How to partition a Linux disk
Linux disk partition: 1. Linux disk can be set with boot partition, swap partition and root partition; 2. Set the directory where the partition is mounted; 3. Allocate partitions to [/home]; 4. [/boot] Just set 100MB.

【Recommended related articles: linux tutorial】
Linux disk partition:
1. Linux can be divided into 3 partitions by default, namely the boot partition, the swap partition and the root partition.

Second, set the directory where the partition is mounted
/ ----The root directory, the only directory that must be mounted. Don't hesitate, pick a partition and mount it!
Swap ----Swap partition may not be necessary, but according to tradition, it is better to mount it. Its capacity only needs to be approximately equal to your physical memory. If it exceeds twice the capacity of your physical memory, it is absolutely a waste.
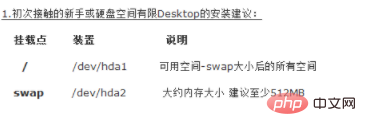
3. For novices who are new to Linux or whose computer hard disk space is relatively small, it is recommended to partition the
partition as shown below:
4. Set the directory where the partition is mounted.
/home --- This is your home directory. Usually the files you create are stored here. You'd better assign a partition to it.
/boot ---If your hard disk does not support LBA mode, you'd better mount it. If so, it should be safer to mount it on the first partition of the hard disk. Generally speaking, the size of the mounted partition is only 100M.
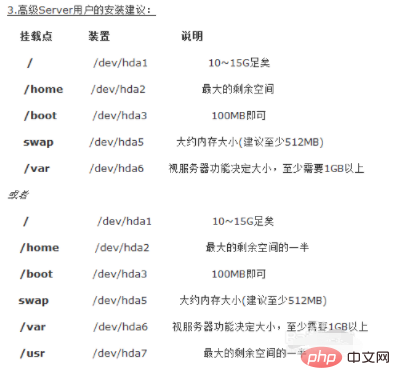
5. Installation suggestions for Linux advanced users:
Add the above mounted directory:

6 , set the directory where the partition is mounted
/var ----If you want to do some server applications, you can consider allocating a larger partition to it.
Seven, installation suggestions for Linux advanced server users:
You can add the above mounted directory in the previous step:
The above is the detailed content of How to partition a Linux disk. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1381
1381
 52
52
 How do I use regular expressions (regex) in Linux for pattern matching?
Mar 17, 2025 pm 05:25 PM
How do I use regular expressions (regex) in Linux for pattern matching?
Mar 17, 2025 pm 05:25 PM
The article explains how to use regular expressions (regex) in Linux for pattern matching, file searching, and text manipulation, detailing syntax, commands, and tools like grep, sed, and awk.
 How do I monitor system performance in Linux using tools like top, htop, and vmstat?
Mar 17, 2025 pm 05:28 PM
How do I monitor system performance in Linux using tools like top, htop, and vmstat?
Mar 17, 2025 pm 05:28 PM
The article discusses using top, htop, and vmstat for monitoring Linux system performance, detailing their unique features and customization options for effective system management.
 How do I implement two-factor authentication (2FA) for SSH in Linux?
Mar 17, 2025 pm 05:31 PM
How do I implement two-factor authentication (2FA) for SSH in Linux?
Mar 17, 2025 pm 05:31 PM
The article provides a guide on setting up two-factor authentication (2FA) for SSH on Linux using Google Authenticator, detailing installation, configuration, and troubleshooting steps. It highlights the security benefits of 2FA, such as enhanced sec
 How do I manage software packages in Linux using package managers (apt, yum, dnf)?
Mar 17, 2025 pm 05:26 PM
How do I manage software packages in Linux using package managers (apt, yum, dnf)?
Mar 17, 2025 pm 05:26 PM
Article discusses managing software packages in Linux using apt, yum, and dnf, covering installation, updates, and removals. It compares their functionalities and suitability for different distributions.
 How do I use sudo to grant elevated privileges to users in Linux?
Mar 17, 2025 pm 05:32 PM
How do I use sudo to grant elevated privileges to users in Linux?
Mar 17, 2025 pm 05:32 PM
The article explains how to manage sudo privileges in Linux, including granting, revoking, and best practices for security. Key focus is on editing /etc/sudoers safely and limiting access.Character count: 159
 Key Linux Operations: A Beginner's Guide
Apr 09, 2025 pm 04:09 PM
Key Linux Operations: A Beginner's Guide
Apr 09, 2025 pm 04:09 PM
Linux beginners should master basic operations such as file management, user management and network configuration. 1) File management: Use mkdir, touch, ls, rm, mv, and CP commands. 2) User management: Use useradd, passwd, userdel, and usermod commands. 3) Network configuration: Use ifconfig, echo, and ufw commands. These operations are the basis of Linux system management, and mastering them can effectively manage the system.
 How to interpret the output results of Debian Sniffer
Apr 12, 2025 pm 11:00 PM
How to interpret the output results of Debian Sniffer
Apr 12, 2025 pm 11:00 PM
DebianSniffer is a network sniffer tool used to capture and analyze network packet timestamps: displays the time for packet capture, usually in seconds. Source IP address (SourceIP): The network address of the device that sent the packet. Destination IP address (DestinationIP): The network address of the device receiving the data packet. SourcePort: The port number used by the device sending the packet. Destinatio
 How to check Debian OpenSSL configuration
Apr 12, 2025 pm 11:57 PM
How to check Debian OpenSSL configuration
Apr 12, 2025 pm 11:57 PM
This article introduces several methods to check the OpenSSL configuration of the Debian system to help you quickly grasp the security status of the system. 1. Confirm the OpenSSL version First, verify whether OpenSSL has been installed and version information. Enter the following command in the terminal: If opensslversion is not installed, the system will prompt an error. 2. View the configuration file. The main configuration file of OpenSSL is usually located in /etc/ssl/openssl.cnf. You can use a text editor (such as nano) to view: sudonano/etc/ssl/openssl.cnf This file contains important configuration information such as key, certificate path, and encryption algorithm. 3. Utilize OPE




