

The Writeup shared today is a dynamic password OTP (One Time Password) for the target system that the author is participating in vulnerability testing, and is implemented by using a simple brute force enumeration method. Bypassing or cracking the target system's two-factor authentication mechanism 2FA (Two-Factor Authentication). The target system is the website of India's largest travel service company, which uses dynamic password OTP as a means of implementing two-factor authentication 2FA.
Generally speaking, OTP is a 4-digit combination from 0000 to 9999. If OTP has 10,000 possible combinations, in today's powerful computer era, it only takes a few minutes to process 10,000 combinations. time. So, if the OTP's verification mechanism is improper, anyone can bypass it through simple brute force enumeration.
Why can I bypass 2FA?
The target system does not rate limit unsuccessful request attempts.
The target system has no new dynamic password measures for unsuccessful request attempts.
Prerequisite preparation:
Web browser, BurpSuite.
The recurrence process of bypassing 2FA
The recurrence process of bypassing 2FA
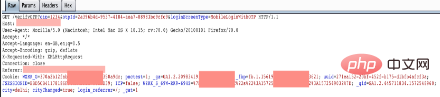
1. Open BurpSuite and log in to the target system website using your mobile phone number , here, deliberately enter the wrong dynamic OTP sent by the system to your mobile phone (here we enter 1234 casually), and then use BurpSuite to capture the traffic;
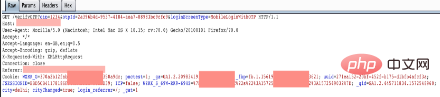
We can see from BurpSuite Relevant information to the OTP API – verifyOTP?otp=:
2. Right-click the OTP sending process and Send to intruder:
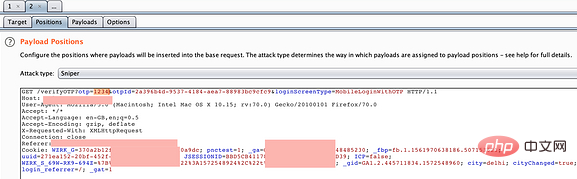
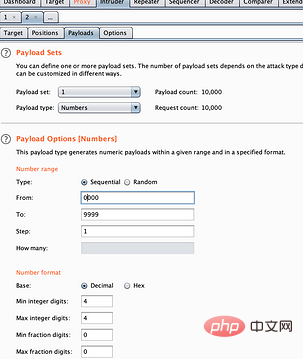
3. Select the otp=1234 placeholder and set it to simple violent enumeration variable mode:
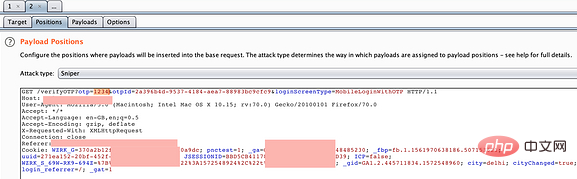
4. Select the Payload tag item, Modify it to any combination, and then click attack:
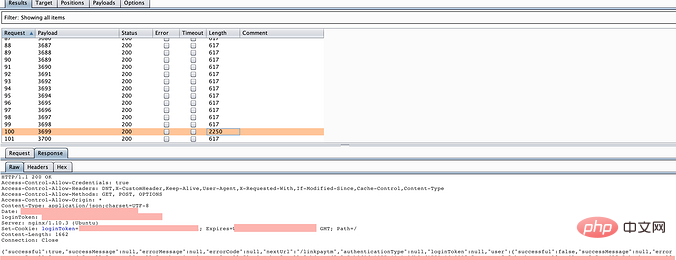
5. The attack begins. From the enumeration response result, we can see an abnormal response with a length of 2250. As expected, this is it:
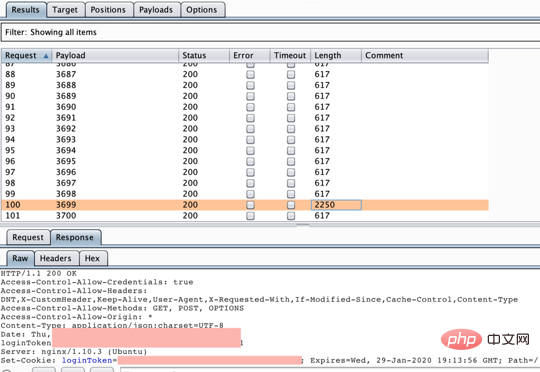
6. Use this OTP to log in, It can be successful and effective!
Related tutorial recommendations: web server security
The above is the detailed content of Experiment on simple brute force enumeration method to bypass the 2FA verification mechanism of the target system. For more information, please follow other related articles on the PHP Chinese website!
 Main purpose of file system
Main purpose of file system
 How to solve garbled tomcat logs
How to solve garbled tomcat logs
 How to restore mysql database
How to restore mysql database
 How to use the decode function
How to use the decode function
 Is there a big difference between c language and Python?
Is there a big difference between c language and Python?
 index.html function
index.html function
 Win10 does not support the disk layout solution of Uefi firmware
Win10 does not support the disk layout solution of Uefi firmware
 How to open state file
How to open state file
 No service on mobile data
No service on mobile data