Sharing of basic security knowledge in Nodejs crypto module
This article mainly shares with you Nodejs advanced: the basic security knowledge you need to master in the crypto module. I hope it can help everyone. In the Internet era, the amount of data on the network is growing at an alarming rate every day. At the same time, various network security issues emerge one after another. Today, as the importance of information security becomes increasingly prominent, as a developer, you need to strengthen your understanding of security and enhance the security of services through technical means.
crypto The module is one of the core modules of nodejs. It provides security-related functions, such as digest operations, encryption, electronic signatures, etc. Many beginners don't know how to get started with the long API list, so it involves a lot of knowledge in the security field.
This article focuses on explaining the theoretical knowledge behind the API, mainly including the following content:
Summary (hash), summary-based message verification code (HMAC)
Symmetric encryption, asymmetric encryption, electronic signature
Block encryption mode
This article is excerpted from "Nodejs Learning Notes", for more chapters and updates, please visit the github homepage address.
2. Digest (hash)
Digest (digest): Take a message with a variable length as input and run the hash function to generate a fixed-length output. This output is called a digest. Usually used to verify that the message is complete and has not been tampered with.
The digest operation is irreversible. In other words, when the input is fixed, a fixed output is produced. But if the output is known, the input cannot be deduced.
The pseudo code is as follows.
digest = Hash(message)
Common digest algorithms and corresponding output digits are as follows:
MD5: 128 bits
SHA-1: 160 bits
SHA256: 256 bits
- ##SHA512: 512 bits
var crypto = require('crypto');
var md5 = crypto.createHash('md5');
var message = 'hello';
var digest = md5.update(message, 'utf8').digest('hex');
console.log(digest);
// 输出如下:注意这里是16进制
// 5d41402abc4b2a76b9719d911017c592const crypto = require('crypto');
// 参数一:摘要函数
// 参数二:秘钥
let hmac = crypto.createHmac('md5', '123456');
let ret = hmac.update('hello').digest('hex');
console.log(ret);
// 9c699d7af73a49247a239cb0dd2f8139Encryption/decryption: Given plain text, through a certain algorithm, The process of generating encrypted ciphertext is called encryption. The reverse is decryption.
encryptedText = encrypt(plainText)plainText = decrypt(encryptedText)
Secret key: In order to further enhance the security of the encryption/decryption algorithm, add/ The secret key is introduced during the decryption process. The secret key can be regarded as a parameter of the encryption/decryption algorithm. When the ciphertext is known, if the secret key used for decryption is not known, the ciphertext cannot be decrypted.
encryptedText = encrypt(plainText, encryptKey)plainText = decrypt(encryptedText, decryptKey)Encryption algorithms can be divided into ## based on whether the secret keys used for encryption and decryption are the same. #Symmetric encryption
, Asymmetric encryption. 1. Symmetric encryption
The secret key used for encryption and decryption is the same, that is,
encryptKey === decryptKey. Common symmetric encryption algorithms: DES, 3DES, AES, Blowfish, RC5, IDEA.
Pseudocode for adding and decrypting:
encryptedText = encrypt(plainText, key); // Encryption
plainText = decrypt(encryptedText, key); // Decryption
2. Asymmetric encryption
is also called public key encryption. The secret keys used for encryption and decryption are different, that is,
encryptKey !== decryptKey. The encryption key is public and is called the public key. The decryption key is kept secret and is called a secret key.
Common asymmetric encryption algorithms: RSA, DSA, ElGamal.
Pseudocode for adding and decrypting:
encryptedText = encrypt(plainText, publicKey); // Encryption
plainText = decrypt(encryptedText, privateKey); // Decryption
3. Comparison and application
In addition to the difference in secret keys, there is also a difference in computing speed. Generally speaking:
- Symmetric encryption is faster than asymmetric encryption.
- Asymmetric encryption is usually used to encrypt short text, and symmetric encryption is usually used to encrypt long text.
- The two can be used in combination, such as the HTTPS protocol, which can generate symmetric keys through RSA exchange during the handshake phase. In the subsequent communication phase, the data can be encrypted using a symmetric encryption algorithm, and the secret key is generated during the handshake phase.
Note: Symmetric key exchange does not necessarily need to be done through RSA, but can also be done through something like DH, which will not be expanded here.
5. Digital signature
From
signature, you can roughly guess the purpose of digital signature. The main functions are as follows:
- Confirm that the information comes from a specific subject.
确认信息完整、未被篡改。
为了达到上述目的,需要有两个过程:
发送方:生成签名。
接收方:验证签名。
1、发送方生成签名
计算原始信息的摘要。
通过私钥对摘要进行签名,得到电子签名。
将原始信息、电子签名,发送给接收方。
附:签名伪代码
digest = hash(message); // 计算摘要
digitalSignature = sign(digest, priviteKey); // 计算数字签名
2、接收方验证签名
通过公钥解开电子签名,得到摘要D1。(如果解不开,信息来源主体校验失败)
计算原始信息的摘要D2。
对比D1、D2,如果D1等于D2,说明原始信息完整、未被篡改。
附:签名验证伪代码
digest1 = verify(digitalSignature, publicKey); // 获取摘要
digest2 = hash(message); // 计算原始信息的摘要
digest1 === digest2 // 验证是否相等
3、对比非对称加密
由于RSA算法的特殊性,加密/解密、签名/验证 看上去特别像,很多同学都很容易混淆。先记住下面结论,后面有时间再详细介绍。
加密/解密:公钥加密,私钥解密。
签名/验证:私钥签名,公钥验证。
六、分组加密模式、填充、初始化向量
常见的对称加密算法,如AES、DES都采用了分组加密模式。这其中,有三个关键的概念需要掌握:模式、填充、初始化向量。
搞清楚这三点,才会知道crypto模块对称加密API的参数代表什么含义,出了错知道如何去排查。
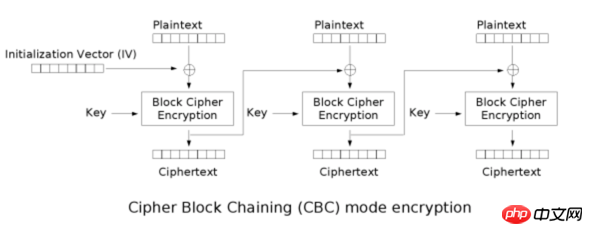
1、分组加密模式
所谓的分组加密,就是将(较长的)明文拆分成固定长度的块,然后对拆分的块按照特定的模式进行加密。
常见的分组加密模式有:ECB(不安全)、CBC(最常用)、CFB、OFB、CTR等。
以最简单的ECB为例,先将消息拆分成等分的模块,然后利用秘钥进行加密。
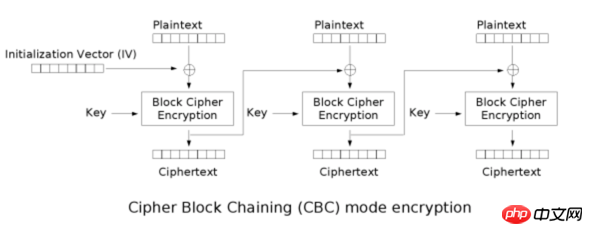
图片来源:这里,更多关于分组加密模式的介绍可以参考 wiki。
后面假设每个块的长度为128位
2、初始化向量:IV
为了增强算法的安全性,部分分组加密模式(CFB、OFB、CTR)中引入了初始化向量(IV),使得加密的结果随机化。也就是说,对于同一段明文,IV不同,加密的结果不同。
以CBC为例,每一个数据块,都与前一个加密块进行亦或运算后,再进行加密。对于第一个数据块,则是与IV进行亦或。
IV的大小跟数据块的大小有关(128位),跟秘钥的长度无关。
如图所示,图片来源 这里
3、填充:padding
分组加密模式需要对长度固定的块进行加密。分组拆分完后,最后一个数据块长度可能小于128位,此时需要进行填充以满足长度要求。
填充方式有多重。常见的填充方式有PKCS7。
假设分组长度为k字节,最后一个分组长度为k-last,可以看到:
不管明文长度是多少,加密之前都会会对明文进行填充 (不然解密函数无法区分最后一个分组是否被填充了,因为存在最后一个分组长度刚好等于k的情况)
如果最后一个分组长度等于k-last === k,那么填充内容为一个完整的分组 k k k ... k (k个字节)
如果最后一个分组长度小于k-last < k,那么填充内容为 k-last mod k
01 -- if lth mod k = k-1 02 02 -- if lth mod k = k-2 . . . k k ... k k -- if lth mod k = 0
概括来说
分组加密:先将明文切分成固定长度的块(128位),再进行加密。
分组加密的几种模式:ECB(不安全)、CBC(最常用)、CFB、OFB、CTR。
填充(padding):部分加密模式,当最后一个块的长度小于128位时,需要通过特定的方式进行填充。(ECB、CBC需要填充,CFB、OFB、CTR不需要填充)
初始化向量(IV):部分加密模式(CFB、OFB、CTR)会将 明文块 与 前一个密文块进行亦或操作。对于第一个明文块,不存在前一个密文块,因此需要提供初始化向量IV(把IV当做第一个明文块 之前的 密文块)。此外,IV也可以让加密结果随机化。
Related recommendations:
Simple method of using CryptoJS
Detailed explanation of the crypto encryption method of nodeJS
Detailed introduction about crypto-js
The above is the detailed content of Sharing of basic security knowledge in Nodejs crypto module. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
 The Next Meme Coin Supercycle: Meet XYZVerse (XYZ), the Heavyweight Champion of Sports and Meme Culture
Nov 03, 2024 pm 09:36 PM
The Next Meme Coin Supercycle: Meet XYZVerse (XYZ), the Heavyweight Champion of Sports and Meme Culture
Nov 03, 2024 pm 09:36 PM
As excitement builds in the crypto world for the last quarter of 2024, investors are on the lookout for digital assets with the potential to deliver extraordinary returns. Insights from successful crypto figures indicate that certain tokens could exp
 Crypto Influencer Cobie Burns 60% of the Supply of a Solana (SOL) Meme Coin Issued via Pump.fun
Nov 09, 2024 am 04:14 AM
Crypto Influencer Cobie Burns 60% of the Supply of a Solana (SOL) Meme Coin Issued via Pump.fun
Nov 09, 2024 am 04:14 AM
Jordan Fish, known more popularly as Cobie, burned 60% of the supply of a Solana (SOL) meme coin issued via Pump.fun on Friday, Nov. 8
 Robinhood Crypto gets rid of SEC investigation! OKX's company pays $84 million in settlement
Mar 04, 2025 am 09:15 AM
Robinhood Crypto gets rid of SEC investigation! OKX's company pays $84 million in settlement
Mar 04, 2025 am 09:15 AM
Signs of a change in US cryptocurrency regulatory policy: Robinhood and OKX case analysis Recently, US regulators' regulatory attitudes towards the cryptocurrency field have undergone subtle changes. Robinhood Crypto (RHC) successfully escaped from the Securities and Exchange Commission (SEC) investigation, while OKX's subsidiary AuxCayes FinTechCo. Ltd. reached a settlement with the U.S. Department of Justice (DOJ) to pay a $84 million fine. Together, these two incidents reveal dynamic adjustments in the US cryptocurrency regulation and the efforts of companies to actively adapt to the compliance environment. RobinhoodCrypto wins: SEC terminates investigation 2025 2
 Crypto Bitlord: The Man Who Mastered the Art of Influence in the Ever-Changing World of Cryptocurrency
Nov 16, 2024 am 04:34 AM
Crypto Bitlord: The Man Who Mastered the Art of Influence in the Ever-Changing World of Cryptocurrency
Nov 16, 2024 am 04:34 AM
Particularly in the world of meme coins, Bitlord—known for his honest attitude, keen insights, and open demeanor—has created a distinct niche for himself
 How to split a recorded blob stream into multiple 5 second WAV files using JavaScript and make sure it plays normally?
Apr 04, 2025 pm 02:39 PM
How to split a recorded blob stream into multiple 5 second WAV files using JavaScript and make sure it plays normally?
Apr 04, 2025 pm 02:39 PM
When recording using JavaScript, we encountered a requirement: the recorded blob stream needs to be...
 Digital cryptocurrency app trading software top10 (the latest ranking of 2025)
Mar 17, 2025 pm 05:12 PM
Digital cryptocurrency app trading software top10 (the latest ranking of 2025)
Mar 17, 2025 pm 05:12 PM
This article lists the top ten digital virtual currency exchange platforms, and ranks and introduces OKX, Binance, Gate.io, Huobi Global, Kraken, Coinbase, KuCoin, Crypto.com, Bitfinex and Bitstamp, analyzing the advantages and characteristics of each platform, such as OKX's powerful trading volume and user-friendly interface, Binance's huge user base and high liquidity, Gate.io's rich currency selection and low transaction fees, etc. When choosing a transaction, factors such as security, fees, currency selection, user interface, liquidity, and customer support are considered. The article emphasizes that investment should be cautious and recommends that users should be based on their own needs.
 How To Use JavaScript Maps - .map()
Jan 13, 2025 am 10:46 AM
How To Use JavaScript Maps - .map()
Jan 13, 2025 am 10:46 AM
From the classic for loop to the forEach() method, various techniques and methods are used to iterate through datasets in JavaScript. One of the most popular methods is the .map() method. .map() creates an array from calling a specific function on each item in the parent array. .map() is a non-mutating method that creates a new js array, as opposed to mutating methods, which only make changes to the calling array.
 Bitcoin Drops Below $67k, Memecoins Gain Strength Amidst Market Uncertainties
Oct 23, 2024 am 04:22 AM
Bitcoin Drops Below $67k, Memecoins Gain Strength Amidst Market Uncertainties
Oct 23, 2024 am 04:22 AM
Today, on October 22nd, 2024, the crypto market saw a small drop, amid geopolitical tensions and electoral uncertainties in the United States.




