What does machine language that computers can directly recognize consist of?
The machine language that the computer can directly recognize is composed of operation code and operand. The operation code specifies the operation of the instruction and is the keyword in the instruction and cannot be defaulted; the operand represents the operation of the instruction. The operation object and the computer's instruction format have a great relationship with the machine's word length, memory capacity and instruction function.
Machine language is the program language or instruction code that the machine can directly recognize. It does not need to be translated. Each An operation code has a corresponding circuit inside the computer to complete it, or refers to a programming language or instruction code that can be directly understood and accepted by the machine without translation. Machine language uses absolute addresses and absolute opcodes. Different computers have their own machine languages, that is, instruction systems. From a usage perspective, machine language is the lowest level language.
Machine language instruction is a binary code consisting of two parts: opcode and operand. The opcode specifies the operation of the instruction. It is a keyword in the instruction and cannot be defaulted. The operand represents the operand of the instruction. The computer's instruction format has a great relationship with the machine's word length, memory capacity and instruction function.
From the perspective of facilitating program design, increasing parallelism of basic operations, and improving instruction functionality, instructions should contain a variety of information. However, in some instructions, because part of the information may be useless, this will waste the storage space occupied by the instruction and increase the number of memory accesses, which may actually affect the speed.
Therefore, how to design the instruction format reasonably and scientifically, so that the instruction can not only give enough information, but also make its length match the word length of the machine as much as possible, so as to save storage space and shorten the value acquisition time. , improve the performance of the machine, which is an important issue in the design of instruction format.
Computers process various data by executing instructions. In order to indicate the source of data, the destination of operation results and the operations performed, an instruction must contain the following information:
(1) Operation code. It specifies the nature and function of the operation. A computer may have dozens to hundreds of instructions, each instruction has a corresponding operation code, and the computer completes different operations by recognizing the operation code.
(2) The address of the operand. The CPU can obtain the required operands through this address.
(3) Storage address of the operation result. The result of processing the operand is saved at this address for reuse.
(4) The address of the next instruction. When executing a program, most instructions are fetched from the main memory in order and executed. Only when a transfer instruction is encountered, the execution order of the program will change. In order to compress the length of the instruction, a program counter (ProgramCounter, PC) can be used to store the instruction address. Every time an instruction is executed, the instruction address of the PC is automatically set to 1 (assuming that the instruction only occupies one main memory unit), indicating the address of the next instruction to be executed. When a transfer instruction is encountered, the transfer address is used to modify the contents of the PC. Due to the use of PC, the address of the next instruction to be executed does not need to be explicitly given in the instruction.
An instruction actually includes two kinds of information, namely Operation code and Address code. The operation code (OperationCode, OP) is used to represent the operation to be completed by the instruction (such as addition, subtraction, multiplication, division, data transfer, etc.). Its length depends on the number of instructions in the instruction system. The address code is used to describe the operand of the instruction. It either directly gives the operand, or indicates the memory address or register address of the operand (that is, the register name).
If you want to know more about programming learning, please pay attention to the php training column!
The above is the detailed content of What does machine language that computers can directly recognize consist of?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
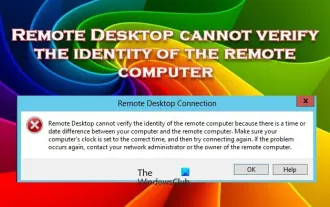 Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Windows Remote Desktop Service allows users to access computers remotely, which is very convenient for people who need to work remotely. However, problems can be encountered when users cannot connect to the remote computer or when Remote Desktop cannot authenticate the computer's identity. This may be caused by network connection issues or certificate verification failure. In this case, the user may need to check the network connection, ensure that the remote computer is online, and try to reconnect. Also, ensuring that the remote computer's authentication options are configured correctly is key to resolving the issue. Such problems with Windows Remote Desktop Services can usually be resolved by carefully checking and adjusting settings. Remote Desktop cannot verify the identity of the remote computer due to a time or date difference. Please make sure your calculations
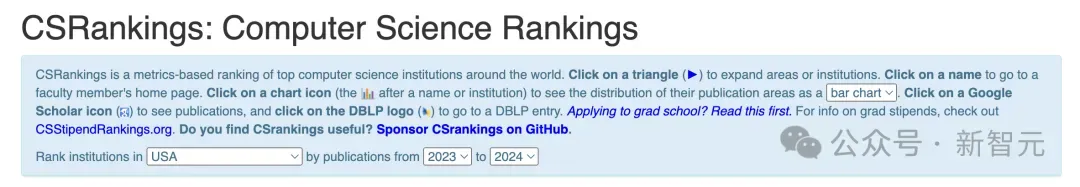 2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
The 2024CSRankings National Computer Science Major Rankings have just been released! This year, in the ranking of the best CS universities in the United States, Carnegie Mellon University (CMU) ranks among the best in the country and in the field of CS, while the University of Illinois at Urbana-Champaign (UIUC) has been ranked second for six consecutive years. Georgia Tech ranked third. Then, Stanford University, University of California at San Diego, University of Michigan, and University of Washington tied for fourth place in the world. It is worth noting that MIT's ranking fell and fell out of the top five. CSRankings is a global university ranking project in the field of computer science initiated by Professor Emery Berger of the School of Computer and Information Sciences at the University of Massachusetts Amherst. The ranking is based on objective
 What is e in computer
Aug 31, 2023 am 09:36 AM
What is e in computer
Aug 31, 2023 am 09:36 AM
The "e" of computer is the scientific notation symbol. The letter "e" is used as the exponent separator in scientific notation, which means "multiplied to the power of 10". In scientific notation, a number is usually written as M × 10^E, where M is a number between 1 and 10 and E represents the exponent.
 Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
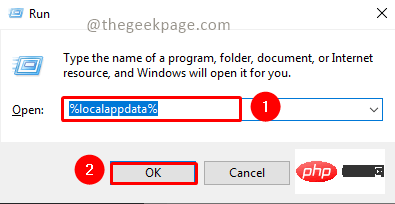
<p>MSTeams is the trusted platform to communicate, chat or call with teammates and colleagues. Error code 80090016 on MSTeams and the message <strong>Your computer's Trusted Platform Module has failed</strong> may cause difficulty logging in. The app will not allow you to log in until the error code is resolved. If you encounter such messages while opening MS Teams or any other Microsoft application, then this article can guide you to resolve the issue. </p><h2&
 What does computer cu mean?
Aug 15, 2023 am 09:58 AM
What does computer cu mean?
Aug 15, 2023 am 09:58 AM
The meaning of cu in a computer depends on the context: 1. Control Unit, in the central processor of a computer, CU is the component responsible for coordinating and controlling the entire computing process; 2. Compute Unit, in a graphics processor or other accelerated processor, CU is the basic unit for processing parallel computing tasks.
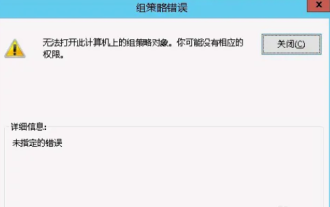 Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Occasionally, the operating system may malfunction when using a computer. The problem I encountered today was that when accessing gpedit.msc, the system prompted that the Group Policy object could not be opened because the correct permissions may be lacking. The Group Policy object on this computer could not be opened. Solution: 1. When accessing gpedit.msc, the system prompts that the Group Policy object on this computer cannot be opened because of lack of permissions. Details: The system cannot locate the path specified. 2. After the user clicks the close button, the following error window pops up. 3. Check the log records immediately and combine the recorded information to find that the problem lies in the C:\Windows\System32\GroupPolicy\Machine\registry.pol file
 What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
Solution to the problem that steam cannot connect to the remote computer: 1. In the game platform, click the "steam" option in the upper left corner; 2. Open the menu and select the "Settings" option; 3. Select the "Remote Play" option; 4. Check Activate the "Remote Play" function and click the "OK" button.
 Python script to log out of computer
Sep 05, 2023 am 08:37 AM
Python script to log out of computer
Sep 05, 2023 am 08:37 AM
In today's digital age, automation plays a vital role in streamlining and simplifying various tasks. One of these tasks is to log off the computer, which is usually done manually by selecting the logout option from the operating system's user interface. But what if we could automate this process using a Python script? In this blog post, we'll explore how to create a Python script that can log off your computer with just a few lines of code. In this article, we'll walk through the step-by-step process of creating a Python script for logging out of your computer. We'll cover the necessary prerequisites, discuss different ways to log out programmatically, and provide a step-by-step guide to writing the script. Additionally, we will address platform-specific considerations and highlight best practices



