Is Tinder a rogue antivirus software?
Tinder is not a rogue anti-virus software. Tinder is a security software that integrates anti-virus, prevention, management and control. It can help security engineers quickly and accurately analyze the malicious behavior of viruses, Trojans, and rogue software. It can also help with virus database upgrades and defense program updates for security software. It can be used in large-scale applications. While greatly improving the work efficiency of safety engineers, it also effectively reduces misjudgments and manslaughter of safety products.
The operating environment of this tutorial: Windows 7 system, Tinder Security 5, Dell G3 computer.
Tinder is not a rogue anti-virus software and is completely free to use.
Tinder is a security software that integrates killing, prevention, management and control. It has products for individuals and enterprises. It has a simple interface, rich functions and a good experience. Especially in response to domestic security trends, we independently developed a high-performance anti-virus engine, built by former Rising core R&D members with many years of network security experience.

After the former CTO of Tinder Security Software Department, Rising Liu Gang, resigned in August 2011, he founded the "Tinder Security Laboratory" with several technical backbones, dedicated to the research of core network security technologies. and development. It can help security engineers quickly and accurately analyze the malicious behavior of viruses, Trojans, and rogue software, and provide assistance for virus database upgrades and defense program updates of security software. It can greatly improve the work efficiency of security engineers while effectively reducing Misjudgment and manslaughter of safety products.
Main advantages
-
A new generation of anti-virus engine with independent intellectual property rights: supports dynamic analysis, static analysis and sandbox analysis;
The personal version supports x86 and x64 Windows systems, and the enterprise version supports Linux systems;
Uses "kernel purification" technology to deal with kernel-level rootkits;
Adopts single-step plus multi-step active defense (HIPS) technology;
Access control allows the owner to adjust the computer to more appropriate guests Status of use;
The program is equipped with security tools, including pop-up blocking tools;
-
No rogue behavior;
The software is streamlined and consumes less system resources.

## Product features
Virus detection
One-click scanning and killing of viruses, a purely local anti-virus engine based on "universal unpacking" and "behavioral sandbox", which is not affected by network disconnection environments- The detection results can be explained: the basis for accurately pointing out that the sample is a virus
- The detection results can be controlled: the false positive rate is low, and the compatibility with the software is good
Protection Center
18 important protection functions, effective against viruses, Trojans, rogue software, malicious websites, etc.- Real-time file monitoring: scan in time before running the program to intercept viruses.
- U disk protection: Scan the U disk connected to the computer immediately.
- Application hardening: Protect browsers, office software, design software and other programs.
- Software installation interception: monitor and prompt software installation behavior in real time.
- Browser Protection: Protect your commonly used browsers and search engines from tampering.
- Network intrusion interception: Prevent viruses and hackers from entering the computer through system vulnerabilities, and resolve the attack source IP address.
- Brute force attack protection: Prevent hackers from invading the system through weak password brute force
- ......
Access Control
Customize the computer usage permissions, allowing you to fully control your computer from being used by others- Control Internet access time and time period
- Restrict access to specified websites
- Restrict the operation of specified programs
- Manage U disk access permissions
Security tools
Provide practical system and network management gadgets- Pop-up interception: intercept annoying pop-ups
- Vulnerability repair: timely repair high-risk system vulnerabilities
- Startup item management : Manage startup items and optimize startup time
- File shredding: Forcefully delete or completely shred files that users do not need
FAQ column!
The above is the detailed content of Is Tinder a rogue antivirus software?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1653
1653
 14
14
 1413
1413
 52
52
 1304
1304
 25
25
 1251
1251
 29
29
 1224
1224
 24
24
 What software is bonjour and can it be uninstalled?
Feb 20, 2024 am 09:33 AM
What software is bonjour and can it be uninstalled?
Feb 20, 2024 am 09:33 AM
Title: Explore the Bonjour software and how to uninstall it Abstract: This article will introduce the functions, scope of use and how to uninstall the Bonjour software. At the same time, it will also be explained how to use other tools to replace Bonjour to meet the needs of users. Introduction: Bonjour is a common software in the field of computer and network technology. Although this may be unfamiliar to some users, it can be very useful in some specific situations. If you happen to have Bonjour software installed but now want to uninstall it, then
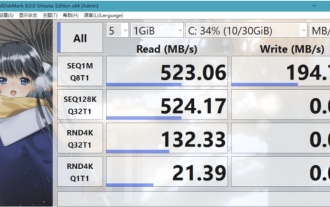 What software is crystaldiskmark? -How to use crystaldiskmark?
Mar 18, 2024 pm 02:58 PM
What software is crystaldiskmark? -How to use crystaldiskmark?
Mar 18, 2024 pm 02:58 PM
CrystalDiskMark is a small HDD benchmark tool for hard drives that quickly measures sequential and random read/write speeds. Next, let the editor introduce CrystalDiskMark to you and how to use crystaldiskmark~ 1. Introduction to CrystalDiskMark CrystalDiskMark is a widely used disk performance testing tool used to evaluate the read and write speed and performance of mechanical hard drives and solid-state drives (SSD). Random I/O performance. It is a free Windows application and provides a user-friendly interface and various test modes to evaluate different aspects of hard drive performance and is widely used in hardware reviews
 What to do if WPS Office cannot open the PPT file - What to do if WPS Office cannot open the PPT file
Mar 04, 2024 am 11:40 AM
What to do if WPS Office cannot open the PPT file - What to do if WPS Office cannot open the PPT file
Mar 04, 2024 am 11:40 AM
Recently, many friends have asked me what to do if WPSOffice cannot open PPT files. Next, let us learn how to solve the problem of WPSOffice not being able to open PPT files. I hope it can help everyone. 1. First open WPSOffice and enter the homepage, as shown in the figure below. 2. Then enter the keyword "document repair" in the search bar above, and then click to open the document repair tool, as shown in the figure below. 3. Then import the PPT file for repair, as shown in the figure below.
![Corsair iCUE software not detecting RAM [Fixed]](https://img.php.cn/upload/article/000/465/014/170831448976874.png?x-oss-process=image/resize,m_fill,h_207,w_330) Corsair iCUE software not detecting RAM [Fixed]
Feb 19, 2024 am 11:48 AM
Corsair iCUE software not detecting RAM [Fixed]
Feb 19, 2024 am 11:48 AM
This article will explore what users can do when the CorsairiCUE software does not recognize the RAM in a Windows system. Although the CorsairiCUE software is designed to let users control their computer's RGB lighting, some users have found that the software does not function properly, resulting in an inability to detect RAM modules. Why doesn't ICUE pick up my memory? The main reason why ICUE cannot correctly identify RAM is usually related to background software conflicts. In addition, incorrect SPD write settings may also cause this problem. Fixed issue with CorsairIcue software not detecting RAM If CorsairIcue software is not detecting RAM on your Windows computer, please use the following suggestions.
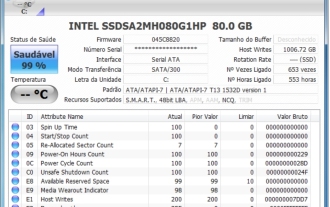 CrystalDiskinfo usage tutorial-What software is CrystalDiskinfo?
Mar 18, 2024 pm 04:50 PM
CrystalDiskinfo usage tutorial-What software is CrystalDiskinfo?
Mar 18, 2024 pm 04:50 PM
CrystalDiskInfo is a software used to check computer hardware devices. In this software, we can check our own computer hardware, such as reading speed, transmission mode, interface, etc.! So in addition to these functions, how to use CrystalDiskInfo and what exactly is CrystalDiskInfo? Let me sort it out for you! 1. The Origin of CrystalDiskInfo As one of the three major components of a computer host, a solid-state drive is the storage medium of a computer and is responsible for computer data storage. A good solid-state drive can speed up file reading and affect consumer experience. When consumers receive new devices, they can use third-party software or other SSDs to
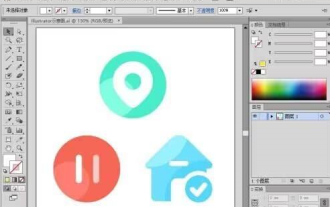 How to set the keyboard increment in Adobe Illustrator CS6 - How to set the keyboard increment in Adobe Illustrator CS6
Mar 04, 2024 pm 06:04 PM
How to set the keyboard increment in Adobe Illustrator CS6 - How to set the keyboard increment in Adobe Illustrator CS6
Mar 04, 2024 pm 06:04 PM
Many users are using the Adobe Illustrator CS6 software in their offices, so do you know how to set the keyboard increment in Adobe Illustrator CS6? Then, the editor will bring you the method of setting the keyboard increment in Adobe Illustrator CS6. Interested users can take a look below. Step 1: Start Adobe Illustrator CS6 software, as shown in the figure below. Step 2: In the menu bar, click the [Edit] → [Preferences] → [General] command in sequence. Step 3: The [Keyboard Increment] dialog box pops up, enter the required number in the [Keyboard Increment] text box, and finally click the [OK] button. Step 4: Use the shortcut key [Ctrl]
 How to resolve an incompatible software attempt to load with Edge?
Mar 15, 2024 pm 01:34 PM
How to resolve an incompatible software attempt to load with Edge?
Mar 15, 2024 pm 01:34 PM
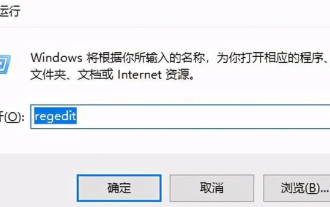
When we use the Edge browser, sometimes incompatible software attempts to be loaded together, so what is going on? Let this site carefully introduce to users how to solve the problem of trying to load incompatible software with Edge. How to solve an incompatible software trying to load with Edge Solution 1: Search IE in the start menu and access it directly with IE. Solution 2: Note: Modifying the registry may cause system failure, so operate with caution. Modify registry parameters. 1. Enter regedit during operation. 2. Find the path\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Micros
 What software is photoshopcs5? -photoshopcs5 usage tutorial
Mar 19, 2024 am 09:04 AM
What software is photoshopcs5? -photoshopcs5 usage tutorial
Mar 19, 2024 am 09:04 AM
PhotoshopCS is the abbreviation of Photoshop Creative Suite. It is a software produced by Adobe and is widely used in graphic design and image processing. As a novice learning PS, let me explain to you today what software photoshopcs5 is and how to use photoshopcs5. 1. What software is photoshop cs5? Adobe Photoshop CS5 Extended is ideal for professionals in film, video and multimedia fields, graphic and web designers who use 3D and animation, and professionals in engineering and scientific fields. Render a 3D image and merge it into a 2D composite image. Edit videos easily



