 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Linux Example (1) Using username and password authentication to connect to Linux
Linux Example (1) Using username and password authentication to connect to Linux
Linux Example (1) Using username and password authentication to connect to Linux
The content of this article is about using username and password authentication to connect to Linux. It has certain reference value. Friends in need can refer to it. I hope it will be helpful to you.
If you are using an SSH key pair, please refer to Connecting to a Linux Instance Using an SSH Key Pair.
If you want to use the management terminal of the ECS console, please refer to Step 3: Connect to the ECS instance.
Prerequisites
Before connecting remotely, you must complete the following work:
The instance must be in the running state. If the instance is not running, start the instance.
The instance has set a login password. If it is not set or the password is lost, please reset the password.
Instances can access the public network:
In a private network (VPC), purchase bandwidth when creating an instance and allocate it to a public IP address, or bind an elasticity address after creating the instance. Public IP address.
Under the classic network, your instance must be assigned a public IP address. The following is how to obtain a public IP address:
Whether it is a subscription instance or a pay-as-you-go instance, as long as you purchase bandwidth when creating the instance, you will be assigned a public IP address.
If you did not set the bandwidth when creating the subscription instance, you can upgrade or downgrade the configuration to obtain the public IP address.
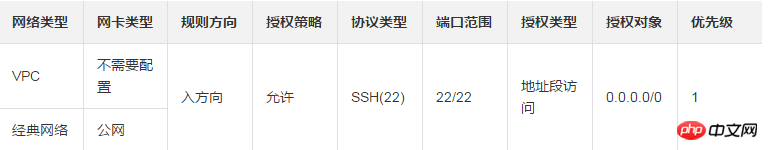
The security group where the instance is located must add the following security group rules (for specific operations, please refer to Adding security group rules):
Network type Network card type Rule direction Authorization policy Protocol type Port range Authorization type Authorization Object Priority
VPC No configuration required Inbound direction Allow SSH(22) 22/22 address segment access 0.0.0.0/0 1
Classic network Public network
Operation steps
Depending on the operating system of the local device, you can use the SSH protocol to remotely connect to the Linux instance in different ways:
Local The device uses Windows operating system
The local device uses Linux or Mac OS X system
The local device uses Android or iOS system
The local device uses Windows operating system
If the local device uses the Windows operating system, you can use remote connection software (such as PuTTY) to connect to the Linux instance. This document uses PuTTY as an example to explain how to remotely connect to a Linux instance. Before performing the following operations, please download PuTTY first.
Description
For specific operations, you can also watch the video: Assistant Series: How to Remotely Connect to a Linux Instance.
Follow the following steps to connect to the Linux instance.
Double-click putty.exe to start the program and enter the PuTTY main interface.
Configuration Session:
Host Name: Enter the public IP address or elastic public IP address of the instance.
Port: Enter 22.
Connection Type: Select SSH.
(Optional) Saved Session: If you want to enter the login interface directly without entering the above information in the future, you can specify an easily identifiable name for this session here, and then click Save to save.
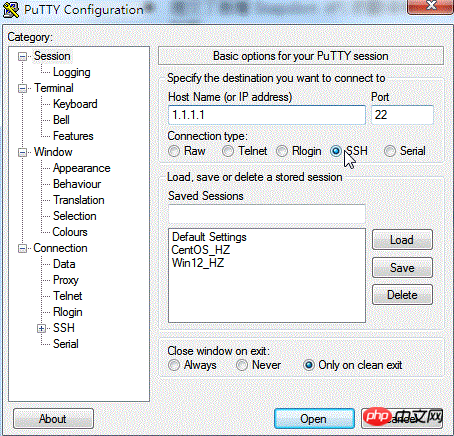
Click Open to enter the login page.
Description
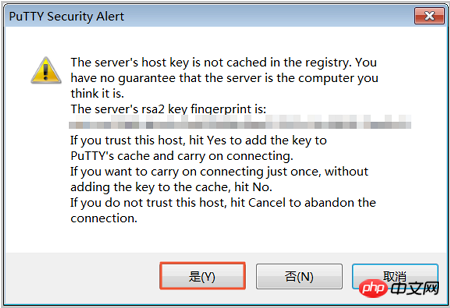
The following warning will appear when connecting for the first time, indicating that PuTTY cannot confirm the authenticity of the remote server (instance) and can only provide the public key fingerprint of the server. You need to confirm whether you trust the server. , and add its public key fingerprint to the registry of the local machine. Generally, select Yes. If this warning pops up again when you log in, it means that your instance may have a man-in-the-middle attack. For more detailed information about this warning, please refer to the PuTTY official website documentation.
According to the prompts, enter the username (default is root) and password of your ECS instance, and press Enter to confirm.
Description
Generally, Linux systems will not display the password input process.
When information similar to the following appears on the PuTTY interface, it means that you have successfully connected to the instance.
Welcome to Alibaba Cloud Elastic Compute Service !
At this point, you can start operating your instance.
The local device uses Linux or Mac OS X system
If the local device uses Linux or Mac OS X system, follow the steps below to connect to the instance remotely.
Enter the SSH command to connect: ssh root@the (elastic) public IP of the instance.
Enter the instance login password.
When information similar to the following appears on the interface, it means that you have successfully connected to the instance.
Welcome to Alibaba Cloud Elastic Compute Service !
At this point, you can start operating your instance.
Local device uses Android or iOS system
The above is the detailed content of Linux Example (1) Using username and password authentication to connect to Linux. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1387
1387
 52
52
 How to use docker desktop
Apr 15, 2025 am 11:45 AM
How to use docker desktop
Apr 15, 2025 am 11:45 AM
How to use Docker Desktop? Docker Desktop is a tool for running Docker containers on local machines. The steps to use include: 1. Install Docker Desktop; 2. Start Docker Desktop; 3. Create Docker image (using Dockerfile); 4. Build Docker image (using docker build); 5. Run Docker container (using docker run).
 How to view the docker process
Apr 15, 2025 am 11:48 AM
How to view the docker process
Apr 15, 2025 am 11:48 AM
Docker process viewing method: 1. Docker CLI command: docker ps; 2. Systemd CLI command: systemctl status docker; 3. Docker Compose CLI command: docker-compose ps; 4. Process Explorer (Windows); 5. /proc directory (Linux).
 What to do if the docker image fails
Apr 15, 2025 am 11:21 AM
What to do if the docker image fails
Apr 15, 2025 am 11:21 AM
Troubleshooting steps for failed Docker image build: Check Dockerfile syntax and dependency version. Check if the build context contains the required source code and dependencies. View the build log for error details. Use the --target option to build a hierarchical phase to identify failure points. Make sure to use the latest version of Docker engine. Build the image with --t [image-name]:debug mode to debug the problem. Check disk space and make sure it is sufficient. Disable SELinux to prevent interference with the build process. Ask community platforms for help, provide Dockerfiles and build log descriptions for more specific suggestions.
 What computer configuration is required for vscode
Apr 15, 2025 pm 09:48 PM
What computer configuration is required for vscode
Apr 15, 2025 pm 09:48 PM
VS Code system requirements: Operating system: Windows 10 and above, macOS 10.12 and above, Linux distribution processor: minimum 1.6 GHz, recommended 2.0 GHz and above memory: minimum 512 MB, recommended 4 GB and above storage space: minimum 250 MB, recommended 1 GB and above other requirements: stable network connection, Xorg/Wayland (Linux)
 vscode cannot install extension
Apr 15, 2025 pm 07:18 PM
vscode cannot install extension
Apr 15, 2025 pm 07:18 PM
The reasons for the installation of VS Code extensions may be: network instability, insufficient permissions, system compatibility issues, VS Code version is too old, antivirus software or firewall interference. By checking network connections, permissions, log files, updating VS Code, disabling security software, and restarting VS Code or computers, you can gradually troubleshoot and resolve issues.
 Can vscode be used for mac
Apr 15, 2025 pm 07:36 PM
Can vscode be used for mac
Apr 15, 2025 pm 07:36 PM
VS Code is available on Mac. It has powerful extensions, Git integration, terminal and debugger, and also offers a wealth of setup options. However, for particularly large projects or highly professional development, VS Code may have performance or functional limitations.
 What is vscode What is vscode for?
Apr 15, 2025 pm 06:45 PM
What is vscode What is vscode for?
Apr 15, 2025 pm 06:45 PM
VS Code is the full name Visual Studio Code, which is a free and open source cross-platform code editor and development environment developed by Microsoft. It supports a wide range of programming languages and provides syntax highlighting, code automatic completion, code snippets and smart prompts to improve development efficiency. Through a rich extension ecosystem, users can add extensions to specific needs and languages, such as debuggers, code formatting tools, and Git integrations. VS Code also includes an intuitive debugger that helps quickly find and resolve bugs in your code.
 How to back up vscode settings and extensions
Apr 15, 2025 pm 05:18 PM
How to back up vscode settings and extensions
Apr 15, 2025 pm 05:18 PM
How to back up VS Code configurations and extensions? Manually backup the settings file: Copy the key JSON files (settings.json, keybindings.json, extensions.json) to a safe location. Take advantage of VS Code synchronization: enable synchronization with your GitHub account to automatically back up all relevant settings and extensions. Use third-party tools: Back up configurations with reliable tools and provide richer features such as version control and incremental backups.



