What are the transmission routes and harms of computer viruses?
Methods of transmission: 1. Through floppy disks, file-type diseases can be spread through floppy disks; 2. Through optical discs, because optical discs have large capacity and can store massive executable files; 3. Through network transmission, this method spreads It is extremely fast and can be transmitted to all machines on the network in a very short time. Hazards: 1. Attack the hard disk's main boot sector, Boot sector, FAT table, and document directory, causing information on the disk to be lost; 2. Delete executable documents or data files on the floppy disk, hard disk, or network, causing the document to be lost; 3. , occupy disk space; 4. Modify or destroy the data in the document, causing the content to change.
The operating environment of this tutorial: Windows 7 system, Dell G3 computer.
Computer virus (Computer Virus) refers to a set of computer instructions or program codes inserted by the programmer into a computer program that destroy computer functions or destroy data, affect the normal use of the computer, and are capable of self-replication.
Computer viruses are artificially created, destructive, contagious and latent programs that damage computer information or systems. It does not exist independently, but is hidden in other executable programs. When a computer is infected with a virus, it may affect the running speed of the machine at first, or crash and damage the system at worst. Therefore, the virus brings great losses to the user. Under normal circumstances, we call this destructive program a computer virus.
The main transmission route of computer viruses
1. Floppy disk: through the use of floppy disks infected by the outside world.
As the most commonly used exchange medium, floppy disks played a huge role in the spread of viruses in the early days of computer application. Because computer applications were relatively simple at that time, executable files and data file systems were small. , many executable files are installed through floppy disks copying each other, so that viruses can spread file-type viruses through floppy disks: In addition, when the floppy disk is cataloged or the machine is booted, the boot area virus will infect each other in the floppy disk and hard disk area. Therefore, floppy disks have also become the main parasitic "breeding ground" for computer viruses.
2. CD
Because the CD has a large capacity and stores a large number of executable files, a large number of viruses may hide in the CD. For read-only CDs, Writing operations cannot be performed, so the virus on the disc cannot be removed. In the process of producing illegally pirated software for profit, it is impossible to take special responsibility for virus protection, and there will never be truly reliable and feasible technical guarantees to avoid the introduction, infection, epidemic and spread of viruses. Currently, the proliferation of pirated CDs has brought great convenience to the spread of viruses.
3. Hard disk
Because the hard disk with the virus is used or repaired locally or moved to other places, the clean floppy disk will be infected and then spread.
4. U disk
U disk has the characteristics of small size, portability, large storage capacity, and low price, but at the same time, viruses can also be transmitted to the computer through the U disk.
5. BBS
Electronic bulletin board BBS is very popular among users because it is easy to get on the site and requires low investment. BBS is a communication site voluntarily organized by computer enthusiasts. Users can exchange files including free software, games, and self-written programs on BBS. Since BBS sites generally do not have strict security management and no restrictions, this provides some virus program writers with a place to spread viruses. BBS stations in various cities are transmitted through central stations, with a wide spread area. With the popularity of BBS in China, new media have been added to the spread of viruses.
6. Network
The great progress of modern communication technology has made the space distance no longer far away, and data, files and emails can be conveniently
Transmission is carried out between various network workstations through cables, optical fibers or telephone lines. The distance between workstations can be as short as computers placed side by side, or as long as tens of thousands of kilometers. As the saying goes, "we are as close as we are to each other at the end of the world", but it is also a computer The spread of the virus provides a new "highway". Computer viruses can attach themselves to normal files and spread when you get an infected program from the other side of the network and run it on your computer without any protection. This method of virus infection is very common in countries where computer network connections are widespread. It is no longer a big deal for domestic computers to be infected by an "imported" virus. While our information is internationalizing, our viruses are also internationalizing. A large number of foreign viruses have been introduced into the country along with the Internet.
With the popularity of the Internet, new ways have been added to the spread of viruses, and they will become the first way of spread. The pioneering development of the Internet has made viruses potentially catastrophic, spreading more rapidly and making anti-virus tasks more difficult. The Internet presents two different security threats. One threat comes from file downloads, which may contain viruses when they are browsed or downloaded via FTP. Another threat comes from email. Most Internet mail systems provide the function of transmitting emails with formatted documents between networks. Therefore, virus-infected documents or files may flood into the corporate network through gateways and mail servers. The ease and openness of using the Internet make this threat increasingly serious.
Currently, the latest trend of viruses on the Internet is:
1) Anonymous personal web pages created by criminals or bad guys directly provide the ability to download a large number of live virus samples. Convenient way.
2) Virus sample providing institutions for academic research can also become tools for people with ulterior motives.
3) Academic electronic papers, journals, magazines and related online academic exchange activities that are dedicated to virus production research and discussion, such as the Virus Production Association, are made possible by anonymous login on the Internet Annual meetings, etc., may become targets and targets for any new virus creators at home and abroad who want to become new virus makers to learn, learn from, steal, and plagiarize.
4) There are a large number of virus creation tools, wizards, programs, etc. scattered on the website, making it possible for people without programming experience and foundation to create new viruses.
5) New technologies and new viruses make almost everyone unintentionally become the carrier or spreader of the virus without knowing it.
Main hazards of computer viruses
1. Attack hard disk master boot sector, Boot sector, FAT table , document directory, causing the information on the disk to be lost.
2. Delete executable documents or data documents on the floppy disk, hard disk or network, causing the documents to be lost.
3. Occupies disk space.
4. Modify or destroy the data in the document to change the content.
5. Seize system resources to reduce memory.
6. It takes up CPU running time and reduces running efficiency.
7. Format the entire disk or sector.
8. Destroy the BIOS content on the computer motherboard and make the computer unable to work.
9. Destroy the normal display of the screen and interfere with the user's operation.
10. Destroy the keyboard input program and cause errors in the user's normal input.
For more related knowledge, please visit the FAQ column!
The above is the detailed content of What are the transmission routes and harms of computer viruses?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1387
1387
 52
52
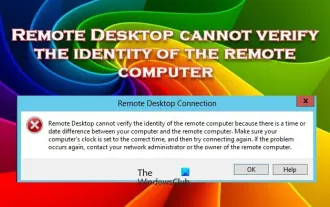 Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Remote Desktop cannot authenticate the remote computer's identity
Feb 29, 2024 pm 12:30 PM
Windows Remote Desktop Service allows users to access computers remotely, which is very convenient for people who need to work remotely. However, problems can be encountered when users cannot connect to the remote computer or when Remote Desktop cannot authenticate the computer's identity. This may be caused by network connection issues or certificate verification failure. In this case, the user may need to check the network connection, ensure that the remote computer is online, and try to reconnect. Also, ensuring that the remote computer's authentication options are configured correctly is key to resolving the issue. Such problems with Windows Remote Desktop Services can usually be resolved by carefully checking and adjusting settings. Remote Desktop cannot verify the identity of the remote computer due to a time or date difference. Please make sure your calculations
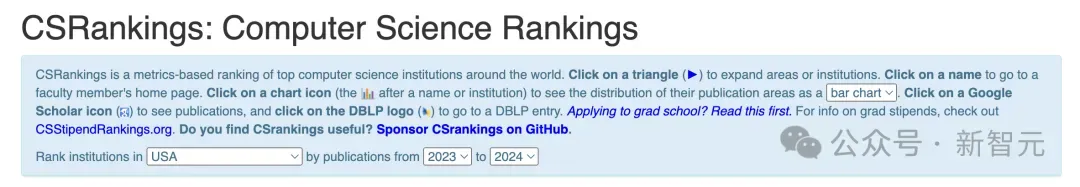 2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
2024 CSRankings National Computer Science Rankings Released! CMU dominates the list, MIT falls out of the top 5
Mar 25, 2024 pm 06:01 PM
The 2024CSRankings National Computer Science Major Rankings have just been released! This year, in the ranking of the best CS universities in the United States, Carnegie Mellon University (CMU) ranks among the best in the country and in the field of CS, while the University of Illinois at Urbana-Champaign (UIUC) has been ranked second for six consecutive years. Georgia Tech ranked third. Then, Stanford University, University of California at San Diego, University of Michigan, and University of Washington tied for fourth place in the world. It is worth noting that MIT's ranking fell and fell out of the top five. CSRankings is a global university ranking project in the field of computer science initiated by Professor Emery Berger of the School of Computer and Information Sciences at the University of Massachusetts Amherst. The ranking is based on objective
 What is e in computer
Aug 31, 2023 am 09:36 AM
What is e in computer
Aug 31, 2023 am 09:36 AM
The "e" of computer is the scientific notation symbol. The letter "e" is used as the exponent separator in scientific notation, which means "multiplied to the power of 10". In scientific notation, a number is usually written as M × 10^E, where M is a number between 1 and 10 and E represents the exponent.
 Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
Fix: Microsoft Teams error code 80090016 Your computer's Trusted Platform module has failed
Apr 19, 2023 pm 09:28 PM
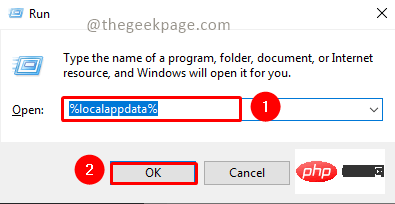
<p>MSTeams is the trusted platform to communicate, chat or call with teammates and colleagues. Error code 80090016 on MSTeams and the message <strong>Your computer's Trusted Platform Module has failed</strong> may cause difficulty logging in. The app will not allow you to log in until the error code is resolved. If you encounter such messages while opening MS Teams or any other Microsoft application, then this article can guide you to resolve the issue. </p><h2&
 What does computer cu mean?
Aug 15, 2023 am 09:58 AM
What does computer cu mean?
Aug 15, 2023 am 09:58 AM
The meaning of cu in a computer depends on the context: 1. Control Unit, in the central processor of a computer, CU is the component responsible for coordinating and controlling the entire computing process; 2. Compute Unit, in a graphics processor or other accelerated processor, CU is the basic unit for processing parallel computing tasks.
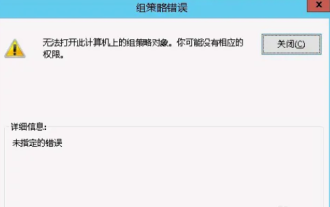 Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Unable to open the Group Policy object on this computer
Feb 07, 2024 pm 02:00 PM
Occasionally, the operating system may malfunction when using a computer. The problem I encountered today was that when accessing gpedit.msc, the system prompted that the Group Policy object could not be opened because the correct permissions may be lacking. The Group Policy object on this computer could not be opened. Solution: 1. When accessing gpedit.msc, the system prompts that the Group Policy object on this computer cannot be opened because of lack of permissions. Details: The system cannot locate the path specified. 2. After the user clicks the close button, the following error window pops up. 3. Check the log records immediately and combine the recorded information to find that the problem lies in the C:\Windows\System32\GroupPolicy\Machine\registry.pol file
 How to completely remove viruses from mobile phones Recommended methods to deal with viruses in mobile phones
Feb 29, 2024 am 10:52 AM
How to completely remove viruses from mobile phones Recommended methods to deal with viruses in mobile phones
Feb 29, 2024 am 10:52 AM
After a mobile phone is infected with a certain Trojan virus, it cannot be detected and killed by anti-virus software. This principle is just like a computer infected with a stubborn virus. The virus can only be completely removed by formatting the C drive and reinstalling the system. , then I will explain how to completely clean the virus after the mobile phone is infected with a stubborn virus. Method 1: Open the phone and click "Settings" - "Other Settings" - "Restore Phone" to restore the phone to factory settings. Note: Before restoring factory settings, you must back up important data in the phone. The factory settings are equivalent to those of the computer. "It's the same as formatting and reinstalling the system". After the recovery, the data in the phone will be cleared. Method 2 (1) First turn off the phone, then press and hold the "power button" + "volume + button or volume - button" on the phone at the same time.
 What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
What should I do if steam cannot connect to the remote computer?
Mar 01, 2023 pm 02:20 PM
Solution to the problem that steam cannot connect to the remote computer: 1. In the game platform, click the "steam" option in the upper left corner; 2. Open the menu and select the "Settings" option; 3. Select the "Remote Play" option; 4. Check Activate the "Remote Play" function and click the "OK" button.



