MD5 encryption method in JS
1
/* 2 * A JavaScript implementation of the RSA Data Security, Inc. MD5 Message 3 * Digest Algorithm, as defined in RFC 1321. 4 * Version 2.1 Copyright (C) Paul Johnston 1999 - 2002. 5 * Other contributors: Greg Holt, Andrew Kepert, Ydnar, Lostinet 6 * Distributed under the BSD License 7 * See http://pajhome.org.uk/crypt/md5 for more info. 8*/
9 10
/* 11 * Configurable variables. You may need to tweak these to be compatible with 12 * the server-side, but the defaults work in most cases. 13*/
14 var hexcase = 0;
/* hex output format. 0 - lowercase;
1 - uppercase*/
15 var b64pad = "";
/* base-64 pad character. "=" for strict RFC compliance*/
16 var chrsz = 8;
/* bits per input character. 8 - ASCII;
16 - Unicode*/
17 18
/* 19 * These are the functions you'll usually want to call 20 * They take string arguments and return either hex or base-64 encoded strings 21*/
22 function hex_md5(s) {
return binl2hex(core_md5(str2binl(s), s.length * chrsz));
}
23 function b64_md5(s) {
return binl2b64(core_md5(str2binl(s), s.length * chrsz));
}
24 function str_md5(s) {
return binl2str(core_md5(str2binl(s), s.length * chrsz));
}
25 function hex_hmac_md5(key, data) {
return binl2hex(core_hmac_md5(key, data));
}
26 function b64_hmac_md5(key, data) {
return binl2b64(core_hmac_md5(key, data));
}
27 function str_hmac_md5(key, data) {
return binl2str(core_hmac_md5(key, data));
}
28 29
/* 30 * Perform a simple self-test to see if the VM is working 31*/
32 function md5_vm_test() 33 {
34 return hex_md5("abc") == "900150983cd24fb0d6963f7d28e17f72";
35 }
36 37
/* 38 * Calculate the MD5 of an array of little-endian words, and a bit length 39*/
40 function core_md5(x, len) 41 {
42
/* append padding*/
43 x[len >> 5] |= 0x80 << ((len) % 32);
44 x[(((len + 64) >>> 9) << 4) + 14] = len;
45 46 var a = 1732584193;
47 var b = -271733879;
48 var c = -1732584194;
49 var d = 271733878;
50 51 for(var i = 0;
i < x.length;
i += 16) 52 {
53 var olda = a;
54 var oldb = b;
55 var oldc = c;
56 var oldd = d;
57 58 a = md5_ff(a, b, c, d, x[i+ 0], 7 , -680876936);
59 d = md5_ff(d, a, b, c, x[i+ 1], 12, -389564586);
60 c = md5_ff(c, d, a, b, x[i+ 2], 17, 606105819);
61 b = md5_ff(b, c, d, a, x[i+ 3], 22, -1044525330);
62 a = md5_ff(a, b, c, d, x[i+ 4], 7 , -176418897);
63 d = md5_ff(d, a, b, c, x[i+ 5], 12, 1200080426);
64 c = md5_ff(c, d, a, b, x[i+ 6], 17, -1473231341);
65 b = md5_ff(b, c, d, a, x[i+ 7], 22, -45705983);
66 a = md5_ff(a, b, c, d, x[i+ 8], 7 , 1770035416);
67 d = md5_ff(d, a, b, c, x[i+ 9], 12, -1958414417);
68 c = md5_ff(c, d, a, b, x[i+10], 17, -42063);
69 b = md5_ff(b, c, d, a, x[i+11], 22, -1990404162);
70 a = md5_ff(a, b, c, d, x[i+12], 7 , 1804603682);
71 d = md5_ff(d, a, b, c, x[i+13], 12, -40341101);
72 c = md5_ff(c, d, a, b, x[i+14], 17, -1502002290);
73 b = md5_ff(b, c, d, a, x[i+15], 22, 1236535329);
74 75 a = md5_gg(a, b, c, d, x[i+ 1], 5 , -165796510);
76 d = md5_gg(d, a, b, c, x[i+ 6], 9 , -1069501632);
77 c = md5_gg(c, d, a, b, x[i+11], 14, 643717713);
78 b = md5_gg(b, c, d, a, x[i+ 0], 20, -373897302);
79 a = md5_gg(a, b, c, d, x[i+ 5], 5 , -701558691);
80 d = md5_gg(d, a, b, c, x[i+10], 9 , 38016083);
81 c = md5_gg(c, d, a, b, x[i+15], 14, -660478335);
82 b = md5_gg(b, c, d, a, x[i+ 4], 20, -405537848);
83 a = md5_gg(a, b, c, d, x[i+ 9], 5 , 568446438);
84 d = md5_gg(d, a, b, c, x[i+14], 9 , -1019803690);
85 c = md5_gg(c, d, a, b, x[i+ 3], 14, -187363961);
86 b = md5_gg(b, c, d, a, x[i+ 8], 20, 1163531501);
87 a = md5_gg(a, b, c, d, x[i+13], 5 , -1444681467);
88 d = md5_gg(d, a, b, c, x[i+ 2], 9 , -51403784);
89 c = md5_gg(c, d, a, b, x[i+ 7], 14, 1735328473);
90 b = md5_gg(b, c, d, a, x[i+12], 20, -1926607734);
91 92 a = md5_hh(a, b, c, d, x[i+ 5], 4 , -378558);
93 d = md5_hh(d, a, b, c, x[i+ 8], 11, -2022574463);
94 c = md5_hh(c, d, a, b, x[i+11], 16, 1839030562);
95 b = md5_hh(b, c, d, a, x[i+14], 23, -35309556);
96 a = md5_hh(a, b, c, d, x[i+ 1], 4 , -1530992060);
97 d = md5_hh(d, a, b, c, x[i+ 4], 11, 1272893353);
98 c = md5_hh(c, d, a, b, x[i+ 7], 16, -155497632);
99 b = md5_hh(b, c, d, a, x[i+10], 23, -1094730640);
100 a = md5_hh(a, b, c, d, x[i+13], 4 , 681279174);
101 d = md5_hh(d, a, b, c, x[i+ 0], 11, -358537222);
102 c = md5_hh(c, d, a, b, x[i+ 3], 16, -722521979);
103 b = md5_hh(b, c, d, a, x[i+ 6], 23, 76029189);
104 a = md5_hh(a, b, c, d, x[i+ 9], 4 , -640364487);
105 d = md5_hh(d, a, b, c, x[i+12], 11, -421815835);
106 c = md5_hh(c, d, a, b, x[i+15], 16, 530742520);
107 b = md5_hh(b, c, d, a, x[i+ 2], 23, -995338651);
108 109 a = md5_ii(a, b, c, d, x[i+ 0], 6 , -198630844);
110 d = md5_ii(d, a, b, c, x[i+ 7], 10, 1126891415);
111 c = md5_ii(c, d, a, b, x[i+14], 15, -1416354905);
112 b = md5_ii(b, c, d, a, x[i+ 5], 21, -57434055);
113 a = md5_ii(a, b, c, d, x[i+12], 6 , 1700485571);
114 d = md5_ii(d, a, b, c, x[i+ 3], 10, -1894986606);
115 c = md5_ii(c, d, a, b, x[i+10], 15, -1051523);
116 b = md5_ii(b, c, d, a, x[i+ 1], 21, -2054922799);
117 a = md5_ii(a, b, c, d, x[i+ 8], 6 , 1873313359);
118 d = md5_ii(d, a, b, c, x[i+15], 10, -30611744);
119 c = md5_ii(c, d, a, b, x[i+ 6], 15, -1560198380);
120 b = md5_ii(b, c, d, a, x[i+13], 21, 1309151649);
121 a = md5_ii(a, b, c, d, x[i+ 4], 6 , -145523070);
122 d = md5_ii(d, a, b, c, x[i+11], 10, -1120210379);
123 c = md5_ii(c, d, a, b, x[i+ 2], 15, 718787259);
124 b = md5_ii(b, c, d, a, x[i+ 9], 21, -343485551);
125 126 a = safe_add(a, olda);
127 b = safe_add(b, oldb);
128 c = safe_add(c, oldc);
129 d = safe_add(d, oldd);
130 }
131 return Array(a, b, c, d);
132
133 }
134
135 /*
136 * These functions implement the four basic operations the algorithm uses.137*/
138 function md5_cmn(q, a, b, x, s, t)139 {
140 return safe_add(bit_rol(safe_add(safe_add(a, q), safe_add(x, t)), s),b);
141 }
142 function md5_ff(a, b, c, d, x, s, t)143 {
144 return md5_cmn((b & c) | ((~b) & d), a, b, x, s, t);
145 }
146 function md5_gg(a, b, c, d, x, s, t)147 {
148 return md5_cmn((b & d) | (c & (~d)), a, b, x, s, t);
149 }
150 function md5_hh(a, b, c, d, x, s, t)
151 {
152 return md5_cmn(b ^ c ^ d, a, b, x, s, t);
153 }
154 function md5_ii(a, b, c, d, x, s, t)
155 {
156 return md5_cmn(c ^ (b | (~d)), a, b, x, s, t);
157 }
158
159
/*160 * Calculate the HMAC-MD5, of a key and some data161*/
162 function core_hmac_md5(key, data)163 {
164 var bkey = str2binl(key);
165 if(bkey.length > 16) bkey = core_md5(bkey, key.length * chrsz);
166 167 var ipad = Array(16), opad = Array(16);
168 for(var i = 0;
i < 16;
i++)169 {
170 ipad[i] = bkey[i] ^ 0x36363636;
171 opad[i] = bkey[i] ^ 0x5C5C5C5C;
172 }
173
174 var hash = core_md5(ipad.concat(str2binl(data)), 512 + data.length * chrsz);
175 return core_md5(opad.concat(hash), 512 + 128);
176 }
177
178
/*179 * Add integers, wrapping at 2^32. This uses 16-bit operations internally180 * to work around bugs in some JS interpreters.181*/
182 function safe_add(x, y)183 {
184 var lsw = (x & 0xFFFF) + (y & 0xFFFF);
185 var msw = (x >> 16) + (y >> 16) + (lsw >> 16);
186 return (msw << 16) | (lsw & 0xFFFF);
187 }
188
189
/*190 * Bitwise rotate a 32-bit number to the left.191*/
192 function bit_rol(num, cnt)193 {
194 return (num << cnt) | (num >>> (32 - cnt));
195 }
196
197
/*198 * Convert a string to an array of little-endian words199 * If chrsz is ASCII, characters >255 have their hi-byte silently ignored.200*/
201 function str2binl(str)202 {
203 var bin = Array();
204 var mask = (1 << chrsz) - 1;
205 for(var i = 0;
i < str.length * chrsz;
i += chrsz)206 bin[i>>5] |= (str.charCodeAt(i / chrsz) & mask) << (i%32);
207 return bin;
208 }
209
210
/*211 * Convert an array of little-endian words to a string212*/
213 function binl2str(bin)214 {
215 var str = "";
216 var mask = (1 << chrsz) - 1;
217 for(var i = 0;
i < bin.length * 32;
i += chrsz)218 str += String.fromCharCode((bin[i>>5] >>> (i % 32)) & mask);
219 return str;
220 }
221 222
/*223 * Convert an array of little-endian words to a hex string.224*/
225 function binl2hex(binarray)226 {
227 var hex_tab = hexcase ? "0123456789ABCDEF" : "0123456789abcdef";
228 var str = "";
229 for(var i = 0;
i < binarray.length * 4;
i++)230 {
231 str += hex_tab.charAt((binarray[i>>2] >> ((i%4)*8+4)) & 0xF) +232 hex_tab.charAt((binarray[i>>2] >> ((i%4)*8 )) & 0xF);
233 }
234 return str;
235 }
236 237
/*238 * Convert an array of little-endian words to a base-64 string239*/
240 function binl2b64(binarray)241 {
242 var tab = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/";
243 var str = "";
244 for(var i = 0;
i < binarray.length * 4;
i += 3)245 {
246 var triplet = (((binarray[i >> 2] >> 8 * ( i %4)) & 0xFF) << 16)247 | (((binarray[i+1 >> 2] >> 8 * ((i+1)%4)) & 0xFF) << 8 )248 | ((binarray[i+2 >> 2] >> 8 * ((i+2)%4)) & 0xFF);
249 for(var j = 0;
j < 4;
j++)250 {
251 if(i * 8 + j * 6 > binarray.length * 32) str += b64pad;
252 else str += tab.charAt((triplet >> 6*(3-j)) & 0x3F);
253 }
254 }
255 return str;
256 }The above is the detailed content of MD5 encryption method in JS. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to write a novel in the Tomato Free Novel app. Share the tutorial on how to write a novel in Tomato Novel.
Mar 28, 2024 pm 12:50 PM
How to write a novel in the Tomato Free Novel app. Share the tutorial on how to write a novel in Tomato Novel.
Mar 28, 2024 pm 12:50 PM
Tomato Novel is a very popular novel reading software. We often have new novels and comics to read in Tomato Novel. Every novel and comic is very interesting. Many friends also want to write novels. Earn pocket money and edit the content of the novel you want to write into text. So how do we write the novel in it? My friends don’t know, so let’s go to this site together. Let’s take some time to look at an introduction to how to write a novel. Share the Tomato novel tutorial on how to write a novel. 1. First open the Tomato free novel app on your mobile phone and click on Personal Center - Writer Center. 2. Jump to the Tomato Writer Assistant page - click on Create a new book at the end of the novel.
 How to recover deleted contacts on WeChat (simple tutorial tells you how to recover deleted contacts)
May 01, 2024 pm 12:01 PM
How to recover deleted contacts on WeChat (simple tutorial tells you how to recover deleted contacts)
May 01, 2024 pm 12:01 PM
Unfortunately, people often delete certain contacts accidentally for some reasons. WeChat is a widely used social software. To help users solve this problem, this article will introduce how to retrieve deleted contacts in a simple way. 1. Understand the WeChat contact deletion mechanism. This provides us with the possibility to retrieve deleted contacts. The contact deletion mechanism in WeChat removes them from the address book, but does not delete them completely. 2. Use WeChat’s built-in “Contact Book Recovery” function. WeChat provides “Contact Book Recovery” to save time and energy. Users can quickly retrieve previously deleted contacts through this function. 3. Enter the WeChat settings page and click the lower right corner, open the WeChat application "Me" and click the settings icon in the upper right corner to enter the settings page.
 Quickly master: How to open two WeChat accounts on Huawei mobile phones revealed!
Mar 23, 2024 am 10:42 AM
Quickly master: How to open two WeChat accounts on Huawei mobile phones revealed!
Mar 23, 2024 am 10:42 AM
In today's society, mobile phones have become an indispensable part of our lives. As an important tool for our daily communication, work, and life, WeChat is often used. However, it may be necessary to separate two WeChat accounts when handling different transactions, which requires the mobile phone to support logging in to two WeChat accounts at the same time. As a well-known domestic brand, Huawei mobile phones are used by many people. So what is the method to open two WeChat accounts on Huawei mobile phones? Let’s reveal the secret of this method. First of all, you need to use two WeChat accounts at the same time on your Huawei mobile phone. The easiest way is to
 The secret of hatching mobile dragon eggs is revealed (step by step to teach you how to successfully hatch mobile dragon eggs)
May 04, 2024 pm 06:01 PM
The secret of hatching mobile dragon eggs is revealed (step by step to teach you how to successfully hatch mobile dragon eggs)
May 04, 2024 pm 06:01 PM
Mobile games have become an integral part of people's lives with the development of technology. It has attracted the attention of many players with its cute dragon egg image and interesting hatching process, and one of the games that has attracted much attention is the mobile version of Dragon Egg. To help players better cultivate and grow their own dragons in the game, this article will introduce to you how to hatch dragon eggs in the mobile version. 1. Choose the appropriate type of dragon egg. Players need to carefully choose the type of dragon egg that they like and suit themselves, based on the different types of dragon egg attributes and abilities provided in the game. 2. Upgrade the level of the incubation machine. Players need to improve the level of the incubation machine by completing tasks and collecting props. The level of the incubation machine determines the hatching speed and hatching success rate. 3. Collect the resources required for hatching. Players need to be in the game
 How to set font size on mobile phone (easily adjust font size on mobile phone)
May 07, 2024 pm 03:34 PM
How to set font size on mobile phone (easily adjust font size on mobile phone)
May 07, 2024 pm 03:34 PM
Setting font size has become an important personalization requirement as mobile phones become an important tool in people's daily lives. In order to meet the needs of different users, this article will introduce how to improve the mobile phone use experience and adjust the font size of the mobile phone through simple operations. Why do you need to adjust the font size of your mobile phone - Adjusting the font size can make the text clearer and easier to read - Suitable for the reading needs of users of different ages - Convenient for users with poor vision to use the font size setting function of the mobile phone system - How to enter the system settings interface - In Find and enter the "Display" option in the settings interface - find the "Font Size" option and adjust it. Adjust the font size with a third-party application - download and install an application that supports font size adjustment - open the application and enter the relevant settings interface - according to the individual
 The difference between Go language methods and functions and analysis of application scenarios
Apr 04, 2024 am 09:24 AM
The difference between Go language methods and functions and analysis of application scenarios
Apr 04, 2024 am 09:24 AM
The difference between Go language methods and functions lies in their association with structures: methods are associated with structures and are used to operate structure data or methods; functions are independent of types and are used to perform general operations.
 How to choose a mobile phone screen protector to protect your mobile phone screen (several key points and tips for purchasing mobile phone screen protectors)
May 07, 2024 pm 05:55 PM
How to choose a mobile phone screen protector to protect your mobile phone screen (several key points and tips for purchasing mobile phone screen protectors)
May 07, 2024 pm 05:55 PM
Mobile phone film has become one of the indispensable accessories with the popularity of smartphones. To extend its service life, choose a suitable mobile phone film to protect the mobile phone screen. To help readers choose the most suitable mobile phone film for themselves, this article will introduce several key points and techniques for purchasing mobile phone film. Understand the materials and types of mobile phone films: PET film, TPU, etc. Mobile phone films are made of a variety of materials, including tempered glass. PET film is relatively soft, tempered glass film has good scratch resistance, and TPU has good shock-proof performance. It can be decided based on personal preference and needs when choosing. Consider the degree of screen protection. Different types of mobile phone films have different degrees of screen protection. PET film mainly plays an anti-scratch role, while tempered glass film has better drop resistance. You can choose to have better
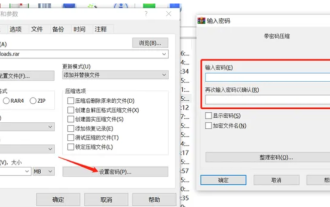 How to encrypt the compressed package in winrar-winrar encrypted compressed package method
Mar 23, 2024 pm 12:10 PM
How to encrypt the compressed package in winrar-winrar encrypted compressed package method
Mar 23, 2024 pm 12:10 PM
The editor will introduce to you three methods of encryption and compression: Method 1: Encryption The simplest encryption method is to enter the password you want to set when encrypting the file, and the encryption and compression are completed. Method 2: Automatic encryption Ordinary encryption method requires us to enter a password when encrypting each file. If you want to encrypt a large number of compressed packages and the passwords are the same, then we can set automatic encryption in WinRAR, and then just When compressing files normally, WinRAR will add a password to each compressed package. The method is as follows: Open WinRAR, click Options-Settings in the setting interface, switch to [Compression], click Create Default Configuration-Set Password Enter the password we want to set here, click OK to complete the setting, we only need to correct






