 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Common security vulnerabilities in parsing web file operations (directory and file name detection vulnerabilities)_PHP tutorial
Common security vulnerabilities in parsing web file operations (directory and file name detection vulnerabilities)_PHP tutorial
Common security vulnerabilities in parsing web file operations (directory and file name detection vulnerabilities)_PHP tutorial
When doing web development, we often do code inspections. Many times, we will randomly check some core functions or logic where loopholes often appear. As the technical team grows, the team members’ skills become increasingly mature. Common fool-type SQL injection vulnerabilities and XSS vulnerabilities. There will be fewer and fewer, but we will also find some emerging covert vulnerabilities that occasionally appear. These vulnerabilities mostly come from developers' insufficient design of a function or common module functions, leaving problems left behind. In the past, we were able to complete some functional modules, but now the requirement is to complete the modules in a safe and correct way. Next, I will share some common functional modules that cause vulnerabilities due to design reasons. Next, let’s first look at the file-reading function vulnerability.
Let’s first look at the following piece of code, which contains different files through the user’s input of different directories
///Read module name
$mod = isset($_GET['m'])?trim($_GET['m']):'index';
///Filter the directory name to prevent jumping to the upper-level directory
$mod = str_replace("..",".",$mod);
///Get the file
$file = " /home/www/blog/".$mod.".php";
///Include file
@include($file);
This code may be in Many friends have encountered this in their programs, and it is very easy for newcomers to have such problems. I remember when I encountered this code during a walkthrough, I asked, what can you do in terms of security of this code?
Answer: 1. The ".." directory is replaced, so any .. directory in the module name passed in by the user will be replaced.
2. Construct the spliced file name. There are restrictions on the front directory and restrictions on the extension at the back. The included files will be limited to that directory.
Does this code really achieve directory security detection?
Let’s test what the result will be if $mod passes this value in.

$mod enters ?mod=…%2F…%2F…%2F…%2Fetc%2Fpasswd%00 through construction, we see that the result will be:

Actually include("/etc/passwd") file.
How did you escape my parameter restrictions?
First of all: It is not a good method to use parameter filtering type to limit user input. The general rule is: if it can be tested, do not replace it. As long as it fails the test, pass it directly. Lose! This is one of our principles. There are countless filtering failures. Let’s take a look at the actual process.
1. Enter "…/…/…/" by replacing ".." with "."
2. The result is "../../../" and it becomes Got this
Some friends will ask, would it be better if I just replace it with spaces? It can indeed be replaced in this one. But it doesn’t mean that you can replace everything with spaces in the future. Let’s take another example. For example: someone replaced the javascript in the string. The code is as follows:
......
$msg = str_replace("javascript"," ",$msg);
It seems that javascript will not appear. However, if you enter: jjavascriptavascript to replace, it will replace the middle one and become empty. The "j" in front and the following one will form a new javascript.
Secondly: Let’s see how to escape the .php restriction behind it. The parameters entered by the user are: "etc/passwd
1. What is whitelist restriction?
Copy code
The code is as follows:
For example:
$mod = isset($_GET['m'])?trim($_GET['m']):'index'; ///After reading the module name
If the mod variable value range is an enumeration type:
if(!in_array($mod,array('user','index','add','edit'))) exit('err! !!');
$mod is completely restricted and can only be in this array, so cruel! ! ! !
2. How to implement whitelist restrictions
Through the example just now, we know that if it is an enumeration type, just put the value directly into the list. However, sometimes, this is not enough. We have another whitelist restriction method. It is to limit the character range
For example:
$mod = isset($_GET ['m'])?trim($_GET['m']):'index'; ///After reading the module name
I know that $mod is a directory name. For general sites, it is a letter Underline numbers and the like.
if(!preg_match(“/^w+$/”,$mod)) exit(‘err!!!’);
The characters can only be: [A-Za-z0-9_] these. Cruel enough! ! !
Summary: Have you discovered that the whitelist restriction method is actually very simple to do? If you know what is needed in that place, input detection is necessary It's those. Moreover, it is much simpler to detect what you already know than to replace those unknown characters. Okay, let’s stop here first. The correct way to solve the problem will make the file simpler and safer! !

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1378
1378
 52
52
 Ten limitations of artificial intelligence
Apr 26, 2024 pm 05:52 PM
Ten limitations of artificial intelligence
Apr 26, 2024 pm 05:52 PM
In the field of technological innovation, artificial intelligence (AI) is one of the most transformative and promising developments of our time. Artificial intelligence has revolutionized many industries, from healthcare and finance to transportation and entertainment, with its ability to analyze large amounts of data, learn from patterns, and make intelligent decisions. However, despite its remarkable progress, AI also faces significant limitations and challenges that prevent it from reaching its full potential. In this article, we will delve into the top ten limitations of artificial intelligence, revealing the limitations faced by developers, researchers, and practitioners in this field. By understanding these challenges, it is possible to navigate the complexities of AI development, reduce risks, and pave the way for responsible and ethical advancement of AI technology. Limited data availability: The development of artificial intelligence depends on data
 Four recommended AI-assisted programming tools
Apr 22, 2024 pm 05:34 PM
Four recommended AI-assisted programming tools
Apr 22, 2024 pm 05:34 PM
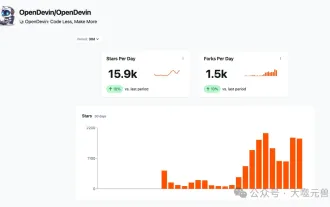
This AI-assisted programming tool has unearthed a large number of useful AI-assisted programming tools in this stage of rapid AI development. AI-assisted programming tools can improve development efficiency, improve code quality, and reduce bug rates. They are important assistants in the modern software development process. Today Dayao will share with you 4 AI-assisted programming tools (and all support C# language). I hope it will be helpful to everyone. https://github.com/YSGStudyHards/DotNetGuide1.GitHubCopilotGitHubCopilot is an AI coding assistant that helps you write code faster and with less effort, so you can focus more on problem solving and collaboration. Git
 Which AI programmer is the best? Explore the potential of Devin, Tongyi Lingma and SWE-agent
Apr 07, 2024 am 09:10 AM
Which AI programmer is the best? Explore the potential of Devin, Tongyi Lingma and SWE-agent
Apr 07, 2024 am 09:10 AM
On March 3, 2022, less than a month after the birth of the world's first AI programmer Devin, the NLP team of Princeton University developed an open source AI programmer SWE-agent. It leverages the GPT-4 model to automatically resolve issues in GitHub repositories. SWE-agent's performance on the SWE-bench test set is similar to Devin, taking an average of 93 seconds and solving 12.29% of the problems. By interacting with a dedicated terminal, SWE-agent can open and search file contents, use automatic syntax checking, edit specific lines, and write and execute tests. (Note: The above content is a slight adjustment of the original content, but the key information in the original text is retained and does not exceed the specified word limit.) SWE-A
 MIT's latest masterpiece: using GPT-3.5 to solve the problem of time series anomaly detection
Jun 08, 2024 pm 06:09 PM
MIT's latest masterpiece: using GPT-3.5 to solve the problem of time series anomaly detection
Jun 08, 2024 pm 06:09 PM
Today I would like to introduce to you an article published by MIT last week, using GPT-3.5-turbo to solve the problem of time series anomaly detection, and initially verifying the effectiveness of LLM in time series anomaly detection. There is no finetune in the whole process, and GPT-3.5-turbo is used directly for anomaly detection. The core of this article is how to convert time series into input that can be recognized by GPT-3.5-turbo, and how to design prompts or pipelines to let LLM solve the anomaly detection task. Let me introduce this work to you in detail. Image paper title: Largelanguagemodelscanbezero-shotanomalydete
 Learn how to develop mobile applications using Go language
Mar 28, 2024 pm 10:00 PM
Learn how to develop mobile applications using Go language
Mar 28, 2024 pm 10:00 PM
Go language development mobile application tutorial As the mobile application market continues to boom, more and more developers are beginning to explore how to use Go language to develop mobile applications. As a simple and efficient programming language, Go language has also shown strong potential in mobile application development. This article will introduce in detail how to use Go language to develop mobile applications, and attach specific code examples to help readers get started quickly and start developing their own mobile applications. 1. Preparation Before starting, we need to prepare the development environment and tools. head
 Improved detection algorithm: for target detection in high-resolution optical remote sensing images
Jun 06, 2024 pm 12:33 PM
Improved detection algorithm: for target detection in high-resolution optical remote sensing images
Jun 06, 2024 pm 12:33 PM
01 Outlook Summary Currently, it is difficult to achieve an appropriate balance between detection efficiency and detection results. We have developed an enhanced YOLOv5 algorithm for target detection in high-resolution optical remote sensing images, using multi-layer feature pyramids, multi-detection head strategies and hybrid attention modules to improve the effect of the target detection network in optical remote sensing images. According to the SIMD data set, the mAP of the new algorithm is 2.2% better than YOLOv5 and 8.48% better than YOLOX, achieving a better balance between detection results and speed. 02 Background & Motivation With the rapid development of remote sensing technology, high-resolution optical remote sensing images have been used to describe many objects on the earth’s surface, including aircraft, cars, buildings, etc. Object detection in the interpretation of remote sensing images
 Analysis of the meaning and usage of midpoint in PHP
Mar 27, 2024 pm 08:57 PM
Analysis of the meaning and usage of midpoint in PHP
Mar 27, 2024 pm 08:57 PM
[Analysis of the meaning and usage of midpoint in PHP] In PHP, midpoint (.) is a commonly used operator used to connect two strings or properties or methods of objects. In this article, we’ll take a deep dive into the meaning and usage of midpoints in PHP, illustrating them with concrete code examples. 1. Connect string midpoint operator. The most common usage in PHP is to connect two strings. By placing . between two strings, you can splice them together to form a new string. $string1=&qu
 Java how to loop through a folder and get all file names
Mar 29, 2024 pm 01:24 PM
Java how to loop through a folder and get all file names
Mar 29, 2024 pm 01:24 PM
Java is a popular programming language with powerful file handling capabilities. In Java, traversing a folder and getting all file names is a common operation, which can help us quickly locate and process files in a specific directory. This article will introduce how to implement a method of traversing a folder and getting all file names in Java, and provide specific code examples. 1. Use the recursive method to traverse the folder. We can use the recursive method to traverse the folder. The recursive method is a way of calling itself, which can effectively traverse the folder.



