Correct way to unlock redis lock
Redis is a good friend of PHP. When writing business in PHP, the concept of lock is sometimes used. Only one person can operate a certain behavior at the same time. At this time we need to use locks. There are several locking methods. PHP cannot use locks in memory, nor can it use ZooKeeper to lock. Using a database to lock will consume a lot of money. At this time, we generally choose redis as the locking mechanism. This article mainly shares with you the correct method of unlocking redis, hoping to help everyone.
setnx
The simplest data structure locked in redis is string. In the earliest days, setnx was generally used for locking operations. This command is to set a val when :lock does not exist. Maybe you will also remember to use expire to increase the expiration of the lock. To unlock the operation, use the del command. The pseudo code is as follows:
if (Redis::setnx("my:lock", 1)) {
Redis::expire("my:lock", 10);
// ... do something
Redis::del("my:lock")
}There is actually a problem here. The problem is that if crash and other behaviors are encountered between setnx and expire, the lock may not be released. So a further optimization solution may be to store the timestamp in the lock. Determine the length of timestamp.
set
Now it is officially recommended to use set directly to implement locking. We can use the set command to replace setnx, which looks like the following
if (Redis::set("my:lock", 1, "nx", "ex", 10)) {
... do something
Redis::del("my:lock")
}The above code sets my:lock to 1 if and only if the lock is not When it exists, set the expiration time to 10 after the setting is completed.
The mechanism for acquiring locks is correct, but it is wrong to use del directly for deleting locks. Because it may lead to accidentally deleting other people's locks.
For example, I locked this lock for 10 seconds, but the processing time was longer than 10 seconds. At 10 seconds, the lock automatically expired, was taken away by others, and was re-locked. Then at this time, when I call Redis::del again, it will delete the lock created by others.
The official also has suggestions for unlocking commands. It is recommended to use lua script, first perform get, and then perform del
The program becomes:
$token = rand(1, 100000);
function lock() {
return Redis::set("my:lock", $token, "nx", "ex", 10);
}
function unlock() {
$script = `
if redis.call("get",KEYS[1]) == ARGV[1]
then
return redis.call("del",KEYS[1])
else
return 0
end
`
return Redis::eval($script, "my:lock", $token)
}
if (lock()) {
// do something
unlock();
}The token here is a random number. When locking, this token is stored in my:lock of redis. When unlocking, first get the token in the lock. If it matches the token I want to delete If they are consistent, it means that the lock was set by me before. Otherwise, it means that the lock has expired and was set by someone else, and I should not perform any operations on it.
So: Don’t use setnx anymore, use set directly for lock implementation.
Related recommendations:
php Use redis lock to limit concurrent access class
php Use redis lock to limit concurrent access class example
Summary of common methods for operating redis in php
The above is the detailed content of Correct way to unlock redis lock. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Solution to 0x80242008 error when installing Windows 11 10.0.22000.100
May 08, 2024 pm 03:50 PM
Solution to 0x80242008 error when installing Windows 11 10.0.22000.100
May 08, 2024 pm 03:50 PM
1. Start the [Start] menu, enter [cmd], right-click [Command Prompt], and select Run as [Administrator]. 2. Enter the following commands in sequence (copy and paste carefully): SCconfigwuauservstart=auto, press Enter SCconfigbitsstart=auto, press Enter SCconfigcryptsvcstart=auto, press Enter SCconfigtrustedinstallerstart=auto, press Enter SCconfigwuauservtype=share, press Enter netstopwuauserv , press enter netstopcryptS
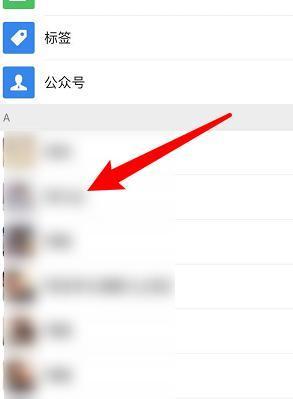 How to recover deleted contacts on WeChat (simple tutorial tells you how to recover deleted contacts)
May 01, 2024 pm 12:01 PM
How to recover deleted contacts on WeChat (simple tutorial tells you how to recover deleted contacts)
May 01, 2024 pm 12:01 PM
Unfortunately, people often delete certain contacts accidentally for some reasons. WeChat is a widely used social software. To help users solve this problem, this article will introduce how to retrieve deleted contacts in a simple way. 1. Understand the WeChat contact deletion mechanism. This provides us with the possibility to retrieve deleted contacts. The contact deletion mechanism in WeChat removes them from the address book, but does not delete them completely. 2. Use WeChat’s built-in “Contact Book Recovery” function. WeChat provides “Contact Book Recovery” to save time and energy. Users can quickly retrieve previously deleted contacts through this function. 3. Enter the WeChat settings page and click the lower right corner, open the WeChat application "Me" and click the settings icon in the upper right corner to enter the settings page.
 The secret of hatching mobile dragon eggs is revealed (step by step to teach you how to successfully hatch mobile dragon eggs)
May 04, 2024 pm 06:01 PM
The secret of hatching mobile dragon eggs is revealed (step by step to teach you how to successfully hatch mobile dragon eggs)
May 04, 2024 pm 06:01 PM
Mobile games have become an integral part of people's lives with the development of technology. It has attracted the attention of many players with its cute dragon egg image and interesting hatching process, and one of the games that has attracted much attention is the mobile version of Dragon Egg. To help players better cultivate and grow their own dragons in the game, this article will introduce to you how to hatch dragon eggs in the mobile version. 1. Choose the appropriate type of dragon egg. Players need to carefully choose the type of dragon egg that they like and suit themselves, based on the different types of dragon egg attributes and abilities provided in the game. 2. Upgrade the level of the incubation machine. Players need to improve the level of the incubation machine by completing tasks and collecting props. The level of the incubation machine determines the hatching speed and hatching success rate. 3. Collect the resources required for hatching. Players need to be in the game
 How to set font size on mobile phone (easily adjust font size on mobile phone)
May 07, 2024 pm 03:34 PM
How to set font size on mobile phone (easily adjust font size on mobile phone)
May 07, 2024 pm 03:34 PM
Setting font size has become an important personalization requirement as mobile phones become an important tool in people's daily lives. In order to meet the needs of different users, this article will introduce how to improve the mobile phone use experience and adjust the font size of the mobile phone through simple operations. Why do you need to adjust the font size of your mobile phone - Adjusting the font size can make the text clearer and easier to read - Suitable for the reading needs of users of different ages - Convenient for users with poor vision to use the font size setting function of the mobile phone system - How to enter the system settings interface - In Find and enter the "Display" option in the settings interface - find the "Font Size" option and adjust it. Adjust the font size with a third-party application - download and install an application that supports font size adjustment - open the application and enter the relevant settings interface - according to the individual
 Golang API caching strategy and optimization
May 07, 2024 pm 02:12 PM
Golang API caching strategy and optimization
May 07, 2024 pm 02:12 PM
The caching strategy in GolangAPI can improve performance and reduce server load. Commonly used strategies are: LRU, LFU, FIFO and TTL. Optimization techniques include selecting appropriate cache storage, hierarchical caching, invalidation management, and monitoring and tuning. In the practical case, the LRU cache is used to optimize the API for obtaining user information from the database. The data can be quickly retrieved from the cache. Otherwise, the cache can be updated after obtaining it from the database.
 How to choose a mobile phone screen protector to protect your mobile phone screen (several key points and tips for purchasing mobile phone screen protectors)
May 07, 2024 pm 05:55 PM
How to choose a mobile phone screen protector to protect your mobile phone screen (several key points and tips for purchasing mobile phone screen protectors)
May 07, 2024 pm 05:55 PM
Mobile phone film has become one of the indispensable accessories with the popularity of smartphones. To extend its service life, choose a suitable mobile phone film to protect the mobile phone screen. To help readers choose the most suitable mobile phone film for themselves, this article will introduce several key points and techniques for purchasing mobile phone film. Understand the materials and types of mobile phone films: PET film, TPU, etc. Mobile phone films are made of a variety of materials, including tempered glass. PET film is relatively soft, tempered glass film has good scratch resistance, and TPU has good shock-proof performance. It can be decided based on personal preference and needs when choosing. Consider the degree of screen protection. Different types of mobile phone films have different degrees of screen protection. PET film mainly plays an anti-scratch role, while tempered glass film has better drop resistance. You can choose to have better
 Caching mechanism and application practice in PHP development
May 09, 2024 pm 01:30 PM
Caching mechanism and application practice in PHP development
May 09, 2024 pm 01:30 PM
In PHP development, the caching mechanism improves performance by temporarily storing frequently accessed data in memory or disk, thereby reducing the number of database accesses. Cache types mainly include memory, file and database cache. Caching can be implemented in PHP using built-in functions or third-party libraries, such as cache_get() and Memcache. Common practical applications include caching database query results to optimize query performance and caching page output to speed up rendering. The caching mechanism effectively improves website response speed, enhances user experience and reduces server load.
 How to upgrade Win11 English 21996 to Simplified Chinese 22000_How to upgrade Win11 English 21996 to Simplified Chinese 22000
May 08, 2024 pm 05:10 PM
How to upgrade Win11 English 21996 to Simplified Chinese 22000_How to upgrade Win11 English 21996 to Simplified Chinese 22000
May 08, 2024 pm 05:10 PM
First you need to set the system language to Simplified Chinese display and restart. Of course, if you have changed the display language to Simplified Chinese before, you can just skip this step. Next, start operating the registry, regedit.exe, directly navigate to HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlNlsLanguage in the left navigation bar or the upper address bar, and then modify the InstallLanguage key value and Default key value to 0804 (if you want to change it to English en-us, you need First set the system display language to en-us, restart the system and then change everything to 0409) You must restart the system at this point.






