Detailed analysis of the data structure and data operations of Redis

Recommended (free): redis
The speed of Redis to complete data operations can reach the microsecond level, Redis can There are two main reasons for such outstanding performance:
- Redis is an in-memory database, all operations are completed in memory, and the memory access speed itself is very fast;
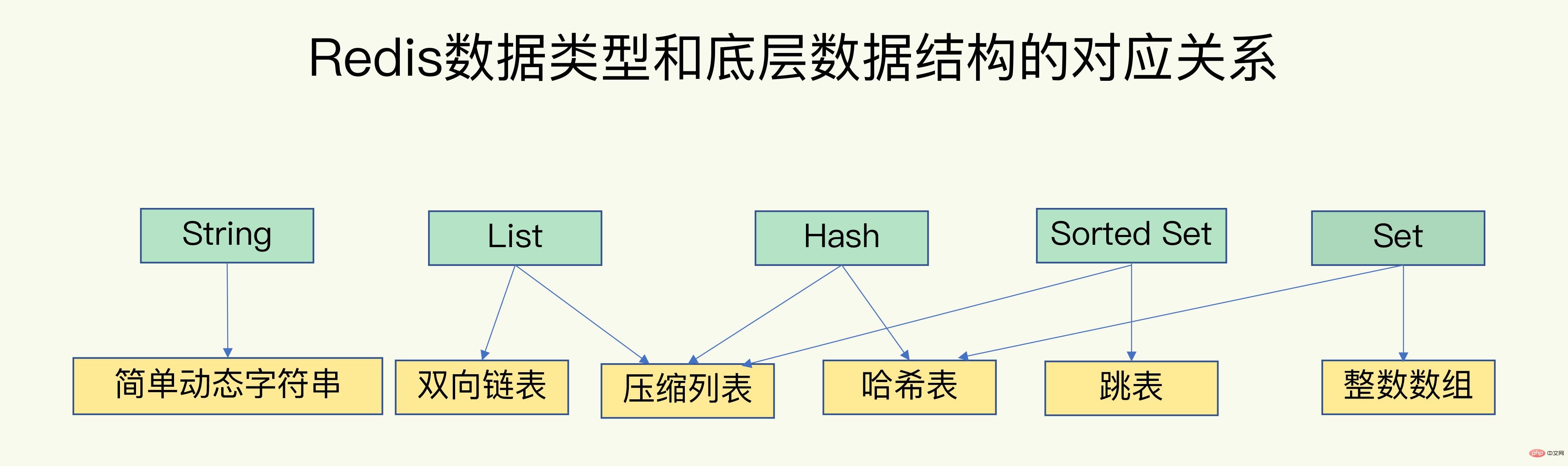
- Redis Have efficient data types and data structures.

In order to achieve fast access from key to value, Redis uses a hash table to store key-value pairs. The entry in the hash bucket saves pointers to the actual key and value, even if the value is A collection can also be found through the value pointer. 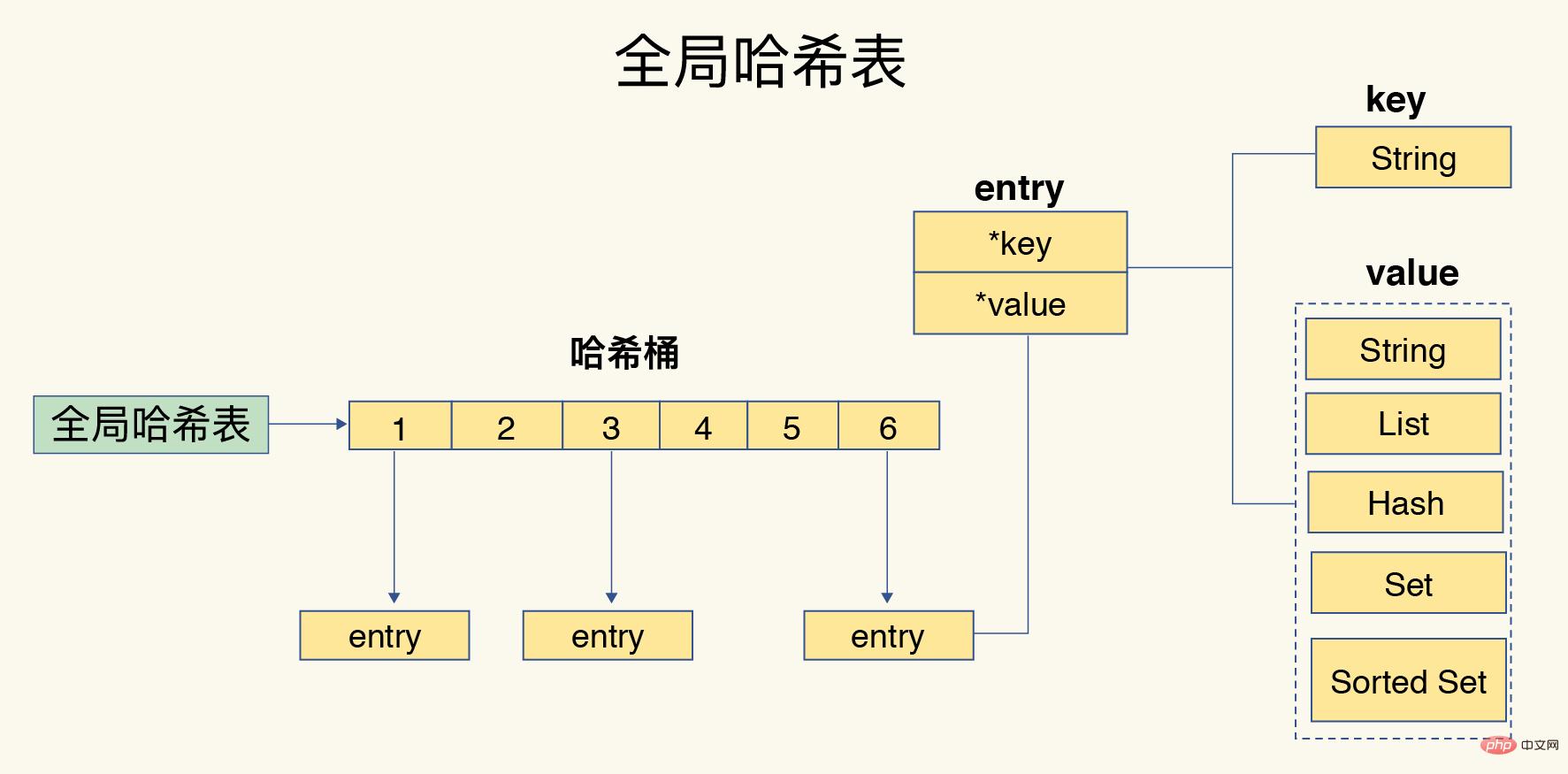
When there is more and more data in the hash table, hash conflicts will occur, that is, the hash values of multiple keys may correspond to the same hash bucket. Redis uses chained hashing to resolve hash conflicts, which means that multiple elements in the same hash bucket are stored in a linked list, and the elements are linked by pointers in turn. 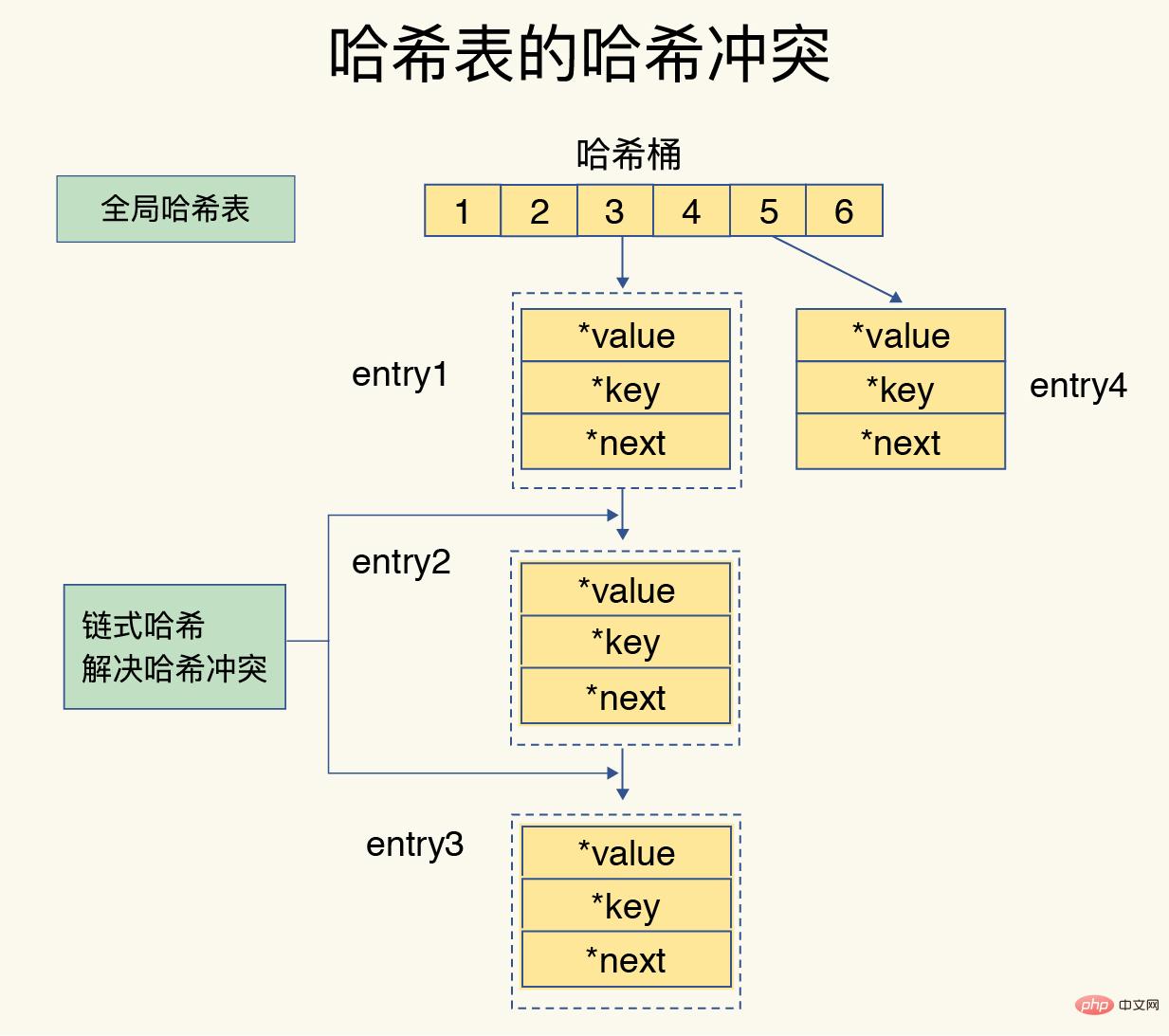
If there are more and more hash conflicts, the hash conflict chain will be too long, which will lead to long time and low efficiency in finding elements. In order to solve this problem, Redis will perform a rehash operation on the hash table to store multiple entry elements in a dispersed manner, reducing the number of elements in a single hash bucket, thereby reducing conflicts in a single bucket.
Redis uses two global hash tables by default for efficient rehash. Hash table 1 is used by default at the beginning, and hash table 2 does not allocate space. When the data continues to increase, redis performs rehash through the following steps:
- Allocate more space to hash table 2
- Copy the data in hash table 1 to hash table 2
- Release the hash table 1 space is reserved for the next rehash expansion
However, if a large amount of data is copied at one time in step 2, it may cause the Redis thread to be blocked and unable to serve other requests, so Redis adopts a gradual approach. Rehash means that every time a request is processed, all entries at this index position are copied. 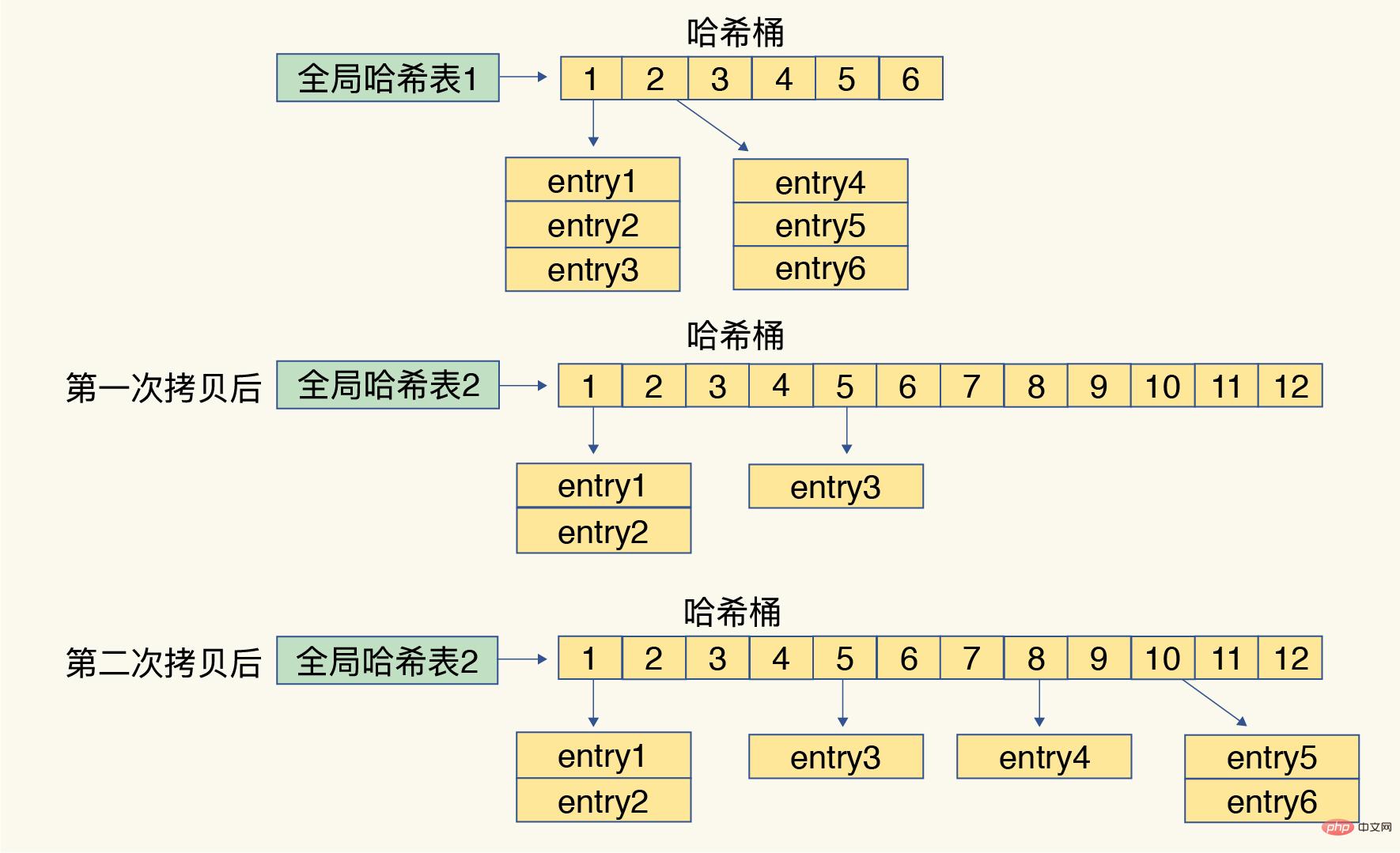
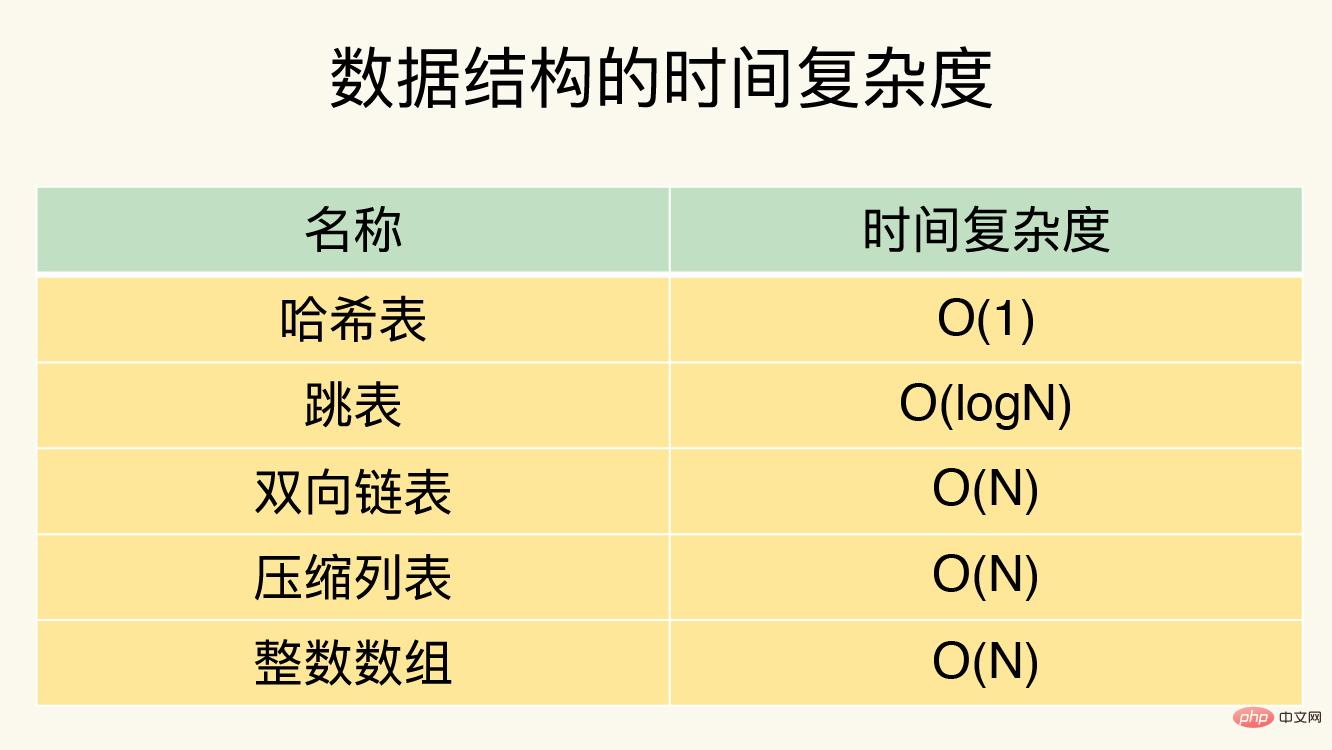
For String type value, you can directly perform CRUD operations after finding the hash bucket. For sets, after finding the corresponding hash bucket through the global hash table, in the set Then perform CRUD. The operation efficiency of a collection is related to the underlying data structure and operation complexity.
- Single element operation is the basis, and the operation complexity is O(1);
- Hash: HGET, HSET, HDEL;
- Set type SADD, SREM, SRANDMEMBER, etc.
- Range operations are very time-consuming and the operation complexity is O(N).
- Hash:HGETALL;
- Set:SMEMBERS;
- List:LRANGE
- ZSet:ZRANGE
- Statistical operations are usually efficient, with operation complexity O(1).
- There are only a few exceptions, and the operation complexity is O(1).
- List: LPOP, RPOP, LPUSH, RPUSH
The above is the detailed content of Detailed analysis of the data structure and data operations of Redis. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1382
1382
 52
52
 How to build the redis cluster mode
Apr 10, 2025 pm 10:15 PM
How to build the redis cluster mode
Apr 10, 2025 pm 10:15 PM
Redis cluster mode deploys Redis instances to multiple servers through sharding, improving scalability and availability. The construction steps are as follows: Create odd Redis instances with different ports; Create 3 sentinel instances, monitor Redis instances and failover; configure sentinel configuration files, add monitoring Redis instance information and failover settings; configure Redis instance configuration files, enable cluster mode and specify the cluster information file path; create nodes.conf file, containing information of each Redis instance; start the cluster, execute the create command to create a cluster and specify the number of replicas; log in to the cluster to execute the CLUSTER INFO command to verify the cluster status; make
 How to clear redis data
Apr 10, 2025 pm 10:06 PM
How to clear redis data
Apr 10, 2025 pm 10:06 PM
How to clear Redis data: Use the FLUSHALL command to clear all key values. Use the FLUSHDB command to clear the key value of the currently selected database. Use SELECT to switch databases, and then use FLUSHDB to clear multiple databases. Use the DEL command to delete a specific key. Use the redis-cli tool to clear the data.
 How to use the redis command
Apr 10, 2025 pm 08:45 PM
How to use the redis command
Apr 10, 2025 pm 08:45 PM
Using the Redis directive requires the following steps: Open the Redis client. Enter the command (verb key value). Provides the required parameters (varies from instruction to instruction). Press Enter to execute the command. Redis returns a response indicating the result of the operation (usually OK or -ERR).
 How to read redis queue
Apr 10, 2025 pm 10:12 PM
How to read redis queue
Apr 10, 2025 pm 10:12 PM
To read a queue from Redis, you need to get the queue name, read the elements using the LPOP command, and process the empty queue. The specific steps are as follows: Get the queue name: name it with the prefix of "queue:" such as "queue:my-queue". Use the LPOP command: Eject the element from the head of the queue and return its value, such as LPOP queue:my-queue. Processing empty queues: If the queue is empty, LPOP returns nil, and you can check whether the queue exists before reading the element.
 How to use single threaded redis
Apr 10, 2025 pm 07:12 PM
How to use single threaded redis
Apr 10, 2025 pm 07:12 PM
Redis uses a single threaded architecture to provide high performance, simplicity, and consistency. It utilizes I/O multiplexing, event loops, non-blocking I/O, and shared memory to improve concurrency, but with limitations of concurrency limitations, single point of failure, and unsuitable for write-intensive workloads.
 How to use redis lock
Apr 10, 2025 pm 08:39 PM
How to use redis lock
Apr 10, 2025 pm 08:39 PM
Using Redis to lock operations requires obtaining the lock through the SETNX command, and then using the EXPIRE command to set the expiration time. The specific steps are: (1) Use the SETNX command to try to set a key-value pair; (2) Use the EXPIRE command to set the expiration time for the lock; (3) Use the DEL command to delete the lock when the lock is no longer needed.
 How to read the source code of redis
Apr 10, 2025 pm 08:27 PM
How to read the source code of redis
Apr 10, 2025 pm 08:27 PM
The best way to understand Redis source code is to go step by step: get familiar with the basics of Redis. Select a specific module or function as the starting point. Start with the entry point of the module or function and view the code line by line. View the code through the function call chain. Be familiar with the underlying data structures used by Redis. Identify the algorithm used by Redis.
 How to make message middleware for redis
Apr 10, 2025 pm 07:51 PM
How to make message middleware for redis
Apr 10, 2025 pm 07:51 PM
Redis, as a message middleware, supports production-consumption models, can persist messages and ensure reliable delivery. Using Redis as the message middleware enables low latency, reliable and scalable messaging.