 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Several practical points for creating high-security PHP websites
Several practical points for creating high-security PHP websites
Several practical points for creating high-security PHP websites
Everyone knows that PHP is currently the most popular web application programming language. But like other scripting languages, PHP also has several dangerous security holes. So in this tutorial, we'll take a look at a few practical tips to help you avoid some common PHP security issues.

Tip 1: Use proper error reporting
Usually during the development process, many programmers always forget to make program error reports. This is a huge mistake, because proper error reports are not only the best debugging tools, but also excellent security vulnerability detection tools. It allows you to identify as many problems as possible before putting the application online.
Of course there are many ways to enable error reporting. For example, in the php.in configuration file you can set it to be enabled at runtime
Start error reporting
error_reporting(E_ALL);
Disable error reporting
error_reporting(0);
Tip 2: Don’t use PHP’s Weak attribute
There are several PHP properties that need to be set to OFF. Generally, they exist in PHP4, but their use is not recommended in PHP5. Especially in PHP6, these attributes were removed.
Register global variables
When register_globals is set to ON, it is equivalent to setting Environment, GET, POST, COOKIE or Server variables are defined as global variables. At this time, you don't need to write $_POST['username'] to get the form variable 'username'. You only need '$username' to get this variable.
So you must be thinking that since setting register_globals to ON has such convenient benefits, why not use it? Because if you do this it will bring about a lot of security issues, and it may also conflict with local variable names.
For example, take a look at the following code:
if( !empty( $_POST['username'] ) && $_POST['username'] == ‘test123′ && !empty( $_POST['password'] ) && $_POST['password'] == “pass123″ )
{
$access = true;
}If register_globals is set to ON during runtime, then the user only needs to pass access=1 in a query string to get anything the PHP script runs.
Disable global variables in .htaccess
php_flag register_globals 0
Disable global variables in php.ini
register_globals = Off
Disable Magic Quotes like magic_quotes_gpc, magic_quotes_runtime, magic_quotes_sybase
Set in .htaccess file
php_flag magic_quotes_gpc 0 php_flag magic_quotes_runtime 0
Set in php.ini
magic_quotes_gpc = Off magic_quotes_runtime = Off magic_quotes_sybase = Off
Tips 3: Validate user input
Of course you can also validate user input. First you must know the data type you expect the user to input. In this way, you can be prepared on the browser side to prevent users from malicious attacks on you.
Tip 4: Avoid cross-site scripting attacks by users
In web applications, they simply accept user input into the form and then feed back the results. When accepting user input, it would be very dangerous to allow HTML format input, because this would also allow JavaScript to intrude in unpredictable ways and execute directly. Even if there is only one such vulnerability, cookie data may be stolen and the user's account may be stolen.
Tip 5: Prevent SQL injection attacks
PHP basically does not provide any tools to protect your database, so when you connect to the database, you can use the following mysqli_real_escape_string function.
$username = mysqli_real_escape_string( $GET['username'] ); mysql_query( “SELECT * FROM tbl_employee WHERE username = ’”.$username.“‘”);
Okay, in this short article, we elaborate on several PHP security issues that cannot be ignored during the development process. But it is ultimately up to the developer to decide whether to use it and how to use it. Hope this article can help you.
The above introduces several practical points for creating a high-security PHP website, including aspects of content. I hope it will be helpful to friends who are interested in PHP tutorials.

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1376
1376
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 CakePHP Working with Database
Sep 10, 2024 pm 05:25 PM
CakePHP Working with Database
Sep 10, 2024 pm 05:25 PM
Working with database in CakePHP is very easy. We will understand the CRUD (Create, Read, Update, Delete) operations in this chapter.
 CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
To work with date and time in cakephp4, we are going to make use of the available FrozenTime class.
 CakePHP File upload
Sep 10, 2024 pm 05:27 PM
CakePHP File upload
Sep 10, 2024 pm 05:27 PM
To work on file upload we are going to use the form helper. Here, is an example for file upload.
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
Validator can be created by adding the following two lines in the controller.
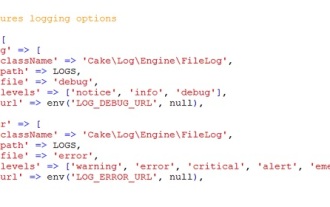 CakePHP Logging
Sep 10, 2024 pm 05:26 PM
CakePHP Logging
Sep 10, 2024 pm 05:26 PM
Logging in CakePHP is a very easy task. You just have to use one function. You can log errors, exceptions, user activities, action taken by users, for any background process like cronjob. Logging data in CakePHP is easy. The log() function is provide
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c



