 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Complete explanation of PHP vulnerabilities (7)-Session hijacking
Complete explanation of PHP vulnerabilities (7)-Session hijacking
Complete explanation of PHP vulnerabilities (7)-Session hijacking
The server and client communicate through sessions. When the client's browser connects to the server, the server will establish a session for the user. Each user's session is independent and maintained by the server. Each user's session is identified by a unique string, called a session id. When a user makes a request, the http header sent contains the value of session id. The server uses the session id in the http header to identify which user submitted the request.
Session saves the personal data of each user. General web applications will use session to save authenticated user accounts and passwords. When converting different web pages, if you need to verify the user's identity, use the account number and password saved in the session to compare. The life cycle of the session starts when the user connects to the server and ends when the user closes the browser or logs out when the session_destroy function deletes the session data. If the user does not use the computer within 20 minutes, the session will automatically end.
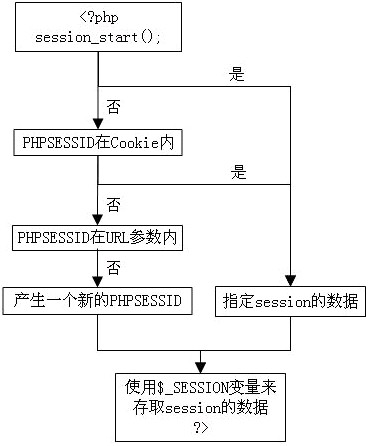
PHP application architecture for processing sessions
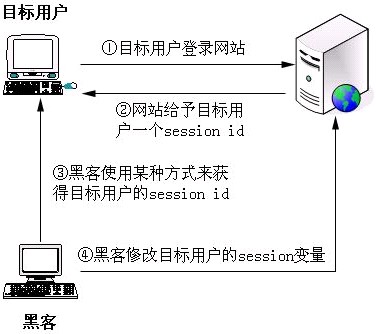
Session hijacking
Session hijacking refers to the attacker using various means to obtain the session id of the target user. Once the session ID is obtained, the attacker can use the target user's identity to log in to the website and obtain the target user's operation permissions.
Methods for attackers to obtain the target user’s session ID:
1) Brute force cracking: try various session IDs until they are cracked.
2) Calculation: If the session id is generated in a non-random way, it is possible to calculate it
3) Stealing: Use network interception, xss attacks and other methods to obtain
Session hijacking attack steps
Instances
//login.php
session_start();
if (isset($_POST["login"]))
{
$link = mysql_connect("localhost", "root", "root")
or die("无法建立MySQL数据库连接:" . mysql_error());
mysql_select_db("cms") or die("无法选择MySQL数据库");
if (!get_magic_quotes_gpc())
{
$query = "select * from member where username=’" . addslashes($_POST["username"]) .
"’ and password=’" . addslashes($_POST["password"]) . "’";
}
else
{
$query = "select * from member where username=’" . $_POST["username"] .
"’ and password=’" . $_POST["password"] . "’";
}
$result = mysql_query($query)
or die("执行MySQL查询语句失败:" . mysql_error());
$match_count = mysql_num_rows($result);
if ($match_count)
{
$_SESSION["book"] = 1;
mysql_close($link);
header("Location: http://localhost/index.php?user=" . $_POST["username"]);
}
…..
// 打开Session
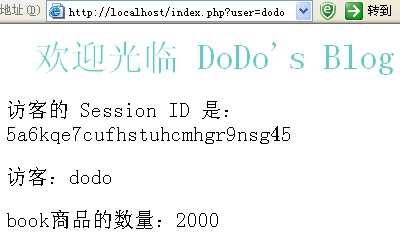
访客的 Session ID 是:echo session_id(); ?>
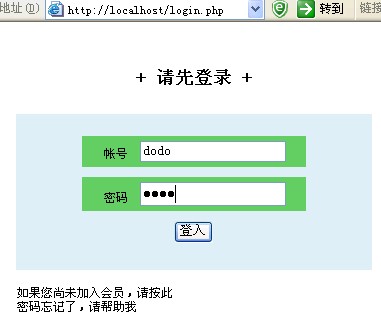
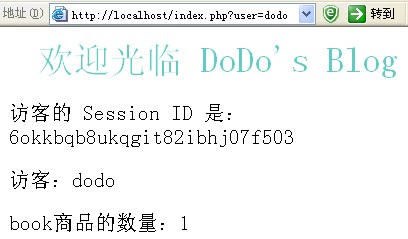
After logging in, it will show
Start attacking
//attack.php
php
//Open Session
session_start();
echo "Session of the target user" The ID is: ". session_id() . "
";
echo "The username of the target user is:" . $_SESSION["username"] . "
";
echo "The password of the target user is: " . $_SESSION["password"] . "
";
// Set the number of books to 2000
$_SESSION["book"] = 2000;
?>
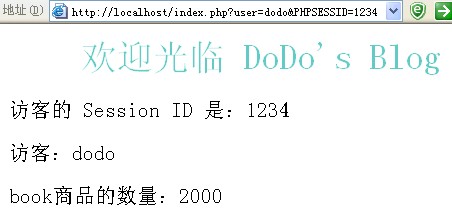
Submit http://localhost/attack.php?PHPSESSID=5a6kqe7cufhstuhcmhgr9nsg45 This ID is the obtained customer session id. After refreshing the customer page
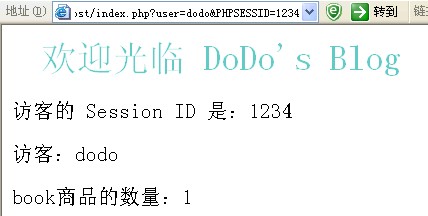
session fixed attack
Hackers can use the method of sending the session id to the user to Complete the attack
http://localhost/index.php?user=dodo&PHPSESSID=1234 Send this link to the user dodo for display
Then the attacker visits http://localhost/attack.php ?PHPSESSID=1234, the customer page refreshed and found
Prevention methods
1) Regularly change the session id
Function bool session_regenerate_id([bool delete_old_session])
delete_old_session If true, the old session file will be deleted; if it is false, the old session will be retained. The default is false. Optional
Add
session_start();
session_regenerate_id(TRUE);
...
This way a new session id will be generated every time it is reloaded
2) Changes The name of the session
The default name of the session is PHPSESSID. This variable will be saved in the cookie. If the hacker does not capture the packet and analyze it, he cannot guess the name and block some attacks
session_start();
session_name( "mysessionid");
......
3) Turn off transparent session id
Transparent session id means that when the http request in the browser does not use cookies to formulate the session id, the sessioin id is passed using a link; open php .ini, edit
session.use_trans_sid = 0
In the code
int_set("session.use_trans_sid", 0);
session_start();
...
4) Only check the session from the cookie id
session.use_cookies = 1 means using cookies to store session id
session.use_only_cookies = 1 means only using cookies to store session id, which can avoid session fixation attacks
In the code
int_set("session.use_cookies", 1 );
int_set("session.use_only_cookies", 1); p>
5) Use URL to pass hidden parameters
session_start();
$seid = md5(uniqid(rand()), TRUE ));
$_SESSION["seid"] = $seid;
Although the attacker can obtain the session data, he cannot know the value of $seid. As long as he checks the value of seid, he can confirm whether the current page is a web program. Called by yourself.
The above is the complete solution to PHP vulnerabilities (7) - Session hijacking. For more related content, please pay attention to the PHP Chinese website (www.php.cn)!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
 Alipay PHP SDK transfer error: How to solve the problem of 'Cannot declare class SignData'?
Apr 01, 2025 am 07:21 AM
Alipay PHP SDK transfer error: How to solve the problem of 'Cannot declare class SignData'?
Apr 01, 2025 am 07:21 AM
Alipay PHP...
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Article discusses late static binding (LSB) in PHP, introduced in PHP 5.3, allowing runtime resolution of static method calls for more flexible inheritance.Main issue: LSB vs. traditional polymorphism; LSB's practical applications and potential perfo
 Describe the SOLID principles and how they apply to PHP development.
Apr 03, 2025 am 12:04 AM
Describe the SOLID principles and how they apply to PHP development.
Apr 03, 2025 am 12:04 AM
The application of SOLID principle in PHP development includes: 1. Single responsibility principle (SRP): Each class is responsible for only one function. 2. Open and close principle (OCP): Changes are achieved through extension rather than modification. 3. Lisch's Substitution Principle (LSP): Subclasses can replace base classes without affecting program accuracy. 4. Interface isolation principle (ISP): Use fine-grained interfaces to avoid dependencies and unused methods. 5. Dependency inversion principle (DIP): High and low-level modules rely on abstraction and are implemented through dependency injection.
 How to automatically set permissions of unixsocket after system restart?
Mar 31, 2025 pm 11:54 PM
How to automatically set permissions of unixsocket after system restart?
Mar 31, 2025 pm 11:54 PM
How to automatically set the permissions of unixsocket after the system restarts. Every time the system restarts, we need to execute the following command to modify the permissions of unixsocket: sudo...
 How does session hijacking work and how can you mitigate it in PHP?
Apr 06, 2025 am 12:02 AM
How does session hijacking work and how can you mitigate it in PHP?
Apr 06, 2025 am 12:02 AM
Session hijacking can be achieved through the following steps: 1. Obtain the session ID, 2. Use the session ID, 3. Keep the session active. The methods to prevent session hijacking in PHP include: 1. Use the session_regenerate_id() function to regenerate the session ID, 2. Store session data through the database, 3. Ensure that all session data is transmitted through HTTPS.
 Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Static binding (static::) implements late static binding (LSB) in PHP, allowing calling classes to be referenced in static contexts rather than defining classes. 1) The parsing process is performed at runtime, 2) Look up the call class in the inheritance relationship, 3) It may bring performance overhead.
 How to debug CLI mode in PHPStorm?
Apr 01, 2025 pm 02:57 PM
How to debug CLI mode in PHPStorm?
Apr 01, 2025 pm 02:57 PM
How to debug CLI mode in PHPStorm? When developing with PHPStorm, sometimes we need to debug PHP in command line interface (CLI) mode...



