What is the main working principle of a computer?
The main working principle of the computer is to store programs and program control. The instruction sequence and raw data that control how the computer operates must be transferred to the computer memory through the input device in advance; each instruction clearly stipulates the computer Which address to fetch the data from, what operation to perform, and then what address to send to, etc.
#The operating environment of this article: Windows 7 system, Dell G3 computer.
The main working principle of a computer is stored programs and program control.
The basic principles of computers are mainly divided into stored programs and program control. The sequence of instructions (called programs) and raw data that control how the computer operates must be transferred to the computer memory through input devices in advance. Each instruction clearly stipulates which address the computer will fetch from, what operation it will perform, and then what address it will send to.
When the computer is running, it first retrieves the first instruction from the memory, decodes it through the controller, and retrieves the data from the memory according to the instructions' requirements to perform specified calculations and logical operations, and then Send the result to the memory according to the address. Next, take out the second instruction and complete the specified operation under the command of the controller. Continue accordingly. Until a stop command is encountered. Programs are accessed in the same way as data. According to the order of programming, instructions are taken out step by step and automatically complete the operations specified by the instructions. This is the most basic working principle of the computer. This principle was originally proposed by the American Hungarian mathematician von Neumann. It was proposed in 1945, so it is called the von Neumann principle. The working principle of the von Neumann architecture computer can be summarized in eight words: stored program, program control.
The above is the detailed content of What is the main working principle of a computer?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
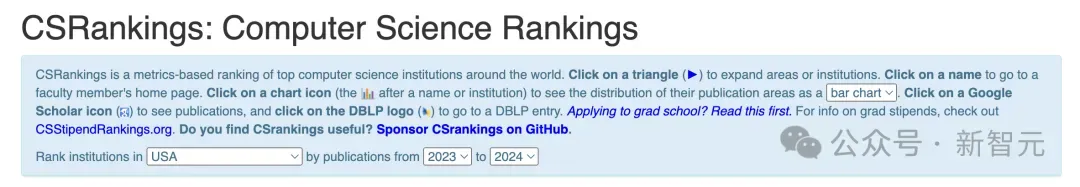 2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
The 2024CSRankings National Computer Science Major Rankings have just been released! This year, in the ranking of the best CS universities in the United States, Carnegie Mellon University (CMU) ranks among the best in the country and in the field of CS, while the University of Illinois at Urbana-Champaign (UIUC) has been ranked second for six consecutive years. Georgia Tech ranked third. Then, Stanford University, University of California at San Diego, University of Michigan, and University of Washington tied for fourth place in the world. It is worth noting that MIT's ranking fell and fell out of the top five. CSRankings is a global university ranking project in the field of computer science initiated by Professor Emery Berger of the School of Computer and Information Sciences at the University of Massachusetts Amherst. The ranking is based on objective
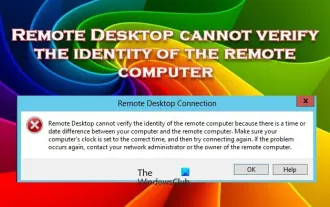 Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Windows Remote Desktop Service allows users to access computers remotely, which is very convenient for people who need to work remotely. However, problems can be encountered when users cannot connect to the remote computer or when Remote Desktop cannot authenticate the computer's identity. This may be caused by network connection issues or certificate verification failure. In this case, the user may need to check the network connection, ensure that the remote computer is online, and try to reconnect. Also, ensuring that the remote computer's authentication options are configured correctly is key to resolving the issue. Such problems with Windows Remote Desktop Services can usually be resolved by carefully checking and adjusting settings. Remote Desktop cannot verify the identity of the remote computer due to a time or date difference. Please make sure your calculations
 What is SOL coin? How does SOL coin work?
Mar 16, 2024 am 10:37 AM
What is SOL coin? How does SOL coin work?
Mar 16, 2024 am 10:37 AM
Solana Blockchain and SOL Token Solana is a blockchain platform focused on providing high performance, security and scalability for decentralized applications (dApps). As the native asset of the Solana blockchain, SOL tokens are mainly used to pay transaction fees, pledge and participate in governance decisions. Solana’s unique features are its fast transaction confirmation times and high throughput, making it a favored choice among developers and users. Through SOL tokens, users can participate in various activities of the Solana ecosystem and jointly promote the development and progress of the platform. How Solana works Solana uses an innovative consensus mechanism called Proof of History (PoH) that is capable of efficiently processing thousands of transactions.
 What is the architecture and working principle of Spring Data JPA?
Apr 17, 2024 pm 02:48 PM
What is the architecture and working principle of Spring Data JPA?
Apr 17, 2024 pm 02:48 PM
SpringDataJPA is based on the JPA architecture and interacts with the database through mapping, ORM and transaction management. Its repository provides CRUD operations, and derived queries simplify database access. Additionally, it uses lazy loading to only retrieve data when necessary, thus improving performance.
 What is Polygon coin? How does Polygon coin work?
Mar 16, 2024 am 09:22 AM
What is Polygon coin? How does Polygon coin work?
Mar 16, 2024 am 09:22 AM
Polygon: A multifunctional blockchain that builds the Ethereum ecosystem Polygon is a multifunctional blockchain platform built on Ethereum, formerly known as MaticNetwork. Its goal is to solve the scalability, high fees, and complexity issues in the Ethereum network. Polygon provides developers and users with a faster, cheaper, and simpler blockchain experience by providing scalability solutions. Here’s how Polygon works: Sidechain Network: Polygon creates a network of multiple sidechains. These sidechains run in parallel with the main Ethereum chain and can handle large volumes of transactions, thereby increasing overall network throughput. Plasma framework: Polygon utilizes the Plasma framework, which
 What is VET coin? How does VET coin work?
Mar 16, 2024 am 11:40 AM
What is VET coin? How does VET coin work?
Mar 16, 2024 am 11:40 AM
VET Coin: Blockchain-based IoT ecosystem VeChainThor (VET) is a platform based on blockchain technology that aims to enhance the Internet of Things (IoT) field by ensuring the credibility of data and enabling safe transfer of value. supply chain management and business processes. VET coin is the native token of the VeChainThor blockchain and has the following functions: Pay transaction fees: VET coins are used to pay transaction fees on the VeChainThor network, including data storage, smart contract execution and identity verification. Governance: VET token holders can participate in the governance of VeChainThor, including voting on platform upgrades and proposals. Incentives: VET coins are used to incentivize validators in the network to ensure the
 What is SHIB coin? How does SHIB coin work?
Mar 17, 2024 am 08:49 AM
What is SHIB coin? How does SHIB coin work?
Mar 17, 2024 am 08:49 AM
ShibaInu Coin: Dog-Inspired Cryptocurrency ShibaInu Coin (SHIB) is a decentralized cryptocurrency inspired by the iconic Shiba Inu emoji. The cryptocurrency was launched in August 2020 and aims to be an alternative to Dogecoin on the Ethereum network. Working Principle SHIB coin is a digital currency built on the Ethereum blockchain and complies with the ERC-20 token standard. It utilizes a decentralized consensus mechanism, Proof of Stake (PoS), which allows holders to stake their SHIB tokens to verify transactions and earn rewards for doing so. Key Features Huge supply: The initial supply of SHIB coins is 1,000 trillion coins, making it one of the largest cryptocurrencies in circulation. Low price: S
 What is Algorand coin? How does Algorand coin work?
Mar 17, 2024 am 08:30 AM
What is Algorand coin? How does Algorand coin work?
Mar 17, 2024 am 08:30 AM
Algorand: A blockchain platform based on pure Byzantine consensus protocol Algorand is a blockchain platform built on pure Byzantine consensus protocol and aims to provide efficient, secure and scalable blockchain solutions. The platform was founded in 2017 by MIT professor Silvio Micali. Working Principle The core of Algorand lies in its unique pure Byzantine consensus protocol, the Algorand consensus. This protocol allows nodes to achieve consensus in a trustless environment, even if there are malicious nodes in the network. Algorand consensus achieves this goal through a series of steps. Key generation: Each node generates a pair of public and private keys. Proposal phase: A randomly selected node proposes a new zone





