 Java
Java
 javaTutorial
javaTutorial
 Method implementation based on SpringBoot password retrieval (picture and text)
Method implementation based on SpringBoot password retrieval (picture and text)
Method implementation based on SpringBoot password retrieval (picture and text)
The content of this article is about the implementation of the SpringBoot password retrieval method (pictures and texts). It has certain reference value. Friends in need can refer to it. I hope it will be helpful to you.
I am working on my own project recently, and one of the functions that everyone knows is to retrieve passwords. I’ll share my approach here, because there are so many pitfalls in the process. So record it.
Used technologies: SpringBoot1.5.6, JPA, SpringSecurity4, MySQL, BootStrap, etc. . .
Password retrieval flow chart:
First of all, let me introduce to you the basic principles of password retrieval: 
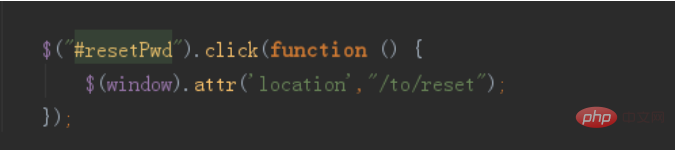
Next, let’s implement it according to the flow chart. The first step is to click to jump to the password retrieval interface: I use this method. You can feel free to

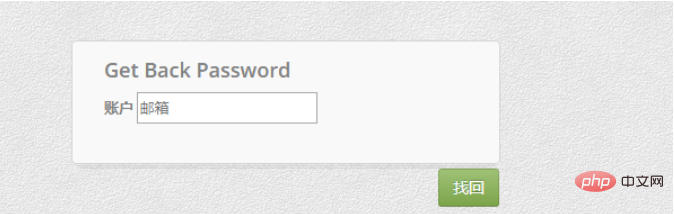
The password retrieval interface is:
Step 2: Determine whether the entered account is valid

The following is the generated URL link if it exists:

backPassword:
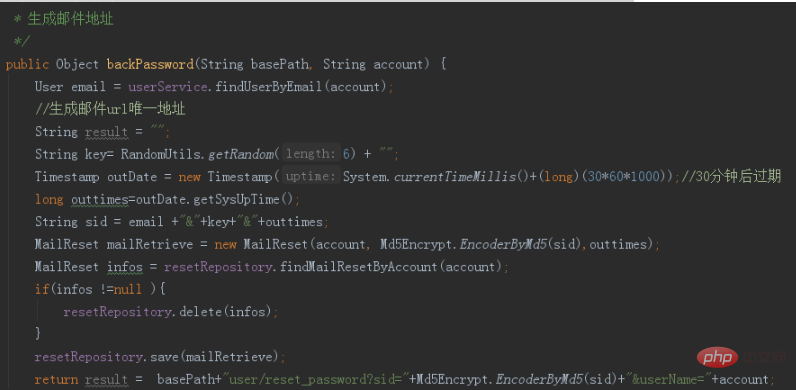
Step 3: Judgment Whether the account exists in the reset table. The reset table is a table that saves URLs (expiration time, sid, account information, etc.)


The purpose of this is: if the data exists and is not deleted, the next time you retrieve the password, 2 data with the same account but different sid will be generated, like this The disadvantage is: I don’t know which URL to return when sending an email, because there are 2 URLs
Step 4: Send the email

Let’s look at it first The following effect:

#The next step is the important part: how to handle the verification link. First we can see that /user/reset_password is a request followed by its parameters, so remember !
We need to write a request, the route is /user/reset_password, and at the same time, we need to allow the request in SpringSecurity. The verification process is as follows: first, compare the sid and userName (that is, the email address) passed from the request with the sid and account in the database, and also compare whether the time is within the validity period of 30 minutes. If these are satisfied It returns true, otherwise false. It should be noted that there is a replacement here where spaces are replaced with numbers. This is because the numbers are automatically converted to spaces when the HTML is passed to the backend. If it is not replaced with numbers, it will always prompt verification failure! ! ! Once true is returned, it means that the verification URL has passed, and it will jump to the password reset interface:

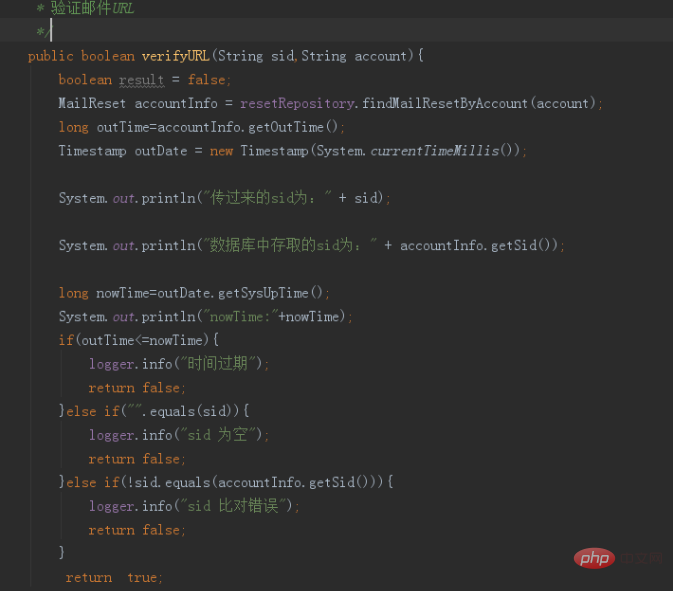
Note: I have no verification here For optimization, there should not be so many if else nests
Release the request route: if not, click the link and it will jump to the login interface

Jump to the reset page. If the passwords we enter twice are inconsistent, the following prompt will appear. I used JS to do the verification:

Of course, for the sake of rigor, we also perform two password verifications in the background. If the inputs are consistent, the information will be updated. If they are inconsistent, an error will be returned.
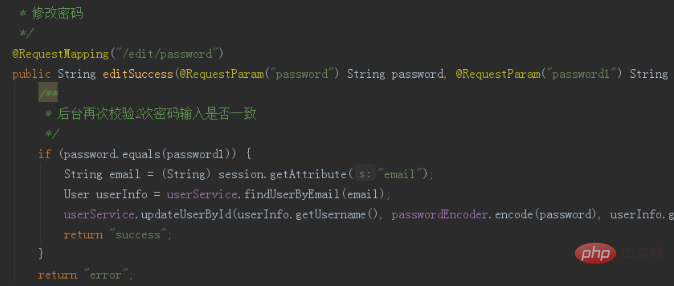
There is nothing here, just pay attention to using MD5 salt to encrypt the password before saving it to the database, and then save it. Let’s take a look at the effect of entering the correct password twice: the page prompts that the modification is successful and no error is reported in the background. At this time Use the new password to log in

The above is the detailed content of Method implementation based on SpringBoot password retrieval (picture and text). For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1389
1389
 52
52
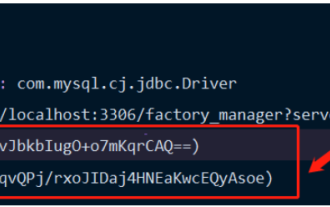 How Springboot integrates Jasypt to implement configuration file encryption
Jun 01, 2023 am 08:55 AM
How Springboot integrates Jasypt to implement configuration file encryption
Jun 01, 2023 am 08:55 AM
Introduction to Jasypt Jasypt is a java library that allows a developer to add basic encryption functionality to his/her project with minimal effort and does not require a deep understanding of how encryption works. High security for one-way and two-way encryption. , standards-based encryption technology. Encrypt passwords, text, numbers, binaries... Suitable for integration into Spring-based applications, open API, for use with any JCE provider... Add the following dependency: com.github.ulisesbocchiojasypt-spring-boot-starter2. 1.1Jasypt benefits protect our system security. Even if the code is leaked, the data source can be guaranteed.
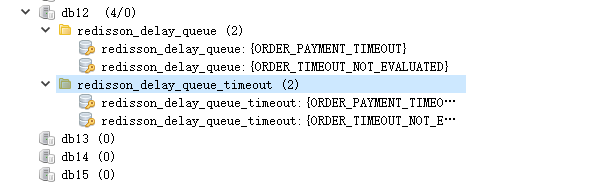 How SpringBoot integrates Redisson to implement delay queue
May 30, 2023 pm 02:40 PM
How SpringBoot integrates Redisson to implement delay queue
May 30, 2023 pm 02:40 PM
Usage scenario 1. The order was placed successfully but the payment was not made within 30 minutes. The payment timed out and the order was automatically canceled. 2. The order was signed and no evaluation was conducted for 7 days after signing. If the order times out and is not evaluated, the system defaults to a positive rating. 3. The order is placed successfully. If the merchant does not receive the order for 5 minutes, the order is cancelled. 4. The delivery times out, and push SMS reminder... For scenarios with long delays and low real-time performance, we can Use task scheduling to perform regular polling processing. For example: xxl-job Today we will pick
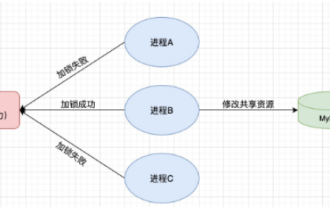 How to use Redis to implement distributed locks in SpringBoot
Jun 03, 2023 am 08:16 AM
How to use Redis to implement distributed locks in SpringBoot
Jun 03, 2023 am 08:16 AM
1. Redis implements distributed lock principle and why distributed locks are needed. Before talking about distributed locks, it is necessary to explain why distributed locks are needed. The opposite of distributed locks is stand-alone locks. When we write multi-threaded programs, we avoid data problems caused by operating a shared variable at the same time. We usually use a lock to mutually exclude the shared variables to ensure the correctness of the shared variables. Its scope of use is in the same process. If there are multiple processes that need to operate a shared resource at the same time, how can they be mutually exclusive? Today's business applications are usually microservice architecture, which also means that one application will deploy multiple processes. If multiple processes need to modify the same row of records in MySQL, in order to avoid dirty data caused by out-of-order operations, distribution needs to be introduced at this time. The style is locked. Want to achieve points
 How to solve the problem that springboot cannot access the file after reading it into a jar package
Jun 03, 2023 pm 04:38 PM
How to solve the problem that springboot cannot access the file after reading it into a jar package
Jun 03, 2023 pm 04:38 PM
Springboot reads the file, but cannot access the latest development after packaging it into a jar package. There is a situation where springboot cannot read the file after packaging it into a jar package. The reason is that after packaging, the virtual path of the file is invalid and can only be accessed through the stream. Read. The file is under resources publicvoidtest(){Listnames=newArrayList();InputStreamReaderread=null;try{ClassPathResourceresource=newClassPathResource("name.txt");Input
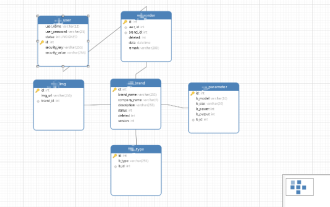 How to implement Springboot+Mybatis-plus without using SQL statements to add multiple tables
Jun 02, 2023 am 11:07 AM
How to implement Springboot+Mybatis-plus without using SQL statements to add multiple tables
Jun 02, 2023 am 11:07 AM
When Springboot+Mybatis-plus does not use SQL statements to perform multi-table adding operations, the problems I encountered are decomposed by simulating thinking in the test environment: Create a BrandDTO object with parameters to simulate passing parameters to the background. We all know that it is extremely difficult to perform multi-table operations in Mybatis-plus. If you do not use tools such as Mybatis-plus-join, you can only configure the corresponding Mapper.xml file and configure The smelly and long ResultMap, and then write the corresponding sql statement. Although this method seems cumbersome, it is highly flexible and allows us to
 Comparison and difference analysis between SpringBoot and SpringMVC
Dec 29, 2023 am 11:02 AM
Comparison and difference analysis between SpringBoot and SpringMVC
Dec 29, 2023 am 11:02 AM
SpringBoot and SpringMVC are both commonly used frameworks in Java development, but there are some obvious differences between them. This article will explore the features and uses of these two frameworks and compare their differences. First, let's learn about SpringBoot. SpringBoot was developed by the Pivotal team to simplify the creation and deployment of applications based on the Spring framework. It provides a fast, lightweight way to build stand-alone, executable
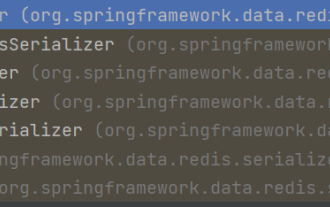 How SpringBoot customizes Redis to implement cache serialization
Jun 03, 2023 am 11:32 AM
How SpringBoot customizes Redis to implement cache serialization
Jun 03, 2023 am 11:32 AM
1. Customize RedisTemplate1.1, RedisAPI default serialization mechanism. The API-based Redis cache implementation uses the RedisTemplate template for data caching operations. Here, open the RedisTemplate class and view the source code information of the class. publicclassRedisTemplateextendsRedisAccessorimplementsRedisOperations, BeanClassLoaderAware{//Declare key, Various serialization methods of value, the initial value is empty @NullableprivateRedisSe
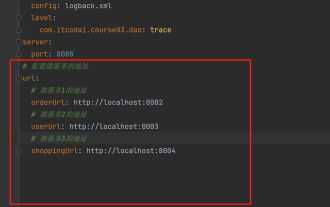 How to get the value in application.yml in springboot
Jun 03, 2023 pm 06:43 PM
How to get the value in application.yml in springboot
Jun 03, 2023 pm 06:43 PM
In projects, some configuration information is often needed. This information may have different configurations in the test environment and the production environment, and may need to be modified later based on actual business conditions. We cannot hard-code these configurations in the code. It is best to write them in the configuration file. For example, you can write this information in the application.yml file. So, how to get or use this address in the code? There are 2 methods. Method 1: We can get the value corresponding to the key in the configuration file (application.yml) through the ${key} annotated with @Value. This method is suitable for situations where there are relatively few microservices. Method 2: In actual projects, When business is complicated, logic



