)
May 07, 2024 pm 03:34 PM
How to set font size on mobile phone (easily adjust font size on mobile phone)
May 07, 2024 pm 03:34 PM
Setting font size has become an important personalization requirement as mobile phones become an important tool in people's daily lives. In order to meet the needs of different users, this article will introduce how to improve the mobile phone use experience and adjust the font size of the mobile phone through simple operations. Why do you need to adjust the font size of your mobile phone - Adjusting the font size can make the text clearer and easier to read - Suitable for the reading needs of users of different ages - Convenient for users with poor vision to use the font size setting function of the mobile phone system - How to enter the system settings interface - In Find and enter the "Display" option in the settings interface - find the "Font Size" option and adjust it. Adjust the font size with a third-party application - download and install an application that supports font size adjustment - open the application and enter the relevant settings interface - according to the individual





