Take a look at the 5 data types of redis

1. 5 data types of redis:
string string (can be integer, floating point and string, collectively called elements)
list list (implementation Queue, elements are not unique, first-in-first-out principle)
set set (different elements)
hash hash value (hash key must be unique)
sort set ordered set
Recommended (free): redis tutorial
2. Common commands for string type:
Self-increment: incr
Self-decrement: decr
Add: incrby
Subtract: decrby 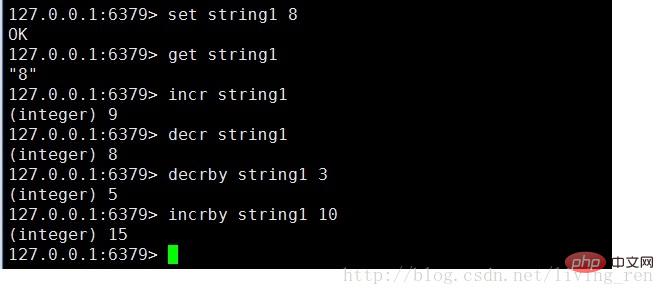
3. Common commands supported by list type:
lpush: push from the left
lpop: pop from the right
rpush: Push from the right
rpop: Pop from the right
llen: Check the length of a list data type 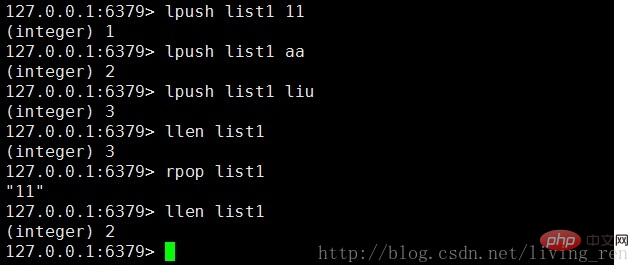
4. Common commands supported by the set type:
sadd: Add data
scard: Check the number of elements existing in the set data
sismember: Determine whether an element exists in the set data
srem: Delete an element in a set data
5. Common commands supported by hash data type:
hset: Add hash data
hget: Get hash data
hmget: Get multiple hash data 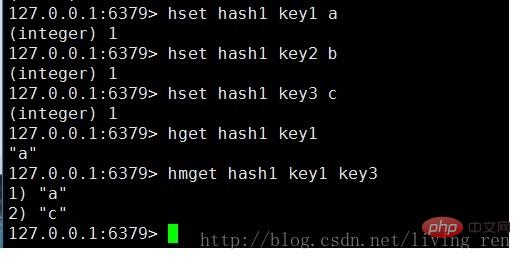
6 , sort set is very similar to hash, and is also a mapping form of storage:
zadd: add
zcard: query
zrange: data sorting 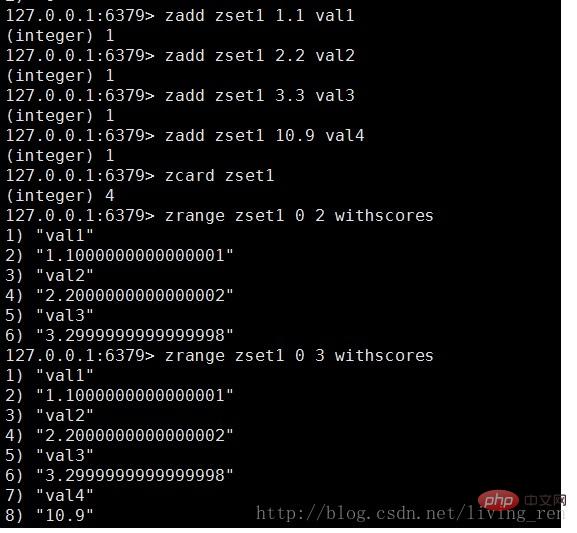
The above is the detailed content of Take a look at the 5 data types of redis. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How do I implement authentication and authorization in Redis?
Mar 17, 2025 pm 06:57 PM
How do I implement authentication and authorization in Redis?
Mar 17, 2025 pm 06:57 PM
The article discusses implementing authentication and authorization in Redis, focusing on enabling authentication, using ACLs, and best practices for securing Redis. It also covers managing user permissions and tools to enhance Redis security.
 How do I choose a shard key in Redis Cluster?
Mar 17, 2025 pm 06:55 PM
How do I choose a shard key in Redis Cluster?
Mar 17, 2025 pm 06:55 PM
The article discusses choosing shard keys in Redis Cluster, emphasizing their impact on performance, scalability, and data distribution. Key issues include ensuring even data distribution, aligning with access patterns, and avoiding common mistakes l
 How do I implement cache invalidation strategies in Redis?
Mar 17, 2025 pm 06:46 PM
How do I implement cache invalidation strategies in Redis?
Mar 17, 2025 pm 06:46 PM
The article discusses strategies for implementing and managing cache invalidation in Redis, including time-based expiration, event-driven methods, and versioning. It also covers best practices for cache expiration and tools for monitoring and automat
 How do I use Redis for job queues and background processing?
Mar 17, 2025 pm 06:51 PM
How do I use Redis for job queues and background processing?
Mar 17, 2025 pm 06:51 PM
The article discusses using Redis for job queues and background processing, detailing setup, job definition, and execution. It covers best practices like atomic operations and job prioritization, and explains how Redis enhances processing efficiency.
 How do I monitor the performance of a Redis Cluster?
Mar 17, 2025 pm 06:56 PM
How do I monitor the performance of a Redis Cluster?
Mar 17, 2025 pm 06:56 PM
Article discusses monitoring Redis Cluster performance and health using tools like Redis CLI, Redis Insight, and third-party solutions like Datadog and Prometheus.
 How do I use Redis for pub/sub messaging?
Mar 17, 2025 pm 06:48 PM
How do I use Redis for pub/sub messaging?
Mar 17, 2025 pm 06:48 PM
The article explains how to use Redis for pub/sub messaging, covering setup, best practices, ensuring message reliability, and monitoring performance.
 How do I use Redis for session management in web applications?
Mar 17, 2025 pm 06:47 PM
How do I use Redis for session management in web applications?
Mar 17, 2025 pm 06:47 PM
The article discusses using Redis for session management in web applications, detailing setup, benefits like scalability and performance, and security measures.
 How do I secure Redis against common vulnerabilities?
Mar 17, 2025 pm 06:57 PM
How do I secure Redis against common vulnerabilities?
Mar 17, 2025 pm 06:57 PM
Article discusses securing Redis against vulnerabilities, focusing on strong passwords, network binding, command disabling, authentication, encryption, updates, and monitoring.






