https certificate generation steps

https certificate generation steps:
1. Generate key
Generate key ( jks file), the code here is to generate a "zinc_server.jks" key.
-alias zinc_server -keyalg RSA -keystore zinc_server.jks -validity 3600 -storepass 123456
Parameter description:
genkey creates a default file ".keystore" in the user's home directory, and also generates an alias of mykey, which contains the user's public key, private key and Certificate
alias: Generate an alias
keystore: Specify the name of the keystore
validity: Specify how many days the created certificate is valid
storepass: Specify the password Keystore password (password required to obtain keystore information)
keyalg: Specify the key algorithm (such as: RSA, DSA; if not specified, DSA is used by default)
More parameters :
keysize: Specify the key length
keypass: Specify the password of the alias entry (password of the private key)
dname: Specify the certificate owner information
list: Display the certificate information in the key store
keytool -list -keystore 指定keystore -storepass 密码
v: Display the certificate details in the key store
keytool -list -v -keystore 指定keystore -storepass 密码
2. Issue the certificate
The zinc_server.jks key in Section 1 is used here to issue the zinc_server.cer certificate
keytool -export -alias zinc_server -file zinc_server.cer -keystore zinc_server.jks -storepass 123456
3. Generate the certificate set bks used by Android
In Android You need to use the certificate set in bks format, so if you use it in Android, you need to convert the certificate generated in section 2. Use the following command
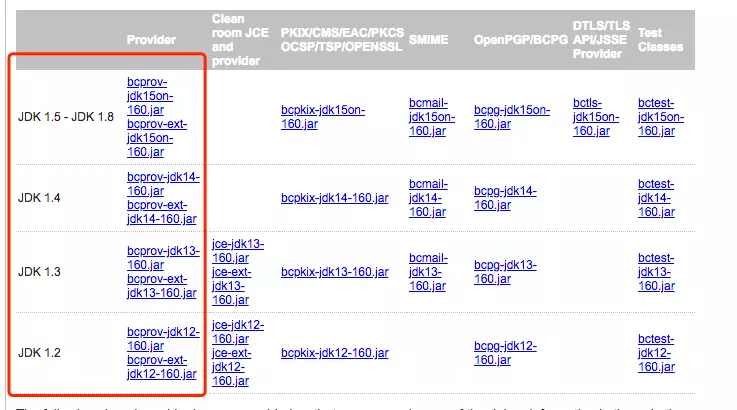
keytool -importcert -file zinc_server.cer -keystore zinc_server.bks -storetype BKS -provider org.bouncycastle.jce.provider.BouncyCastleProvider
If you use the above command, you may encounter an exception that the BouncyCastleProvider class cannot be found. At this time, you need to configure the environment a little
Enter bouncycastle official website to download The corresponding jdk version. Place the downloaded jar package in the path of your jdk installation/Contents/Home/jre/lib/ext, and try again.
4. Convert jks to bks
The content of this section is because some apps need to perform two-way verification and need to The client's key is placed in the app.
The above is the detailed content of https certificate generation steps. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1378
1378
 52
52
 How to use Nginx Proxy Manager to implement reverse proxy under HTTPS protocol
Sep 26, 2023 am 08:40 AM
How to use Nginx Proxy Manager to implement reverse proxy under HTTPS protocol
Sep 26, 2023 am 08:40 AM
How to use NginxProxyManager to implement reverse proxy under HTTPS protocol. In recent years, with the popularity of the Internet and the diversification of application scenarios, the access methods of websites and applications have become more and more complex. In order to improve website access efficiency and security, many websites have begun to use reverse proxies to handle user requests. The reverse proxy for the HTTPS protocol plays an important role in protecting user privacy and ensuring communication security. This article will introduce how to use NginxProxy
 How to use Nginx Proxy Manager to implement automatic jump from HTTP to HTTPS
Sep 26, 2023 am 11:19 AM
How to use Nginx Proxy Manager to implement automatic jump from HTTP to HTTPS
Sep 26, 2023 am 11:19 AM
How to use NginxProxyManager to implement automatic jump from HTTP to HTTPS. With the development of the Internet, more and more websites are beginning to use the HTTPS protocol to encrypt data transmission to improve data security and user privacy protection. Since the HTTPS protocol requires the support of an SSL certificate, certain technical support is required when deploying the HTTPS protocol. Nginx is a powerful and commonly used HTTP server and reverse proxy server, and NginxProxy
 Nginx with SSL: Configure HTTPS to protect your web server
Jun 09, 2023 pm 09:24 PM
Nginx with SSL: Configure HTTPS to protect your web server
Jun 09, 2023 pm 09:24 PM
Nginx is a high-performance web server software and a powerful reverse proxy server and load balancer. With the rapid development of the Internet, more and more websites are beginning to use the SSL protocol to protect sensitive user data, and Nginx also provides powerful SSL support, making the security performance of the web server even further. This article will introduce how to configure Nginx to support the SSL protocol and protect the security performance of the web server. What is SSL protocol? SSL (SecureSocket
 What does the https workflow look like?
Apr 07, 2024 am 09:27 AM
What does the https workflow look like?
Apr 07, 2024 am 09:27 AM
The https workflow includes steps such as client-initiated request, server response, SSL/TLS handshake, data transmission, and client-side rendering. Through these steps, the security and integrity of data during transmission can be ensured.
 How to configure https in tomcat
Jan 05, 2024 pm 05:15 PM
How to configure https in tomcat
Jan 05, 2024 pm 05:15 PM
Configuration steps: 1. Obtain the SSL certificate; 2. Configure the SSL certificate; 3. Edit the Tomcat configuration file; 4. Restart Tomcat. Detailed introduction: 1. You need to obtain an SSL certificate, either a self-signed certificate or a valid SSL certificate from a certification agency (such as Let's Encrypt); 2. Place the obtained SSL certificate and private key files on the server and ensure that these files Located in a safe location, only users with sufficient permissions can access; 3. Edit Tomcat configuration files, etc.
 Solution: urllib3 ProxySchemeUnknown(proxy.scheme)
Feb 29, 2024 pm 07:01 PM
Solution: urllib3 ProxySchemeUnknown(proxy.scheme)
Feb 29, 2024 pm 07:01 PM
The reason for the error is that the ProxySchemeUnknown(proxy.scheme) error of urllib3 is usually caused by the use of an unsupported proxy protocol. In this case, urllib3 does not recognize the proxy server's protocol type and therefore cannot use the proxy for network connections. To resolve this issue, you need to ensure that you are using a supported proxy protocol, such as HTTP or https. How to resolve To resolve this issue, you need to ensure that you are using a supported proxy protocol, such as HTTP or HTTPS. You can solve this problem by setting the proxy parameters of urllib3. If you are using an http proxy, the code example is as follows: importurllib3http
 How to use Nginx to implement HTTPS two-way authentication
Jun 03, 2023 pm 08:38 PM
How to use Nginx to implement HTTPS two-way authentication
Jun 03, 2023 pm 08:38 PM
The difference between one-way verification and two-way verification: One-way verification: refers to the client verifying the server-side certificate, and the server does not need to verify the client certificate. Two-way verification: refers to the client verifying the server-side certificate, and the server also needs to verify the client certificate through the CA's public key certificate. Detailed handshake process: One-way authentication The browser sends a connection request to the security server. 1. The server sends its own certificate and certificate-related information to the client browser. 2. The client browser checks whether the certificate sent by the server is issued by the CA center it trusts. If it is, continue to execute the agreement; if not, the client's browser will give the client a warning message: warning the client that this certificate is not trustworthy and asking the client if it needs to continue. 3. Pick up customers
 How Nginx firewall ensures HTTPS secure communication
Jun 10, 2023 am 10:16 AM
How Nginx firewall ensures HTTPS secure communication
Jun 10, 2023 am 10:16 AM
In today's Internet era, secure communication has become an indispensable part. Especially in HTTPS communication, how to ensure its security is particularly important. As a popular web server and reverse proxy server, Nginx's firewall can also play an important role in ensuring HTTPS secure communication. This article will discuss the Nginx firewall from the following aspects. TLS/SSL encryption The security of HTTPS communication is mainly based on TLS/SSL encryption technology, which can prevent data from being transmitted during transmission.



