 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Detailed explanation of PHP security configuration under lnmp (disabling unsafe PHP functions and separating PHP uploads, etc.)
Detailed explanation of PHP security configuration under lnmp (disabling unsafe PHP functions and separating PHP uploads, etc.)
Detailed explanation of PHP security configuration under lnmp (disabling unsafe PHP functions and separating PHP uploads, etc.)
|
This article introduces the method of PHP security configuration under the lnmp architecture, including disabling unsafe PHP functions, turning off PHP error logs, PHP upload separation, turning off PHP information, disabling dynamic loading of link libraries, disabling opening remote URLs and other security measures.
Several aspects of php security configuration: 1. Use open_basedir to limit virtual host cross-directory access [HOST=www.xingzuo51.com] open_basedir=/data/site/www.xingzuo51.com/:/tmp/ [HOST=test.xingzuo51.com] open_basedir=/data/site/test.xingzuo51.com/:/tmp/Instructions: The PHP program under www.xingzuo51.com is limited to the two directories configured by open_basedir, and cannot access other directories. If the above configuration is not done, the programs of test.xingzuo51.com and www.xingzuo51.com can access each other. If one of the sites has a vulnerability and a hacker has implanted a webshell, you can use this site to take down other sites on the same server and finally install a Trojan horse. Note: The directory must be appended with / at the end. For example, if you write /tmp, the site also has /tmp123 and other directories starting with /tmp, then hackers can also access these directories. In addition, php5.3 and above support this writing method, but 5.2 does not. 2. Disable unsafe PHP functions disable_functions = show_source,system,shell_exec,passthru,exec,popen,proc_open,proc_get_status,phpinfo PHP is prohibited from executing the above PHP functions. The above PHP programs can execute Linux commands, such as ping, netstat, mysql, etc. If your system has a privilege escalation bug, you will know the consequences. 3. Pay attention to software security information Actively pay attention to the Linux kernel, PHP security and other information and take timely action on errors 4. PHP users can read only This method is my most recommended method, but you must discuss it with the PHP engineer before executing it. Why? For example, the user and group in the root directory of the site www.xingzuo51.com are nobody, and the user and group running php are phpuser. The directory permissions are 755 and the file permissions are 644. In this way, php is read-only and cannot write any files to the site directory. In other words, users cannot upload files. Even if there are loopholes, hackers cannot pass the backdoor, let alone install Trojans. Before doing this, tell the programmer to change the file cache to NoSQL memory cache (such as memcached, redis, etc.), and the uploaded files will pass through The interface is passed to other servers (static servers). Note: It is a very bad habit to program to generate local cache. Using file cache is slow and wastes disk space. The most important thing is that the server cannot scale horizontally under normal circumstances 5. Close php error log display_errors = On Change to display_errors = OffOnce an error occurs in the program, detailed error information will be immediately displayed to the user, including the path, and sometimes even the database account password. Injection and penetration passwords are basically guessed through this error report. Strongly turn it off in production environments 6. PHP upload separation Upload files to remote server such as nfs etc. Of course, you can also call the PHP interface you wrote. Even if there is an upload vulnerability, the file will be transferred to the static server. Trojan horses and other files cannot be executed at all. Example: php site www.xingzuo51.com, directory/data/site/www.xingzuo51.com Static file site static.xingzuo51.com, directory/data/site/static.xingzuo51.com The file was directly transferred to /data/site/static.xingzuo51.com. The uploaded file cannot be accessed through www.xingzuo51.com. It can only be accessed through static.xingzuo51.com, but static.xingzuo51.com does not support php. 7. Close php information expose_php = On Change to expose_php = OffDo not disclose your PHP version information easily to prevent hackers from launching attacks against this version of PHP. 8. Disable dynamic loading of link libraries disable_dl = On; Change to enable_dl = Off;9. Disable opening remote url allow_url_fopen = On Change to allow_url_fopen = OffIn fact, this is not really safe and will not lead to problems such as web intrusion. However, this greatly affects performance. The author believes that it is a security issue in a narrow sense. The following methods will not be able to obtain the remote url content $data = file_get_contents("http://www.baidu.com/");Get local file content: $data = file_get_contents("1.txt");If the site traffic is not large and the database is running well, but the web server load is surprisingly high, please check directly to see if this method is available. php obtains the content of the remote web, it is recommended to use curl. |

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Working with Flash Session Data in Laravel
Mar 12, 2025 pm 05:08 PM
Working with Flash Session Data in Laravel
Mar 12, 2025 pm 05:08 PM
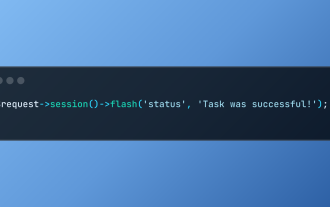
Laravel simplifies handling temporary session data using its intuitive flash methods. This is perfect for displaying brief messages, alerts, or notifications within your application. Data persists only for the subsequent request by default: $request-
 Build a React App With a Laravel Back End: Part 2, React
Mar 04, 2025 am 09:33 AM
Build a React App With a Laravel Back End: Part 2, React
Mar 04, 2025 am 09:33 AM
This is the second and final part of the series on building a React application with a Laravel back-end. In the first part of the series, we created a RESTful API using Laravel for a basic product-listing application. In this tutorial, we will be dev
 cURL in PHP: How to Use the PHP cURL Extension in REST APIs
Mar 14, 2025 am 11:42 AM
cURL in PHP: How to Use the PHP cURL Extension in REST APIs
Mar 14, 2025 am 11:42 AM
The PHP Client URL (cURL) extension is a powerful tool for developers, enabling seamless interaction with remote servers and REST APIs. By leveraging libcurl, a well-respected multi-protocol file transfer library, PHP cURL facilitates efficient execution of various network protocols, including HTTP, HTTPS, and FTP. This extension offers granular control over HTTP requests, supports multiple concurrent operations, and provides built-in security features.
 Simplified HTTP Response Mocking in Laravel Tests
Mar 12, 2025 pm 05:09 PM
Simplified HTTP Response Mocking in Laravel Tests
Mar 12, 2025 pm 05:09 PM
Laravel provides concise HTTP response simulation syntax, simplifying HTTP interaction testing. This approach significantly reduces code redundancy while making your test simulation more intuitive. The basic implementation provides a variety of response type shortcuts: use Illuminate\Support\Facades\Http; Http::fake([ 'google.com' => 'Hello World', 'github.com' => ['foo' => 'bar'], 'forge.laravel.com' =>
 12 Best PHP Chat Scripts on CodeCanyon
Mar 13, 2025 pm 12:08 PM
12 Best PHP Chat Scripts on CodeCanyon
Mar 13, 2025 pm 12:08 PM
Do you want to provide real-time, instant solutions to your customers' most pressing problems? Live chat lets you have real-time conversations with customers and resolve their problems instantly. It allows you to provide faster service to your custom
 Notifications in Laravel
Mar 04, 2025 am 09:22 AM
Notifications in Laravel
Mar 04, 2025 am 09:22 AM
In this article, we're going to explore the notification system in the Laravel web framework. The notification system in Laravel allows you to send notifications to users over different channels. Today, we'll discuss how you can send notifications ov
 Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Article discusses late static binding (LSB) in PHP, introduced in PHP 5.3, allowing runtime resolution of static method calls for more flexible inheritance.Main issue: LSB vs. traditional polymorphism; LSB's practical applications and potential perfo
 PHP Logging: Best Practices for PHP Log Analysis
Mar 10, 2025 pm 02:32 PM
PHP Logging: Best Practices for PHP Log Analysis
Mar 10, 2025 pm 02:32 PM
PHP logging is essential for monitoring and debugging web applications, as well as capturing critical events, errors, and runtime behavior. It provides valuable insights into system performance, helps identify issues, and supports faster troubleshoot





