 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 In-depth analysis of ThinkPHP's RBAC (role-based access control)_PHP tutorial
In-depth analysis of ThinkPHP's RBAC (role-based access control)_PHP tutorial
In-depth analysis of ThinkPHP's RBAC (role-based access control)_PHP tutorial
1. What is RBAC
Role-Based Access Control (Role-Based Access Control) is a promising alternative to traditional access control (discretionary access, mandatory access) instead received widespread attention.
In RBAC, permissions are associated with roles, and users gain permissions from these roles by becoming members of the appropriate roles. This greatly simplifies the management of permissions.
In an organization, roles are created to complete various tasks, and users are assigned corresponding roles based on their responsibilities and qualifications. Users can be easily assigned from one role to another. Roles can be granted new permissions based on new requirements and system integration, and permissions can also be reclaimed from a role as needed. Character-to-character relationships can be established to encompass a wider range of objective circumstances.
2. RBAC in ThinkPHP
Let’s first look at the data tables used in the official examples. Permission control is implemented through 5 tables, which are defined as follows:
RBAC uses 5 data tables
think_user (user table)
think_role (user grouping table)
think_node (operation node)
think_role_user (correspondence between users and user groups)
think_access (Correspondence between each operation and user group)

User table

Role table, what roles are there, this role is associated with the corresponding userid user

According to the id in the user table, the corresponding role id is associated, that is, the user is assigned a role. For example, the role with userid 3 is 2. According to the role role table, 7 represents the role of the employee

access table, permission table, for example, the role id is 2, which is the employee's permissions, and the corresponding node can be

The node table represents the applications-modules-module methods and defines a relationship between them. For example, the noteid of 30 is the Public module, and the noteid of 31 and 32 , Methods 33 and 34 add, insert, edit, and update all belong to Public. The test method with noteid 85 belongs to the method under the Game module with noteid 84.
3. Detailed explanation of config configuration file
Let’s take a look at the config file in the official example of thinkphp:
array(
'APP_AUTOLOAD_PATH'=>'@.TagLib',
'SESSION_AUTO_START'=>true,
'USER_AUTH_ON' => ;true,
‘USER_AUTH_TYPE ' 'USER_AUTH_KEY' =>'authId', //Default authentication type 1 Login authentication 2 Real-time authentication
=>'administrator', does not require the authentication module > 'Not_auth_action' = & gt; '', // The default does not require the authentication operation
'reques_Auth_ACTION' = & GT; '', // The authentication operation is required
'guest_auth_on' = & gt; / false, / / / Whether to open tourists authorized Visit
'guest_auth_id' = & gt; 0, // The user's user ID
'db_like_fields' = & gt;' title | remark ',
' rbac_role_table '= & gt;' think_role ',
' RBAC_USER_TABLE' =>'think_role_user',
'RBAC_ACCESS_TABLE' =>'think_access',
'RBAC_NODE_TABLE' =>'think_node',
'SHOW_PAGE_TRACE'=>1//Show debugging information
);
You should understand most of it by reading the comments. The Public module does not require authentication. The reason is very simple. Before logging in, everyone is a guest. If the login page also requires permissions, where can I log in? Right, haha. The default gateway address means that the authentication failed and you do not have permission to jump here and log in again. ADMIN_AUTH_KEY represents super administrator permissions. If you create a user named admin in the user table, then this user is the super administrator. There is no need to assign permissions to it. It has all permissions. Why should you set up such an administrator? Because when If you assign the wrong permissions, it can easily cause confusion in the system permissions, making it impossible for everyone to access. At this time, the super administrator will come.
4. Several important methods of the RBAC class
authenticate($map,$model=") method passes in the conditions for querying users and the MODEL of the user table The return array contains the user's information
The saveAccessList($authId=null) method passes in the user's ID. This method does not return a value, but only sets the value of $_SESSION['_ACCESS_LIST'], which contains all the user groups corresponding to the user. All nodes that have permission to operate $_SESSION['_ACCESS_LIST']['project name']['module name']['operation name']. In the future, judging permissions is to judge whether the current project, module and operation are in $_SESSION[' _ACCESS_LIST']. The
checkAccess() method detects whether the current module and operation require verification and returns a bool type.
checkLogin() method detects login.
AccessDecision($appName=APP_NAME) method is to detect the current project module Whether the operation is in the $_SESSION['_ACCESS_LIST'] array, that is, in the $_SESSION['_ACCESS_LIST'] array $_SESSION['_ACCESS_LIST']['current operation']['current module']['current operation' ] exists. If it exists, it means there is permission. Otherwise, the
getAccessList($authId) method returns the value of the permission list $_SESSION['_ACCESS_LIST'].
http://www.bkjia.com/PHPjc/327598.html

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
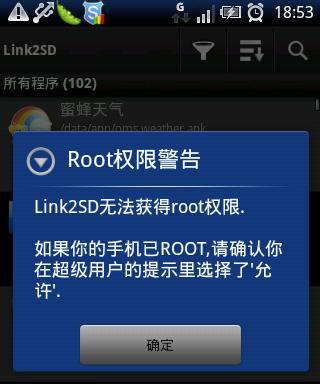 Enable root permissions with one click (quickly obtain root permissions)
Jun 02, 2024 pm 05:32 PM
Enable root permissions with one click (quickly obtain root permissions)
Jun 02, 2024 pm 05:32 PM
It allows users to perform more in-depth operations and customization of the system. Root permission is an administrator permission in the Android system. Obtaining root privileges usually requires a series of tedious steps, which may not be very friendly to ordinary users, however. By enabling root permissions with one click, this article will introduce a simple and effective method to help users easily obtain system permissions. Understand the importance and risks of root permissions and have greater freedom. Root permissions allow users to fully control the mobile phone system. Strengthen security controls, customize themes, and users can delete pre-installed applications. For example, accidentally deleting system files causing system crashes, excessive use of root privileges, and inadvertent installation of malware are also risky, however. Before using root privileges
 How many characters are there in Blazlan Chaos Effect?
Mar 21, 2024 pm 10:56 PM
How many characters are there in Blazlan Chaos Effect?
Mar 21, 2024 pm 10:56 PM
Blue Wings Chaos Effect features a diverse cast of characters, each with a unique identity and backstory. For this reason, the editor has specially compiled an introduction to the characters of BlazBlue Chaos Effect for all players. How many characters are there in BlazBlue Chaos Effect? Answer: There are 7 characters. 1. [God of Death] Ragnar Chad Bradedge (nicknamed RG, Nissan), his brother and sister were raised by church nuns. One day, one of the six heroes of the villain broke in, killed the nuns, and burned them down. Church, took his sister away, leaving behind his younger brother "The Weapon of Things" Ice Sword Snow Girl. 2. Noel Vermillion The adopted daughter of the Vermillion family looks almost the same as Ragnar's sister. After graduation, he joined the governing body as secretary to Ragnar's younger brother. 3. λ-11 is collectively known as Lambda and Eleventh Sister. After the original developer gave up, Kokonoe rescued and
 How to run thinkphp project
Apr 09, 2024 pm 05:33 PM
How to run thinkphp project
Apr 09, 2024 pm 05:33 PM
To run the ThinkPHP project, you need to: install Composer; use Composer to create the project; enter the project directory and execute php bin/console serve; visit http://localhost:8000 to view the welcome page.
 There are several versions of thinkphp
Apr 09, 2024 pm 06:09 PM
There are several versions of thinkphp
Apr 09, 2024 pm 06:09 PM
ThinkPHP has multiple versions designed for different PHP versions. Major versions include 3.2, 5.0, 5.1, and 6.0, while minor versions are used to fix bugs and provide new features. The latest stable version is ThinkPHP 6.0.16. When choosing a version, consider the PHP version, feature requirements, and community support. It is recommended to use the latest stable version for best performance and support.
 How to run thinkphp
Apr 09, 2024 pm 05:39 PM
How to run thinkphp
Apr 09, 2024 pm 05:39 PM
Steps to run ThinkPHP Framework locally: Download and unzip ThinkPHP Framework to a local directory. Create a virtual host (optional) pointing to the ThinkPHP root directory. Configure database connection parameters. Start the web server. Initialize the ThinkPHP application. Access the ThinkPHP application URL and run it.
 How to install thinkphp
Apr 09, 2024 pm 05:42 PM
How to install thinkphp
Apr 09, 2024 pm 05:42 PM
ThinkPHP installation steps: Prepare PHP, Composer, and MySQL environments. Create projects using Composer. Install the ThinkPHP framework and dependencies. Configure database connection. Generate application code. Launch the application and visit http://localhost:8000.
 Which one is better, laravel or thinkphp?
Apr 09, 2024 pm 03:18 PM
Which one is better, laravel or thinkphp?
Apr 09, 2024 pm 03:18 PM
Performance comparison of Laravel and ThinkPHP frameworks: ThinkPHP generally performs better than Laravel, focusing on optimization and caching. Laravel performs well, but for complex applications, ThinkPHP may be a better fit.
 Analysis of new features of Win11: How to skip logging in to Microsoft account
Mar 27, 2024 pm 05:24 PM
Analysis of new features of Win11: How to skip logging in to Microsoft account
Mar 27, 2024 pm 05:24 PM
Analysis of new features of Win11: How to skip logging in to a Microsoft account. With the release of Windows 11, many users have found that it brings more convenience and new features. However, some users may not like having their system tied to a Microsoft account and wish to skip this step. This article will introduce some methods to help users skip logging in to a Microsoft account in Windows 11 and achieve a more private and autonomous experience. First, let’s understand why some users are reluctant to log in to their Microsoft account. On the one hand, some users worry that they





