 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Demonstration and prevention of CSRF attacks in PHP development
Demonstration and prevention of CSRF attacks in PHP development
Demonstration and prevention of CSRF attacks in PHP development
The full name of CSRF is Cross-site request forgery, and its Chinese name is cross-site request forgery (forged cross-site request [read more smoothly]). CSRF is a kind of web application that holds users logged in An attack method that performs unintended operations. Compared with XSS, CSRF takes advantage of the system's trust in the page browser, while XSS takes advantage of the system's trust in the user.
csrf attack, that is, cross site request forgery cross-site (domain name) request forgery, where forgery means forgery. There are many introductions about CSRF on the Internet. For example, a senior article explains in detail the attack methods of CSRF. Please refer to this article for a brief explanation: The realization of CSRF attacks relies on such a simple fact: when we use a browser to browse the web, we usually Open several browser tabs (or windows). If we log in to a site A, if site A tracks the user's session through cookies, then after the user logs in to site A, site A will set the settings on the user's client. Cookie, if site A has a page siteA-page.php (url resource) and site B knows the url address, and the address of this page is embedded in a page siteB-page.php of site B in some way, if At this time, the user opens siteB-page.php of site B while maintaining the session of site A. Then as long as the siteB-page.php page can trigger this url address (requesting the url resource of site A), a csrf attack is achieved.
The above explanation is very confusing, so let’s give a simple example to demonstrate.
1, background and normal request process
A site domain name is html5.yang.com, it has a /get-update.php?uid=uid&username=username address, which can be seen This address can pass some parameters through the get method. If the logic of this page is: it updates the username by judging whether the uid is legal. The script of this page is as follows:
<?php
// 这里简便起见, 从data.json中取出数据代替请求数据库
$str = file_get_contents('data.json');
$data = json_decode($str, true);
// 检查cookie和请求更改的uid, 实际应检查数据库中的用户是否存在
empty($_COOKIE['uid']) ||empty($_GET['uid']) || $_GET['uid'] != $data['id'] ? die('非法用户') : '';
// 检查username参数
$data['username'] = empty($_GET['username']) ? die('用户名不能为空') : $_GET['username'];
// 更新数据
$data['username'] = $_GET['username'];
if(file_put_contents('data.json', json_encode($data))) {
echo "用户名已更改为{$data['username']}<br>";
} else {
die('更新失败');
}Normally, the link to this page is placed under site A, such as the csrfdemo.php page of site A. After logging in to site A, the user can click this link to send a request, such as Site A has a page script that contains this link:
<?php
// 这里用一个data.json文件保存用户数据,模拟数据库中的数据
// 先初始化data.json中的数据为{"id":101,"username":"jack"}, 注意这句只让它执行一次, 然后把它注释掉
// file_put_contents('data.json','{"id":101,"username":"jack"}');
$data = json_decode(file_get_contents('data.json'), true);
// 这里为了简便, 省略了用户身份验证的过程
if ($data['username']) {
// 设置cookie
setcookie('uid', $data['id'], 0);
echo "登录成功, {$data['username']}<br>";
}
?>
<a href="http://html5.yang.com/csrfdemo/get-update.php?uid=101&username=json" rel="external nofollow" >
更新用户名为json
</a>Loading this page is as follows:

Click the link on the page to get to the get-update.php page:

The above is the normal request process. Let’s take a look at how site B implements the CSRF attack.
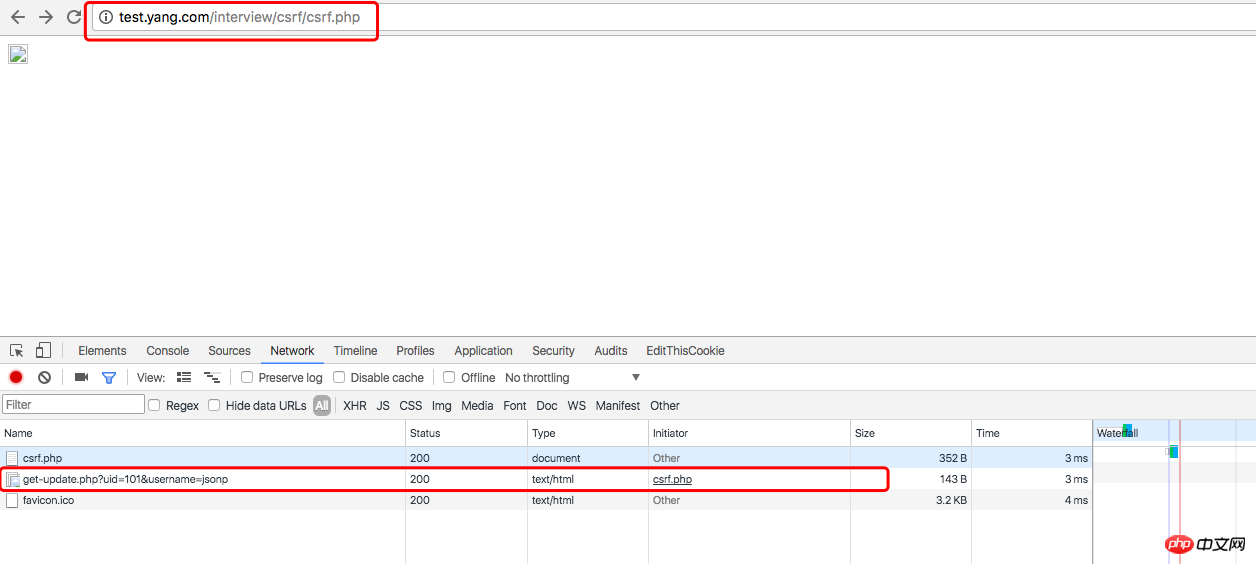
2, the simplest implementation of csrf attack
The domain name of site B is test.yang.com, which has a page csrf.php, as long as the user opens this while maintaining the session of site A page, then site B can implement CSRF attacks. As for why it is opened..., in fact, this situation is very common when we browse the web. For example, when I was writing this blog, I felt that I didn’t understand something about CSRF, and then I went to Baidu Well, there are a lot of results from Baidu. If there is a website called CSRF Encyclopedia Knowledge, which introduces CSRF in a very detailed and authoritative way, then I will probably click on it, but this website is actually a phishing website. It is on a certain website. The URL address of my blog editing page is embedded in a frequently visited page, so it can implement a CSRF attack on my blog. Okay, let’s get down to business, let’s take a look at the csrf.php script code:
<?php ?> <img src="http://html5.yang.com/csrfdemo/get-update.php?uid=101&username=jsonp">
You can see that the above code has no php code, only one img tag, img The src of the tag is the link to update the username of site A, but the username is changed to jsonp. Visit the csrf.php page of site B:
Visit again below Download the csrfdemo.php page of site A:

You can see that the user name has been changed to jsonp.
A brief analysis: The csrf.php of site B uses the img tag in HTML. We all know that the img tag has a src attribute, and the attribute value points to the address of the image that needs to be loaded. When the page is loaded, Loading an image is equivalent to initiating an http request to the address pointed to by src. As long as the address of the image is changed to a script address, the simplest CSRF attack will naturally be realized. In this way, CSRF is actually very easy to implement, but everyone is a "gentleman", and no one will be idle to do such "obscene" things. But you must not have the intention to harm others, and you must not have the intention to guard against others. Let’s take a look at how to simply prevent this simplest CSRF attack.
3, simple preventive measures
In fact, the preventive measures are relatively simple. Site A can determine the source of the request header in the get-update.php script. If the source is not site A, it can truncate the request. , add some code to get-update.php below:
<?php
// 检查上一页面是否为当前站点下的页面
if (!empty($_SERVER['HTTP_REFERER'])) {
if (parse_url($_SERVER['HTTP_REFERER'], PHP_URL_HOST) != 'html5.yang.com') {
// 可以设置http错误码或者指向一个无害的url地址
//header('HTTP/1.1 404 not found');
//header('HTTP/1.1 403 forbiden');
header('Location: http://html5.yang.com/favicon.ico');
// 这里需要注意一定要exit(), 否则脚本会接着执行
exit();
}
}
$str = file_get_contents('data.json');
// 代码省略但是,这样就万事大吉了吗,如果http请求头被伪造了呢?A站点升级了防御,B站点同时也可以升级攻击,通过curl请求来实现csrf,修改B站点的csrf.php代码如下:
<?php $url = 'http://html5.yang.com/csrfdemo/get-update.php?uid=101&username=jsonp'; $refer = 'http://html5.yang.com/'; // curl方法发起csrf攻击 $ch = curl_init(); curl_setopt($ch, CURLOPT_URL, $url); // 设置Referer curl_setopt($ch, CURLOPT_REFERER, $refer); // 这里需要携带上cookie, 因为A站点get-update.php对cooke进行了判断 curl_setopt($ch, CURLOPT_COOKIE, 'uid=101'); curl_exec($ch); curl_close($ch); ?> <img src="http://html5.yang.com/csrfdemo/get-update.php?uid=101&username=jsonp">
这样同样可以实现csrf攻击的目的。那么就没有比较好的防范方法了吗?
4,小结
下面我们回到问题的开始,站点A通过cookie来跟踪用户会话,在cookie中存放了重要的用户信息uid,get-update.php脚本通过判断用户的cookie正确与否来决定是否更改用户信息,看来靠cookie来跟踪会话并控制业务逻辑是不太安全的,还有最严重的一点:get-update.php通过get请求来修改用户信息,这个是大忌。所以站点A可以接着升级防御:用session来代替cookie来跟踪用户会话信息,将修改用户信息的逻辑重写,只允许用post方法来请求用户信息。站点B同样可以升级攻击:curl可以构造post请求,劫持session等等,不过这些我还没研究过,后续再说吧。
相关推荐:
php curl带有csrf-token验证模拟提交实例详解
The above is the detailed content of Demonstration and prevention of CSRF attacks in PHP development. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c
 7 PHP Functions I Regret I Didn't Know Before
Nov 13, 2024 am 09:42 AM
7 PHP Functions I Regret I Didn't Know Before
Nov 13, 2024 am 09:42 AM
If you are an experienced PHP developer, you might have the feeling that you’ve been there and done that already.You have developed a significant number of applications, debugged millions of lines of code, and tweaked a bunch of scripts to achieve op
 How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
This tutorial demonstrates how to efficiently process XML documents using PHP. XML (eXtensible Markup Language) is a versatile text-based markup language designed for both human readability and machine parsing. It's commonly used for data storage an
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
A string is a sequence of characters, including letters, numbers, and symbols. This tutorial will learn how to calculate the number of vowels in a given string in PHP using different methods. The vowels in English are a, e, i, o, u, and they can be uppercase or lowercase. What is a vowel? Vowels are alphabetic characters that represent a specific pronunciation. There are five vowels in English, including uppercase and lowercase: a, e, i, o, u Example 1 Input: String = "Tutorialspoint" Output: 6 explain The vowels in the string "Tutorialspoint" are u, o, i, a, o, i. There are 6 yuan in total
 Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Static binding (static::) implements late static binding (LSB) in PHP, allowing calling classes to be referenced in static contexts rather than defining classes. 1) The parsing process is performed at runtime, 2) Look up the call class in the inheritance relationship, 3) It may bring performance overhead.
 What are PHP magic methods (__construct, __destruct, __call, __get, __set, etc.) and provide use cases?
Apr 03, 2025 am 12:03 AM
What are PHP magic methods (__construct, __destruct, __call, __get, __set, etc.) and provide use cases?
Apr 03, 2025 am 12:03 AM
What are the magic methods of PHP? PHP's magic methods include: 1.\_\_construct, used to initialize objects; 2.\_\_destruct, used to clean up resources; 3.\_\_call, handle non-existent method calls; 4.\_\_get, implement dynamic attribute access; 5.\_\_set, implement dynamic attribute settings. These methods are automatically called in certain situations, improving code flexibility and efficiency.



