What are the two important functions of computer networks?
Two important functions: 1. Data communication is a communication method and communication service that uses data transmission technology to transfer data information between two terminals according to a certain communication protocol; it can realize computer and Data information transfer between computers, computers and terminals, and terminals. 2. Resource sharing, that is, multiple users share the hardware, software and data resources in the computer system, which can improve the utilization of equipment, avoid repeated investment in equipment, and also make full use of existing information resources and reduce the time spent in the software development process. labor and avoid repeated construction of large databases.
The operating environment of this tutorial: Windows 7 system, Dell G3 computer.
Computer network refers to the connection of multiple computers and their external devices with independent functions in different geographical locations through communication lines. Under the management and coordination of network operating systems, network management software and network communication protocols , a computer system that realizes resource sharing and information transfer.
Computer networks are mainly interconnected by some general-purpose, programmable hardware that is not designed to achieve a specific purpose (for example, transmitting data or video signals). These programmable hardware can be used to transfer many different types of data and support a wide and growing number of applications.
Two important functions of computer networks
1. Data communication
Data communication is One of the most important functions of computer networks. Data communication is a communication method and communication service that uses data transmission technology to transfer data information between two terminals according to a certain communication protocol. It can realize the transmission of data information between computers, computers and terminals, and terminals. It is the third largest communication service after telegraph and telephone services. The information transmitted in data communication is expressed in the form of binary data. Another characteristic of data communication is that it is always connected with telematics. It is a generalized information processing including scientific computing, process control, information retrieval, etc.
2. Resource sharing
Resource sharing is one of the main purposes for people to establish computer networks.
In a network, multiple computers or multiple users on the same computer, usually the resources required by multiple users at the same time always exceed the number of actual physical resources of the system, but logical (or virtual) resource allocation is used , realizing resource sharing can better handle this contradiction, thereby improving the efficiency of computer use.
Computer resources include hardware resources, software resources and data resources. The sharing of hardware resources can improve the utilization of equipment and avoid repeated investment in equipment, such as using computer networks to establish network printers; the sharing of software resources and data resources can make full use of existing information resources, reduce labor in the software development process, and avoid Repeated construction of large databases.
Two basic principles of resource sharing:
-
1. The law of large numbers:
The law of large numbers says: If the number of users is very Large, and their resource usage requirements are sudden and random. When all users are considered as a whole, the user's overall resource usage requirements become quite smooth, stable, and predictable.
-
2. Economies of scale
Economies of scale say: when the resources and the number of users in a system increase in proportion at the same time, within a certain range, The larger the size of the system, the more economical the system is.
For more relevant knowledge, please visit the FAQ column!
The above is the detailed content of What are the two important functions of computer networks?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1385
1385
 52
52
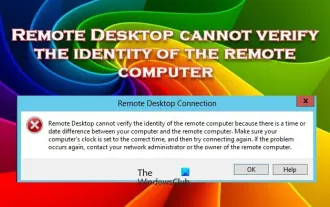 Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Windows Remote Desktop Service allows users to access computers remotely, which is very convenient for people who need to work remotely. However, problems can be encountered when users cannot connect to the remote computer or when Remote Desktop cannot authenticate the computer's identity. This may be caused by network connection issues or certificate verification failure. In this case, the user may need to check the network connection, ensure that the remote computer is online, and try to reconnect. Also, ensuring that the remote computer's authentication options are configured correctly is key to resolving the issue. Such problems with Windows Remote Desktop Services can usually be resolved by carefully checking and adjusting settings. Remote Desktop cannot verify the identity of the remote computer due to a time or date difference. Please make sure your calculations
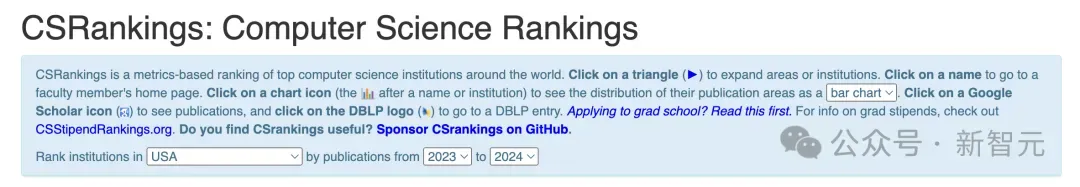 2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
The 2024CSRankings National Computer Science Major Rankings have just been released! This year, in the ranking of the best CS universities in the United States, Carnegie Mellon University (CMU) ranks among the best in the country and in the field of CS, while the University of Illinois at Urbana-Champaign (UIUC) has been ranked second for six consecutive years. Georgia Tech ranked third. Then, Stanford University, University of California at San Diego, University of Michigan, and University of Washington tied for fourth place in the world. It is worth noting that MIT's ranking fell and fell out of the top five. CSRankings is a global university ranking project in the field of computer science initiated by Professor Emery Berger of the School of Computer and Information Sciences at the University of Massachusetts Amherst. The ranking is based on objective
 What is e in computer
Aug 31, 2023 am 09:36 AM
What is e in computer
Aug 31, 2023 am 09:36 AM
The "e" of computer is the scientific notation symbol. The letter "e" is used as the exponent separator in scientific notation, which means "multiplied to the power of 10". In scientific notation, a number is usually written as M × 10^E, where M is a number between 1 and 10 and E represents the exponent.
 Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
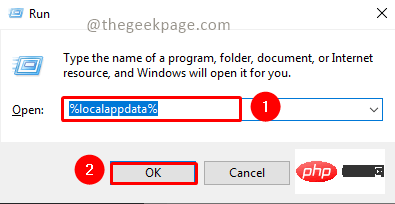
<p>MSTeams is the trusted platform to communicate, chat or call with teammates and colleagues. Error code 80090016 on MSTeams and the message <strong>Your computer's Trusted Platform Module has failed</strong> may cause difficulty logging in. The app will not allow you to log in until the error code is resolved. If you encounter such messages while opening MS Teams or any other Microsoft application, then this article can guide you to resolve the issue. </p><h2&
 What does computer cu mean?
Aug 15, 2023 am 09:58 AM
What does computer cu mean?
Aug 15, 2023 am 09:58 AM
The meaning of cu in a computer depends on the context: 1. Control Unit, in the central processor of a computer, CU is the component responsible for coordinating and controlling the entire computing process; 2. Compute Unit, in a graphics processor or other accelerated processor, CU is the basic unit for processing parallel computing tasks.
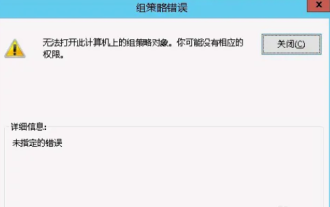 Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Occasionally, the operating system may malfunction when using a computer. The problem I encountered today was that when accessing gpedit.msc, the system prompted that the Group Policy object could not be opened because the correct permissions may be lacking. The Group Policy object on this computer could not be opened. Solution: 1. When accessing gpedit.msc, the system prompts that the Group Policy object on this computer cannot be opened because of lack of permissions. Details: The system cannot locate the path specified. 2. After the user clicks the close button, the following error window pops up. 3. Check the log records immediately and combine the recorded information to find that the problem lies in the C:\Windows\System32\GroupPolicy\Machine\registry.pol file
 What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
Solution to the problem that steam cannot connect to the remote computer: 1. In the game platform, click the "steam" option in the upper left corner; 2. Open the menu and select the "Settings" option; 3. Select the "Remote Play" option; 4. Check Activate the "Remote Play" function and click the "OK" button.
 Python script to log out of computer
Sep 05, 2023 am 08:37 AM
Python script to log out of computer
Sep 05, 2023 am 08:37 AM
In today's digital age, automation plays a vital role in streamlining and simplifying various tasks. One of these tasks is to log off the computer, which is usually done manually by selecting the logout option from the operating system's user interface. But what if we could automate this process using a Python script? In this blog post, we'll explore how to create a Python script that can log off your computer with just a few lines of code. In this article, we'll walk through the step-by-step process of creating a Python script for logging out of your computer. We'll cover the necessary prerequisites, discuss different ways to log out programmatically, and provide a step-by-step guide to writing the script. Additionally, we will address platform-specific considerations and highlight best practices



